Aqua Security Connector
Aqua Security is a cloud-native security platform purpose-built for protecting containerized and cloud workloads across modern infrastructure. The Aqua Security CSPM connector integrates with Qualys Enterprise TruRisk Management via scheduled API calls to ingest cloud asset inventory, vulnerability findings, and misconfiguration data from across cloud environments, giving security teams a consolidated view of their cloud risk posture within ETM. It eliminates the manual effort of correlating Aqua findings with broader enterprise risk data by normalizing and enriching ingested assets through TruRisk scoring, enabling more informed prioritization and remediation decisions. Security teams managing cloud-native workloads gain unified visibility across cloud providers without duplicating effort across disconnected security tools.
The Aqua Security Connector is available on demand. To activate it for your subscription, contact your Technical Account Manager (TAM) or Qualys Support.
Overview
The Aqua Security Connector pulls asset and vulnerability data from Aqua's platform via REST API and imports it into the Qualys ETM Unified Asset Inventory. The connector supports multiple cloud-native asset classes — compute instances, container images, container instances, and serverless functions, across AWS, Azure, and GCP. Vulnerability findings are fetched for each supported asset class and correlated with ETM assets for risk analysis.
The connector operates unidirectionally, pulling data from Aqua into Qualys ETM. Each execution performs a full data pull; incremental sync is not supported.
Connector Details
Here is a comprehensive overview of what the Aqua Security Connector supports.
|
Vendor |
Aqua |
|
Product Name |
Aqua Security |
|
Connector Category |
Cloud Security |
|
Asset Types Supported |
Cloud Resources |
|
Findings Supported |
Yes |
|
Supported Version & Type |
SaaS (Latest) |
|
Integration Method |
API Integration (REST) |
|
Direction |
Unidirectional (Aqua Security to Qualys) |
|
Incremental Sync (Delta) |
Not Supported |
|
Import of Installed Software |
Not Supported |
|
Import of Source Tags |
Supported |
|
Filters/Filter Query |
Not Supported |
Connection Settings
User Roles and Permissions
An Administrator-level account is required to configure credentials for the Aqua Security Connector. The following objects must be created in Aqua before the connector can be configured:
Permission Set — Create a permission set with at least View access enabled for the following modules:
- Aqua Hub
- CSPM
- Workload Protection
For each module, set the toggle to Module is Enabled and select Set all as > View.
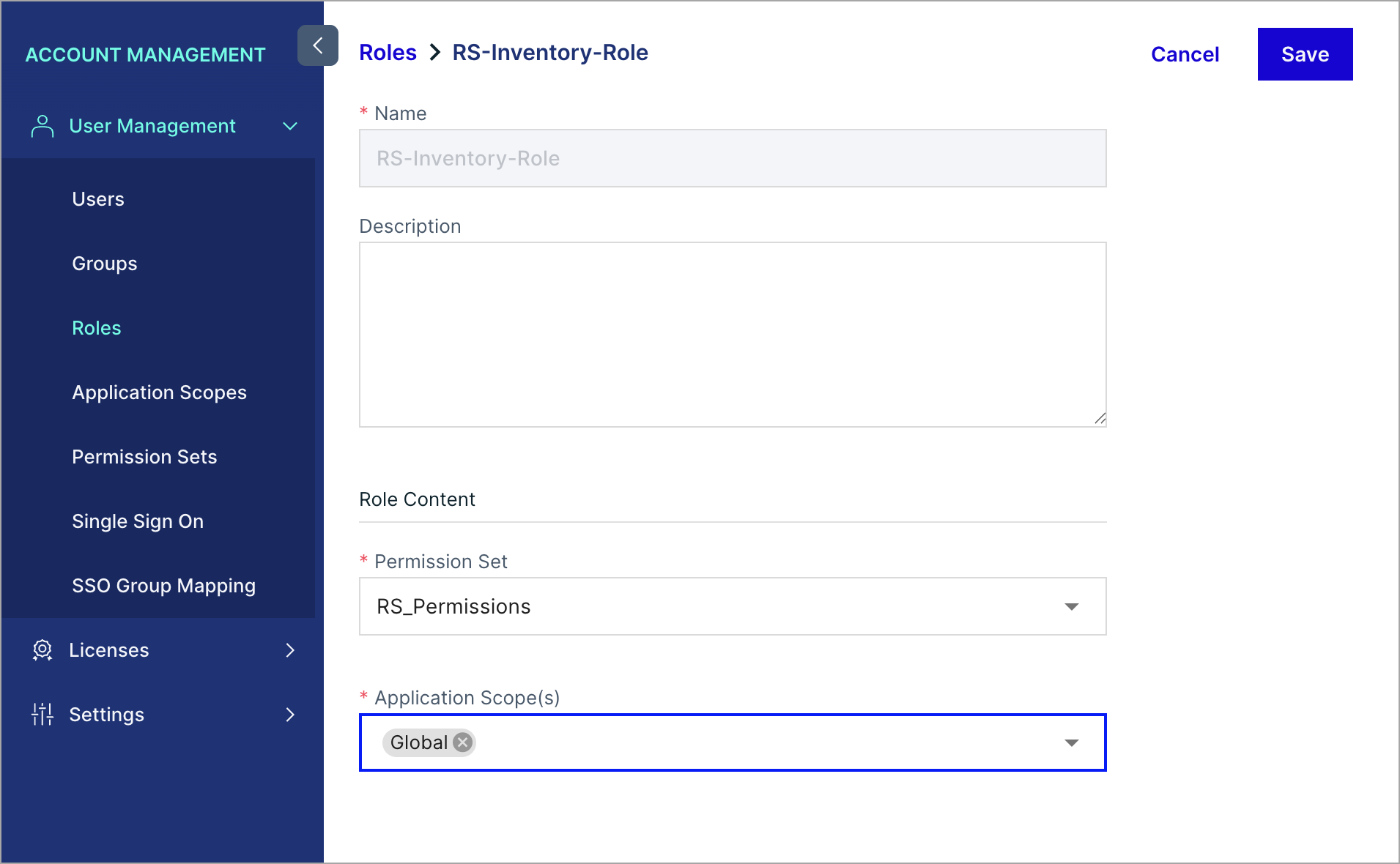
Role — Attach the permission set to a new role with Application Scope set to Global.
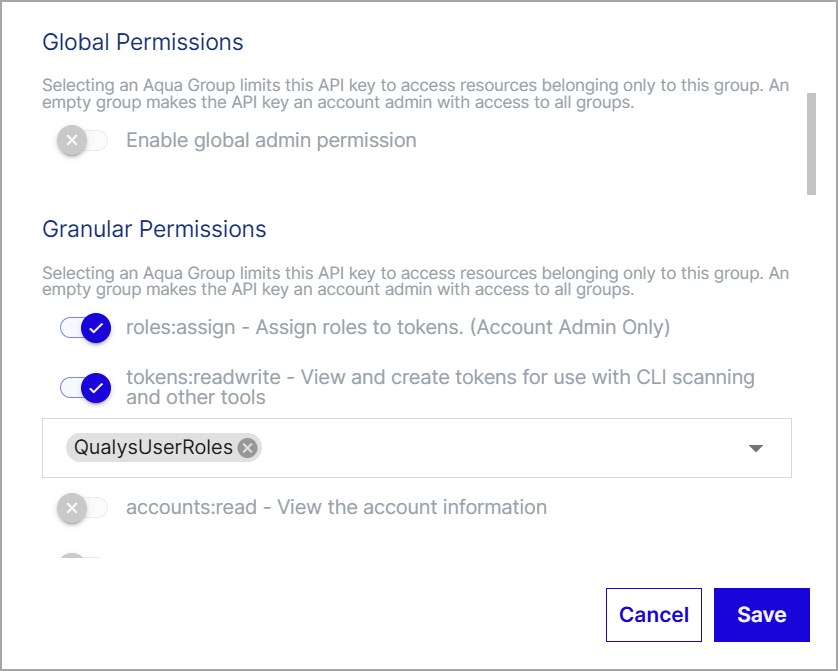
API Key — Generate an API key with the following configuration:
- Disable Enable global admin permission
- Enable the roles:assign and tokens:readwrite permissions
- Associate the key with the role created above
Steps to Create a Permission Set and Role
- Log in to the Aqua Security platform.
- From the top-left menu, select Account Management.
- From the left navigation menu, select Permission Sets, then select Add Permission Set.
- Enter a name for the permission set.
- In the Aqua Hub, CSPM, and Workload Protection sections:
- Set the toggle to Module is Enabled.
- Select Set all as > View.
- Select Confirm, then select Save.
- From the top-left menu, select Account Management.
- From the left navigation menu, select Roles, then select Add Role.
- Enter a name for the role.
- For Permission Set, select the permission set you created.
- For Application Scope(s), select Global.
- Select Save.
Steps to Generate an API Key
- Log in to the Aqua Security platform.
- From the top-left menu, select Account Management.
- From the left navigation menu, select Settings > API Keys.
- Select Generate Key.
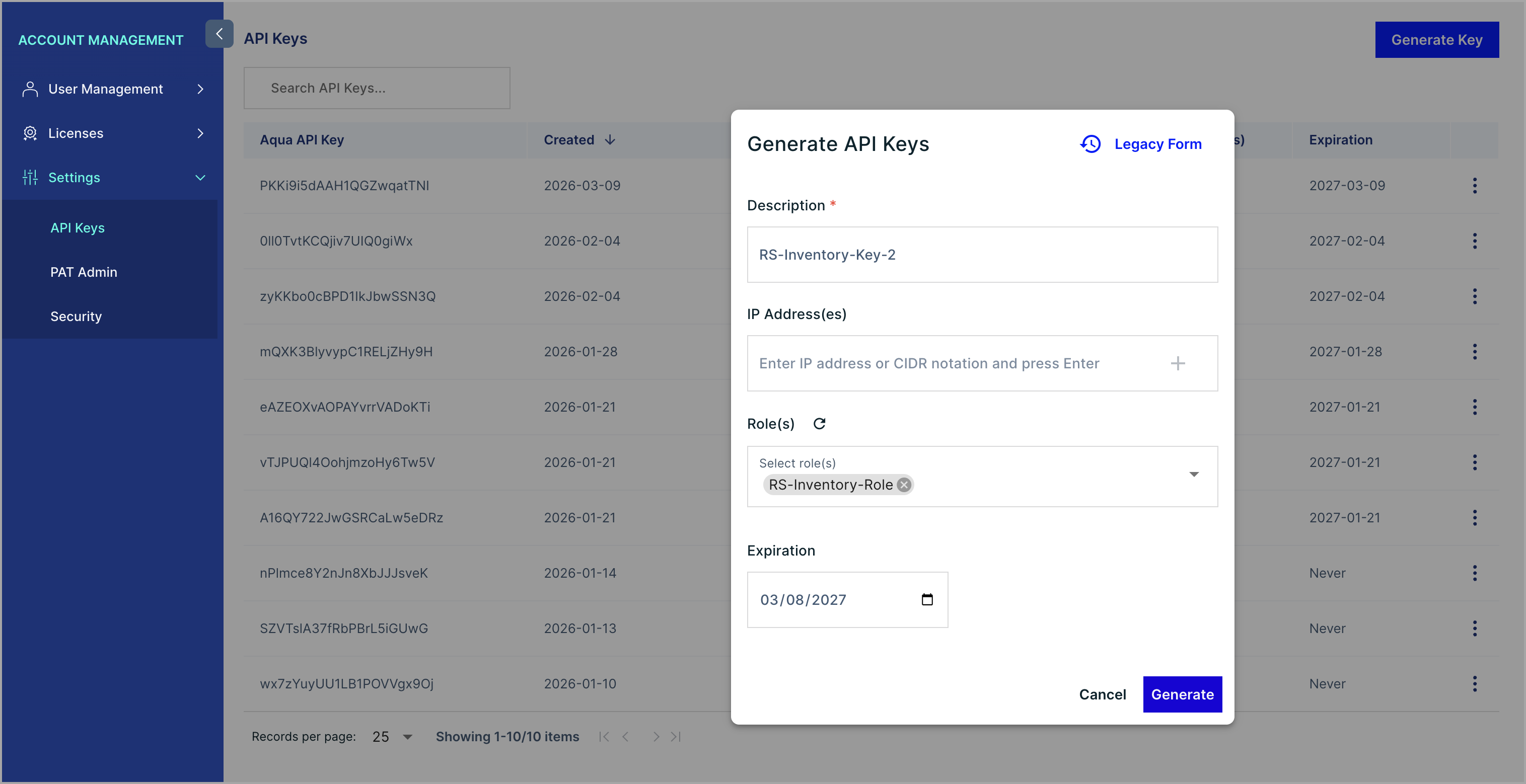
- Enter a description for the new API key and select Create.
- Copy the API Key and Secret values to a secure location. These values are not retrievable after the window is closed.
- On the API Keys page, select the vertical ellipses for the key you created and select Edit.
- Clear the Enable global admin permission toggle.
- Select the roles:assign and tokens:readwrite permissions.
- From the dropdown, select the role you created.
- Select Save.
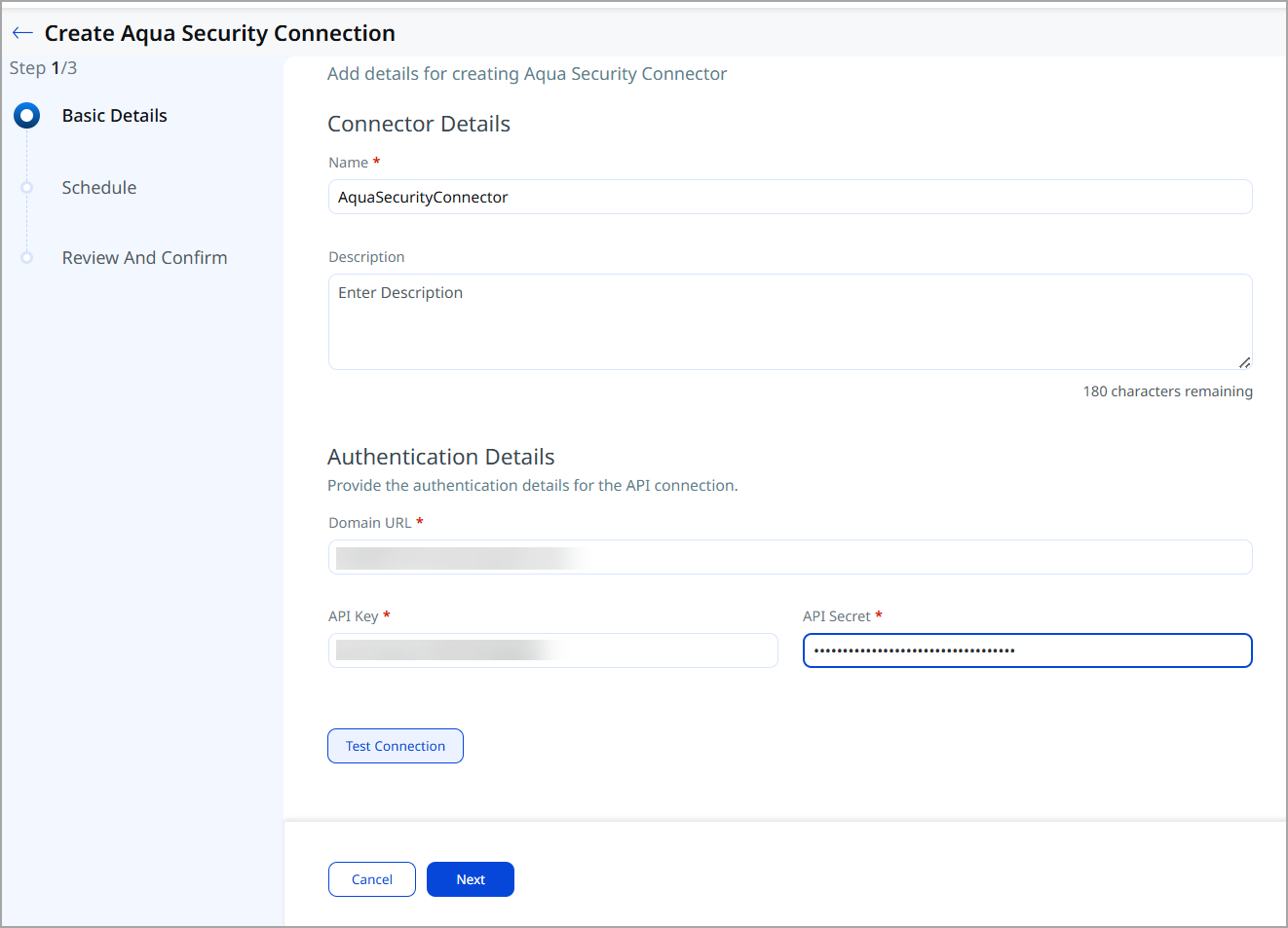
Authentication Details
Provide the following credentials in the connector configuration screen:
| Name | Key | Type | Description |
|---|---|---|---|
| Domain URL | domainUrl |
String | Authentication token endpoint. Example:
|
| API Key | api_key |
String | API Key generated in Aqua Security |
| API Secret | api_secret |
Encrypted | API Secret associated with the API Key |
Connector Configuration
Basic Details
- Log in to Qualys ETM.
- Navigate to Connectors > Integration and locate the Aqua Security Connector.
- Click Manage from the ellipses menu.
- Provide a Name and Description for the connector.
- Enter the Domain URL, API Key, and API Secret.
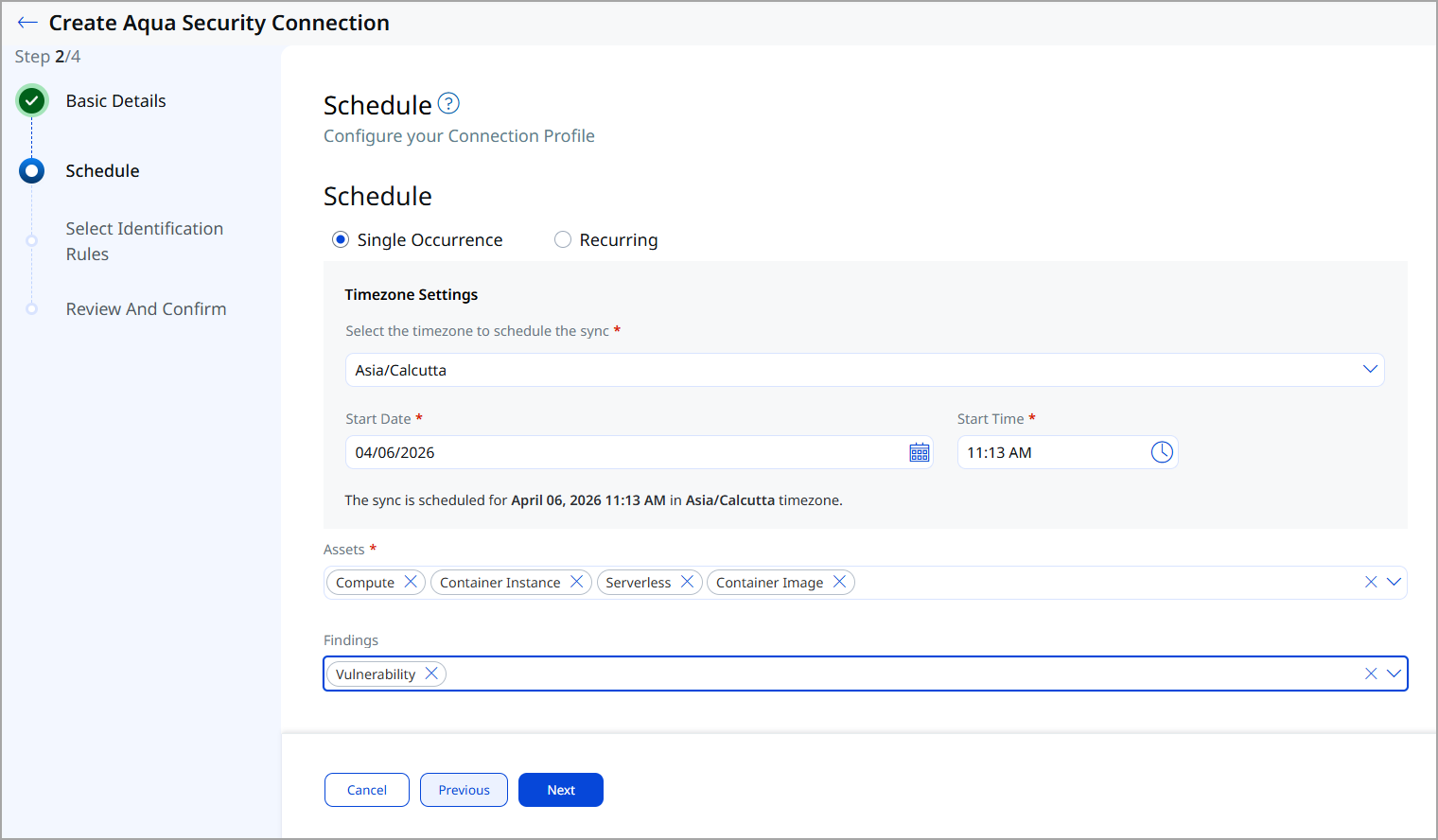
Schedule
Schedules control the execution and scope of the connector.
- Configure the execution Schedule — Single Occurrence or Recurring with start and end dates/times.
- Select the supported Asset Types to ingest.
- Select the Findings types to ingest.
Mapping Details
Data Model
The Aqua Security Connector provides out-of-the-box data model mappings for each supported asset class, both with and without associated vulnerability findings. View the data models in ETM to review all supported fields and their types.
Transform Maps
Default transform maps are provided for each asset class and finding type. You can create new maps or clone existing ones to customize field transformations.
Data Model Mapping – Compute: AWS EC2 Instance
| # | Source Field | Target Field |
|---|---|---|
| 1 | name | asset.assetDetail.name |
| 2 | tags[].key | asset.assetDetail.externalTags[].key |
| 3 | tags[].value | asset.assetDetail.externalTags[].value |
| 4 | externalAssetId | asset.assetHeader.externalAssetId (Required) |
| 5 | id | asset.assetHeader.vendorAssetId |
| 6 | sourceCreatedAt | asset.assetDetail.sourceCreatedAt |
| 7 | sourceUpdatedAt | asset.assetDetail.sourceUpdatedAt |
| 8 | region | asset.assetDetail.cloudInfo.region |
| 9 | cloud_info.vm_account_id | asset.assetDetail.cloudInfo.accountId |
| 10 | cloud_provider (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| 11 | cloud_info.vm_vpc_ids | asset.assetDetail.computeAssetClass.cloudInstance.vpcId |
| 12 | cloud_info.vm_image_id | asset.assetDetail.computeAssetClass.cloudInstance.imageId |
| 13 | resource_type | asset.assetDetail.computeAssetClass.services[].name |
| 14 | os | asset.assetDetail.operatingSystem.name |
| 15 | os | asset.assetDetail.operatingSystem.osCatalog.name |
| 16 | cloud_info.vm_hostname | asset.assetDetail.hostname |
| 17 | cloud_info.vm_private_ips[] | asset.assetDetail.network[].ipv4Addresses[] |
| 18 | cloud_info.vm_public_ips[] | asset.assetDetail.network[].publicIpv4Addresses[] |
| 19 | cloud_info.vm_hostname | asset.assetDetail.hostIdentity.hostname |
| 20 | externalAssetId | findingGroup.findings[].asset.externalAssetId |
| 21 | findings[].cwe_info[].Id | findingGroup.findings[].findingType.vulnerability.cweIds[] |
| 22 | findings[].resource.name | findingGroup.findings[].product.name |
| 23 | findings[].resource.cpe | findingGroup.findings[].product.cpeName |
| 24 | findings[].resource.version | findingGroup.findings[].product.version |
| 25 | findings[].name | findingGroup.findings[].name |
| 26 | findings[].vulnerability_id | findingGroup.findings[].externalFindingId (Required) |
| 27 | findings[].description | findingGroup.findings[].description |
| 28 | findings[].aqua_severity (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| 29 | findings[].first_found_date (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| 30 | findings[].last_found_date (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| 31 | name | findingGroup.findings[].findingType.vulnerability.cveId |
| 32 | vendor_url | findingGroup.findings[].findingURL |
| 33 | vendor_url | findingGroup.findings[].findingDetectionURL |
| 34 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Compute: Azure VM Instance
| # | Source Field | Target Field |
|---|---|---|
| 1 | name | asset.assetDetail.name |
| 2 | tags[].key | asset.assetDetail.externalTags[].key |
| 3 | tags[].value | asset.assetDetail.externalTags[].value |
| 4 | externalAssetId | asset.assetHeader.externalAssetId (Required) |
| 5 | id | asset.assetHeader.vendorAssetId |
| 6 | sourceCreatedAt | asset.assetDetail.sourceCreatedAt |
| 7 | sourceUpdatedAt | asset.assetDetail.sourceUpdatedAt |
| 8 | region | asset.assetDetail.cloudInfo.region |
| 9 | cloud_info.vm_account_id | asset.assetDetail.cloudInfo.accountId |
| 10 | cloud_provider (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| 11 | cloud_info.vm_vpc_ids | asset.assetDetail.computeAssetClass.cloudInstance.vpcId |
| 12 | cloud_info.vm_image_id | asset.assetDetail.computeAssetClass.cloudInstance.imageId |
| 13 | resource_type | asset.assetDetail.computeAssetClass.services[].name |
| 14 | os | asset.assetDetail.operatingSystem.name |
| 15 | os | asset.assetDetail.operatingSystem.osCatalog.name |
| 16 | cloud_info.vm_hostname | asset.assetDetail.hostname |
| 17 | cloud_info.vm_private_ips[] | asset.assetDetail.network[].ipv4Addresses[] |
| 18 | cloud_info.vm_public_ips[] | asset.assetDetail.network[].publicIpv4Addresses[] |
| 19 | cloud_info.vm_hostname | asset.assetDetail.hostIdentity.hostname |
| 20 | externalAssetId | findingGroup.findings[].asset.externalAssetId |
| 21 | findings[].cwe_info[].Id | findingGroup.findings[].findingType.vulnerability.cweIds[] |
| 22 | findings[].resource.name | findingGroup.findings[].product.name |
| 23 | findings[].resource.cpe | findingGroup.findings[].product.cpeName |
| 24 | findings[].resource.version | findingGroup.findings[].product.version |
| 25 | findings[].name | findingGroup.findings[].name |
| 26 | findings[].vulnerability_id | findingGroup.findings[].externalFindingId (Required) |
| 27 | findings[].description | findingGroup.findings[].description |
| 28 | findings[].aqua_severity (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| 29 | findings[].first_found_date (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| 30 | findings[].last_found_date (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| 31 | name | findingGroup.findings[].findingType.vulnerability.cveId |
| 32 | vendor_url | findingGroup.findings[].findingURL |
| 33 | vendor_url | findingGroup.findings[].findingDetectionURL |
| 34 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Compute: GCP VM Instance
| # | Source Field | Target Field |
|---|---|---|
| 1 | name | asset.assetDetail.name |
| 2 | tags[].key | asset.assetDetail.externalTags[].key |
| 3 | tags[].value | asset.assetDetail.externalTags[].value |
| 4 | externalAssetId | asset.assetHeader.externalAssetId (Required) |
| 5 | id | asset.assetHeader.vendorAssetId |
| 6 | sourceCreatedAt | asset.assetDetail.sourceCreatedAt |
| 7 | sourceUpdatedAt | asset.assetDetail.sourceUpdatedAt |
| 8 | region | asset.assetDetail.cloudInfo.region |
| 9 | cloud_info.vm_account_id | asset.assetDetail.cloudInfo.accountId |
| 10 | cloud_provider (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| 11 | cloud_info.vm_vpc_ids | asset.assetDetail.computeAssetClass.cloudInstance.vpcId |
| 12 | cloud_info.vm_image_id | asset.assetDetail.computeAssetClass.cloudInstance.imageId |
| 13 | resource_type | asset.assetDetail.computeAssetClass.services[].name |
| 14 | os | asset.assetDetail.operatingSystem.name |
| 15 | os | asset.assetDetail.operatingSystem.osCatalog.name |
| 16 | cloud_info.vm_hostname | asset.assetDetail.hostname |
| 17 | cloud_info.vm_private_ips[] | asset.assetDetail.network[].ipv4Addresses[] |
| 18 | cloud_info.vm_public_ips[] | asset.assetDetail.network[].publicIpv4Addresses[] |
| 19 | cloud_info.vm_hostname | asset.assetDetail.hostIdentity.hostname |
| 20 | externalAssetId | findingGroup.findings[].asset.externalAssetId |
| 21 | findings[].cwe_info[].Id | findingGroup.findings[].findingType.vulnerability.cweIds[] |
| 22 | findings[].resource.name | findingGroup.findings[].product.name |
| 23 | findings[].resource.cpe | findingGroup.findings[].product.cpeName |
| 24 | findings[].resource.version | findingGroup.findings[].product.version |
| 25 | findings[].name | findingGroup.findings[].name |
| 26 | findings[].vulnerability_id | findingGroup.findings[].externalFindingId (Required) |
| 27 | findings[].description | findingGroup.findings[].description |
| 28 | findings[].aqua_severity (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| 29 | findings[].first_found_date (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| 30 | findings[].last_found_date (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| 31 | name | findingGroup.findings[].findingType.vulnerability.cveId |
| 32 | vendor_url | findingGroup.findings[].findingURL |
| 33 | vendor_url | findingGroup.findings[].findingDetectionURL |
| 34 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Container Image
| # | Source Field | Target Field |
|---|---|---|
| 1 | name | asset.assetDetail.name |
| 2 | tags[].key | asset.assetDetail.externalTags[].key |
| 3 | tags[].value | asset.assetDetail.externalTags[].value |
| 4 | created (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| 5 | scan_date (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| 6 | name | asset.assetDetail.containerImageAssetClass.name |
| 7 | tag | asset.assetDetail.containerImageAssetClass.tag |
| 8 | registry | asset.assetDetail.containerImageAssetClass.registry |
| 9 | repository | asset.assetDetail.containerImageAssetClass.repository |
| 10 | digest | asset.assetDetail.containerImageAssetClass.digest |
| 11 | externalAssetId | asset.assetHeader.externalAssetId (Required) |
| 12 | externalAssetId | asset.assetHeader.vendorAssetId |
| 13 | architecture | asset.assetDetail.containerImageAssetClass.architecture |
| 14 | FUNCTION_PICKER (CONCAT os + " " + os_version) | asset.assetDetail.operatingSystem.name |
| 15 | FUNCTION_PICKER (CONCAT os + " " + os_version) | asset.assetDetail.operatingSystem.osCatalog.name |
| 16 | os_version | asset.assetDetail.operatingSystem.version |
| 17 | os_version | asset.assetDetail.operatingSystem.osCatalog.version |
| 18 | size | asset.assetDetail.containerImageAssetClass.sizeInBytes |
| 19 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Container Image Vulnerability
| # | Source Field | Target Field |
|---|---|---|
| 1 | image_digest | asset.assetHeader.externalAssetId (Required) |
| 2 | image_digest | asset.assetHeader.vendorAssetId |
| 3 | image_name | asset.assetDetail.name |
| 4 | cwe_info[].Id | findingGroup.findings[].findingType.vulnerability.cweIds[] |
| 5 | resource.name | findingGroup.findings[].product.name |
| 6 | resource.cpe | findingGroup.findings[].product.cpeName |
| 7 | resource.version | findingGroup.findings[].product.version |
| 8 | name | findingGroup.findings[].name |
| 9 | vulnerability_id | findingGroup.findings[].externalFindingId (Required) |
| 10 | description | findingGroup.findings[].description |
| 11 | aqua_severity (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| 12 | first_found_date (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| 13 | last_found_date (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| 14 | name | findingGroup.findings[].findingType.vulnerability.cveId |
| 15 | vendor_url | findingGroup.findings[].findingURL |
| 16 | vendor_url | findingGroup.findings[].findingDetectionURL |
| 17 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Container Instance: AWS
| # | Source Field | Target Field |
|---|---|---|
| 1 | image_id | asset.assetDetail.containerInstanceAssetClass.image.digest |
| 2 | container_uid | asset.assetHeader.vendorAssetId |
| 3 | container_uid | asset.assetDetail.containerInstanceAssetClass.id |
| 4 | name | asset.assetDetail.name |
| 5 | id | asset.assetHeader.externalAssetId (Required) |
| 6 | create_time | asset.assetDetail.sourceCreatedAt |
| 7 | create_time | asset.assetDetail.sourceUpdatedAt |
| 8 | imageTag | asset.assetDetail.containerInstanceAssetClass.image.tag |
| 9 | imageRegistry | asset.assetDetail.containerInstanceAssetClass.image.registry |
| 10 | imageRepository | asset.assetDetail.containerInstanceAssetClass.image.repository |
| 11 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Container Instance: Azure
| # | Source Field | Target Field |
|---|---|---|
| 1 | image_id | asset.assetDetail.containerInstanceAssetClass.image.digest |
| 2 | container_uid | asset.assetHeader.vendorAssetId |
| 3 | container_uid | asset.assetDetail.containerInstanceAssetClass.id |
| 4 | name | asset.assetDetail.name |
| 5 | id | asset.assetHeader.externalAssetId (Required) |
| 6 | create_time | asset.assetDetail.sourceCreatedAt |
| 7 | create_time | asset.assetDetail.sourceUpdatedAt |
| 8 | imageTag | asset.assetDetail.containerInstanceAssetClass.image.tag |
| 9 | imageRegistry | asset.assetDetail.containerInstanceAssetClass.image.registry |
| 10 | imageRepository | asset.assetDetail.containerInstanceAssetClass.image.repository |
| 11 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Container Instance: GCP
| # | Source Field | Target Field |
|---|---|---|
| 1 | image_id | asset.assetDetail.containerInstanceAssetClass.image.digest |
| 2 | container_uid | asset.assetHeader.vendorAssetId |
| 3 | container_uid | asset.assetDetail.containerInstanceAssetClass.id |
| 4 | name | asset.assetDetail.name |
| 5 | id | asset.assetHeader.externalAssetId (Required) |
| 6 | create_time | asset.assetDetail.sourceCreatedAt |
| 7 | create_time | asset.assetDetail.sourceUpdatedAt |
| 8 | imageTag | asset.assetDetail.containerInstanceAssetClass.image.tag |
| 9 | imageRegistry | asset.assetDetail.containerInstanceAssetClass.image.registry |
| 10 | imageRepository | asset.assetDetail.containerInstanceAssetClass.image.repository |
| 11 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Container Instance Vulnerability
| # | Source Field | Target Field |
|---|---|---|
| 1 | container_id | asset.assetHeader.externalAssetId (Required) |
| 2 | container_id | asset.assetHeader.vendorAssetId |
| 3 | container_name | asset.assetDetail.name |
| 4 | resource.name | findingGroup.findings[].product.name |
| 5 | resource.cpe | findingGroup.findings[].product.cpeName |
| 6 | resource.version | findingGroup.findings[].product.version |
| 7 | name | findingGroup.findings[].name |
| 8 | vulnerability_id | findingGroup.findings[].externalFindingId (Required) |
| 9 | aqua_severity (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| 10 | first_found_date (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| 11 | last_found_date (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| 12 | name | findingGroup.findings[].findingType.vulnerability.cveId |
| 13 | vendor_url | findingGroup.findings[].findingURL |
| 14 | vendor_url | findingGroup.findings[].findingDetectionURL |
| 15 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Serverless: AWS Lambda Function
| # | Source Field | Target Field |
|---|---|---|
| 1 | name | asset.assetDetail.name |
| 2 | tags[].key | asset.assetDetail.externalTags[].key |
| 3 | tags[].value | asset.assetDetail.externalTags[].value |
| 4 | externalAssetId | asset.assetHeader.externalAssetId (Required) |
| 5 | externalAssetId | asset.assetHeader.vendorAssetId |
| 6 | cloud_provider (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| 7 | name | asset.assetDetail.serverlessAssetClass.functionName |
| 8 | FUNCTION_PICKER (CONCAT runtime_language + runtime_version) | asset.assetDetail.serverlessAssetClass.runtime |
| 9 | last_scan (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| 10 | last_scan (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| 11 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Serverless: Azure App Service
| # | Source Field | Target Field |
|---|---|---|
| 1 | name | asset.assetDetail.name |
| 2 | tags[].key | asset.assetDetail.externalTags[].key |
| 3 | tags[].value | asset.assetDetail.externalTags[].value |
| 4 | externalAssetId | asset.assetHeader.externalAssetId (Required) |
| 5 | externalAssetId | asset.assetHeader.vendorAssetId |
| 6 | cloud_provider (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| 7 | name | asset.assetDetail.serverlessAssetClass.functionName |
| 8 | FUNCTION_PICKER (CONCAT runtime_language + runtime_version) | asset.assetDetail.serverlessAssetClass.runtime |
| 9 | last_scan (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| 10 | last_scan (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| 11 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Serverless: GCP Cloud Run
| # | Source Field | Target Field |
|---|---|---|
| 1 | name | asset.assetDetail.name |
| 2 | tags[].key | asset.assetDetail.externalTags[].key |
| 3 | tags[].value | asset.assetDetail.externalTags[].value |
| 4 | externalAssetId | asset.assetHeader.externalAssetId (Required) |
| 5 | externalAssetId | asset.assetHeader.vendorAssetId |
| 6 | cloud_provider (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| 7 | name | asset.assetDetail.serverlessAssetClass.functionName |
| 8 | FUNCTION_PICKER (CONCAT runtime_language + runtime_version) | asset.assetDetail.serverlessAssetClass.runtime |
| 9 | last_scan (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| 10 | last_scan (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| 11 | FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Data Model Mapping – Serverless Vulnerability
| # | Source Field | Target Field |
|---|---|---|
| 1 | function_id | asset.assetHeader.externalAssetId (Required) |
| 2 | function_id | asset.assetHeader.vendorAssetId |
| 3 | function_name | asset.assetDetail.name |
| 4 | cwe_info[].Id | findingGroup.findings[].findingType.vulnerability.cweIds[] |
| 5 | resource.name | findingGroup.findings[].product.name |
| 6 | resource.cpe | findingGroup.findings[].product.cpeName |
| 7 | resource.version | findingGroup.findings[].product.version |
| 8 | name | findingGroup.findings[].name |
| 9 | vulnerability_id | findingGroup.findings[].externalFindingId (Required) |
| 10 | description | findingGroup.findings[].description |
| 11 | aqua_severity (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| 12 | first_found_date (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| 13 | last_found_date (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| 14 | name | findingGroup.findings[].findingType.vulnerability.cveId |
| 15 | nvd_url | findingGroup.findings[].findingURL |
| 16 | nvd_url | findingGroup.findings[].findingDetectionURL |
| 17 | asset_type_name | asset.assetHeader.assetTypeName |
Identification Rules
Identification Rules are provided out-of-the-box by Qualys CSAM. They control how findings are matched to assets within ETM. These rules are applicable to compute asset types; other asset classes are not affected. Proceed without changes unless your environment requires custom matching logic. Ensure at least one identification rule is active before running the connector.
How Does a Connection Work?
On schedule or on demand, the Aqua Security Connector retrieves selected asset classes and vulnerability findings from Aqua via REST API and imports them into the ETM Inventory. Each execution performs a full pull; no incremental or delta sync occurs. Only High and Critical CVEs are fetched due to the high volume of vulnerability data generated by Aqua's per-package vulnerability model.
A successfully configured connector transitions through the following states:
- Registered — The connector is created and registered to fetch data from Aqua Security.
- Scheduled — The connector is scheduled to execute at the configured time.
- Processing — The connector is actively fetching asset and findings data from Aqua.
- Processed — Asset data has been successfully fetched. Findings processing may continue in the background.
The Processed state confirms the connector is operational, but findings import — particularly for large datasets — may require additional time to complete. The full import process may take up to a few hours depending on data volume.
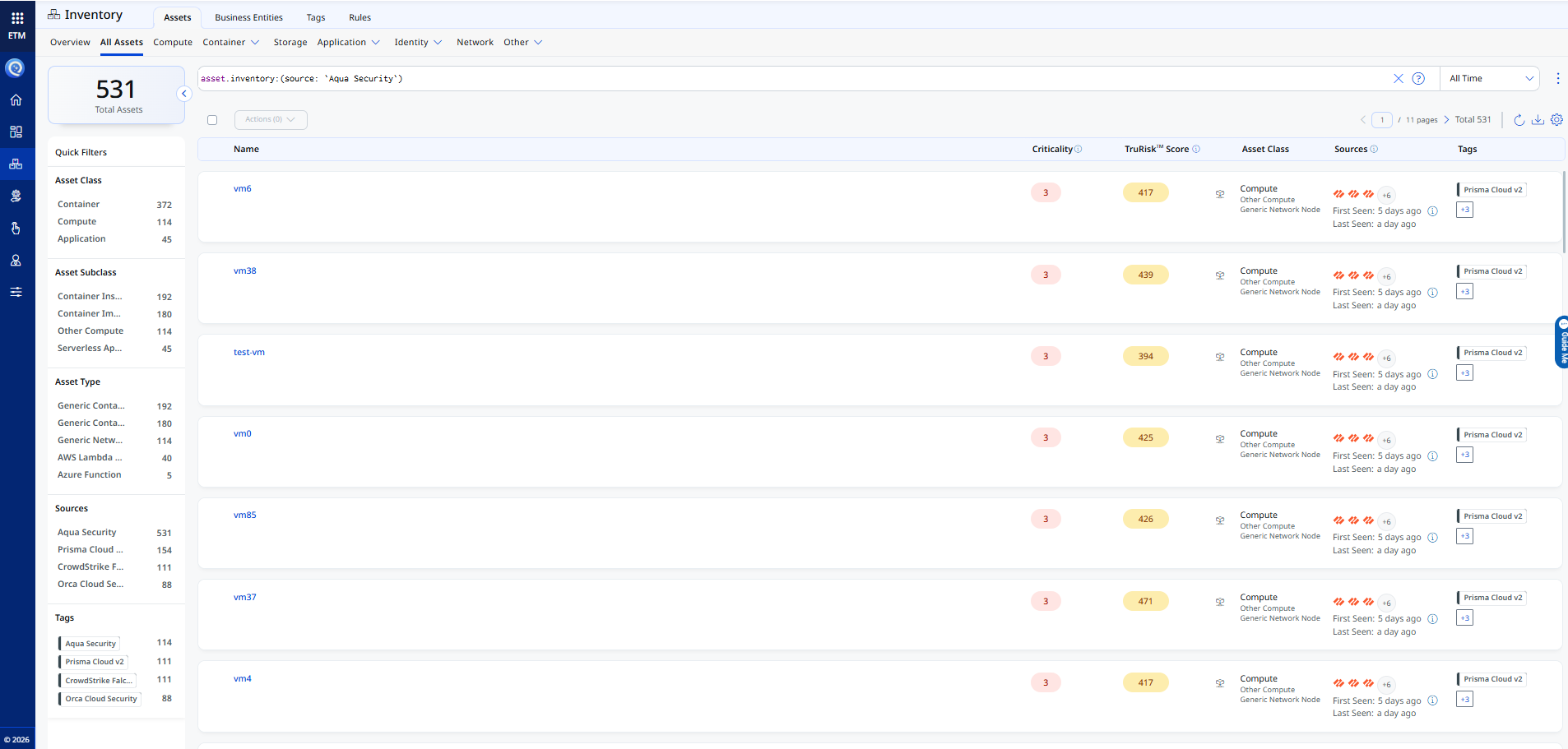
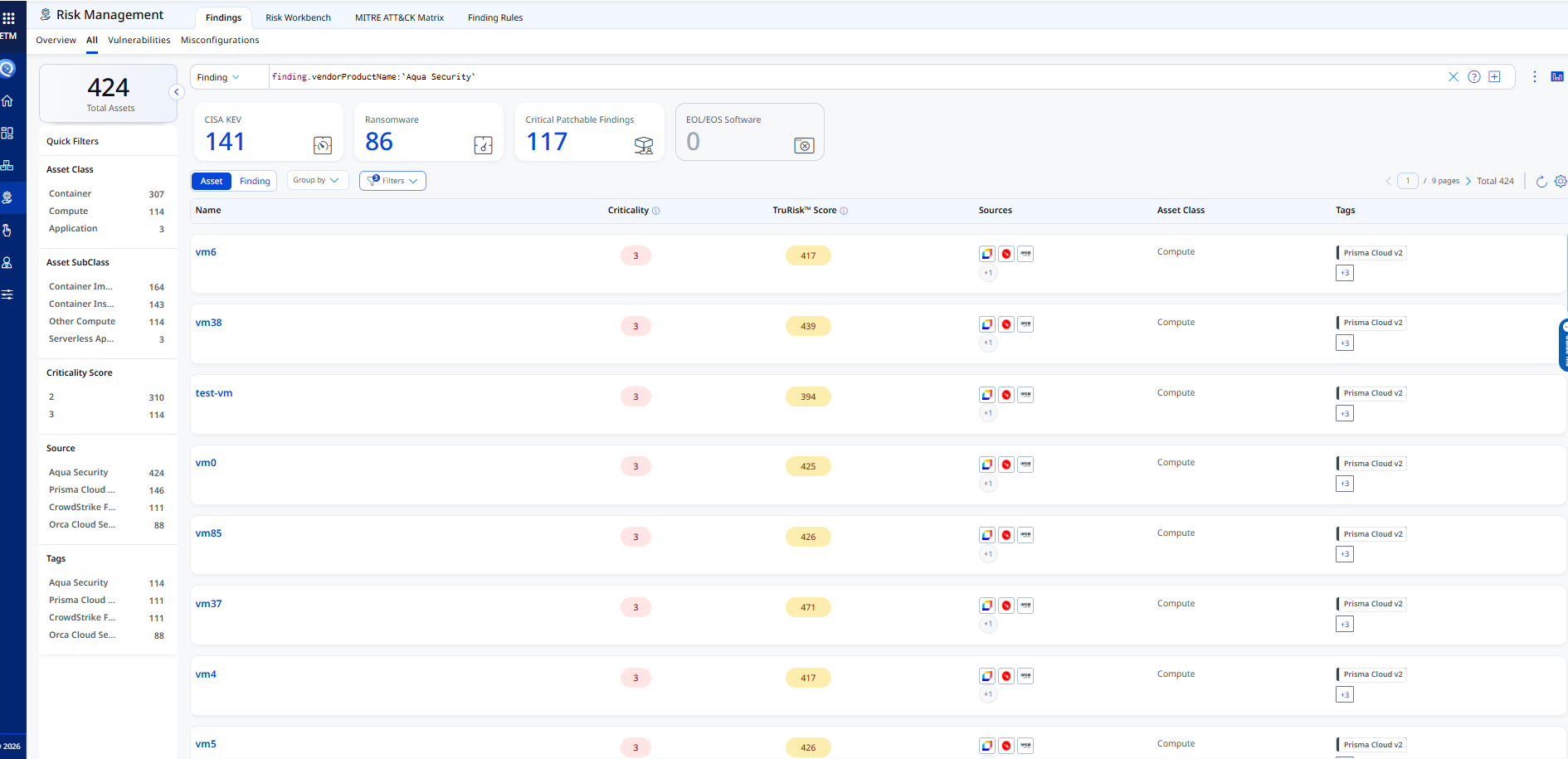
Viewing Assets and Findings in ETM
After a successful run, Aqua Security assets and findings are available in ETM.
- Assets: Go to Inventory > Assets > All Assets. Filter with
tags.name:"Aqua Security"orasset.inventory:"Aqua Security".
- Findings: Go to Risk Management > Findings > Vulnerability. Filter with
finding.vendorProductName:"Aqua Security". Click any finding to open a detailed view.
API Reference
The connector uses the following Aqua Security API endpoints to fetch asset and vulnerability data:
| API Function | Endpoint | Notes |
|---|---|---|
| Authentication | POST https://api.cloudsploit.com/v2/tokens |
Returns bearer token using API Key and Secret |
| Fetch VM Assets | GET <domain>/api/v2/infrastructure/vms |
Returns compute assets for AWS, Azure, and GCP |
| Fetch Container Images | GET <domain>/api/v2/images |
Cloud-agnostic; covers all registries |
| Fetch Container Instances | GET <domain>/api/v2/containers |
Returns running container instances |
| Fetch Serverless Functions | GET <domain>/api/v2/serverless/functions |
Returns Lambda, App Service, and Cloud Run functions |
| Fetch Image Vulnerabilities | GET <domain>/api/v2/risks/vulnerabilities |
Vulnerabilities for container images |
| Fetch Serverless Vulnerabilities | GET <domain>/api/v2/risks/functions/vulnerabilities |
Vulnerabilities for serverless functions |
| Fetch Container Vulnerabilities | GET <domain>/api/v2/hub/findings/vulnerabilities/containers/list |
Vulnerabilities for container instances |
| Fetch VM Vulnerabilities | GET <domain>/api/v2/hub/findings/vulnerabilities/hosts/list |
Filtered by search_attribute=vm_name |