Armis Centrix Connector
Armis Centrix is a cyber exposure management platform that delivers real-time visibility, risk assessment, and proactive protection of an organization's entire digital attack surface. Powered by an AI-driven Asset Intelligence Engine, it continuously discovers, monitors, and secures every asset across complex environments, spanning IT, OT, IoT, and IoMT devices.
Through automated risk scoring, vulnerability detection, and dynamic network segmentation, Armis Centrix helps organizations minimize cyber risk, enforce security policies, and remediate threats before they impact business operations. This connector enables ingestion of compute assets and their associated security findings into the Qualys Enterprise TruRisk Platform, which uses that data for further correlation and processing.
Connector Details
The following table summarizes the supported capabilities of the Armis Centrix Connector.
|
Vendor |
Armis |
|
Product |
Armis Centrix |
|
Connector Category |
Assets & Assets + findings |
|
Asset Types Supported |
Host-Machine |
|
Finding Support |
Yes |
|
Supported Version & Type |
1.0.0 |
|
Integration Method |
API Integration (REST) |
|
Direction |
Unidirectional (Armis Centrix to Qualys) |
|
Incremental Sync (Delta) |
Supported (Asset-only connector) |
Configure the Connector
Before You Begin - AuthenticationBefore You Begin - Authentication
Generate a Secret Key in Armis
- Log in to your Armis Centrix instance.
- Navigate to the Settings icon.
- Go to Medical Device Security Settings > API Management.
- Click Create Secret Key.
- Copy the generated Secret Key for use during connector configuration.
Permissions Required
The Armis account used for the connector must have read access permissions to retrieve device inventory and vulnerability data.
Scope and Data Access
The connector retrieves data using the following Armis REST API endpoints:
| API Function | Endpoint |
| Retrieve Devices | https://ic.armis.com/api/v1/device/_search |
| Retrieve Vulnerabilities | https://ic.armis.com/api/v1/cve/_search |
Key Rotation
Rotate the Secret Key periodically according to your organization's credential rotation policy.
Create a Profile & ConnectionCreate a Profile & Connection
Create the connector profile and provide authentication details for the Armis platform.
Connector Details
| Field | Description |
| Name | Name of the connector profile. |
| Description | Optional description for the connector profile. |
| Supported Format | Armis Centrix |
Authentication Details
| Field | Type | Description |
|---|---|---|
| Base URL | String | Base URL of the Armis platform. Example: https://lab-qualys.armis.com |
| Secret Key | Encrypted String | Secret Key generated from the Armis API Management settings. |
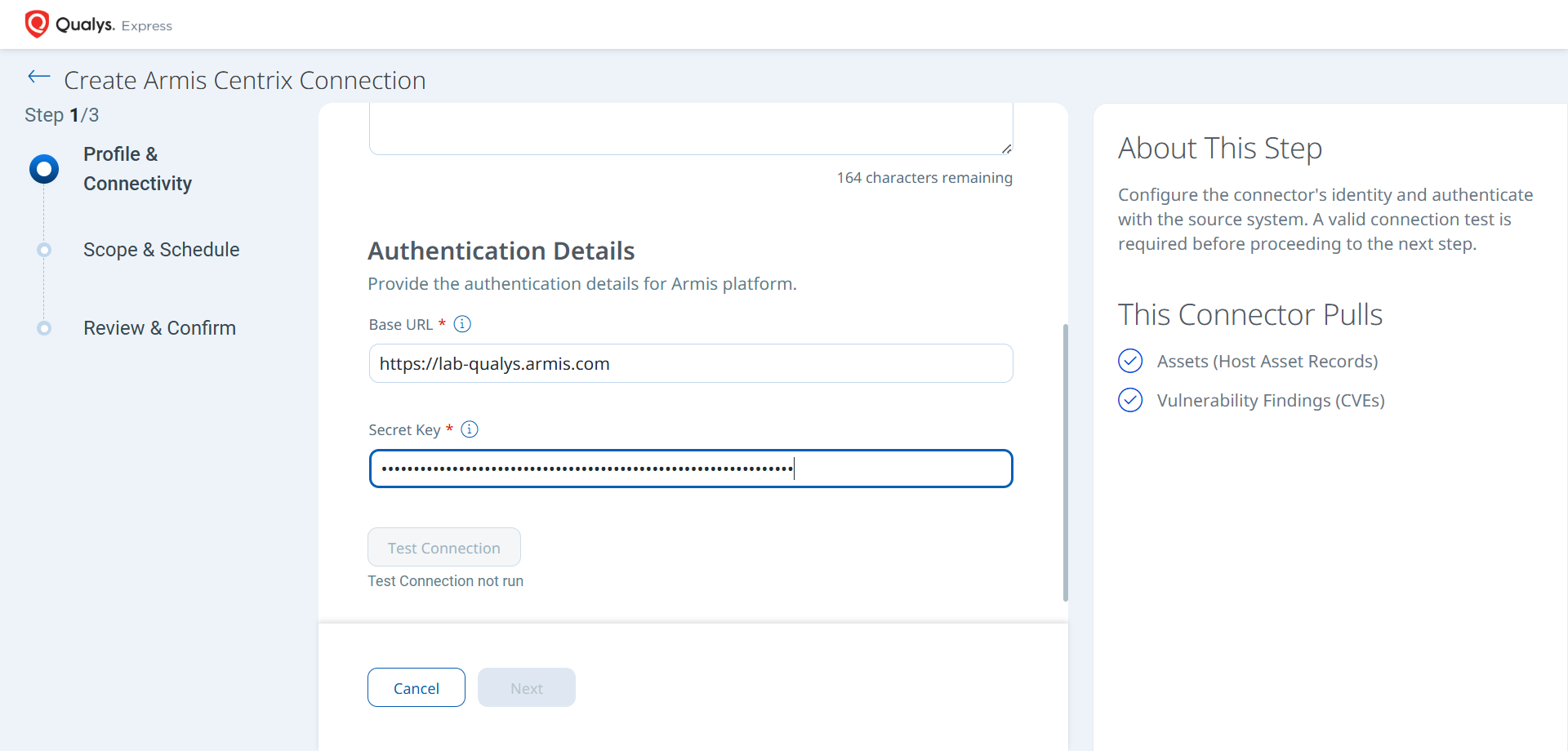
After entering the authentication details, click Test Connection to validate connectivity.
- Network Reachability — Verifies that the connector endpoint is reachable over HTTPS (port 443).
- TLS Handshake — Confirms that a secure TLS connection can be established with the remote endpoint.
- Authentication Credential Check — Validates the configured credentials against the source system's authentication endpoint.
- Authorization Scope Check — Confirms that the provided credentials have the required permissions to access the configured data scope.
- Data Fetch — Verifies that data can be successfully retrieved from the source system using the configured connection.
Set the Scope & ScheduleSet the Scope & Schedule
Select the type of data to import and configure the synchronization schedule.
- Assets & Findings – Imports both asset inventory and CVE findings.
- Assets – Imports only asset inventory records.
Configure the schedule frequency using the Occurs field. The connector supports recurring scheduled imports.
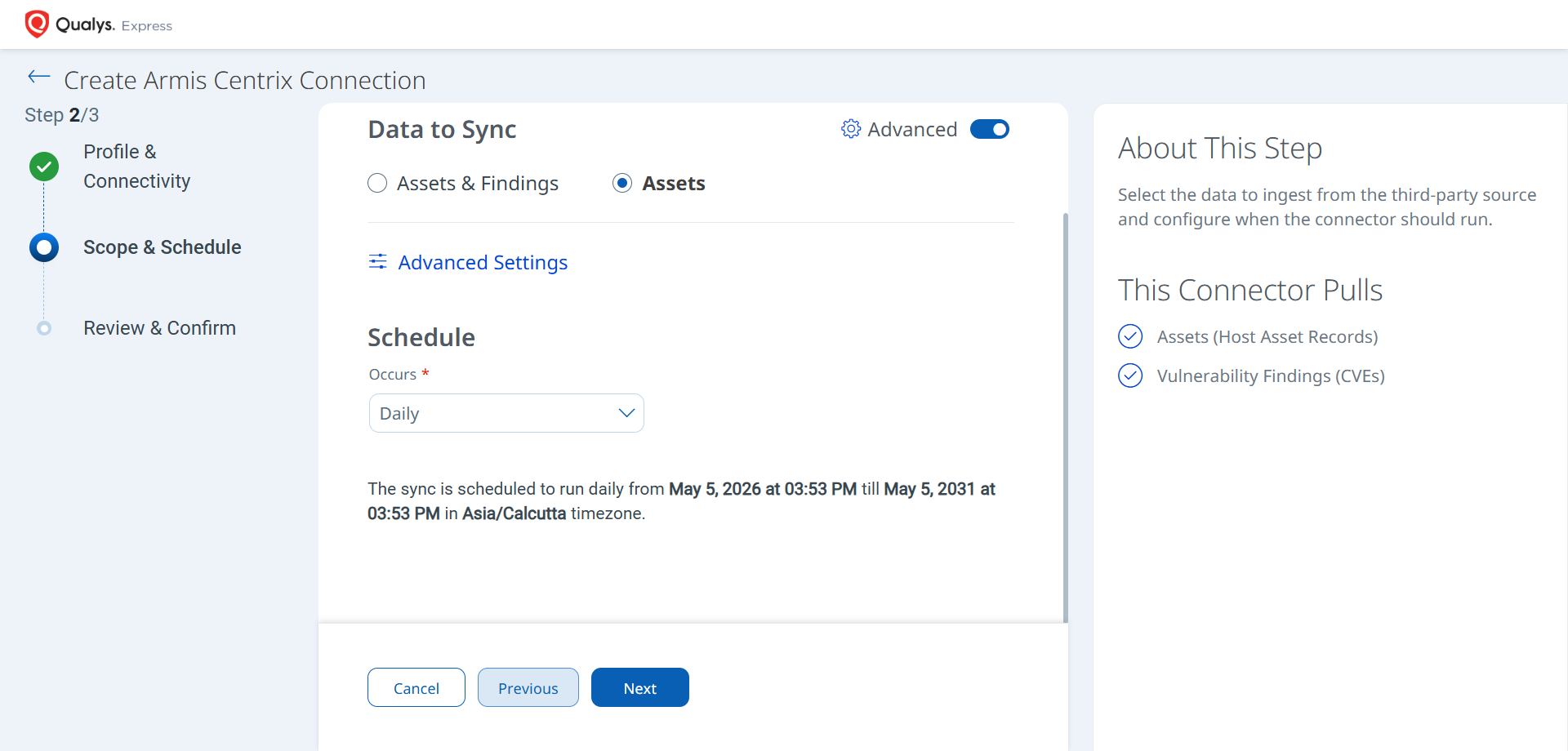
Note: The schedule duration is configured for a 5-year period based on the selected timezone.
Advanced Settings
The Advanced Settings page allows you to configure optional filters and transformation maps.
Filters Tab
The connector supports filter-based scoping using free-text input fields.
Supported filter fields include:
Site NameBoundary NameBusiness ImpactBaseline Start FromTime Frame
These filters restrict the assets and findings imported during connector execution.
Note: Click Save after configuring Advanced Settings to retain the filter values.
How the Connection Works
The Armis Centrix Connector retrieves device inventory data and associated vulnerability findings from the Armis platform and imports them into Qualys ETM.
The connector supports importing:
- Assets (Host Asset Records)
- Vulnerability Findings (CVEs)
The connector can be configured to import assets only or assets with associated findings.
Connector States
During execution, the connector transitions through the following states:
- Registered – The connector is successfully created.
- Scheduled – The connector is queued for execution.
- Processing – Asset and findings data is actively being retrieved and processed.
- Processed – The connector completed the import process successfully.
Note: Initial imports may take up to 2 hours to complete depending on data volume.
Note: The connector may display the Processed state while findings correlation and indexing continue in the background.
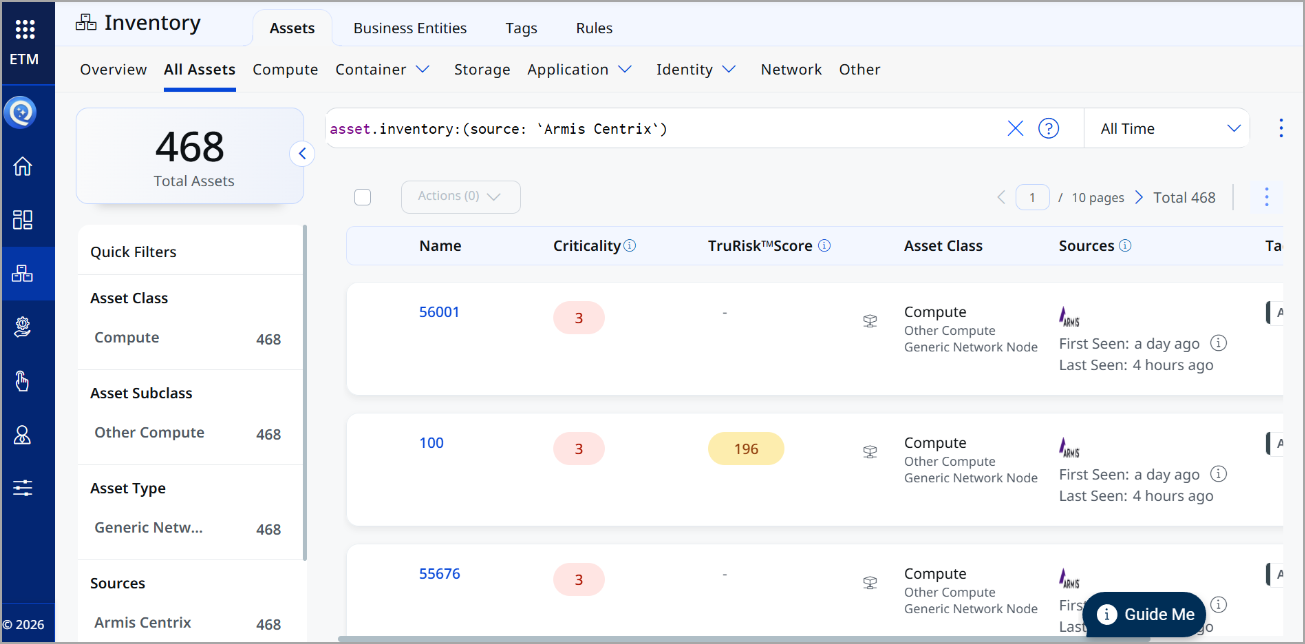
Viewing Assets and Findings in ETM
After successful synchronization, imported data can be viewed in ETM.
Assets
Go to Inventory > Assets and filter using:
inventory:(source:"Armis")
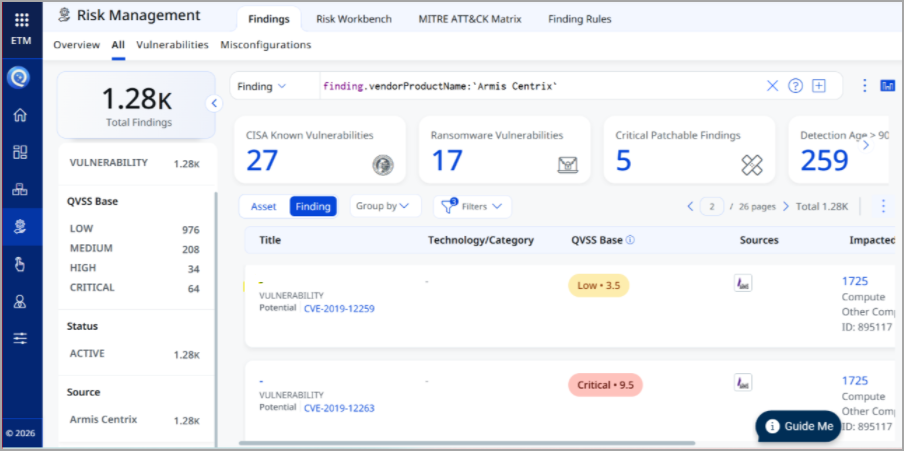
Findings
Go to Risk Management > Findings and filter using:
findings.vendorProductname:"Armis Centrix"
Troubleshooting
| Connector remains in Processing state | The full import process may take up to 2 hours to complete. Allow sufficient processing time before troubleshooting the connector. |
Additional Information
API Reference
| API Function | Endpoint |
|---|---|
| Retrieve Devices | https://ic.armis.com/api/v1/device/_search |
| Retrieve Vulnerabilities | https://ic.armis.com/api/v1/cve/_search |
Transform Map Tab
The connector uses default transformation maps to normalize imported data into the Qualys ETM schema.
Asset Transformation MapAsset Transformation Map
| Source Field | Target Field |
|---|---|
id |
asset.assetHeader.externalAssetId |
id |
asset.assetHeader.vendorAssetId |
type |
asset.assetHeader.assetTypeName |
operatingSystem |
asset.assetDetail.operatingSystem.name |
operatingSystemVersion |
asset.assetDetail.operatingSystem.version |
ipAddresses[] |
asset.assetDetail.network[].ipv4Addresses[ |
macAddress |
asset.assetDetail.network[].macAddress |
firstSeen |
sourceCreatedDate |
lastSeen |
sourceLastUpdatedDate |
firstSeen |
asset.assetDetail.openPorts[].firstFound |
displayTitle |
asset.assetDetail.hostname |
displayTitle |
asset.assetDetail.hostIdentity.hostname |
displayTitle |
asset.assetDetail.name |
model |
asset.assetDetail.hardware.model |
manufacturer |
asset.assetDetail.hardware.manufacturer |
accessSwitch |
asset.assetDetail.typedAttributes.& |
boundaries |
asset.assetDetail.typedAttributes.& |
businessImpact |
asset.assetDetail.typedAttributes.& |
category |
asset.assetDetail.typedAttributes.& |
dataSources |
asset.assetDetail.untypedAttributes.& |
ipv6 |
asset.assetDetail.untypedAttributes.& |
purdueLevel |
asset.assetDetail.typedAttributes.& |
riskLevel |
asset.assetDetail.typedAttributes.& |
Sensor |
asset.assetDetail.untypedAttributes.& |
site |
asset.assetDetail.untypedAttributes.& |
tags |
asset.assetDetail.untypedAttributes.& |
tier |
asset.assetDetail.typedAttributes.& |
userIds |
asset.assetDetail.untypedAttributes.& |
visibility |
asset.assetDetail.typedAttributes.& |
Vulnerability Transformation MapVulnerability Transformation Map
| Source Field | Target Field |
|---|---|
vulnerabilities.data.sample[].description |
findingGroup.findings[].description |
vulnerabilities.data.sample[].status |
findingGroup.findings[].findingStatus |
vulnerabilities.data.sample[].cveUid |
findingGroup.findings[].name |
vulnerabilities.data.sample[]. |
findingGroup.findings[].typeDetected |
vulnerabilities.data.sample[].id |
findingGroup.findings[].externalFindingId |
vulnerabilities.data.sample[]. |
findingGroup.findings[].detectionResult |
vulnerabilities.data.sample[]. |
findingGroup.findings[].findingType.v |
vulnerabilities.data.sample[].severity |
findingGroup.findings[].severity |
vulnerabilities.data.sample[].cveUid |
findingGroup.findings[].findingType. |
vulnerabilities.data.sample[]. |
findingGroup.findings[].firstFoundOn |
vulnerabilities.data.sample[]. |
findingGroup.findings[].lastFoundOn |