Amazon Inspector V2 Connector
The Amazon Inspector API Connector bridges AWS Inspector and Qualys ETM to consolidate vulnerability findings from your cloud infrastructure into a centralized risk management platform. By automatically pulling EC2 instance, ECR container images and Serverless Lamda functions and its vulnerabilities and deduplicating data through normalizing data formats and enriching findings with additional context, security teams gain unified visibility into their AWS security posture rather than managing assessments across separate tools. The connector calculates risk scores using TruRisk and enables faster remediation by combining cloud vulnerabilities with on-premises findings in one system. This integration transforms AWS vulnerability discovery from an isolated assessment into an actionable component of enterprise-wide threat and risk management.
This connector supports Amazon Inspector V2 only. Amazon Inspector Classic is not supported. AWS China regions and AWS GovCloud regions are not supported in the current implementation.
Connector Details
The following table provides a summary of what the Amazon Inspector V2 Connector supports.
|
Vendor |
Amazon Web Services (AWS) |
|
Product |
Amazon Inspector V2 |
|
Connector Category |
Vulnerability Management |
|
Asset Types Supported |
Cloud Resources |
|
Finding Supported |
Yes |
|
Supported Version & Type |
SaaS (Latest) — Amazon Inspector V2 only |
|
Integration Method |
API Integration (REST / AWS SDK) |
|
Direction |
Unidirectional (AWS Inspector V2 to Qualys ETM) |
|
Incremental Sync (Delta) |
Supported for Vulnerability Findings (ListFindings API); Not Supported for Assets |
|
Import of Installed Software |
Not Supported |
|
Import of Source Tags |
Not Supported |
|
Filters / Filter Query |
Not Supported |
|
Multi-Account (Organization Level) |
Not Supported |
|
Supported AWS Regions |
Standard AWS commercial regions only. AWS China and AWS GovCloud regions are not supported. |
Connection Settings
User Roles and Permissions
The connector uses IAM role-based authentication via AWS Secure Token Service (STS) AssumeRole. The IAM role must be configured in your AWS account and must include the following managed and inline policies depending on the asset types you intend to ingest.
| Entity Type | Permission Name | Permission Blob | Permission Type |
|
AWS EC2 Instances |
AmazonEC2ReadOnlyAccess |
- |
AWS Managed |
|
AWS Lambda |
AwsLambdaCustomReadAccess |
Lambda PermissionsLambda Permissions { "Version": "2012-10-17", "Statement": [ { "Sid": "VisualEditor0", "Effect": "Allow", "Action": [ "lambda:GetDurableExecutionState", "lambda:ListVersionsByFunction", "lambda:GetLayerVersion", "lambda:ListCapacityProviders", "lambda:GetAccountSettings", "lambda:GetFunctionConfiguration", "lambda:ListFunctionVersionsByCapacityProvider", "lambda:GetLayerVersionPolicy", "lambda:GetCapacityProvider", "lambda:ListProvisionedConcurrencyConfigs", "lambda:GetProvisionedConcurrencyConfig", "lambda:ListTags", "lambda:GetRuntimeManagementConfig", "lambda:GetDurableExecutionHistory", "lambda:ListLayerVersions", "lambda:ListLayers", "lambda:ListCodeSigningConfigs", "lambda:GetAlias", "lambda:ListFunctions", "lambda:GetEventSourceMapping", "lambda:GetFunction", "lambda:GetFunctionRecursionConfig", "lambda:ListAliases", "lambda:GetFunctionScalingConfig", "lambda:GetFunctionUrlConfig", "lambda:ListFunctionUrlConfigs", "lambda:GetFunctionCodeSigningConfig", "lambda:ListDurableExecutionsByFunction", "lambda:ListFunctionEventInvokeConfigs", "lambda:ListFunctionsByCodeSigningConfig", "lambda:GetFunctionConcurrency", "lambda:GetFunctionEventInvokeConfig", "lambda:ListEventSourceMappings", "lambda:GetDurableExecution", "lambda:GetCodeSigningConfig", "lambda:GetPolicy" ], "Resource": "*" } ] } |
Customer inline |
|
AWS ECR |
AwsEcrCustomReadAccess |
ECR PermissionsECR Permissions { "Version": "2012-10-17", "Statement": [ { "Sid": "VisualEditor0", "Effect": "Allow", "Action": [ "ecr:DescribeImageReplicationStatus", "ecr:DescribeImageSigningStatus", "ecr:DescribeRepositoryCreationTemplates", "ecr:GetSigningConfiguration", "ecr:ListTagsForResource", "ecr:ListImages", "ecr:BatchGetRepositoryScanningConfiguration", "ecr:GetRegistryScanningConfiguration", "ecr:DescribeRepositories", "ecr:BatchCheckLayerAvailability", "ecr:GetLifecyclePolicy", "ecr:GetRegistryPolicy", "ecr:ListPullTimeUpdateExclusions", "ecr:DescribeImageScanFindings", "ecr:GetLifecyclePolicyPreview", "ecr:DescribeRegistry", "ecr:GetDownloadUrlForLayer", "ecr:DescribePullThroughCacheRules", "ecr:GetAuthorizationToken", "ecr:ValidatePullThroughCacheRule", "ecr:GetAccountSetting", "ecr:BatchGetImage", "ecr:DescribeImages", "ecr:GetImageCopyStatus", "ecr:GetRepositoryPolicy" ], "Resource": "*" } ] } In case with above set permissions for ECR, if ECR related data is not fetched add below custom permissions as well by creating new custom Permission policy Permission Name: AwsEcsCustomReadAccess ECS PermissionsECS Permissions { "Version": "2012-10-17", "Statement": [ { "Sid": "VisualEditor0", "Effect": "Allow", "Action": [ "ecs:ListServicesByNamespace", "ecs:GetTaskProtection", "ecs:DescribeExpressGatewayService", "ecs:ListAttributes", "ecs:ListServiceDeployments", "ecs:DescribeTaskSets", "ecs:DescribeTaskDefinition", "ecs:DescribeClusters", "ecs:ListServices", "ecs:ListAccountSettings", "ecs:DescribeCapacityProviders", "ecs:ListTagsForResource", "ecs:ListTasks", "ecs:ListTaskDefinitionFamilies", "ecs:DescribeServiceDeployments", "ecs:DescribeServiceRevisions", "ecs:DescribeServices", "ecs:ListContainerInstances", "ecs:DescribeContainerInstances", "ecs:DescribeTasks", "ecs:ListTaskDefinitions", "ecs:ListClusters" ], "Resource": "*" } ] } |
Customer inline |
|
VulnerabilityFindings |
AmazonInspector2ReadOnlyAccess |
- |
AWS Manage |
To allow the connector to assume the role, add the Qualys-provided AWS user account to the Trust Relationships of the IAM role and configure an External ID for additional security.
- Qualys Provided AWS User Account:
arn:aws:iam::178650962893:user/aws-connector - Base Account ID: 178650962893
Create a role and assign permissions
-
Log in to your organization's AWS Management Console as an administrator.
-
Navigate to the Identity and Access Management (IAM) dashboard.
-
From the IAM dashboard, click Roles, and then click Create role.
-
Choose AWS account for the Trusted entity type and click Next.
-
Search for and select the AmazonInspectorReadOnlyAccess permission from the list of permissions and click Next.
-
Assign a name and description and then click Create role.
-
Back on the Roles page, click the new role and copy the value in the ARN field.
If you do not have permissions to create IAM roles, contact your AWS administrator. Refer to AWS documentation for details.
Authentication Details
Provide the following credentials in the connector configuration screen:
| Name | Key | Type | Description |
|---|---|---|---|
| Default Region | defaultRegion |
String | The AWS region for the connector to use. If not specified, the AWS SDK default region is used. Refer to AWS Inspector supported regions. |
| Assume Role ARN | assumeRoleArn |
String | The Amazon Resource Name (ARN) of the IAM role the connector assumes when accessing AWS services. The role must have the required permissions and trust relationships configured. |
| External ID | externalId |
Encrypted | The External ID configured in the IAM role trust relationship for additional security. Provided by Qualys during connector setup. |
How to Get Prerequisites Data in AWS
Create a Role and Assign Permissions
- Log in to your AWS Management Console as an administrator.
- Navigate to Identity and Access Management (IAM).
- From the IAM dashboard, click Roles, then click Create role.
- Choose AWS account as the Trusted entity type and click Next.
- Search for and select AmazonInspector2ReadOnlyAccess from the permissions list and click Next.
- Assign a name and description, then click Create role.
- On the Roles page, open the new role and copy the ARN value. This is used as the
assumeRoleArnin the connector configuration.Display the partial Role ARN value only. Do not expose the full ARN in public-facing documentation.
- Attach any additional required policies (Lambda, ECR) as inline customer policies to the same role based on the asset types you are ingesting. Refer to the Permissions table above.
- Under the Trust relationships tab of the role, add the Qualys-provided AWS user account (
arn:aws:iam::178650962893:user/aws-connector) as a trusted principal and configure the External ID condition.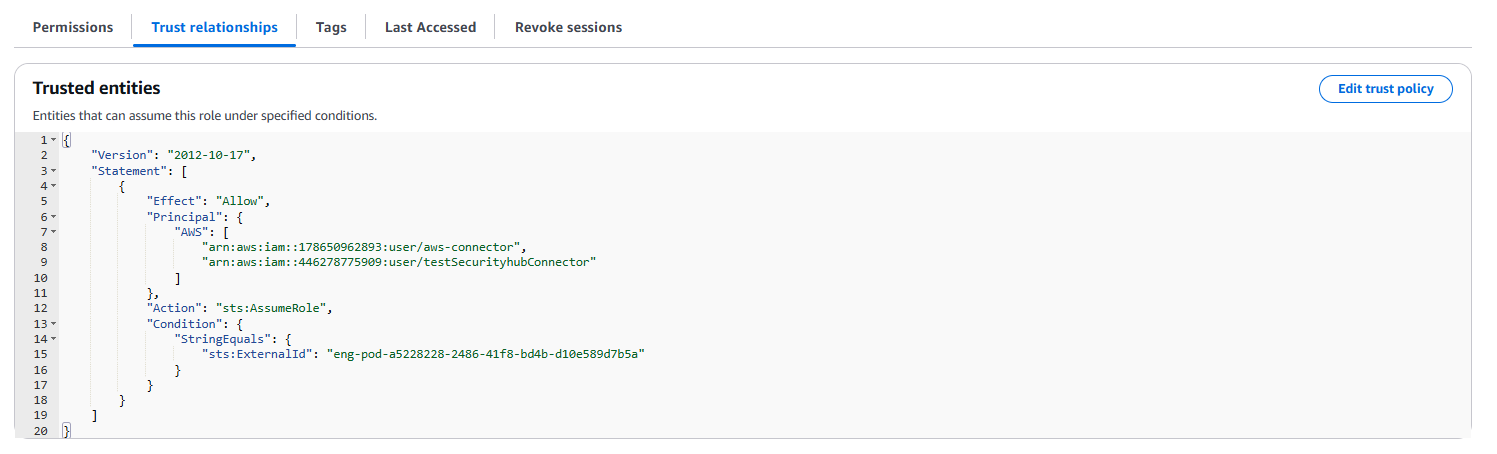
Connector Configuration
Basic Details
- Log in to Qualys ETM.
- Go to Connectors > Integration tab and locate the Amazon Inspector V2 Connector.
- Click Manage from the ellipsis menu.
- Provide a Name and Description for the connector.
- Select the supported findings type: Vulnerability / Host Asset.
- Enter the Default Region, Assume Role ARN, and External ID.
- Click Save to create the connector.
Mapping Details
Data Model
The Amazon Inspector V2 Connector provides out-of-the-box data model mappings for all four supported asset types, with or without associated vulnerabilities. The connector supports the following object-to-data-model relationships:
| Integration Type | Asset Type | Data Model |
|---|---|---|
| API Connector | Compute (EC2 Instance) | Asset and Vulnerability |
| API Connector | Serverless (Lambda Function) | Asset and Vulnerability |
| API Connector | Container Image (ECR) | Asset and Vulnerability |
| API Connector | Repository (ECR) | Asset only |
View the full data models in ETM to understand all supported and optional fields.
Transform Maps
Default transform maps are provided for each asset type. You can create new maps or clone existing ones to customize field transformations.
Data Model Mapping – AWS EC2 Instance (Asset Transformation)
| Source Field | Target Field |
|---|---|
instanceArnValue |
asset.assetHeader.externalAssetId (Required) |
instanceArnValue |
asset.assetHeader.vendorAssetId |
| EXPRESSION (CONSTANT: "aws-ec2-instance") | asset.assetHeader.assetTypeName |
| EXPRESSION (LOOKUP: state.name) | asset.assetHeader.status |
instanceId |
asset.assetDetail.name |
launchTime |
asset.assetDetail.sourceCreatedAt |
architecture |
asset.assetDetail.processor.name |
cpuOptions.coreCount |
asset.assetDetail.processor.numberOfCpu |
cpuOptions.coreCount |
asset.assetDetail.processor.coresPerSocket |
cpuOptions.threadsPerCore |
asset.assetDetail.processor.threadsPerCore |
platformDetails |
asset.assetDetail.operatingSystem.name |
platform |
asset.assetDetail.operatingSystem.publisher |
hypervisor |
asset.assetDetail.hardware.model |
instanceType |
asset.assetDetail.hardware.manufacturer |
placement.availabilityZone |
asset.assetDetail.cloudInfo.availabilityZone |
| EXPRESSION (CONSTANT: "AWS") | asset.assetDetail.cloudInfo.provider |
tags[].key |
asset.assetDetail.externalTags[].key |
tags[].value |
asset.assetDetail.externalTags[].value |
instanceArnValue |
asset.assetDetail.computeAssetClass.cloudInstance.id |
imageId |
asset.assetDetail.computeAssetClass.cloudInstance.imageId |
state.name |
asset.assetDetail.computeAssetClass.cloudInstance.state |
instanceType |
asset.assetDetail.computeAssetClass.cloudInstance.type |
instanceId |
asset.assetDetail.computeAssetClass.cloudInstance.hostname |
privateIpAddress |
asset.assetDetail.computeAssetClass.cloudInstance.privateIpv4Address |
publicIpAddress |
asset.assetDetail.computeAssetClass.cloudInstance.publicIpv4Address |
ipv6Address |
asset.assetDetail.computeAssetClass.cloudInstance.publicIpv6Address |
vpcId |
asset.assetDetail.computeAssetClass.cloudInstance.vpcId |
subnetId |
asset.assetDetail.computeAssetClass.cloudInstance.subnetId |
launchTime |
asset.assetDetail.computeAssetClass.cloudInstance.launchTime |
blockDeviceMappings[].ebs.volumeId |
asset.assetDetail.computeAssetClass.storage[].id |
blockDeviceMappings[].deviceName |
asset.assetDetail.computeAssetClass.storage[].name |
rootDeviceType |
asset.assetDetail.computeAssetClass.storage[].type |
launchTime |
asset.assetDetail.computeAssetClass.lastBoot |
networkInterfaces[].macAddress |
asset.assetDetail.network[].macAddress |
networkInterfaces[].privateDnsName |
asset.assetDetail.network[].privateDnsName |
networkInterfaces[].association.publicDnsName |
asset.assetDetail.network[].publicDnsName |
networkInterfaces[].privateIpAddress |
asset.assetDetail.network[].ipv4Addresses[] |
networkInterfaces[].association.publicIp |
asset.assetDetail.network[].publicIpv4Addresses[] |
networkInterfaces[].interfaceType |
asset.assetDetail.network[].type |
networkInterfaces[].association.carrierIp |
asset.assetDetail.network[].addresses[] |
instanceId |
asset.assetDetail.hostIdentity.hostname |
networkInterfaces[].privateDnsName |
asset.assetDetail.network[].hostname |
Data Model Mapping – AWS Lambda Serverless Function (Asset Transformation)
| Source Field | Target Field |
|---|---|
functionArn |
asset.assetHeader.externalAssetId (Required) |
functionArn |
asset.assetHeader.vendorAssetId |
| EXPRESSION (CONSTANT: "aws-lambda-function") | asset.assetHeader.assetTypeName |
| EXPRESSION (CONSTANT: "AWS") | asset.assetDetail.cloudInfo.provider |
| EXPRESSION (LOOKUP: state) | asset.assetHeader.status |
| EXPRESSION (LOOKUP: packageType) | asset.assetDetail.serverlessAssetClass.type |
functionName |
asset.assetDetail.name |
| EXPRESSION (DATE_FORMAT: lastModified) | asset.assetDetail.sourceUpdatedAt |
runtime |
asset.assetDetail.operatingSystem.name |
functionName |
asset.assetDetail.serverlessAssetClass.functionName |
handler |
asset.assetDetail.serverlessAssetClass.handler |
runtime |
asset.assetDetail.serverlessAssetClass.runtime |
codeSize |
asset.assetDetail.serverlessAssetClass.codeSizeInBytes |
environment.variables |
asset.assetDetail.serverlessAssetClass.environmentVariables |
memorySizeInBytes |
asset.assetDetail.serverlessAssetClass.memoryInBytes |
awsAccountId |
asset.assetDetail.cloudInfo.accountId |
functionRegion |
asset.assetDetail.cloudInfo.region |
Data Model Mapping – AWS ECR Repository (Asset Transformation)
| Source Field | Target Field |
|---|---|
repositoryArn |
asset.assetHeader.externalAssetId (Required) |
repositoryArn |
asset.assetHeader.vendorAssetId |
| EXPRESSION (CONSTANT: "binary-repository") | asset.assetHeader.assetTypeName |
| EXPRESSION (CONSTANT: "ACTIVE") | asset.assetHeader.status |
| EXPRESSION (CONSTANT: "BINARY") | asset.assetDetail.repositoryAssetClass.type |
repositoryName |
asset.assetDetail.name |
createdAt |
asset.assetDetail.sourceCreatedAt |
repositoryUri |
asset.assetDetail.repositoryAssetClass.repoUrl |
| EXPRESSION (CONSTANT: "PACKAGE") | asset.assetDetail.repositoryAssetClass.kind |
| EXPRESSION (CONSTANT: "PRIVATE") | asset.assetDetail.repositoryAssetClass.visibility |
| EXPRESSION (CONSTANT: "AWS") | asset.assetDetail.cloudInfo.provider |
awsAccountId |
asset.assetDetail.cloudInfo.accountId |
repositoryRegion |
asset.assetDetail.cloudInfo.region |
Data Model Mapping – AWS ECR Container Image (Asset Transformation)
| Source Field | Target Field |
|---|---|
imageDigest |
asset.assetHeader.externalAssetId (Required) |
imageDigest |
asset.assetHeader.vendorAssetId |
| EXPRESSION (CONSTANT: "container-image") | asset.assetHeader.assetTypeName |
| EXPRESSION (LOOKUP: imageStatus) | asset.assetHeader.status |
| EXPRESSION (CONSTANT: "AWS") | asset.assetDetail.cloudInfo.provider |
repositoryName |
asset.assetDetail.containerImageAssetClass.repository |
imageSizeInBytes |
asset.assetDetail.containerImageAssetClass.sizeInBytes |
imageDigest |
asset.assetDetail.containerImageAssetClass.digest |
imageTagsString |
asset.assetDetail.containerImageAssetClass.tag |
| EXPRESSION (CONSTANT: "IMAGE_DIGEST") | asset.assetDetail.containerImageAssetClass.digestType |
imageDigest |
asset.assetDetail.containerImageAssetClass.imageDigest |
imageName |
asset.assetDetail.name |
imageName |
asset.assetDetail.containerImageAssetClass.name |
imagePushedAt |
asset.assetDetail.untypedAttributes |
imageTags |
asset.assetDetail.untypedAttributes |
imageStatus |
asset.assetDetail.typedAttributes |
Data Model Mapping – AWS EC2 Vulnerability Transformation
| Source Field | Target Field |
|---|---|
resources.0.instanceArnValue |
asset.assetHeader.externalAssetId (Required) |
resources.0.instanceArnValue |
asset.assetHeader.vendorAssetId |
| EXPRESSION (CONSTANT: "aws-ec2-instance") | asset.assetHeader.assetTypeName |
| EXPRESSION (CONSTANT: "ACTIVE") | asset.assetHeader.status |
resources.0.id |
asset.assetDetail.name |
| EXPRESSION (CONSTANT: "AWS") | asset.assetDetail.cloudInfo.provider |
resources.0.region |
asset.assetDetail.cloudInfo.region |
resources.0.details.awsEc2Instance.ipV4Addresses[] |
asset.assetDetail.network[].ipv4Addresses[] |
resources.0.details.awsEc2Instance.ipV6Addresses[] |
asset.assetDetail.network[].ipv6Addresses[] |
resources.0.details.awsEc2Instance.imageId |
asset.assetDetail.computeAssetClass.cloudInstance.imageId |
resources.0.details.awsEc2Instance.type |
asset.assetDetail.computeAssetClass.cloudInstance.type |
resources.0.instanceArnValue |
asset.assetDetail.computeAssetClass.cloudInstance.id |
resources.0.id |
asset.assetDetail.computeAssetClass.cloudInstance.hostname |
resources.0.details.awsEc2Instance.vpcId |
asset.assetDetail.computeAssetClass.cloudInstance.vpcId |
resources.0.details.awsEc2Instance.subnetId |
asset.assetDetail.computeAssetClass.cloudInstance.subnetId |
resources.0.details.awsEc2Instance.launchedAt |
asset.assetDetail.computeAssetClass.cloudInstance.launchTime |
resources.0.details.awsEc2Instance.launchedAt |
asset.assetDetail.computeAssetClass.lastBoot |
resources.0.details.awsEc2Instance.ipV4Addresses.0 |
asset.assetDetail.computeAssetClass.cloudInstance.privateIpv4Address |
resources.0.details.awsEc2Instance.ipV6Addresses.0 |
asset.assetDetail.computeAssetClass.cloudInstance.privateIpv6Address |
resources.0.id |
asset.assetDetail.hostIdentity.hostname |
title |
findingGroup.findings[].name |
description |
findingGroup.findings[].description |
findingArn |
findingGroup.findings[].externalFindingId (Required) |
| EXPRESSION (LOOKUP: status) | findingGroup.findings[].findingStatus |
| EXPRESSION (LOOKUP: severity) | findingGroup.findings[].severity |
remediation.recommendation.text |
findingGroup.findings[].solutionRecommendation |
packageVulnerabilityDetails.referenceUrls[] |
findingGroup.findings[].references[] |
firstObservedAt |
findingGroup.findings[].firstFoundOn |
lastObservedAt |
findingGroup.findings[].lastFoundOn |
findingArn |
findingGroup.findings[].findingType.vulnerability.vendorId |
packageVulnerabilityDetails.vulnerabilityId |
findingGroup.findings[].findingType.vulnerability.cveId |
codeVulnerabilityDetails.cwes[] |
findingGroup.findings[].findingType.vulnerability.cweIds[] |
fixAvailable |
findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
exploitAvailable |
findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
inspectorScore |
findingGroup.findings[].sourceRiskScore |
severity |
findingGroup.findings[].sourceSeverity |
awsInspectorFindingUrl |
findingGroup.findings[].findingURL |
findingDetectionUrl |
findingGroup.findings[].findingDetectionURL |
Data Model Mapping – AWS Lambda Vulnerability Transformation
| Source Field | Target Field |
|---|---|
resources.0.id |
asset.assetHeader.externalAssetId (Required) |
resources.0.id |
asset.assetHeader.vendorAssetId |
| EXPRESSION (CONSTANT: "aws-lambda-function") | asset.assetHeader.assetTypeName |
| EXPRESSION (CONSTANT: "ACTIVE") | asset.assetHeader.status |
| EXPRESSION (CONSTANT: "AWS") | asset.assetDetail.cloudInfo.provider |
resources.0.region |
asset.assetDetail.cloudInfo.region |
resources.0.details.awsLambdaFunction.functionName |
asset.assetDetail.name |
resources.0.details.awsLambdaFunction.functionName |
asset.assetDetail.serverlessAssetClass.functionName |
resources.0.details.awsLambdaFunction.runtime |
asset.assetDetail.serverlessAssetClass.runtime |
| EXPRESSION (LOOKUP: packageType) | asset.assetDetail.serverlessAssetClass.type |
title |
findingGroup.findings[].name |
description |
findingGroup.findings[].description |
findingArn |
findingGroup.findings[].externalFindingId (Required) |
| EXPRESSION (LOOKUP: status) | findingGroup.findings[].findingStatus |
| EXPRESSION (LOOKUP: severity) | findingGroup.findings[].severity |
remediation.recommendation.text |
findingGroup.findings[].solutionRecommendation |
packageVulnerabilityDetails.referenceUrls[] |
findingGroup.findings[].references[] |
firstObservedAt |
findingGroup.findings[].firstFoundOn |
lastObservedAt |
findingGroup.findings[].lastFoundOn |
findingArn |
findingGroup.findings[].findingType.vulnerability.vendorId |
packageVulnerabilityDetails.vulnerabilityId |
findingGroup.findings[].findingType.vulnerability.cveId |
codeVulnerabilityDetails.cwes[] |
findingGroup.findings[].findingType.vulnerability.cweIds[] |
fixAvailable |
findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
exploitAvailable |
findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
inspectorScore |
findingGroup.findings[].sourceRiskScore |
severity |
findingGroup.findings[].sourceSeverity |
awsInspectorFindingUrl |
findingGroup.findings[].findingURL |
findingDetectionUrl |
findingGroup.findings[].findingDetectionURL |
Data Model Mapping – AWS ECR Container Image Vulnerability Transformation
| Source Field | Target Field |
|---|---|
resources.0.details.awsEcrContainerImage.imageHash |
asset.assetHeader.externalAssetId (Required) |
resources.0.details.awsEcrContainerImage.imageHash |
asset.assetHeader.vendorAssetId |
| EXPRESSION (CONSTANT: "container-image") | asset.assetHeader.assetTypeName |
| EXPRESSION (CONSTANT: "ACTIVE") | asset.assetHeader.status |
| EXPRESSION (CONSTANT: "AWS") | asset.assetDetail.cloudInfo.provider |
resources.0.region |
asset.assetDetail.cloudInfo.region |
resources.0.details.awsEcrContainerImage.repositoryName |
asset.assetDetail.containerImageAssetClass.repository |
resources.0.details.awsEcrContainerImage.imageHash |
asset.assetDetail.containerImageAssetClass.digest |
resources.0.details.awsEcrContainerImage.imageTagsString |
asset.assetDetail.containerImageAssetClass.tag |
| EXPRESSION (CONSTANT: "IMAGE_DIGEST") | asset.assetDetail.containerImageAssetClass.digestType |
resources.0.details.awsEcrContainerImage.imageHash |
asset.assetDetail.containerImageAssetClass.imageDigest |
resources.0.details.awsEcrContainerImage.architecture |
asset.assetDetail.containerImageAssetClass.architecture |
resources.0.details.awsEcrContainerImage.imageName |
asset.assetDetail.name |
resources.0.details.awsEcrContainerImage.imageName |
asset.assetDetail.containerImageAssetClass.name |
resources.0.details.awsEcrContainerImage.pushedAt |
asset.assetDetail.untypedAttributes |
resources.0.details.awsEcrContainerImage.imageTags |
asset.assetDetail.untypedAttributes |
title |
findingGroup.findings[].name |
description |
findingGroup.findings[].description |
findingArn |
findingGroup.findings[].externalFindingId (Required) |
| EXPRESSION (LOOKUP: status) | findingGroup.findings[].findingStatus |
| EXPRESSION (LOOKUP: severity) | findingGroup.findings[].severity |
remediation.recommendation.text |
findingGroup.findings[].solutionRecommendation |
packageVulnerabilityDetails.referenceUrls[] |
findingGroup.findings[].references[] |
firstObservedAt |
findingGroup.findings[].firstFoundOn |
lastObservedAt |
findingGroup.findings[].lastFoundOn |
findingArn |
findingGroup.findings[].findingType.vulnerability.vendorId |
packageVulnerabilityDetails.vulnerabilityId |
findingGroup.findings[].findingType.vulnerability.cveId |
codeVulnerabilityDetails.cwes[] |
findingGroup.findings[].findingType.vulnerability.cweIds[] |
fixAvailable |
findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
exploitAvailable |
findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
inspectorScore |
findingGroup.findings[].sourceRiskScore |
severity |
findingGroup.findings[].sourceSeverity |
awsInspectorFindingUrl |
findingGroup.findings[].findingURL |
findingDetectionUrl |
findingGroup.findings[].findingDetectionURL |
Profiles
Profiles control the execution schedule and transform map assignment for the connector.
- Click + to add a new profile.
- Provide a Name and Description.
- Select the required Transform Map.
- Set Status (Active or Inactive).
- Configure a Schedule: Single Occurrence or Recurring with start and end dates/times.
Identification Rules
Identification Rules are provided out-of-the-box by Qualys CSAM. They control how vulnerability findings are matched to assets during ingestion. At least one rule must be active. You may proceed without modification in most environments, but review active rules to confirm they align with your asset identification strategy for cloud workloads.
How Does a Connection Work?
The Amazon Inspector V2 Connector executes on schedule (based on the configured profile) or on demand. On each run, it authenticates to AWS via STS AssumeRole using the configured ARN and External ID, then calls the AWS Inspector V2 and EC2 APIs to retrieve assets and findings. Data is mapped through the configured transform map and imported into ETM.
The following APIs are called during execution:
|
Entity type |
API / Operation |
Pagination |
Max PageSize |
Delta |
Default Filter |
Rate Limit |
Caching Needed |
|---|---|---|---|---|---|---|---|
|
Compute |
DescribeInstances |
Yes |
1000 |
No |
No |
NA |
No |
|
Serverless |
ListFunctions |
Yes |
50 |
No |
No |
NA |
No |
|
Repository |
DescribeRepositories |
Yes |
1000 |
No |
No |
NA |
No |
|
Container Images |
DescribeImages |
Yes |
1000 |
No |
No |
NA |
No |
|
Vulnerabilities (In Amazon Inspector term : Findings) |
ListFindings |
Yes |
100 |
Yes |
AWS_EC2_INSTANCE, AWS_ECR_CONTAINER_IMAGE, AWS_ECR_REPOSITORY, AWS_LAMBDA_FUNCTION |
NA |
No |
The ListFunctions API is limited to 50 results per call by AWS. The connector handles pagination automatically to retrieve all Lambda functions.
The connector state transitions from Registered to Scheduled, then Processing, and finally Processed upon successful completion. The connector state is visible in the Connectors screen in ETM.
Viewing Assets and Findings in ETM
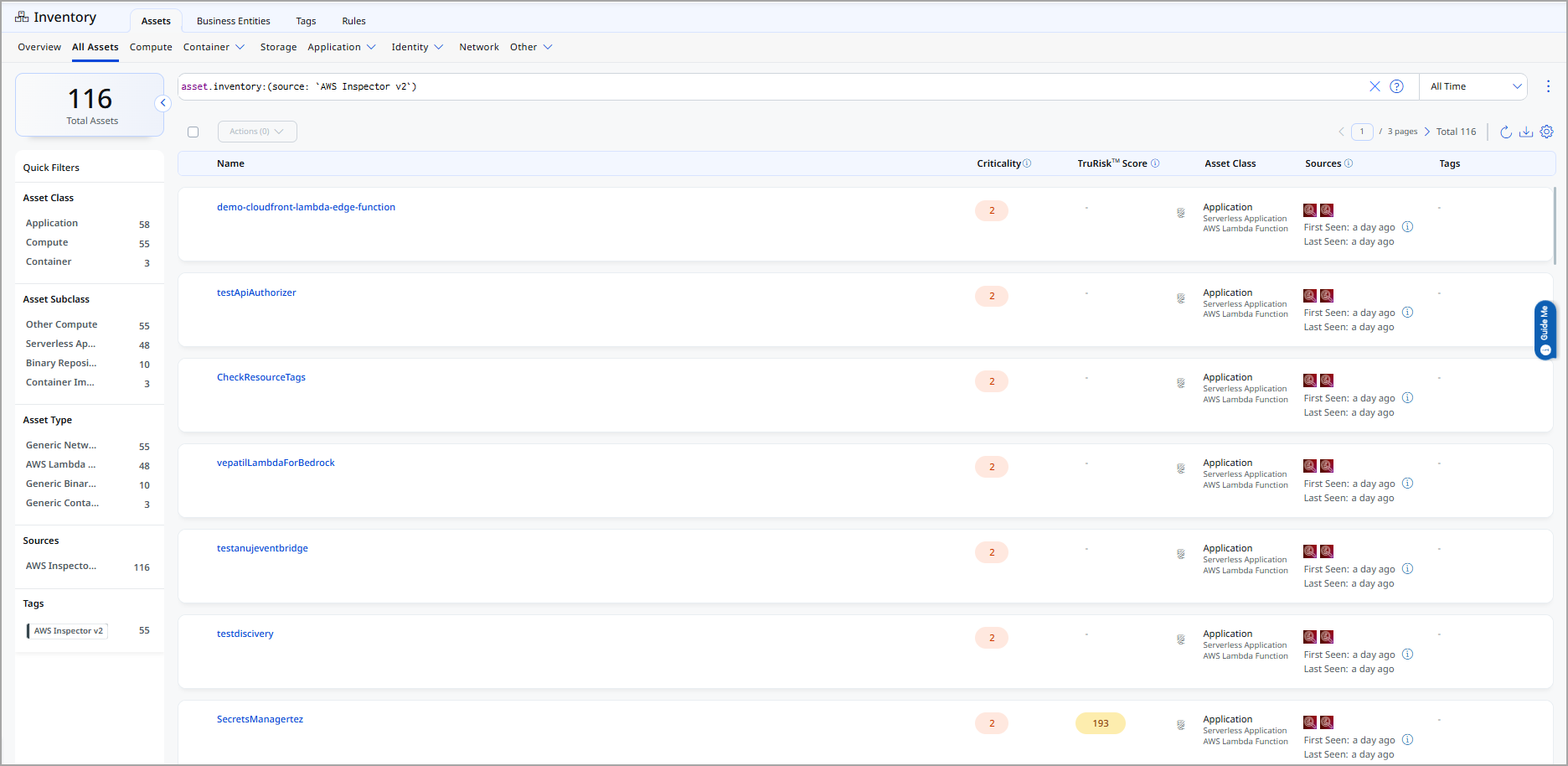
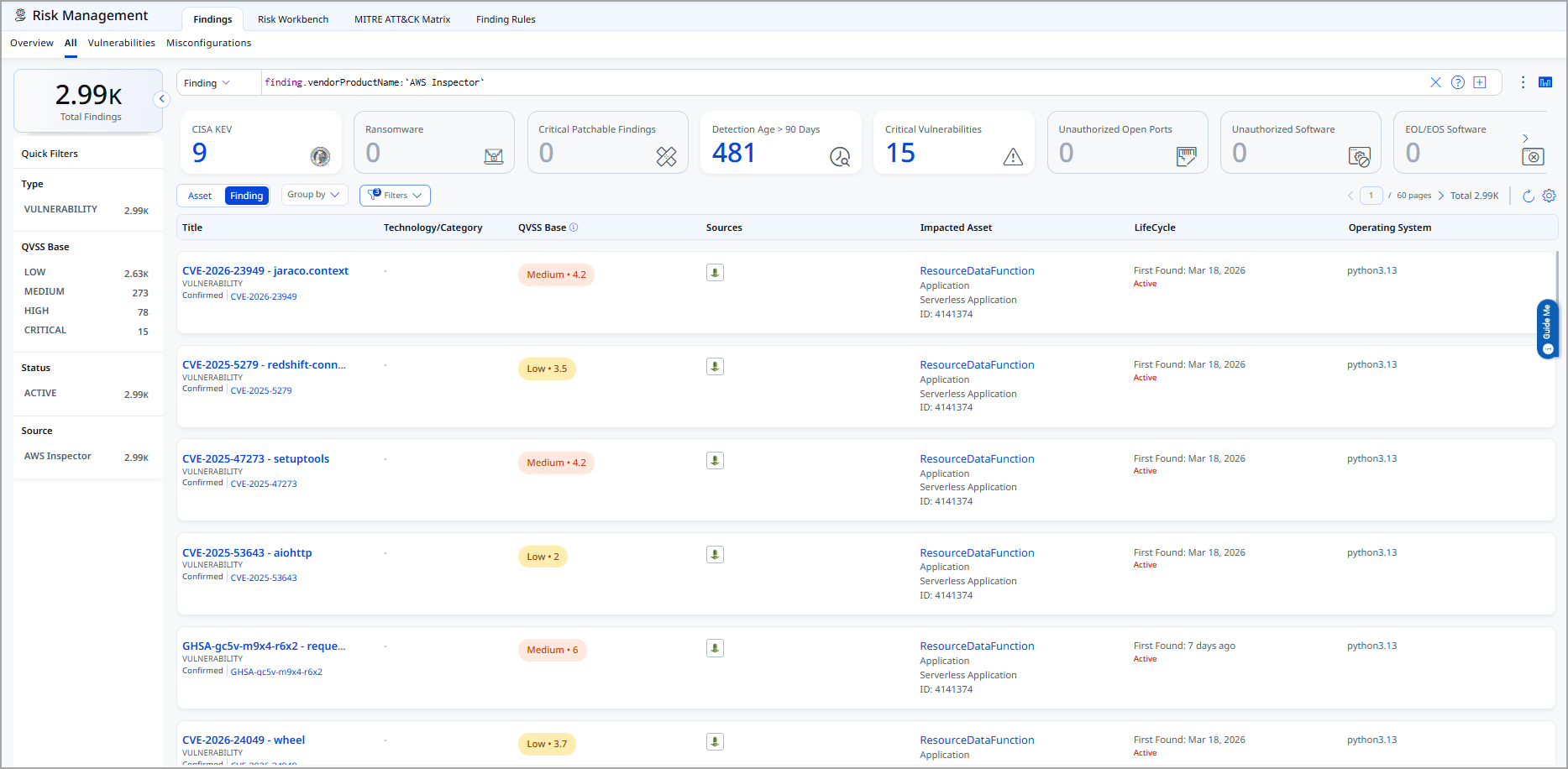
After a successful connector run, Amazon Inspector V2 assets and findings appear in ETM:
- Assets: Go to Inventory > Assets > Host. Filter with
tags.name:"AWS Inspector".
- Findings: Go to Risk Management > Findings > Vulnerability. Filter with
finding.vendorProductName:"Amazon Inspector".
API Endpoint
The connector does not use REST APIs to fetch the assets or findings from Amazon Inspector. Instead. Instead, the Amazon Inspector connector uses the AWS SDK version 2.42.4.
Assumptions and Limitations
- This connector supports Amazon Inspector V2 only. Amazon Inspector Classic is not supported.
- AWS China regions and AWS GovCloud regions are not supported.
- Organization-level multi-account setup is not supported in the current implementation.
- The
ListFunctionsAPI supports a maximum of 50 functions per call. Paginated calls retrieve all available functions automatically. - Delta poll/fetch support is available only for the
ListFindingsAPI (vulnerability ingestion). Asset ingestion performs a full pull on each run. - For ECR scanning, AWS Inspector V2 can only scan container images stored in AWS ECR private registries and repositories. Public registries are not supported. See AWS documentation on ECR scanning.