Black Duck SCA
The Black Duck SCA Connector bridges code repository security data into Qualys Enterprise TruRisk Management by automatically importing projects, components, and vulnerability findings from Black Duck.
This integration enables security teams to consolidate risk visibility across their software supply chain and development assets rather than managing separate vendor platforms. By ingesting code repository findings alongside other enterprise risk data, teams gain the unified prioritization and remediation tracking needed to address vulnerabilities in their codebase within their broader risk management workflow.
The connector performs full data pulls on a scheduled basis, allowing organizations to maintain current visibility into code-level security issues as part of their comprehensive risk management program.
Connector details
The following table provides a high-level overview of the Black Duck SCA connector.
| Vendor | Synopsys |
| Product name | Blackduck SCA |
| Category | Assets (Code Repo) |
| Findings supported | Code repository findings and vulnerabilities |
| Assets supported | Code Repository |
| Version | 1.0.0 |
| Integration type | API Integration (REST) |
| Direction | Unidirectional (Black Duck > Qualys) |
| Delta support | Not supported (Full pull on each execution) |
Connection settings
Authentication details
Provide the values below in the connector configuration screen in ETM.
| Name | Key | Type | Description / Example |
|---|---|---|---|
| BASE URL | baseURL |
String | Base URL of Black Duck SCA. Example: https://blackduck.intranet.qualys.com |
| API TOKEN | api_token |
Encrypted string | API token created from a Black Duck user profile |
Setting up an API token in Black Duck
- Log in to your Black Duck instance.
- Open the User Menu.
- Click My Profile. Near the center of the page is an option to create a user access token.
- Type a descriptive name in the Name field.
- Select the access level required: Read Access and/or Write Access.
- Click Generate. The API token appears in a pop-up window. This is the only time the token is shown. Store it securely.
- Click Copy in the pop-up to copy the token, then paste it into a secure store or the ETM connector configuration.
- In ETM, configure the connector with the Black Duck base URL and the API token.
Required permissions
Ensure the token has the permissions below so the connector can read vulnerability data from Black Duck.
| Entity type | Permissions |
|---|---|
| VulnerabilityFindings | read: vulnerabilities |
API endpoints
Here are the APIs executed for the Black Duck connection.
| Name | Endpoint | Notes / Example |
|---|---|---|
| Authorization API | https://<baseURL>/api/tokens/authenticate |
Authenticate using the API token (Bearer token). |
| Get Projects | https://<baseURL>/api/projects |
Fetch list of projects available in the Black Duck instance. |
| Get Project Versions | https://<baseURL>/api/projects/<project-reference>/versions |
Replace <project-reference> with the project UUID; example: xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx. |
| Get Vulnerabilities (per project version) | https://<baseURL>/api/projects/<project-reference>/versions/<projectVersion-reference> |
Replace <projectVersion-reference> with the version UUID. |
Configure Black Duck SCA connector
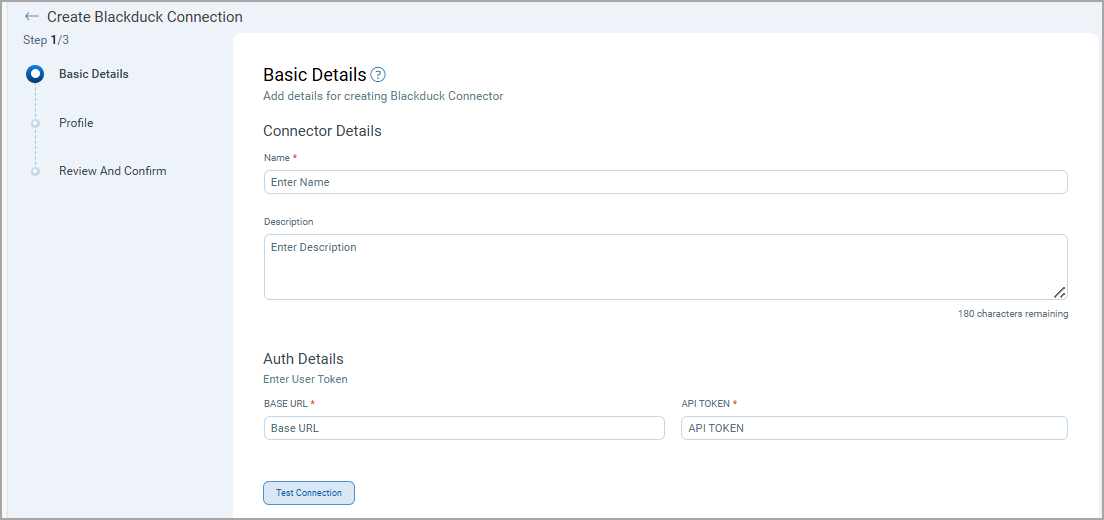
Basic details
When creating the connector provide:
- Connector Name and Description
- Authentication details: Base URL and API Token
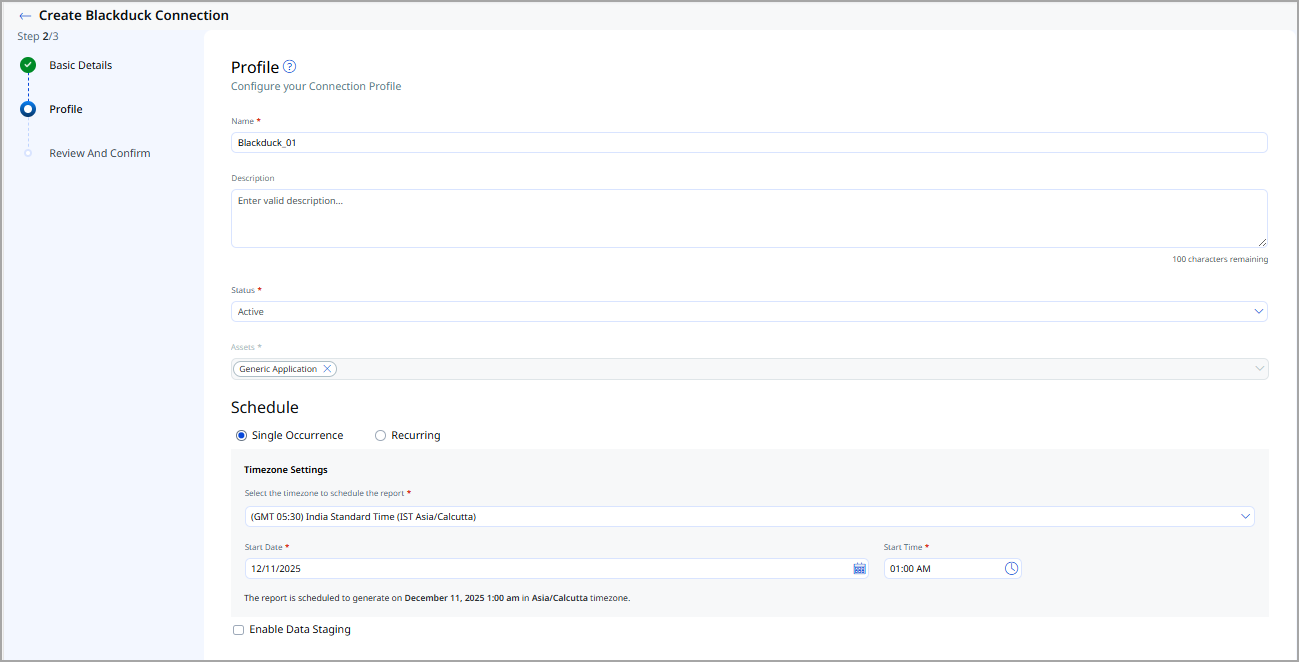
Profiles
Profiles control execution. Create a profile to define what the connector imports and when it runs.
- Log in to Qualys ETM.
- Navigate to Connectors > Integration and locate the Black Duck SCA Connector.
- Click + to create a new profile.
- Provide a Name and Description.
- Select the required Transform Map.
- Set Status to Active or Inactive.
- Configure a Schedule: Single Occurrence or Recurring (provide start and end date/time).
- Click Next and then Create to register the profile.
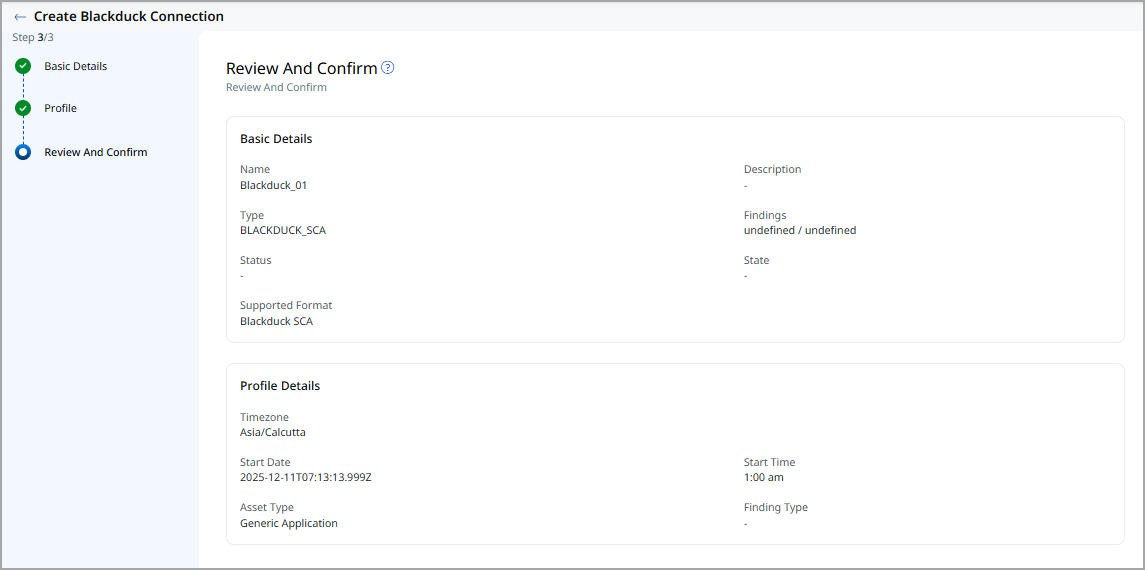
Review and confirm
- Review the connection and profile settings.
- Click Create to complete creation and register the connector in ETM.
How Does the Connection Work?
On schedule (or on demand), the connector fetches Black Duck findings and imports them into ETM. The connector performs a full pull on each execution; profiles control which data is synchronized and when. Imported data is mapped to ETM's data model using the transform map assigned to the profile.
Connector States
After creation the connector proceeds through these states in ETM:
| State | Description |
|---|---|
| Registered | The connector is created and registered to fetch vendor data. |
| Scheduled | The connector has a scheduled profile to execute a connection with the vendor. |
| Processing | A connection is executing and the connector is fetching assets and findings data. |
| Processed | The connector has successfully fetched assets; it may still be importing findings. Processed indicates configuration succeeded and import is underway or complete. |
The findings import process can take time depending on volume. The entire import (assets + findings) may take up to 2 hours. After completion, imported assets and findings are available in Enterprise TruRisk Management (ETM).
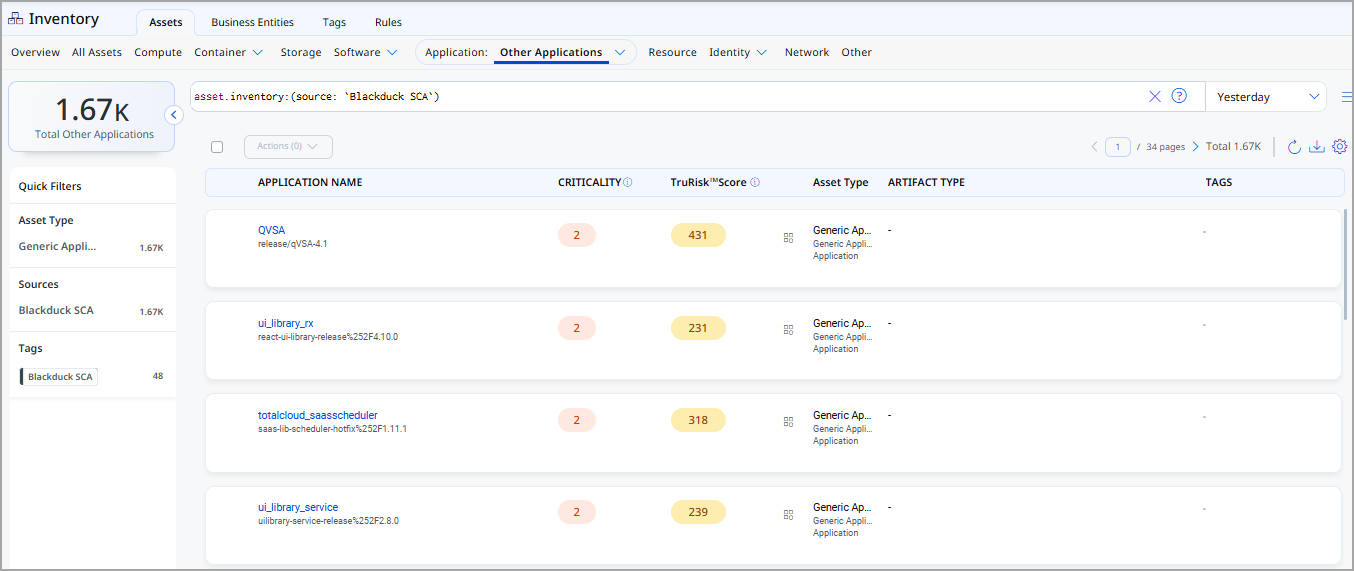
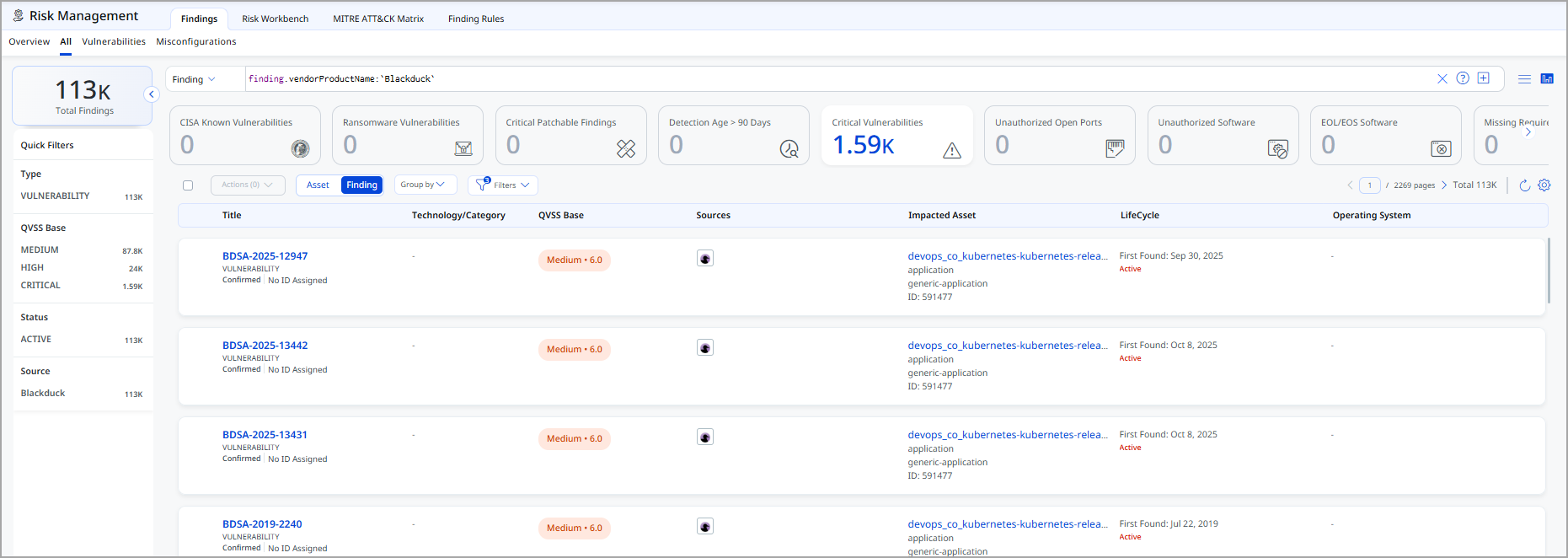
Viewing assets and findings in ETM
- Assets - Navigate to Enterprise TruRisk Management > Inventory > Assets > Application > Other Applications. Use the asset filter
asset.inventory: (source: 'BlackDuck SCA')to narrow results.
- Findings - Risk Management > Findings > Vulnerability. Use the vendor filter:
finding.vendorProductName:'Blackduck'.
Mapping details
The default transformation map is used during profile execution to transform Black Duck source fields into ETM target fields. The table below lists the primary source > target mappings.
| Source field | Target field |
|---|---|
versionName |
name |
versionName |
externalAssetId |
versionName |
vendorAssetId |
createdAt |
sourceCreatedAt |
projectGroup |
repoUrl |
settingUpdatedAt |
sourceUpdatedAt |
vulnerabilities[].vulnerabilityWithRemediation.vulnerabilityName |
findings[].name |
vulnerabilities[].vulnerabilityWithRemediation.description |
findings[].description |
vulnerabilities[].vulnerabilityWithRemediation.vulnerabilityPublishedDate |
findings[].firstFoundOn |
vulnerabilities[].vulnerabilityWithRemediation.vulnerabilityUpdatedDate |
findings[].lastFoundOn |
vulnerabilities[].vulnerabilityWithRemediation.cweId |
findings[].findingType.vulnerability.cweId |
vulnerabilities[].vulnerabilityWithRemediation.severity |
findings[].severity |
vulnerabilities[].vulnerabilityWithRemediation.vulnerabilityName |
findings[].findingType.vulnerability.cveId |
source |
findings[].subCategory |