Checkmarx One SCA
The Checkmarx One SCA connector brings open source vulnerability findings from Checkmarx into Qualys Enterprise TruRisk Management, enabling organizations to centralize these findings in ETM for risk visualization, prioritization, and remediation efforts.
By automatically ingesting software composition analysis data alongside other security findings, teams gain a unified view of vulnerabilities across their code repositories and can make more informed decisions about which risks to address first.
This integration matters because unmanaged open source dependencies represent a significant attack surface that most enterprises struggle to track, and consolidating these insights with other risk data helps security teams allocate remediation resources more effectively.
Connector Details
|
Vendor |
Checkmarx |
|
Product Name |
CheckmarxOne SCA |
|
Category |
Application Security |
|
Findings Supported |
Yes |
|
Assets Supported |
Code Repository |
|
Version |
1.0.0 |
|
Integration Type |
API Integration (REST) |
|
Direction |
Unidirectional |
|
Delta Support |
Not Supported |
Authentication
|
Checkmarx Region |
checkmarxRegion |
String |
Example: deu |
|
Tenant Name |
tenantName |
String |
Tenant ID for the user profile. |
|
API Key |
api_key |
String |
API Key for the user profile |
Setting Up API Key
Reference: Creating OAuth Clients – Checkmarx Docs
- Log in to your Checkmarx One environment (choose the appropriate server base URL).
Checkmarx One Server Base URLs:
-
- US Environment - https://ast.checkmarx.net
- US2 Environment - https://us.ast.checkmarx.net
- EU Environment - https://eu.ast.checkmarx.net
- EU2 Environment - https://eu-2.ast.checkmarx.net
- DEU Environment - https://deu.ast.checkmarx.net
- Australia & New Zealand – https://anz.ast.checkmarx.net
- India - https://ind.ast.checkmarx.net
- Singapore - https://sng.ast.checkmarx.net
- UAE - https://mea.ast.checkmarx.net
- Israel (gov) - https://gov-il.ast.checkmarx.net
2. Navigate to Settings > Identity and Access Management.
3. In the main navigation, click API Keys > Create Key.
4. Configure the API Key with an optional Note description, the expiration period of the key, and the notification email(s).
5. Click Create and copy the API Key. Store it securely for later use.
Required Permissions:
|
Entity Type |
Permissions |
|---|---|
|
VulnerabilityFindings |
read: vulnerabilities |
API Endpoints
Here are the APIs executed for the Checkmarx SCA connection.
|
Authorization API |
https://<domain>.checkmarx.net/auth/realms/ |
Grant Type: client_credentials |
|
Fetch Projects |
https://<domain>api/projects/?limit=10&offset=0 |
Example Domain: deu.ast |
|
Fetch Last Scan |
https://<domain>.checkmarx.net/api/projects/last-scan?scan-status=Completed&project-ids=<projectId>&engine=sca |
Example Project ID: xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx |
|
Fetch Scan Details |
https://<domain>.checkmarx.net/api/results/?scan-id=<scanId>&limit=5000&offset=0 |
Example Scan ID: xxxxxxxx-xxxx-xxxx-xxxx- |
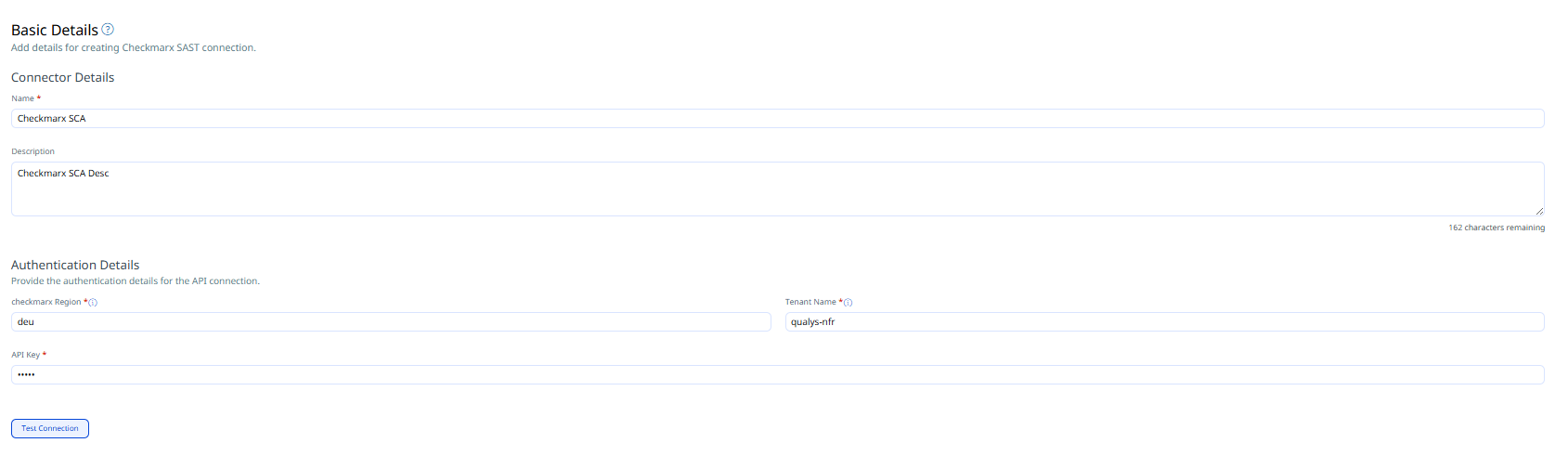
Configure Checkmarx SCA Connector
Basic Details
Provide the following details
- Connector Name and Description
- Authentication details (Checkmarx region, Tenant Name, API Key)
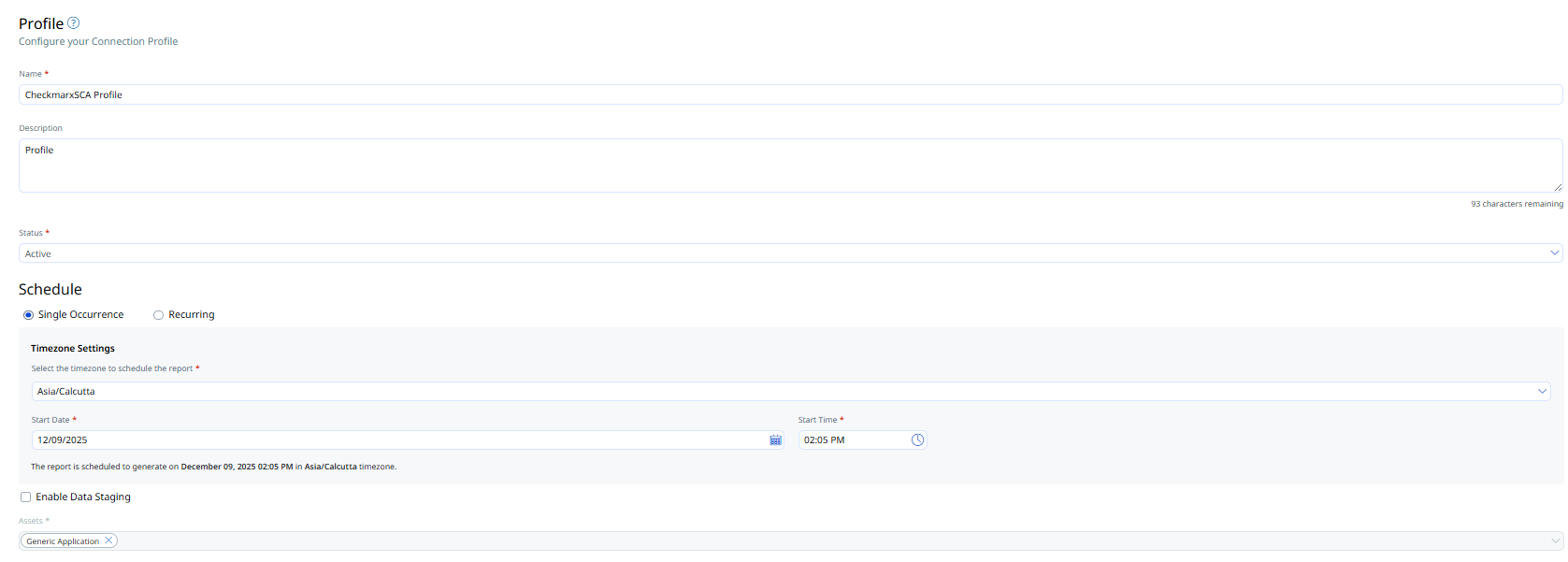
Profile
Profiles control the execution of the connector.
- Provide a Name and Description.
- Set Status (Active or Inactive).
- Configure a Schedule: Single Occurrence or Recurring with start and end dates/times.
- Assets value will be Generic Application by default for the Checkmarx SCA connector
- Click Next.
How Does the Connection Work?
On schedule (or on-demand), the connector fetches Checkmarx One findings and imports them into ETM. Profiles define what is synchronized and when. The Checkmarx SCA connector performs a full pull on each execution.
In the Connector screen, you can find your newly configured connector listed and marked in the Processed state.
Connector States
A successfully configured connector goes through 4 states.
- Registered - The connector is successfully created and registered to fetch data from the vendor.
- Scheduled - The connector is scheduled to execute a connection with the vendor.
- Processing - A connection is executed and the connector is fetching the asset and findings data.
- Processed - The connector has successfully fetched the assets, it may still be under process of fetching the findings. Wait for some more time for the connector to fetch the findings completely.
The Processed state indicates that the Connector is successfully configured but it is under the process of importing all your assets and findings. This process (specifically for findings) may take some time.
This entire process may take up to 2 hours for completion. Once it is done, you can find the imported data in Enterprise TruRisk Management (ETM).
Viewing Assets and Findings in ETM
- Navigate to Enterprise TruRisk Management > Inventory.
- Go to Assets > Applications > Other Applications to view imported Checkmarx applications.
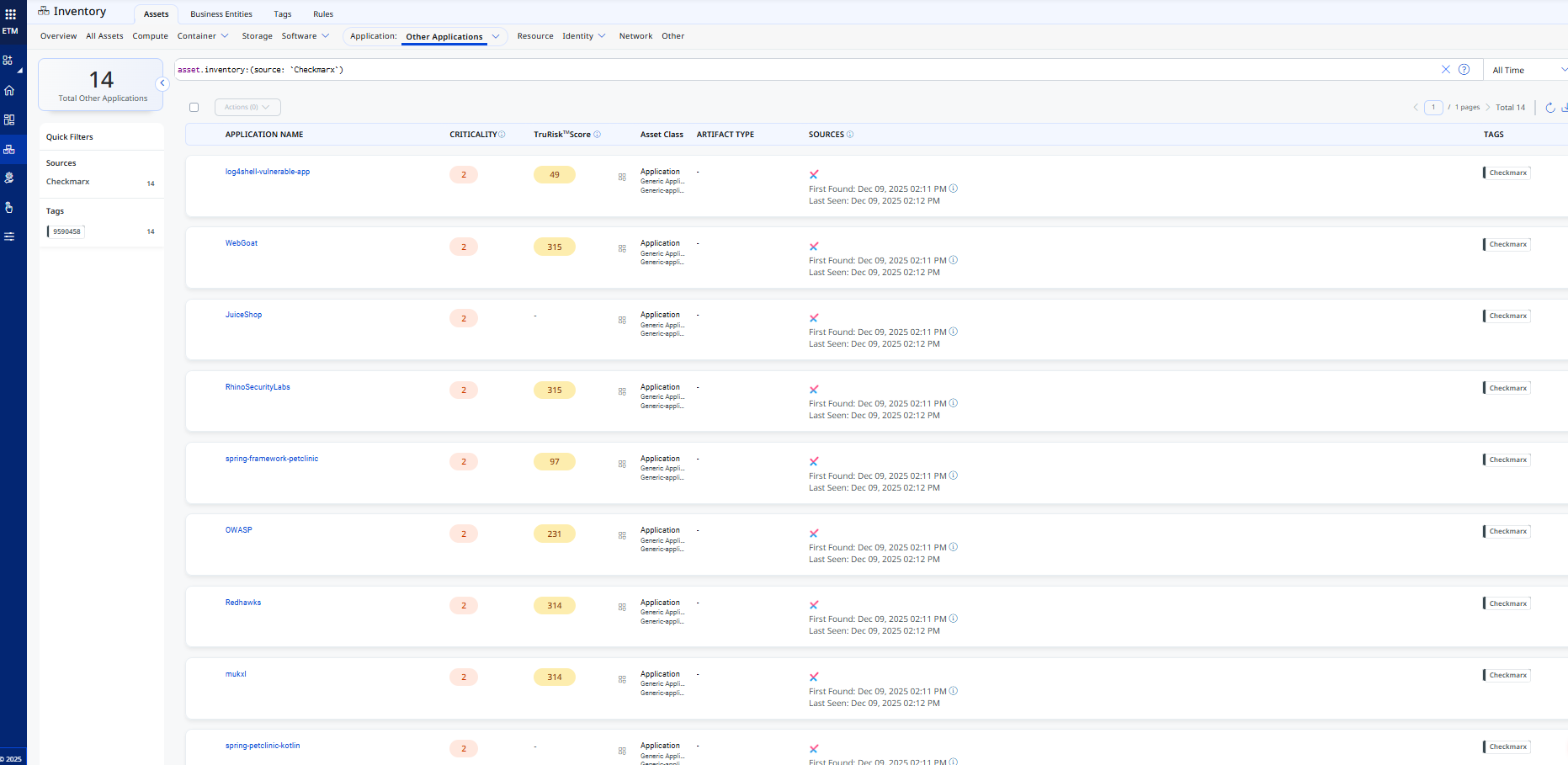
- Go to Assets > Applications > Other Applications to view imported Checkmarx applications.
- Navigate to Risk Management > Findings > Vulnerability.
- Use filter: finding.vendorProductName:"Checkmarx" to list Checkmarx findings.
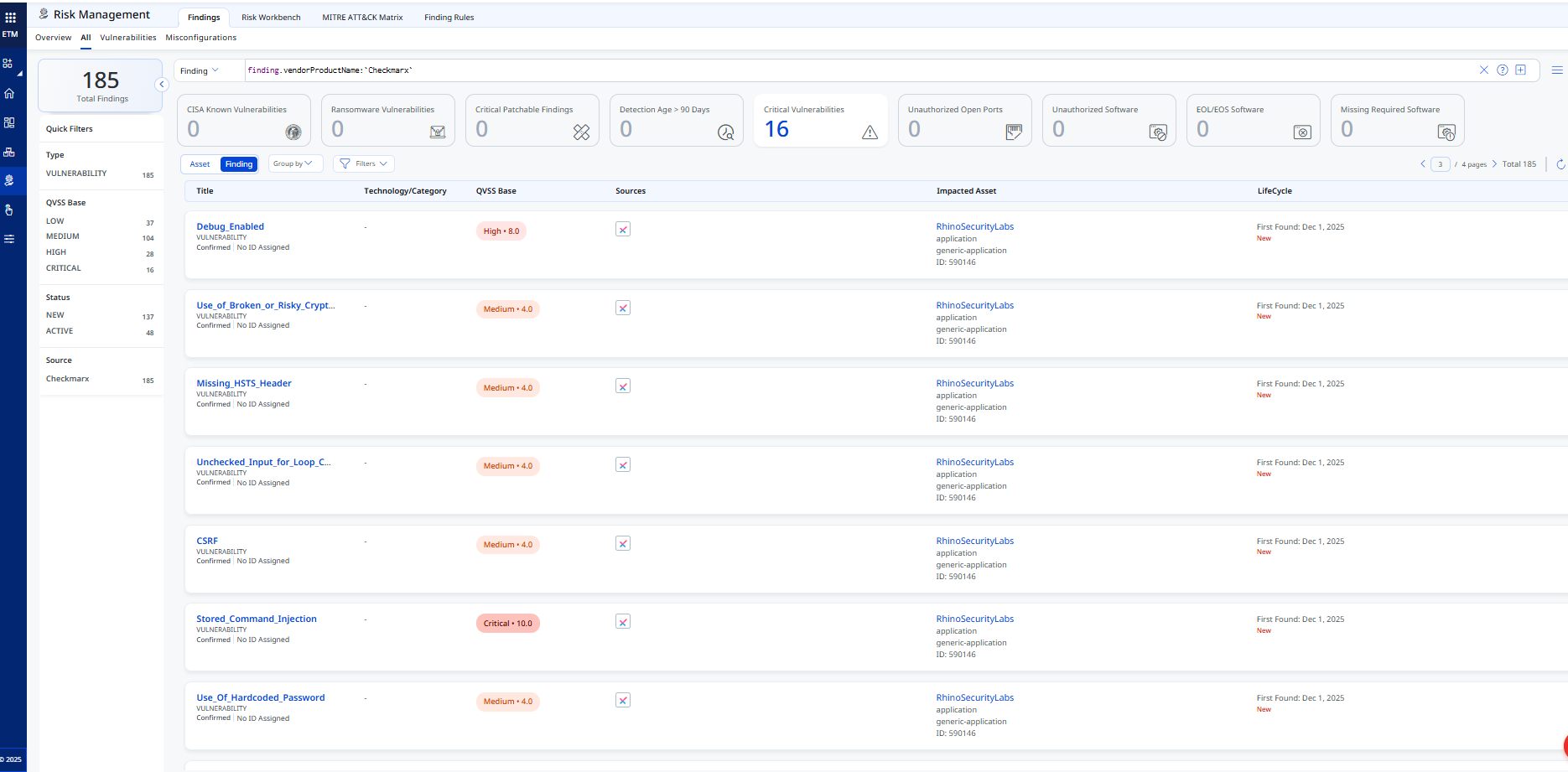
- Use filter: finding.vendorProductName:"Checkmarx" to list Checkmarx findings.
Activating Web Applications in WAS
Assets (Code Repositories) synced from the Checkmarx SAST Connector appear in:
- ETM
- CSAM
- WAS
By default, these applications are not activated for scanning in WAS.
To activate web applications in WAS
- Navigate to CSAM > Web Applications.
- Select the desired web application.
- Choose Quick Actions > Activate WAS.
- Activating web applications will consume WAS licenses. You should activate only the required applications.
- This connector fetches the latest scans for the Web Applications.
Checkmarx SCA Transformation Map:
The default transformation map configured for the Checkmarx SCA connector is fetched from the database and utilized during the execution of the connector profile to perform data transformation.
|
findings[].vulnerabilityDetails.cveName |
cveId |
|
repoUrl |
repoUrl |
|
createdAt |
sourceCreatedAt |
|
name |
assetDetail.name |
|
id |
externalAssetId |
|
id |
vendorAssetId |
|
findings[].type |
findings[].subCategory |
|
findings[].id |
findings[].externalFindingId |
|
findings[].status |
findings[].findingStatus |
|
findings[].severity |
findings[].severity |
|
findings[].firstFoundAt |
findings[].firstFoundOn |
|
findings[].foundAt |
findings[].lastFoundOn |
|
findings[].description |
findings[].description |
|
findings[].data.queryName |
findings[].name |
|
findings[].vulnerabilityDetails.cweId |
cweId |