Cortex XDR
The Cortex XDR Connector ingests endpoint asset and vulnerability data from Palo Alto Networks Cortex XDR into Qualys Enterprise TruRisk Management (ETM). This integration enables security teams to correlate endpoint vulnerabilities with other enterprise findings, improving visibility and prioritization across the attack surface.
Connector Details
High-level details for the Cortex XDR Vulnerability connector.
| Vendor | Palo Alto Networks |
| Product | Cortex XDR |
| Connector Category | Endpoint Security |
| Asset Types Supported | Host Assets (Compute) |
| Finding Supported | Yes |
| Version | 1.0.0 |
| Integration Type | API Integration (REST) |
| Direction | Unidirectional (Cortex XDR to Qualys) |
| Incremental Sync (Delta) |
Not Supported |
|
Import of Installed Software |
Not Supported |
|
Import of Source Tags |
Not Supported |
|
Filters / Filter Query |
Not Supported |
Connection Settings
User Roles and Permissions
Ensure the following requirements are met when generating API credentials in Cortex XDR:
- API Key role must be Viewer (read-only access).
- Security Level should be Standard.
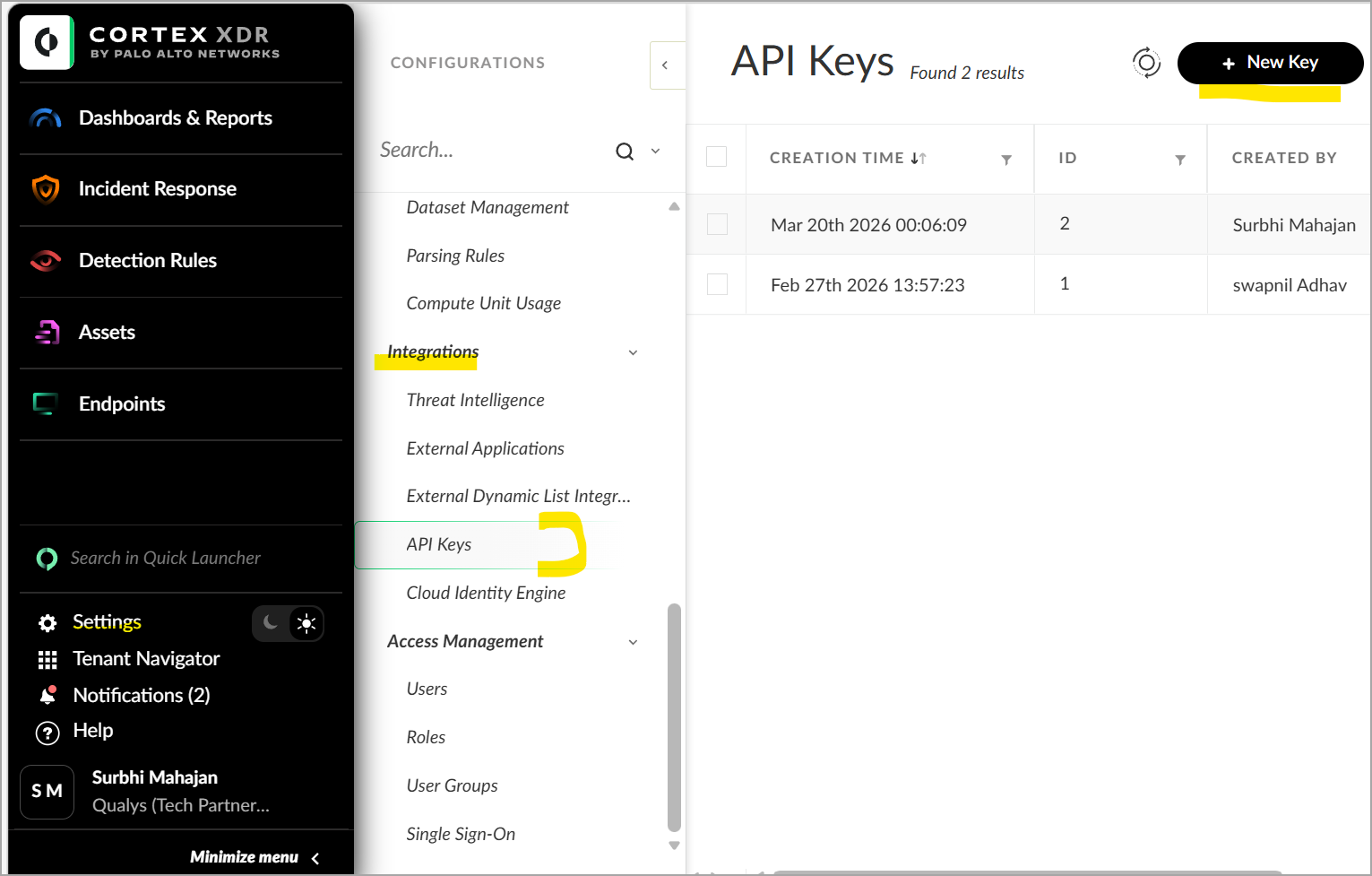
To generate API keys:
- Navigate to Settings > Configurations > Integrations > API Keys.
- Click + New Key.
- Select Standard or Advanced security level.
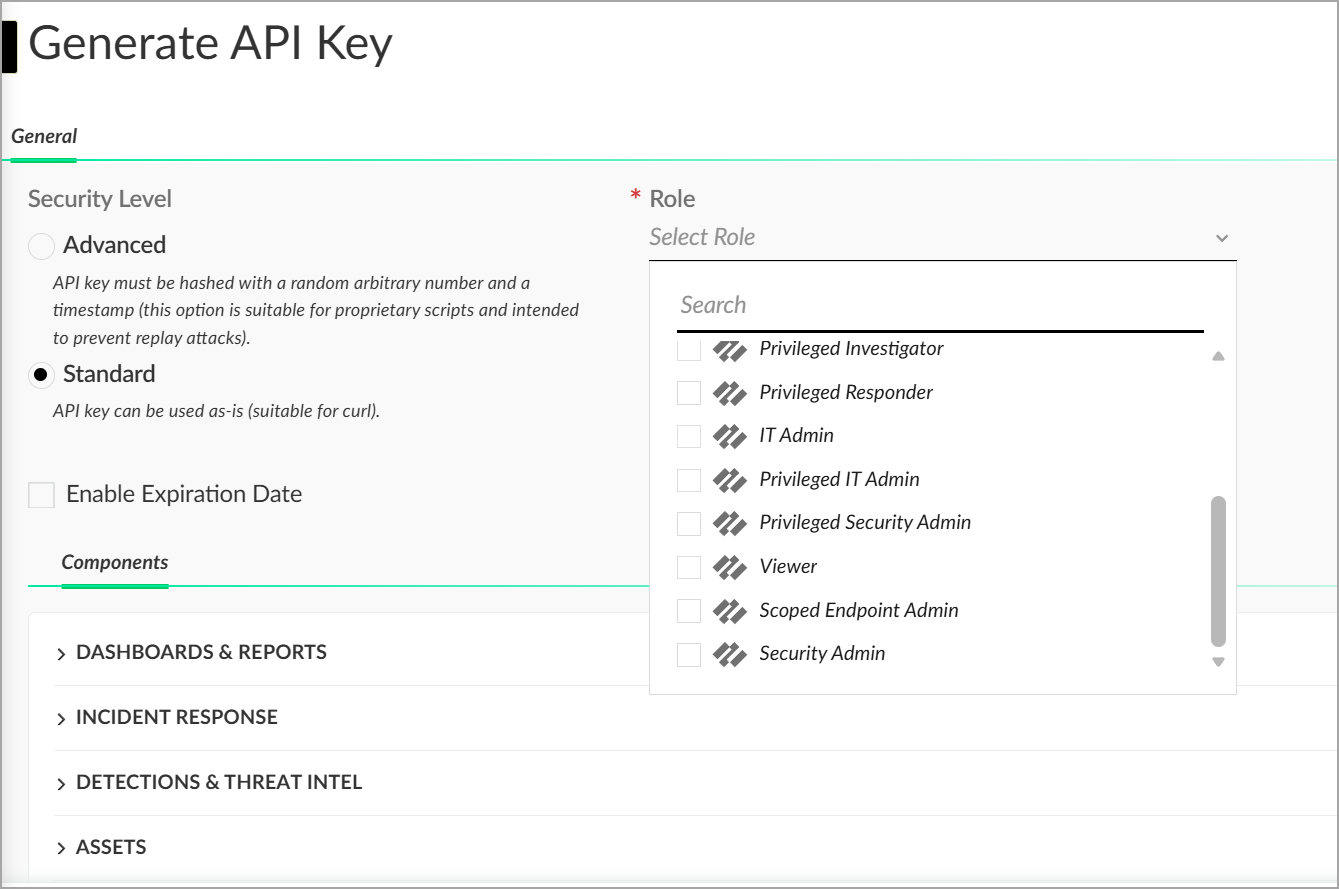
- Assign the Viewer role.
- Generate and copy the API Key and API Key ID.
Refer to the Cortex XDR API documentation to learn more about creating the API Keys. Make sure the API key is assigned the Viewer role with Standard security level.
Reference - Cortex XDR API Overview
Authentication Details
Provide the following credentials in the connector configuration screen:
| Name | Key | Type | Description |
|---|---|---|---|
| Base URL | baseURL |
String | Base URL of Cortex XDR API (e.g. https://api-<fqdn>) |
| API Key | apiKey |
Encrypted String | API Token generated in Cortex XDR |
| API Key ID | x-xdr-auth-id |
String | API Key ID associated with the API key |
Connector Configuration
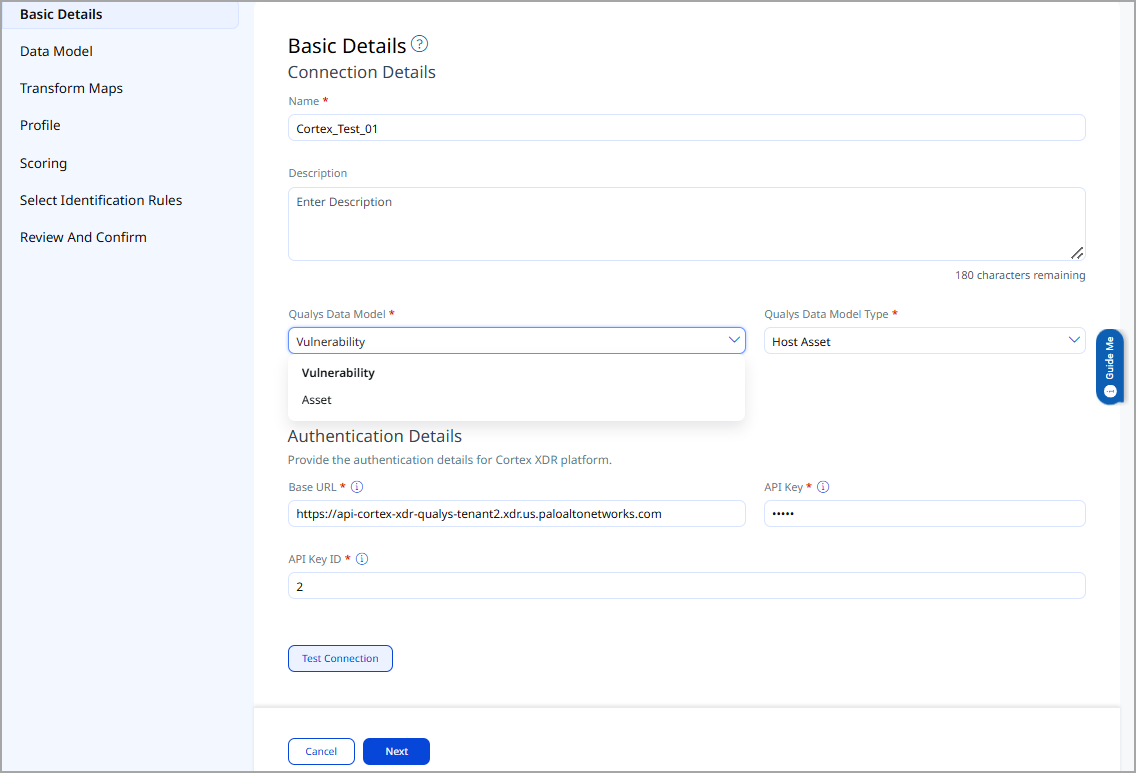
Basic Details
- Log in to Qualys ETM.
- Navigate to Connectors > Integration tab.
- Locate Cortex XDR Connector from the Marketplace and click Manage.
- Provide a Name and Description.
- Select findings type: Vulnerability / Host Asset.
- Enter Base URL, API Key, and API Key ID.
Mapping Details
Data Model
The Cortex XDR connector provides an out-of-the-box data model mapping aligned with the Qualys ETM schema. You can review the schema within ETM to understand all supported attributes.
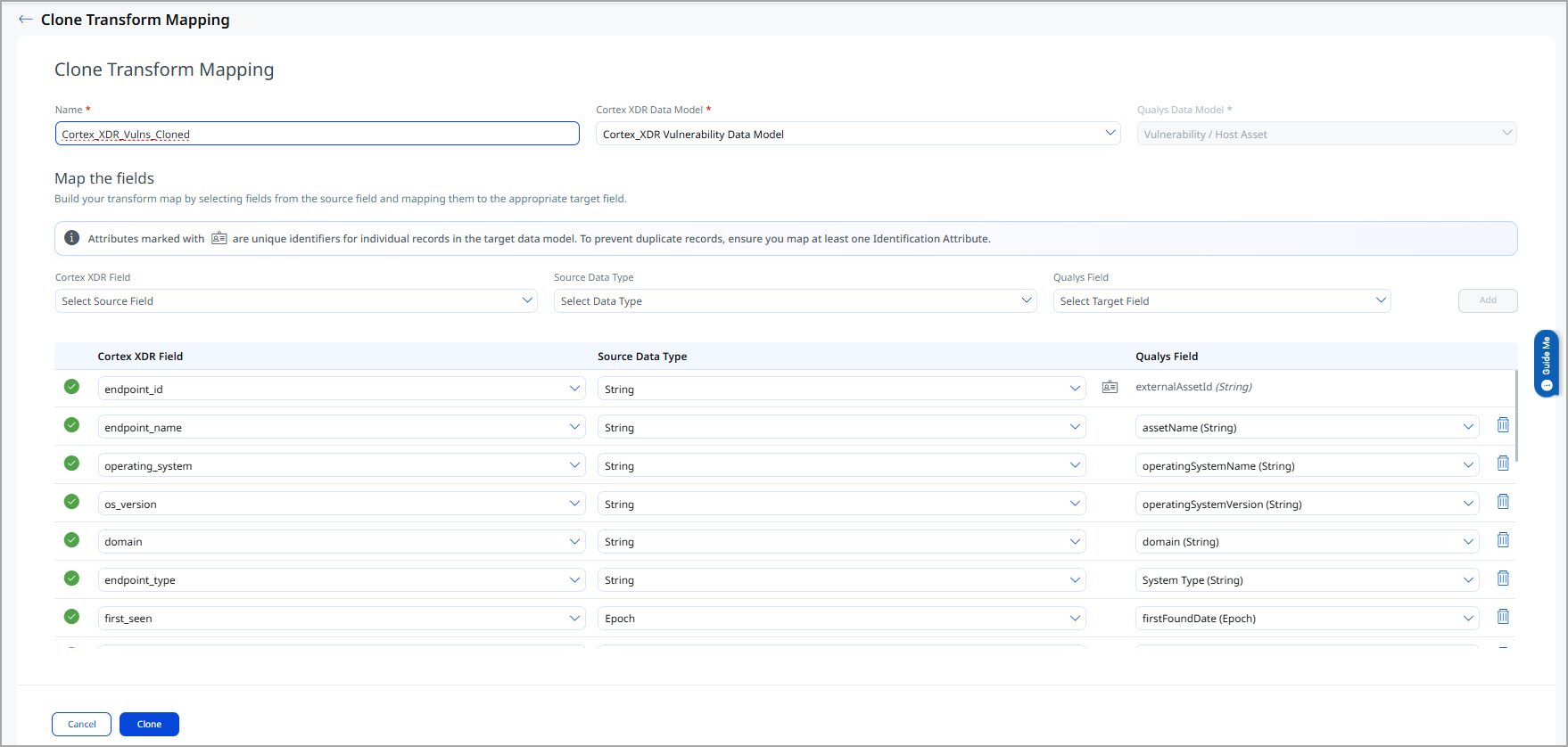
Transform Maps
Default transform maps are available. You can use them directly or create/clone maps to customize data transformation.
- Click Create New to create a transform map.
- Provide Transform Map Name.
- Select Source Data Model.
- Select Target Data Model.
- Save the configuration.
- Alternatively, use Clone to modify the default map.
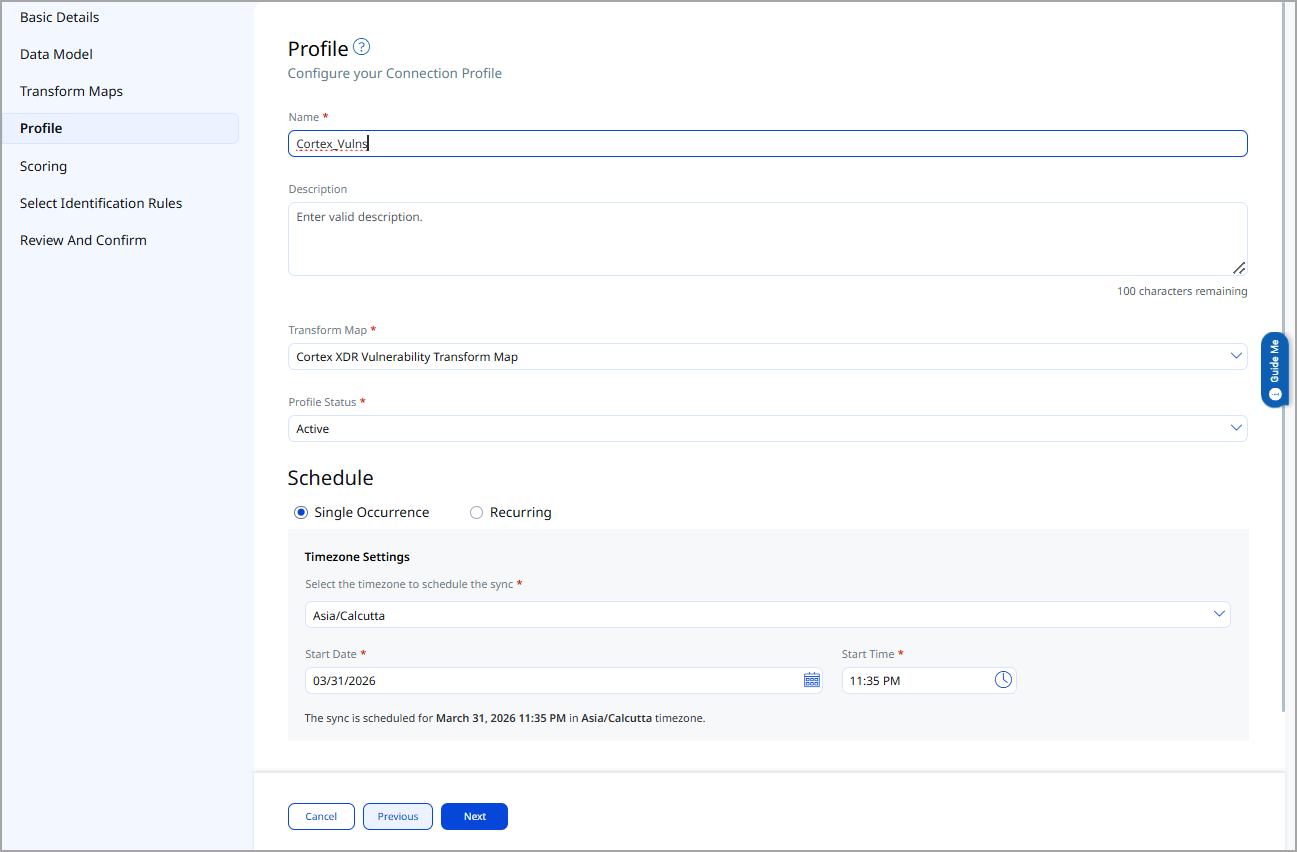
Profiles
Profiles control connector execution.
- Click + to create a new profile.
- Provide Name and Description.
- Select the required Transform Map.
- Set Status (Active / Inactive).
- Configure schedule:
- Single Occurrence – specify date/time.
- Recurring – specify start and end date/time.
Identification Rules
Identification Rules are predefined precedence rules from Qualys CSAM used to match findings to assets. You may proceed without changes.
How Does a Connection Work?
The Cortex XDR connector operates using configured profiles that determine what data is imported and when. Based on the defined schedule or manual execution, the connector pulls vulnerability and asset data from Cortex XDR into ETM.
Once processed, the connector status is updated to Processed on the Connectors screen.
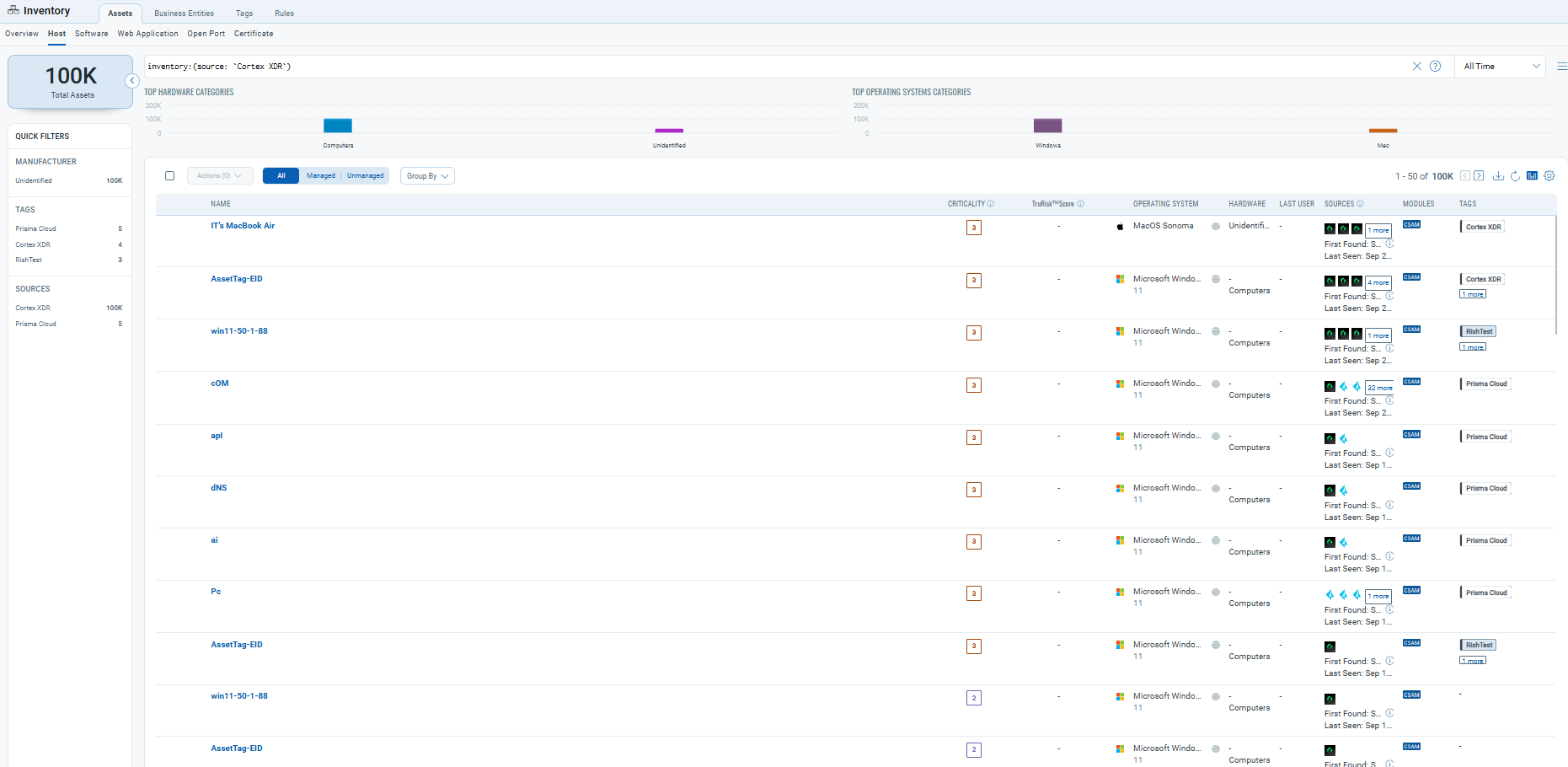
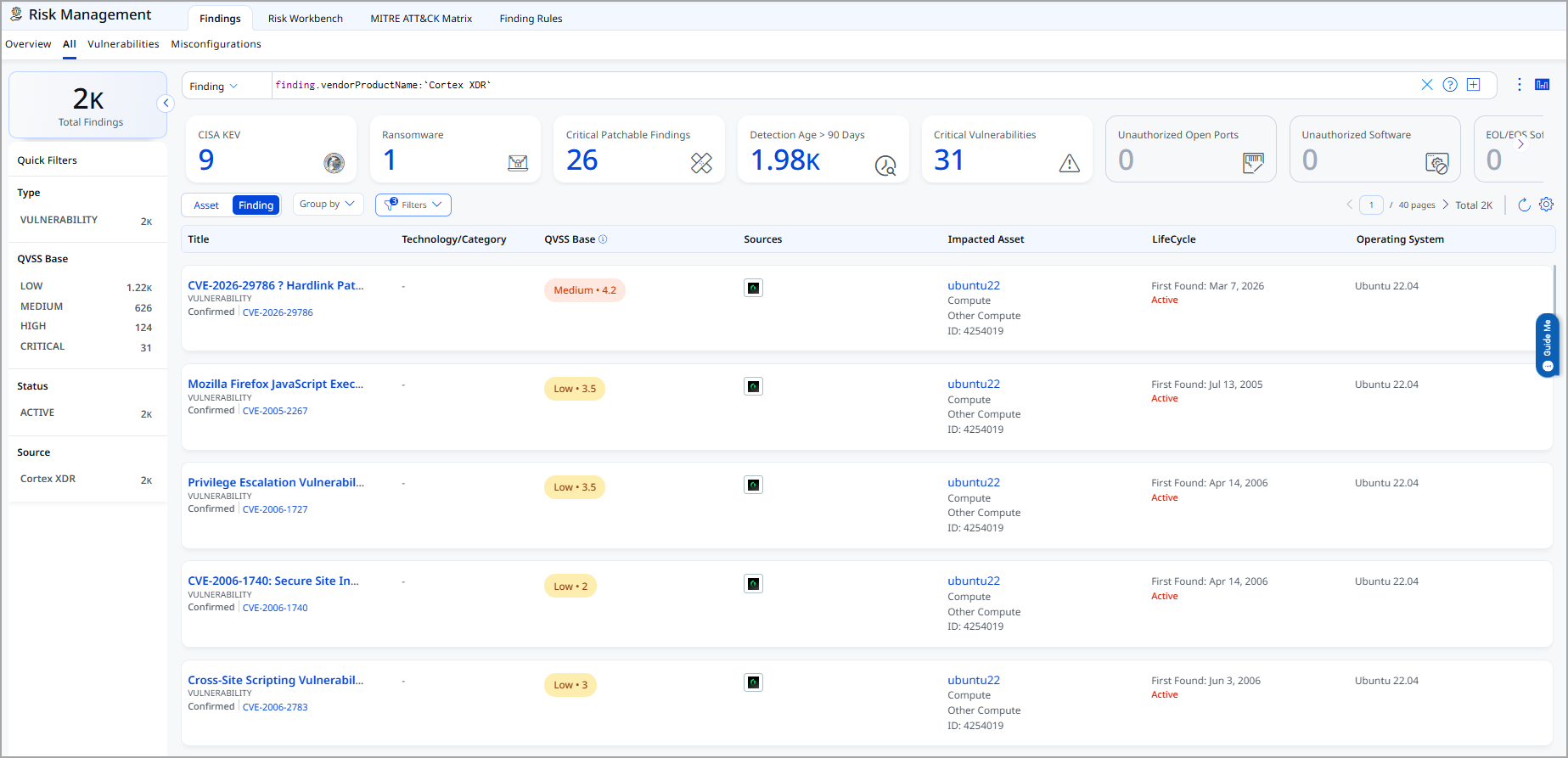
Viewing Assets and Findings in ETM
- Assets: Navigate to Inventory and use the query:
asset.inventory:(source:`Cortex XDR`)
- Findings: Navigate to Risk Management and use:
finding.vendorProductName:`Cortex XDR`
Cortex XDR Transformation Map (for Assets)
The default Assets transformation map configured for the Cortex XDR connector is fetched from the database and utilized during the execution of the connector profile to perform data transformation.
|
Source Field |
Target Field |
|---|---|
| endpoint_id | externalAssetId |
| endpoint_name | hostName |
| operating_system | operatingSystem.name |
| os_version | operatingSystem.version |
| domain | domain |
| endpoint_type | type |
| first_seen | firstFoundDate |
| allIPs | networkInterfaces[].ipv4Address |
| ipv6 | networkInterfaces[].ipv6Address |
| mac_address[] | networkInterfaces[].macAddress |
| tags.server_tags | temp_q_customAttributes.serverTags |
| tags.endpoint_tags | temp_q_customAttributes.endPointTags |
Cortex XDR Transformation Map (Vulnerabilities)
The default transformation map configured for the Cortex XDR connector is fetched from the database and utilized during the execution of the connector profile to perform data transformation.
|
Source Field |
Target Field |
|---|---|
| endpoint_id | externalAssetId |
| endpoint_name | hostName |
| operating_system | operatingSystem.name |
| os_version | operatingSystem.version |
| domain | domain |
| endpoint_type | type |
| first_seen | firstFoundDate |
| allIPs | networkInterfaces[].ipAddress |
| ip | networkInterfaces[].ipv4Address |
| ipv6 | networkInterfaces[].ipv6Address |
| mac_address[] | networkInterfaces[].macAddress |
| tags.server_tags | temp_q_customAttributes.serverTags |
| tags.endpoint_tags | temp_q_customAttributes.endPointTags |
| cves[].name | finding[].externalFindingId |
| cves[].name | finding[].findingType.vulnerability.cveId |
| cves[].severity | finding[].severity |
| cves[].description | finding[].description |
| cves[].publication_date | finding[].firstFoundOn |
| cves[].severity_score | finding[].sourceRiskScore |
| cves[].severity | finding[].sourceSeverity |
| cves[].name | finding[].name |
| cloud_provider | asset.assetDetail.cloudInfo.provider |