Crowdstrike Endpoint Security
The CrowdStrike Endpoint Security Connector integrates asset and vulnerability data from CrowdStrike Spotlight directly into Qualys Enterprise TruRisk Management, enabling security teams to consolidate endpoint detection and response findings with their broader vulnerability management strategy.
By automatically syncing host assets and their associated vulnerabilities into a centralized platform, teams gain unified visibility into their security posture without manual data aggregation. This integration eliminates data silos between endpoint protection and vulnerability management systems, allowing practitioners to correlate findings and prioritize remediation efforts more effectively.
The connector's automated, scheduled execution ensures that vulnerability data remains current, supporting faster incident response and more informed risk decisions across the organization.
Connector Details
Here is a comprehensive overview of what the Crowdstrike Connector supports.
| Vendor | Crowdstrike |
| Product Name | Crowdstrike |
| Category | Endpoint Security |
| Findings Supported | Yes |
| Assets Supported | Host Assets (Compute) |
| Version | 1.0.0 |
| Integration Type | API Integration (REST) |
| Direction | Unidirectional |
| Delta Support | Supported |
| Supported Version & Type | SaaS (Latest) |
| Import of Installed Software | Not Supported |
| Import of Source Tags | Not Supported |
| Filters/Filter Query | Not Supported |
Prerequisites
These are the required configurations you need to successfully create an connection for Qualys ETM.
User Roles and Permissions
You need the following API Access information to configure the connection:
- Auth URL
- Client ID
- Client Secrets
For quick reference on how to obtain the required values, follow the steps below.
Auth URL
To obtain the Auth URL, refer to your Crowdstrike Cloud Environment URL. For example, https://api.us-2.crowdstrike.com or https://api.eu-1.crowdstrike.com.
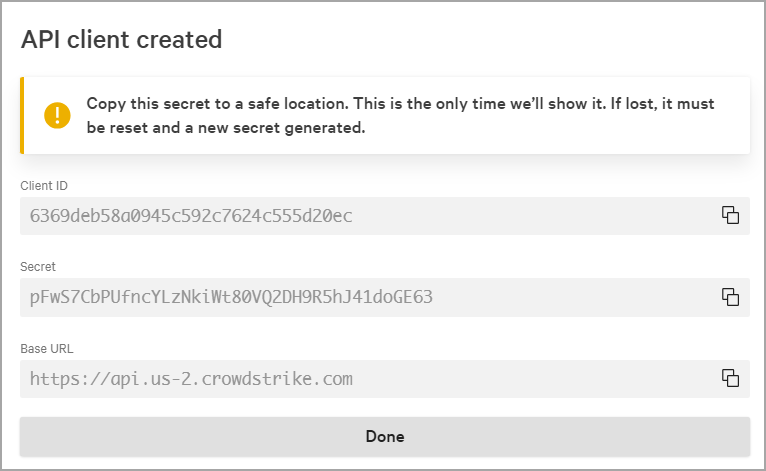
Client ID and Client Secret
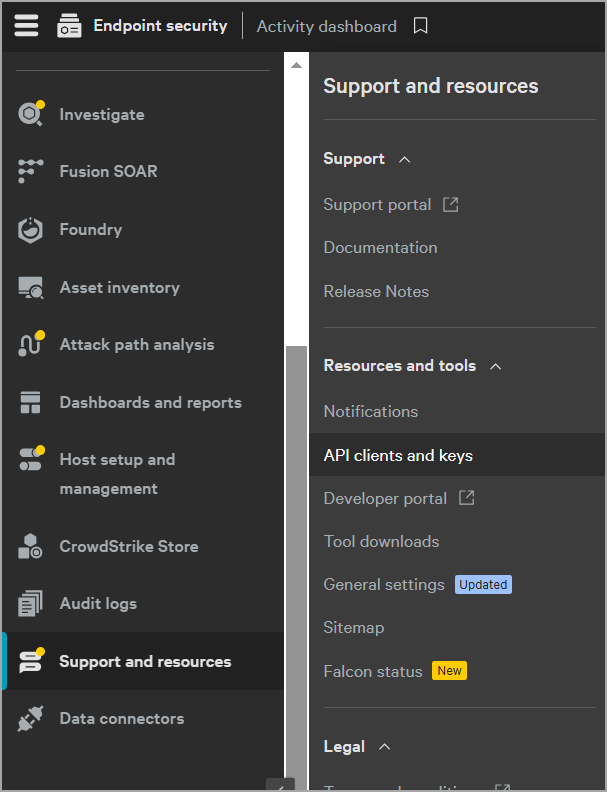
- Naviagate to your Crowdstrike portal.
- Go to Support > API Clients and Keys. When the API Key page appears, select Add a new API client.
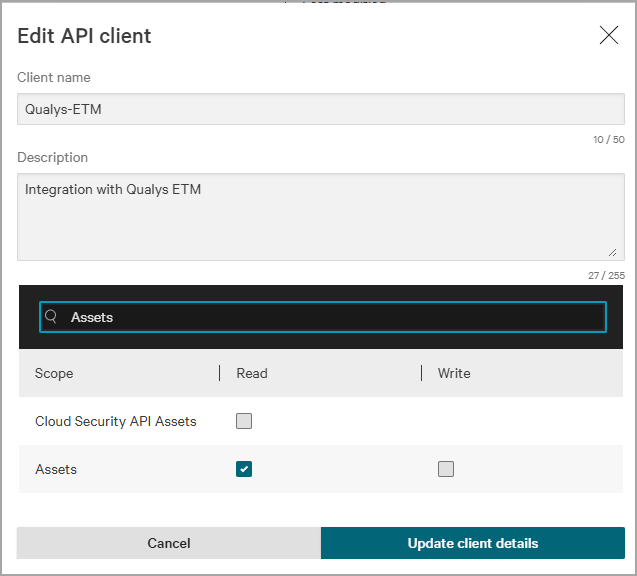
- Provide the following details for the API client:
- Client name : Provide an API client name of your choice.
- API scope :
- To ingest host details, search, and include read permissions for Hosts and Host Groups.
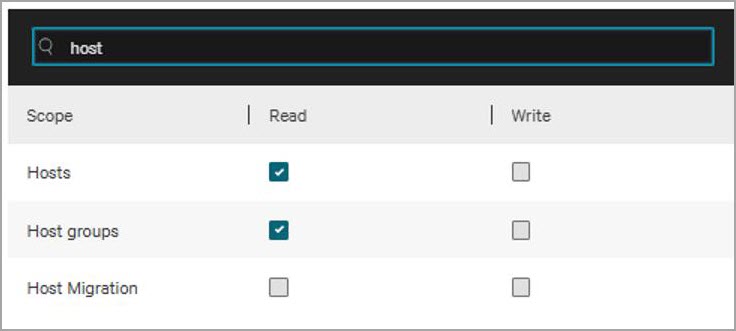
- To ingest vulnerability data, search and include read permissions for Hosts, Host Groups and Vulnerabilities.
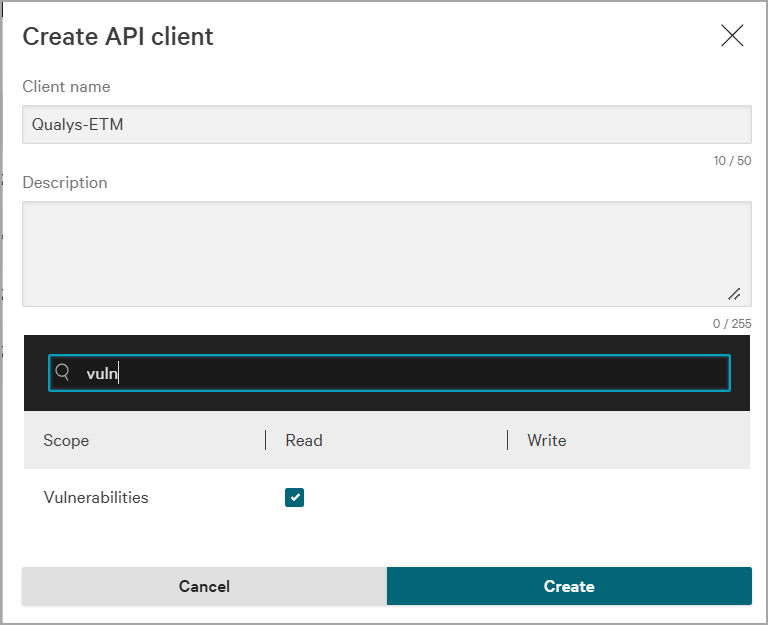
- To ingest software data, search and include read permissions for Assets, Hosts, and Host Groups.
- To ingest host details, search, and include read permissions for Hosts and Host Groups.
Some CrowdStrike accounts consist of multiple customers, each assigned its own Customer ID (CID). These CIDs are organized in a parent/child hierarchy. The parent CID has access to all hosts within the account, including those linked to its child CIDs. However, only the child CID can access its own host groups and vulnerabilities.
When creating the API client, ensure that you use the appropriate user account.
When you are done, add the client. An API client created window appears and displays the Client ID and Client Secret. Store them securely for later use.
Required Permissions
Enable these permissions for the Connection.
|
Permission |
Permission display name |
|---|---|
|
Vulnerabilities |
Read permissions for Vulnerabilities. |
|
Hosts |
|
Create a New API Connector
- Provide the Connector's Name and Description.
- Select the type of findings you want to import or export - currently, we support Vulnerability.
- Select the Asset Type - currently we support Host Asset.
- Select the Supported Format - currently, we support CrowdStrike Spotlight.
The following screenshot displays the Basic Details fields.
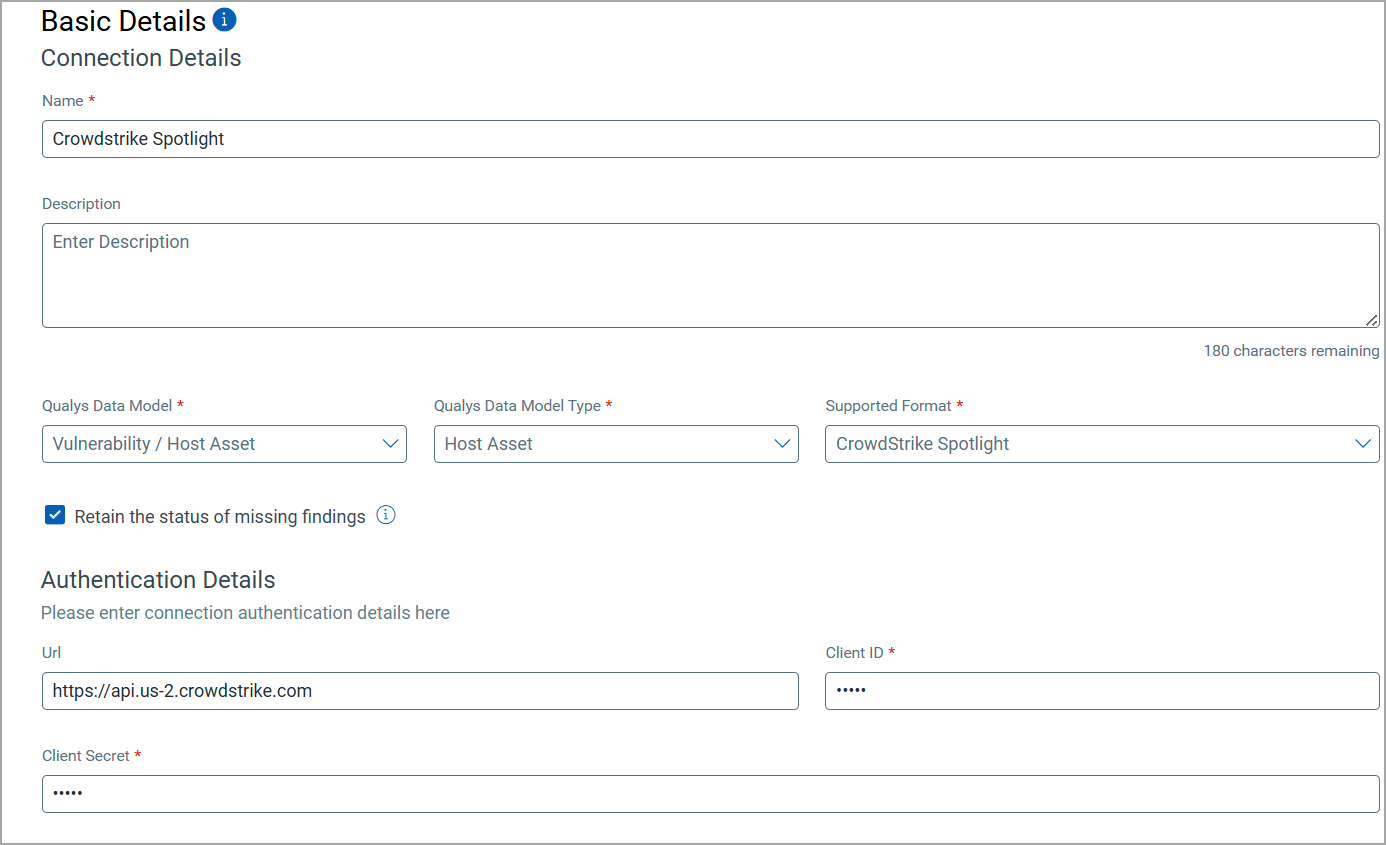
-
Next, provide the API authentication details of the Crowdstrike environment. You need to provide the following.
- URL: Enter the authentication URL of your Crowdstrike environment.
- Client ID: Provide the application client ID from your Crowdstrike instance.
- Client Secret: Enter the secret key generated for your application.
These values can be obtained by following the steps laid out in the User Roles and Permissions section.
The Crowdstrike API Connector offers an out-of-box data model mapping for you to map with Qualys ETM schema. You can view the schema to understand the attributes in the data model.
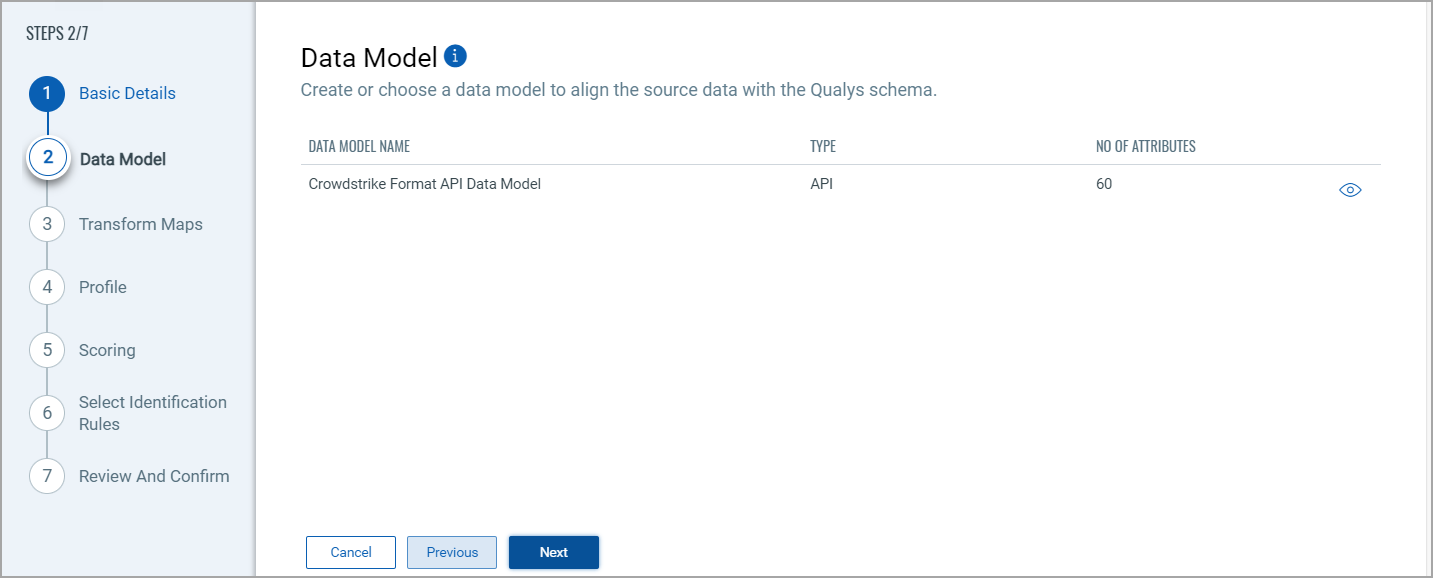
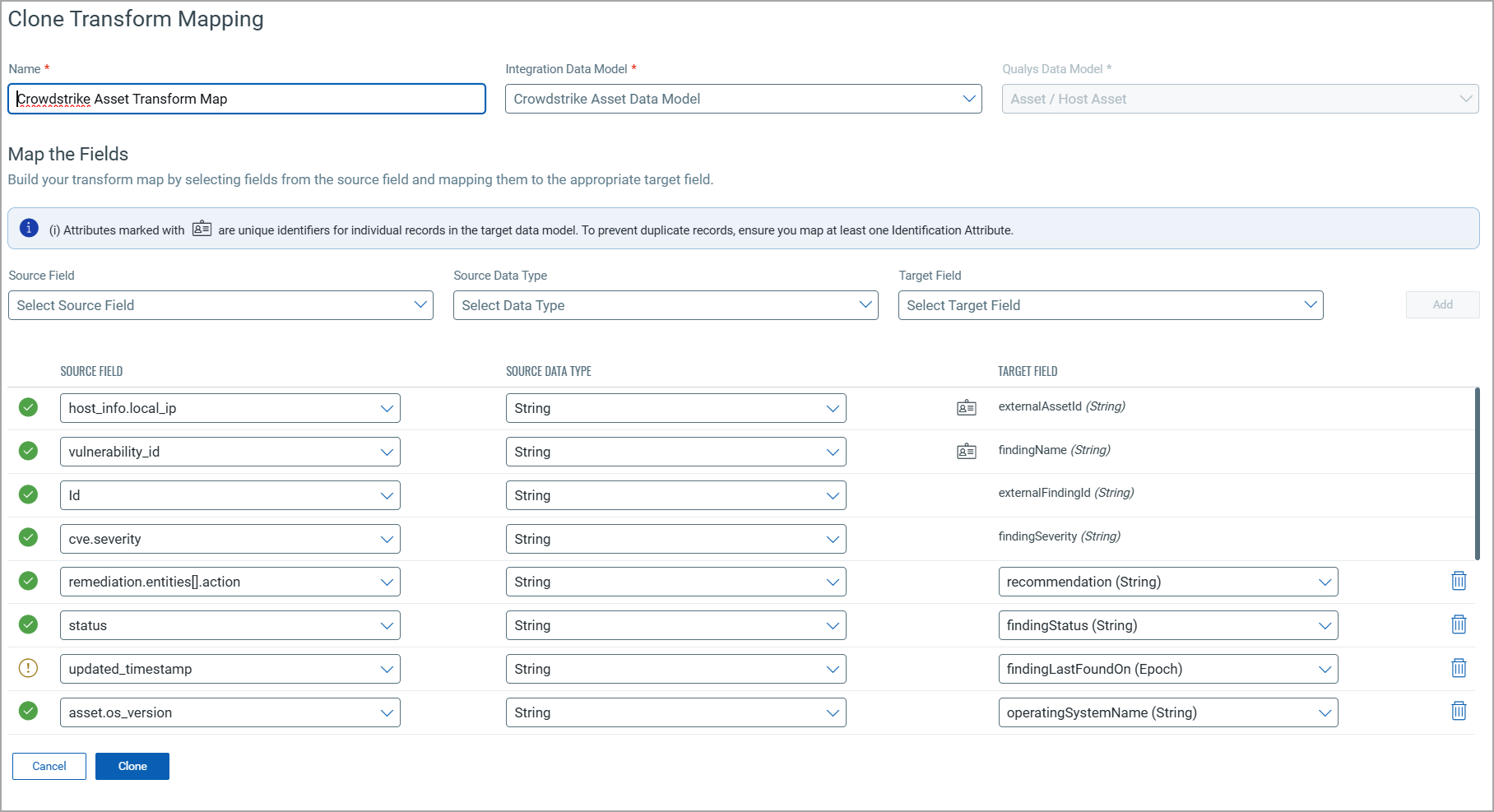
Map the fields from CrowdStrike to the corresponding fields in your target system. Transform Maps ensure the data is transformed correctly during the import or export process.
The Crowdstrike Connector offers an out-of-box transform map for you to proceed without further configuration. View the map to understand the data transformation or clone the map to edit its configurations.
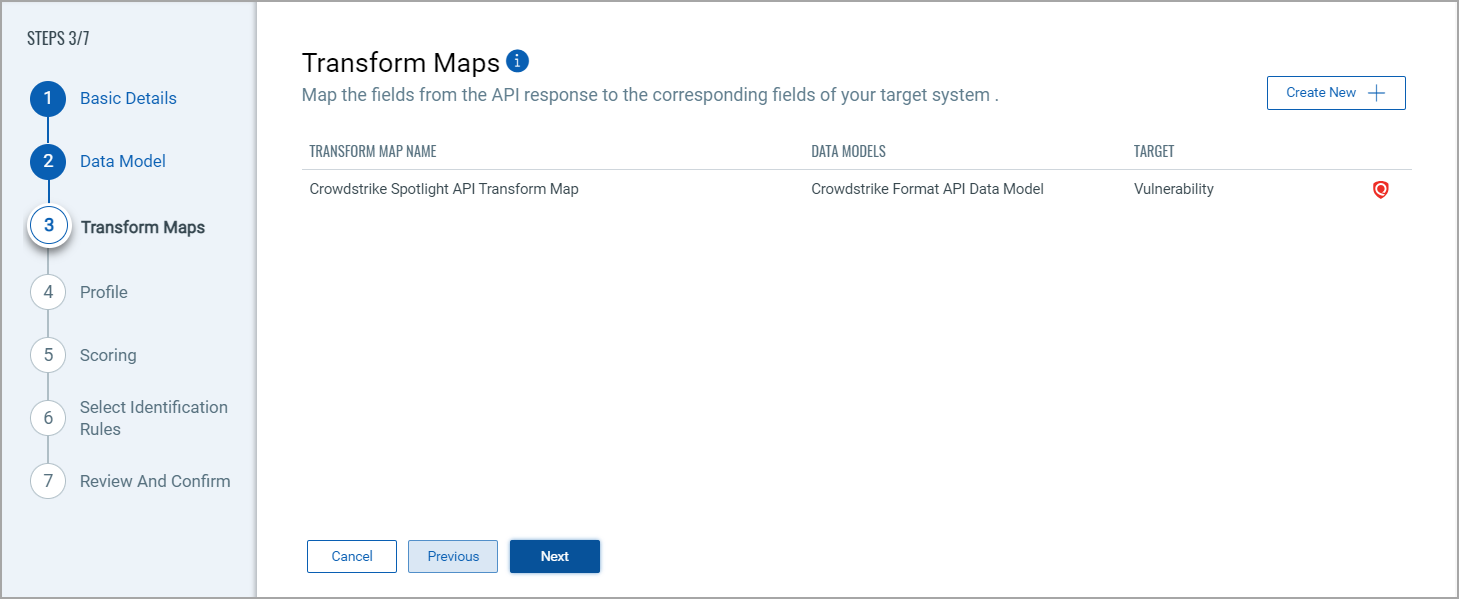
Click Create New for a new Transform Map.
Perform the following steps to configure a Transform Model:
- Transform Map Name: Enter a unique name for the Transform Map. This name helps identify the specific transformation configuration within this connector.
- Source Data Model: Select the data model that serves as the input for the transformation. This is the model from which data will be extracted.
- Target Data Model: Choose the data model that receives the transformed data. This model defines how the data will be structured after the transformation.
To learn more about the data mapping from Crowdstrike to Qualys ETM, refer to Data Model Mapping.
Fields Mapping
The Fields Mapping section maps fields from the Source Data Model to the Target Data Model.
- Source Field: Specify the field in the Source Data Model containing the transformed data.
- Data Type: Indicate the data type of the Source Field (e.g., string, integer, date).
- Target Field: Designate the corresponding field where the transformed data will be placed in the Target Data Model.
Click Add to create and display the mapping for the Source Field, Data Type, and Target Field below the section. This visual helps ensure that all necessary fields are mapped correctly and allows easy verification and adjustments.
Create a profile for your connector. A profile decides the connector status, execution schedule and transform map to choose. The connector follows the configurations of this profile for all future executions.

Click the "+" to create a new profile.
In the Add Profile screen, provide the necessary inputs for your new profile.
Provide a Name and Description.
Select the required Transform Map for the data mapping.
The Status field determines whether the connector should be in Active or Inactive state after creation.
Select Identification RulesSelect Identification Rules
The Identification Rules are a set of out-of-the-box precedence rules set by Qualys CSAM. The connector discovers findings based on the order set by the selected Identification Rules.
You can proceed to the next step without making any changes to this screen.
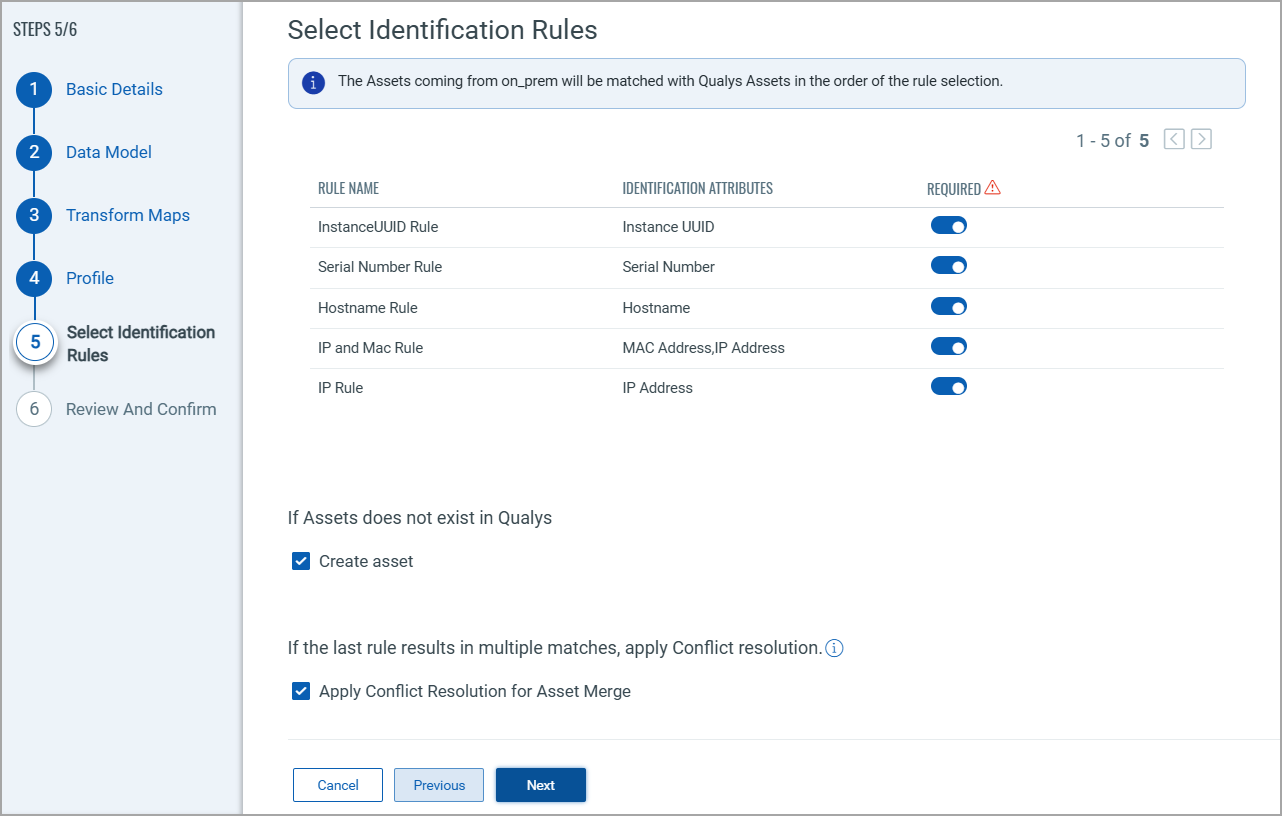
If you don't want to choose a specific rule, turn off the toggle next to it. But, ensure that at least one rule is selected.
To learn more about the different rules and options present in this screen, refer to the CSAM Online Help.
Once you are done with all the configuration, review the configurations provided in the previous steps. Ensure all details are correct and complete. Confirm the setup to finalize the configuration of the API connector.
Save and run the connector to process the data accordingly, transforming and importing it as per the configurations set.
How Does a Connection Work?
The Crowdstrike connector functions through configured profiles that determine what data gets synchronized and when.
A Connection usually involves creating a profile that defines which vulnerabilities to import based on detection data types and asset types. The connector then automatically executes according to the schedule (or on-demand), pulling vulnerability data from Crowdstrike into Qualys ETM where it can be viewed alongside other security findings.
With the Crowdstrike API Connector successfully configured, you are almost ready to view all the assets and findings from Crowdstrike.
In the Connector screen, you can find your newly configured connector listed and marked in the Processed state.
Connector States
A successfully configured connector goes through 4 states.
- Registered - The connector is successfully created and registered to fetch data from the vendor.
- Scheduled - The connector is scheduled to execute a connection with the vendor.
- Processing - A connection is executed and the connector is fetching the asset and findings data.
- Processed - The connector has successfully fetched the assets, it may still be under process of fetching the findings. Wait for some more time for the connector to fetch the findings completely.
The Processed state indicates that the Connector is successfully configured but it is under the process of importing all your assets and findings. This process (specifically for findings) may take some time.
This entire process may take up to 2 hours for completion. Once it is done, you can find the imported data in Enterprise TruRisk Management (ETM).
View Assets and Findings in ETM
Navigate to Enterprise TruRisk Management to get started with analyzing your Connector's vulnerability findings.
You can view the assets imported from the Crowdstrike connection by navigating to Inventory tab of ETM.
Go to Assets > Host to find all of your imported assets.
Use the token, inventory: (source: `CrowdStrike Spotlight`) to view all the imported assets.
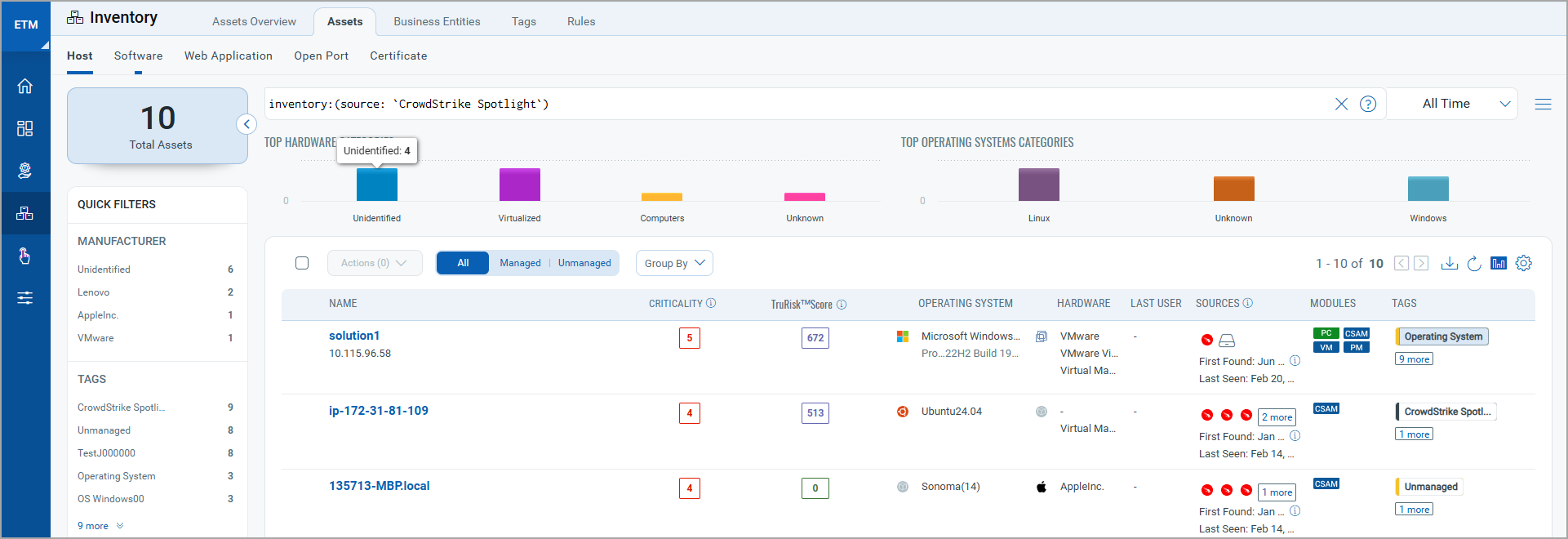
Here, you can learn about the criticality of your assets and their Risk Scores. Click any of the asset to find more details about them.
Next, you can navigate to the Risk Management tab to view your vulnerability findings.
Go to Findings > Vulnerability to view all the discovered vulnerabilities.
Use the token, finding.vendorProductName: `Spotlight` to view all the discovered vulnerabilities.
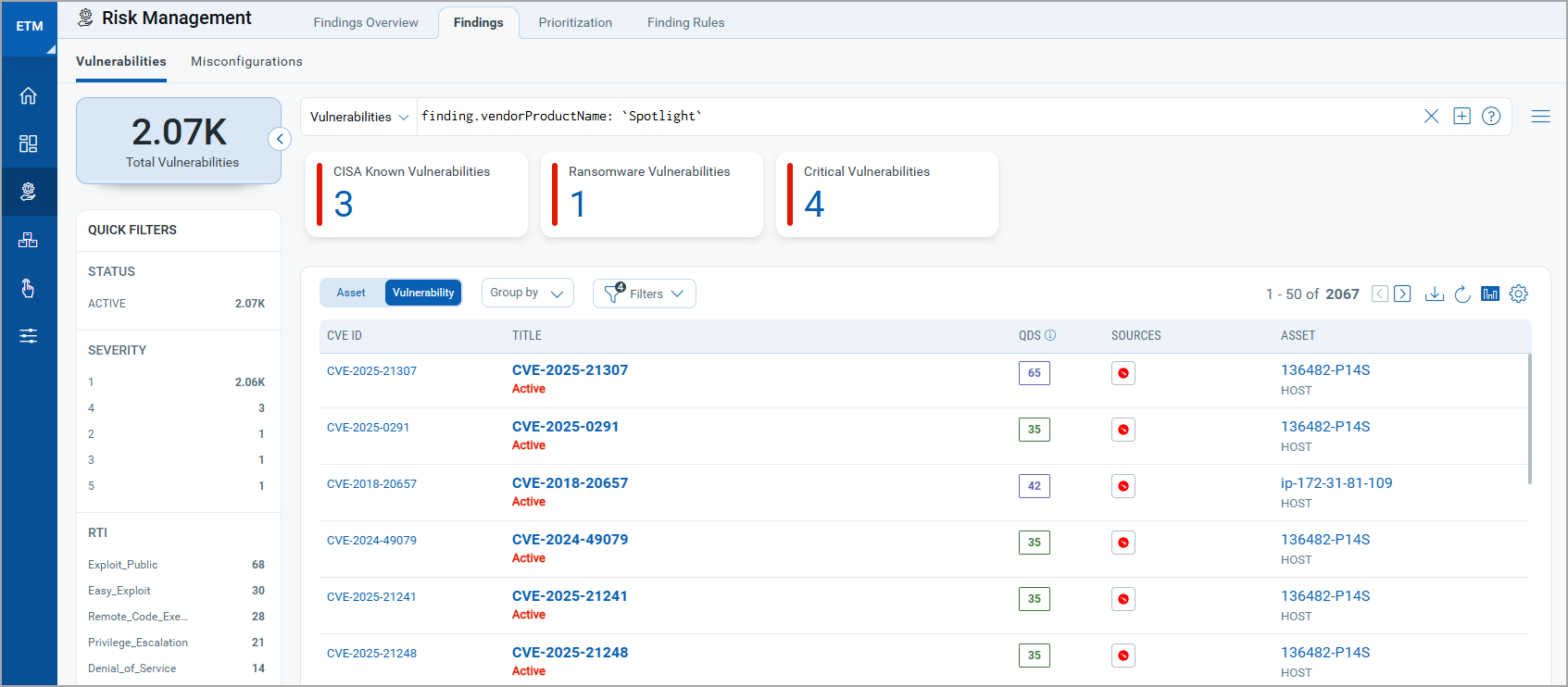
To know more about how the CrowdStrike API Connector leverages the findings, refer to the Qualys ETM Documentation.
Additional Asset Filters in the Crowdstrike Profile
We offer additional filters for the Crowdstrike connection profile to help narrow down the specific assets you want to fetch. To access these filters, you must update an existing connector.
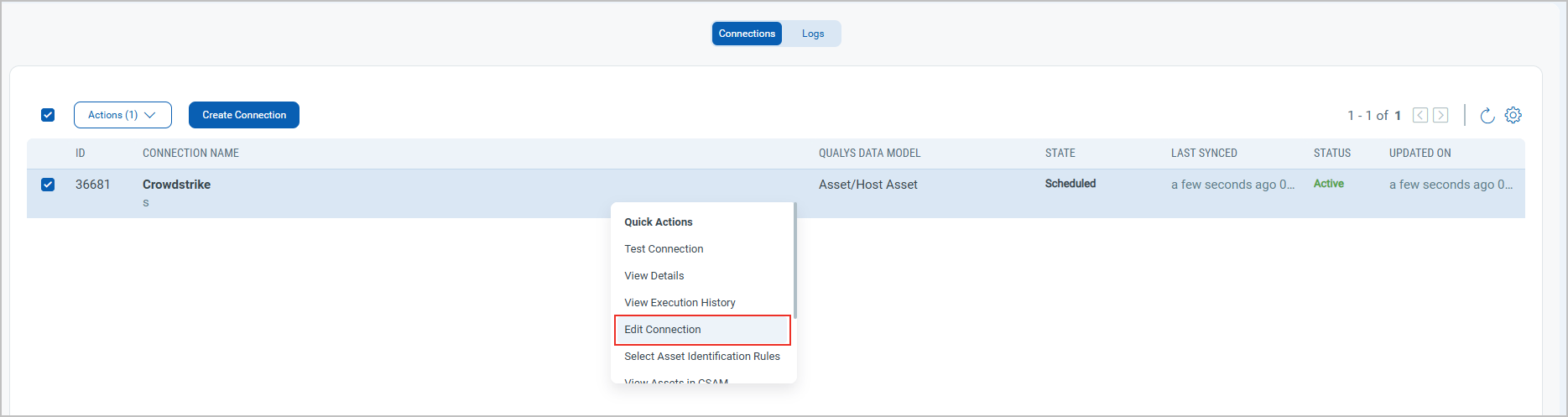
Navigate to the connector you have just created > Open the Quick Actions menu >Select Edit Connection.
Navigate to the Profile section and you can view two additional drop-downs, Product Type and Data Provider.
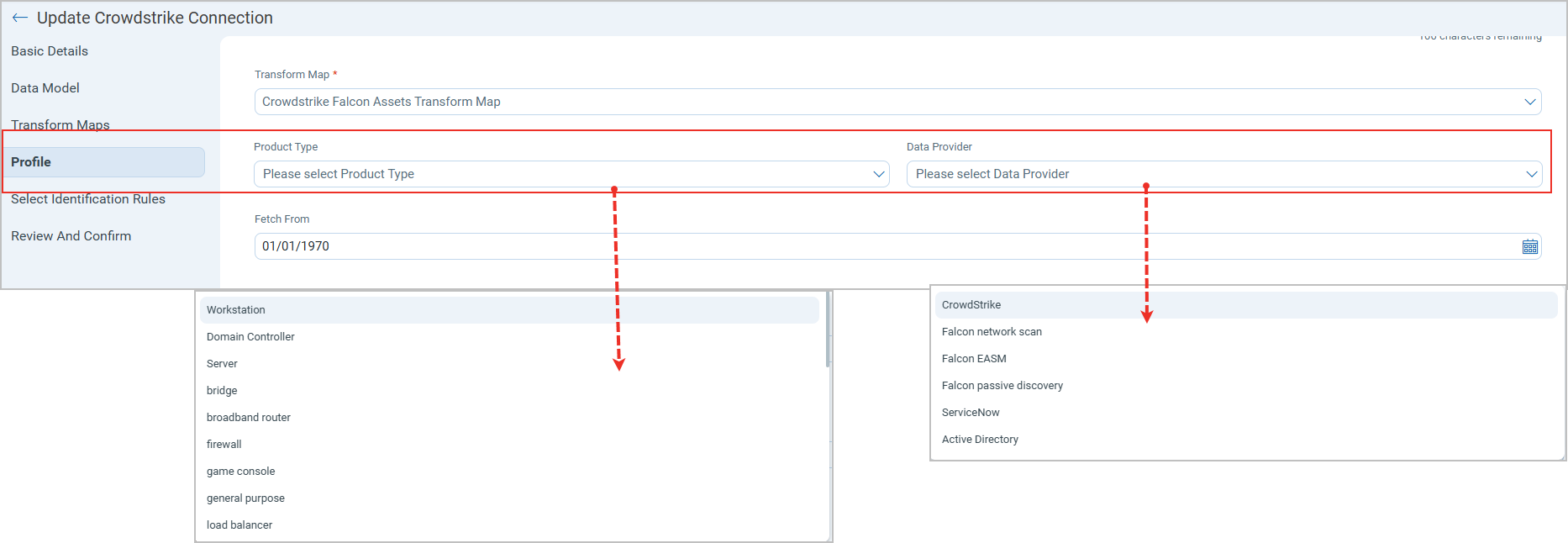
These drop-downs enable more granular filtering of Host Assets discovered in the ETM inventory. You can select multiple filters, such as load balancers and Game consoles, for the product type and Falcon Network Scan, and Active Directory for the Data Provider. Only combination of assets that match the selected Product Type and Data Source appear in the ETM asset inventory.
Additional Resources
Additional Information related to the Crowdstrike Connector.
API Reference
Here are the APIs executed for the Crowdstrike connection.
|
Name |
Filters |
Endpoint |
|---|---|---|
|
Auth API |
N/A | https://api.<domain>.crowdstrike.com https://api.<domain>.crowdstrike.com |
|
Fetch Vulnerabilities API |
Finding Type: Vulnerabilities |
https://api.<domain>.crowdstrike.com/spotlight/combined/vulnerabilities/v1 |
| Fetch Assets/Resources API | Asset type: Hosts | https://api.<domain>.crowdstrike.com/discover/entities/hosts/v1?ids=<aid> |
Data Model Map
CrowdStrike Vulnerability Transformation Mapping
| Source Attribute Key | Target Attribute Label |
|---|---|
| network_interfaces[].local_ip | externalAssetId (Required) |
| Vulnerability Id | findingName (Required) |
| id | externalFindingId (Required) |
| CVE Severity | findingSeverity (Required) |
| Remediation Entities action | recommendation |
| Status | findingStatus |
| Updated Timestamp | findingLastFoundOn |
| os_version | operatingSystemName |
| Data Provider | detectectionMethod |
| CVE Id | cveId |
| CVE Description | findingDescription |
| CVE Base Score | cvssV2Base |
|
confidence Available values: |
findingSubType Available values: |
| system_serial_number | biosInfoSerialNumber |
| bios_manufacturer | biosInfoManufacturer |
| hostname | assetName |
| network_interfaces[].mac_address | macAddress |
| network_interfaces[].local_ip | ipAddress |