Qualys Dataflow for Container Security
The Qualys Dataflow for Container Security Connector automates the ingestion of container image and instance data from Qualys Container Security into Qualys Enterprise TruRisk Management for centralized risk analysis. By consolidating container asset information with vulnerability findings in a unified platform, security teams can prioritize remediation efforts more effectively and gain comprehensive visibility into container-based infrastructure risks.
The connector supports delta synchronization and bidirectional mapping between container security data models and the ETM risk management system, enabling teams to correlate container vulnerabilities with business context and organizational risk posture. This integration eliminates manual data silos between container security tools and enterprise risk management, allowing teams to make faster, more informed decisions about container security investments and remediation strategies.
Connector Details
High-level connector information and supported asset types.
| Vendor | Qualys |
|---|---|
| Product Name | Container Security |
| Connector Category | Cloud Security |
| Asset Types Supported | Containers & Images |
| Findings Supported | Yes |
| Version | 1.0.0 |
| Integration Type | API Integration (REST) |
| Direction | Unidirectional (Container Security to Qualys ETM) |
| Delta Support | Supported |
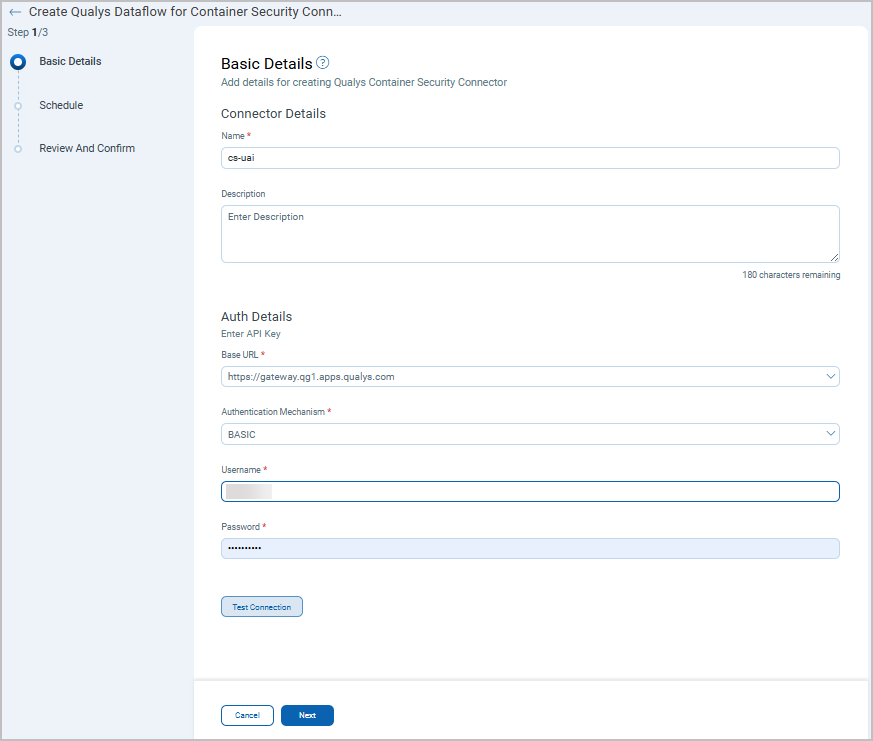
Connection Settings
Authentication Details
Provide the following credentials in the connector configuration screen:
| Name | Key | Type | Description |
|---|---|---|---|
| BASE URL | baseURL |
Drop Down |
Base URL of Container Security. Example:https://gateway.qg1.apps.qualys.com
|
| Authentication Mechanism |
- | Drop Down |
Choose between Basic or OAuth. |
| Username | Username |
String | For Basic Authenitcation, provide the Qualys Container Security username |
| Password | Password |
String | For Basic Authenitcation, provide the Qualys Container Security password |
| Client ID | Client ID |
String | For OAuth Authenitcation, provide the Client ID |
| Client secret | Client secret |
String | For Basic Authenitcation, provide the Client Secret |
API Endpoints
APIs used by the connector (use the Gateway URL configured in the connector when calling these endpoints):
| Name | Endpoint |
|---|---|
| Get Images | https://<gateway_url>/csapi/v1.3/images/list |
| Get Instance | https://<gateway_url>/csapi/v1.3/containers/list |
Connector Configuration
Basic Details
- Login to Qualys ETM.
- Go to Connectors > Integration tab and locate the Container Security Connector.
- Click Manage from the ellipses menu.
- Provide a Name and Description for the connector.
- Enter authentication details (Gateway URL & credentials as required).
- Click Next to configure scheduling and profiles.
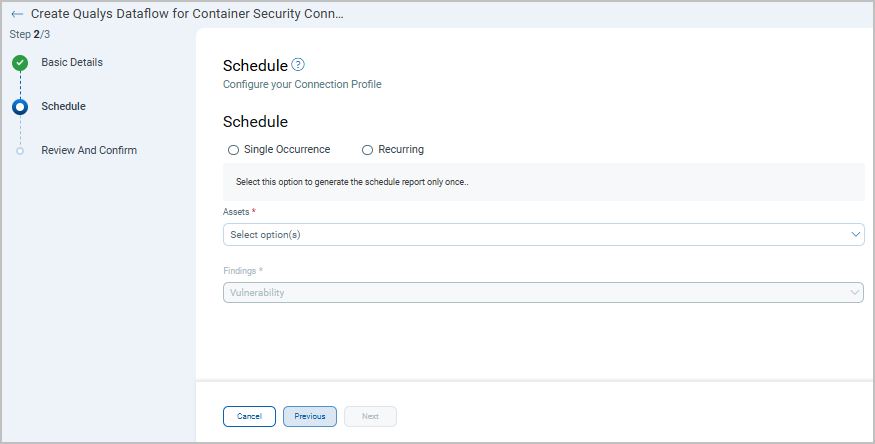
Schedule
Profiles following details:
- Configure a Schedule: Single Occurrence or Recurring with start and end dates/times.
- Assets value will be
CONTAINERby default for container security connector.
Click Next.
Mapping Details
Transform Maps
The Container Security connector provides default data model transform maps for Container Image and Container Instance. The default transformation maps configured for the connector are fetched from the database and utilized during the execution of the connector profile to perform data transformation.
- Click Create New to add a new transform map.
- Provide a Transform Map Name, select Source Data Model, and select Target Data Model.
- Save the map or clone the default map from the quick menu.
Container Security Image - Transformation Map
The default transformation map configured for the Container Security Image – connector is used during connector execution:
| Source Field | Target Field |
|---|---|
| repo.0.registry | asset.assetDetail.containerImageAssetClass.registry |
| repo.0.tag | asset.assetDetail.containerImageAssetClass.tag |
| repo.0.repository | asset.assetDetail.containerImageAssetClass.name |
| repo.0.repository | asasset.assetDetail.name |
| repo.0.repository | asset.assetDetail.containerImageAssetClass.repository |
| sha | asset.assetHeader.externalAssetId |
| sha | asset.assetDetail.containerImageAssetClass.digest |
| architecture | asset.assetDetail.containerImageAssetClass.architecture |
| uuid | asset.assetHeader.vendorAssetId |
| size | asset.assetDetail.containerImageAssetClass.sizeInBytes |
| layers[].size | asset.assetDetail.containerImageAssetClass.layers[].sizeInBytes |
| layers[].sha | asset.assetDetail.containerImageAssetClass.layers[].digest |
| layers[].createdBy | asset.assetDetail.containerImageAssetClass.layers[].command |
| created | asset.assetDetail.containerImageAssetClass.creationDate |
| qid | findingGroup.findings[].externalFindingId |
| qid | findingGroup.findings[].findingType.vulnerability.vendorId |
| cveids.0 | findingGroup.findings[].findingType.vulnerability.cveId |
| severity | findingGroup.findings[].severity |
| status | findingGroup.findings[].findingStatus |
| firstFound | findingGroup.findings[].firstFoundOn |
| lastFound | findingGroup.findings[].lastFoundOn |
| Version | findingGroup.findings[].product.version |
| Software Name | findingGroup.findings[].product.name |
| Fix Version | findingGroup.findings[].solutionRecommendation |
| Type Detected | findingGroup.findings[].typeDetected |
| Affected Layer | findingGroup.findings[].attributes.affected_layer_sha |
| attackVector | findingGroup.findings[].findingType.vulnerability.cvss.vector |
| title | findingGroup.findings[].name |
| title | findingGroup.findings[].description |
| baseScore | findingGroup.findings[].findingType.vulnerability.cvss.baseScore |
| operatingSystem | asset.assetDetail.containerImageAssetClass.os |
| Category (SCA/STATIC) | findingGroup.findings[].findingType.vulnerability.category |
| Scan Type | findingGroup.findings[].detectionMethod |
Container Security Instance - Transformation Map
The default transformation map configured for the Container Security Instance – connector is used during connector execution:
| Source Field | Target Field |
|---|---|
| portMapping.port | asset.assetDetail.containerInstanceAssetClass.ports[].containerPort |
| portMapping.protocol | asset.assetDetail.containerInstanceAssetClass.ports[].protocol |
| portMapping.hostport | asset.assetDetail.containerInstanceAssetClass.ports[].hostPort |
| created | asset.assetDetail.firstSeen |
| updated | asset.assetDetail.lastSeen |
| uuid | asset.assetHeader.vendorAssetId |
| sha | asset.assetHeader.externalAssetId |
| imageDetails[0].repo.0.repository | asset.assetDetail.containerInstanceAssetClass.image.name |
| imageDetails[0].repo.0.repository | asset.assetDetail.containerInstanceAssetClass.image.registry |
| imageSha | asset.assetDetail.containerInstanceAssetClass.image.digest |
| imageDetails[0].repo.0.tag | asset.assetDetail.containerInstanceAssetClass.image.tag |
| name | asset.assetDetail.name |
| host.hostname | asset.assetDetail.containerInstanceAssetClass.host.name |
| host.ipAddress | asset.assetDetail.containerInstanceAssetClass.host.ipAddress |
| state | asset.assetDetail.containerInstanceAssetClass.status |
| state | asset.assetHeader.status |
| customerUuid | asset.assetHeader.customerId |
| containerId | asset.assetDetail.containerInstanceAssetClass.id |
| stateChanged | asset.assetDetail.containerInstanceAssetClass.startTime |
| ipv4 | asset.assetDetail.containerInstanceAssetClass.privateIpv4Addresses[0] |
| ipv6 | asset.assetDetail.containerInstanceAssetClass.privateIpv6Addresses[0] |
| QID | findingGroup.findings[].externalFindingId |
| QID | findingGroup.findings[].findingType.vulnerability.vendorId |
| vulnDetails.details[].cveids.0 | findingGroup.findings[].findingType.vulnerability.cveId |
| Severity | findingGroup.findings[].severity |
| status | findingGroup.findings[].findingStatus |
| First Found (ms) | findingGroup.findings[].firstFoundOn |
| Last Found (ms) | findingGroup.findings[].lastFoundOn |
| Version | findingGroup.findings[].product.version |
| Software Name | findingGroup.findings[].product.name |
| Fix Version | findingGroup.findings[].solutionRecommendation |
| Type Detected | findingGroup.findings[].typeDetected |
| Affected Layer | findingGroup.findings[].attributes.affected_layer_sha |
| attackVector | findingGroup.findings[].findingType.vulnerability.cvss.vector |
| Title | findingGroup.findings[].name |
| Title | findingGroup.findings[].description |
| CVSS v3 Base Score | findingGroup.findings[].findingType.vulnerability.cvss.baseScore |
| Operating System | asset.assetDetail.containerInstanceAssetClass.os |
| Category (SCA/STATIC) | findingGroup.findings[].findingType.vulnerability.category |
| Scan Type | findingGroup.findings[].detectionMethod |
Viewing Assets and Findings in ETM
- Navigate to Enterprise TruRisk Management > Inventory.
- Go to Assets > All Assets to and use the filter
inventory.source: 'Qualys Container Security'
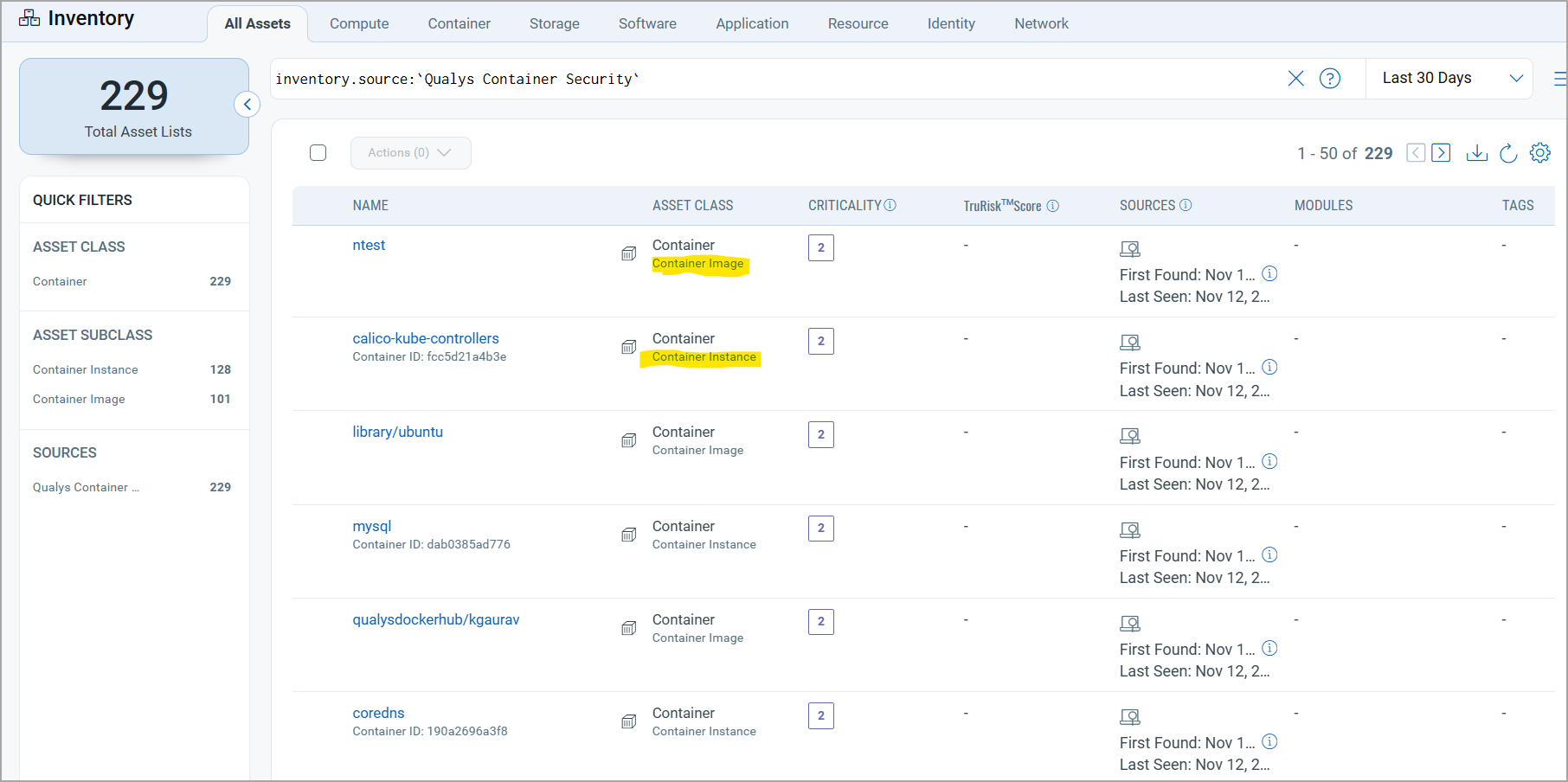
- Navigate to Risk Management > Findings > Vulnerability.
- Use filter: inventory .source:'Qualys Container Security’ and asset.subclass:'container-image'
Connector States
A successfully configured connector goes through the lifecycle states below.
| Registered | The connector is successfully created and registered to fetch data from the vendor. |
| Scheduled | The connector is scheduled to execute a connection with the vendor. |
| Processing | A connection is executed and the connector is fetching the asset and findings data. |
| Processed | The connector has successfully fetched the assets; it may still be under process of fetching findings. The Processed state indicates the connector is configured and importing assets and findings. This process may take up to 2 hours for completion. Once it is done, you can find the imported data in Enterprise TruRisk Management (ETM). |