JFrog Artifactory & Xray Connector
Security teams operating in software-driven environments often lack visibility into vulnerabilities embedded within the artifacts, packages, and container images that make up their software supply chain. The JFrog Artifactory and Xray Connector brings that visibility into Qualys Enterprise TruRisk Management by ingesting Artifactory inventory & software composition analysis findings from Xray's binary-level scans into a centralized risk platform. This allows practitioners to correlate application-layer vulnerabilities discovered in build artifacts and container images with the broader asset inventory already tracked in Qualys ETM. By consolidating software supply chain risk alongside cloud and endpoint security data, security teams can prioritize remediation based on true organizational risk rather than managing findings in isolation across separate toolchains.
Qualys ETM is compatible with JFrog Artifactory and JFrog Xray. JFrog is not affiliated with or endorsing this integration.
Connector Details
The following table provides a comprehensive overview of what the JFrog Artifactory & Xray Connector supports.
|
Vendor |
JFrog |
|
Product Name |
JFrog Artifactory & JFrog Xray (JFrog Security Essentials) |
|
Connector Category |
Application Security |
|
Asset Types Supported |
Code Repository, Container images (Docker) |
|
Finding Types Supported |
Yes |
|
Supported Version & Type |
SaaS (Latest) |
|
Integration Method |
API Integration (REST) |
|
Direction |
Unidirectional (JFrog Artifactory & Xray to Qualys) |
|
Incremental Sync (Delta) |
Not Supported |
|
Import of Installed Software |
Not Supported |
|
Import of Source Tags |
Not Supported |
|
Filters / Filter Query |
Not Supported |
Connection Settings
User Roles and Permissions
The JFrog Artifactory & Xray Connector requires an access token with administrative scope to retrieve asset and vulnerability data from Artifactory and Xray APIs.
To generate an access token in JFrog:
- Log in to your JFrog instance.
- Navigate to Administration > User Management > Access Tokens.
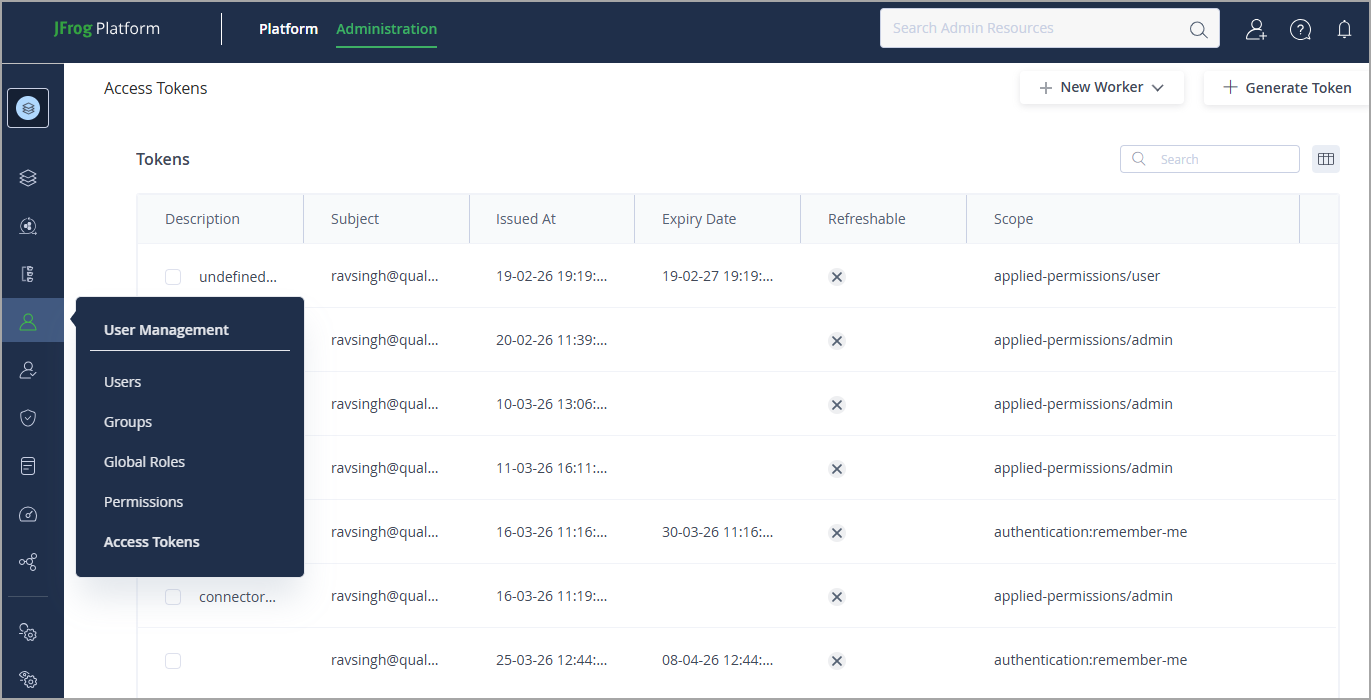
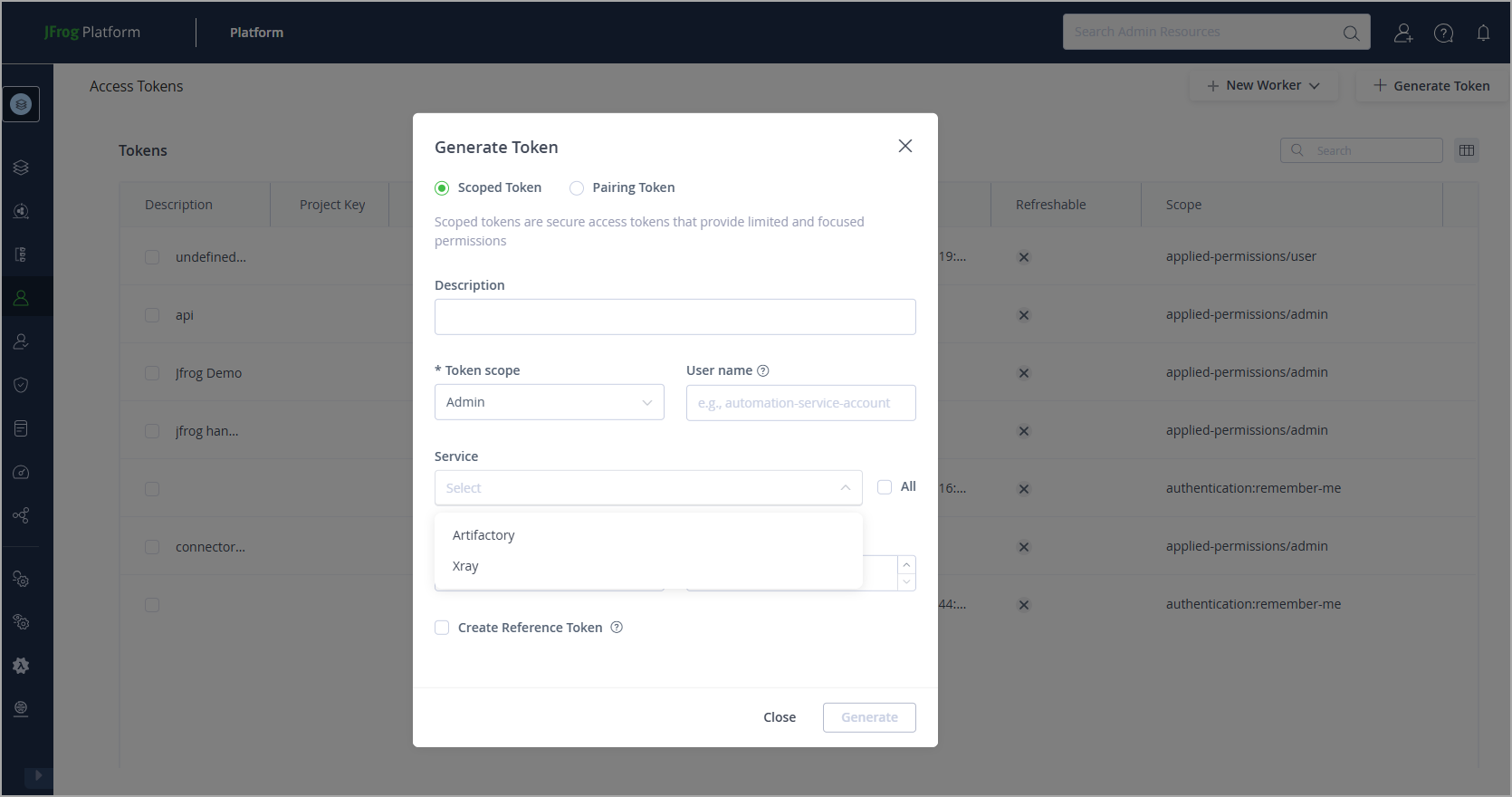
- Click Generate Token.
- Provide a token description and set the expiry as required.
- Set Token Scope to Admin.
- Under Services, select All or select both Artifactory and Xray.
- Click Generate and copy the token value. This value is shown only once.
The following permission is required:
| Entity Type | Required Permission |
|---|---|
| Access Token | Admin |
Authentication Details
Provide the following credentials in the connector configuration screen:
| Name | Key | Type | Description |
|---|---|---|---|
| Domain Name | domainName |
String | Base URL of the JFrog instance. Example: https://yourcompany.jfrog.io |
| API Token | password |
Encrypted | Access token generated in JFrog with Admin scope |
Connector Configuration
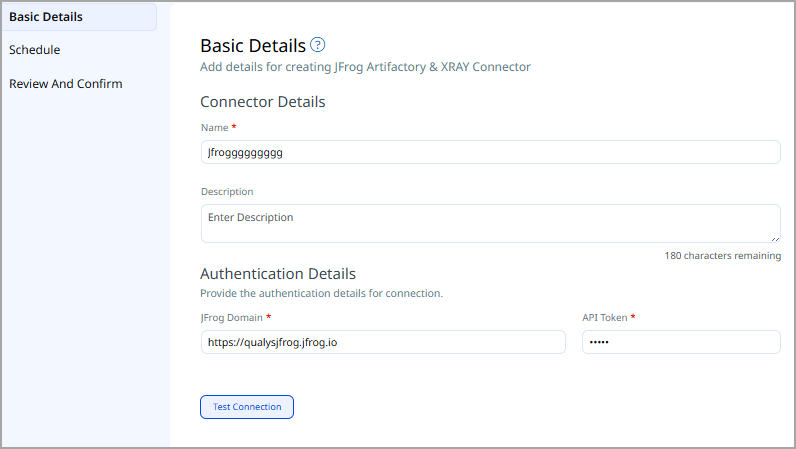
Basic Details
- Log in to Qualys ETM.
- Navigate to Connectors > Integration tab and locate the JFrog Artifactory & Xray Connector from the Connector Marketplace.
- Next, to the JFrog connector tile, click Manage from the ellipses menu.
- Provide a Name and Description for the connector.
- Select the supported findings type: Vulnerability / Host Asset.
- Enter the Domain Name and API Token.
Mapping Details
Data Model
The JFrog Artifactory & Xray Connector provides out-of-the-box data model mappings for the following asset types: container images (Docker) and binary repositories. Vulnerability findings are supported for container image assets. View the models in ETM to see all supported fields.
Transform Maps
Default transform maps are provided for each asset and findings type. Transform maps can be created or cloned to customize field transformations.
- Click Create New to add a new transform map.
- Provide a Transform Map Name, select a Source Data Model, and select a Target Data Model.
- Save the map.
- Alternatively, use Clone from the quick menu to copy and adjust an existing default transform map.
Data Model Mapping – Container Image (Docker Image) Asset Transformation
| Source Field | Target Field |
|---|---|
|
container-image |
asset.assetHeader.assetTypeName |
|
imageName |
asset.assetDetail.name |
|
IMAGE_DIGEST |
asset.assetDetail.containerImageAssetClass.digestType |
|
imageRegistry |
asset.assetDetail.containerImageAssetClass.registry |
|
imageRepository |
asset.assetDetail.containerImageAssetClass.repository |
|
imageName |
asset.assetDetail.containerImageAssetClass.name |
|
imageTag |
asset.assetDetail.containerImageAssetClass.tag |
|
blobConfig.architecture |
asset.assetDetail.containerImageAssetClass.architecture |
|
config.digest |
asset.assetDetail.containerImageAssetClass.digest |
|
storageManifest.checksums.sha256 |
asset.assetDetail.containerImageAssetClass.manifestDigest |
|
ImageSize |
asset.assetDetail.containerImageAssetClass.sizeInBytes |
|
blobConfig.created |
asset.assetDetail.containerImageAssetClass.creationDate |
|
layers[].digest |
asset.assetDetail.containerImageAssetClass.layers[].digest |
|
layers[].size |
asset.assetDetail.containerImageAssetClass.layers[].sizeInBytes |
|
evalExternalId |
asset.assetHeader.externalAssetId |
|
evalVendorAssetId |
asset.assetHeader.vendorAssetId |
|
storageManifest.downloadUri |
asset.assetDetail.typedAttributes.jfrog_artifactory_manifestUrl |
|
storageManifest.createdBy |
asset.assetDetail.typedAttributes.jfrog_artifactory_createdBy |
|
storageManifest.modifiedBy |
asset.assetDetail.typedAttributes.jfrog_artifactory_modifiedBy |
|
blobConfig.config.Cmd |
asset.assetDetail.untypedAttributes.jfrog_container_cmd |
|
blobConfig.config.Env |
asset.assetDetail.untypedAttributes.jfrog_container_env |
|
blobConfig.config.WorkingDir |
asset.assetDetail.typedAttributes.jfrog_container_workingDir |
|
blobConfig.os |
asset.assetDetail.typedAttributes.jfrog_container_os |
|
blobConfig.docker_version |
asset.assetDetail.typedAttributes.jfrog_container_dockerVersion |
|
blobConfig.rootfs |
asset.assetDetail.untypedAttributes.jfrog_container_uncompressed_layers |
|
blobConfig.history |
asset.assetDetail.untypedAttributes.jfrog_container_history |
Data Model Mapping – Binary Repository (Application) Asset Transformation
| Source Field | Target Field |
|---|---|
|
(constant) "binary-repository" |
asset.assetHeader.assetTypeName |
|
key |
asset.assetHeader.externalAssetId |
|
key |
asset.assetHeader.vendorAssetId |
|
key |
asset.assetDetail.name |
|
packageType |
asset.assetDetail.repositoryAssetClass.repositoryPackageType |
|
url |
asset.assetDetail.repositoryAssetClass.repoUrl |
|
description |
asset.assetDetail.typedAttributes.jfrog_artifact_description |
|
type |
asset.assetDetail.typedAttributes.jfrog_artifact_type |
Data Model Mapping – Container Image Vulnerability Transformation
| Source Field | Target Field |
|---|---|
|
container-image |
asset.assetHeader.assetTypeName |
|
imageName |
asset.assetDetail.name |
|
vulnerabilities[].severity |
findingGroup.findings[].severity |
|
evalExternalId |
asset.assetHeader.externalAssetId |
|
evalVendorAssetId |
asset.assetHeader.vendorAssetId |
|
imageRegistry |
asset.assetDetail.containerImageAssetClass.registry |
|
imageRepository |
asset.assetDetail.containerImageAssetClass.repository |
|
imageName |
asset.assetDetail.containerImageAssetClass.name |
|
imageTag |
asset.assetDetail.containerImageAssetClass.tag |
|
dockerManifest.config.digest |
asset.assetDetail.containerImageAssetClass.imageDigest |
|
dockerManifest.layers[].digest |
asset.assetDetail.containerImageAssetClass.layers[].digest |
|
dockerManifest.layers[].size |
asset.assetDetail.containerImageAssetClass.layers[].sizeInBytes |
|
dockerManifest.config.size |
asset.assetDetail.containerImageAssetClass.sizeInBytes |
|
storageManifest.checksums.sha256 |
asset.assetDetail.containerImageAssetClass.manifestDigest |
|
(date_format) storageManifest. |
asset.assetDetail.containerImageAssetClass.creationDate |
|
storageManifest.downloadUri |
asset.assetDetail.typedAttributes.jfrog_artifactory_manifestUrl |
|
storageManifest.createdBy |
asset.assetDetail.typedAttributes.jfrog_artifactory_createdBy |
|
storageManifest.modifiedBy |
asset.assetDetail.typedAttributes.jfrog_artifactory_modifiedBy |
|
vulnerabilities[].externalFindingId |
findingGroup.findings[].externalFindingId |
|
vulnerabilities[].cve |
findingGroup.findings[].name |
|
vulnerabilities[].summary |
findingGroup.findings[].description |
|
vulnerabilities[].severity |
findingGroup.findings[].sourceSeverity |
|
vulnerabilities[].cve |
findingGroup.findings[].findingType.vulnerability.cveId |
|
vulnerabilities[].cwe |
findingGroup.findings[].findingType.vulnerability.cweIds |
|
vulnerabilities[].cwe |
findingGroup.findings[].findingType.vulnerability.cweId |
|
vulnerabilities[].cvss_v3 |
findingGroup.findings[].findingType.vulnerability.cvss.cvss3Base |
|
vulnerabilities[].created |
findingGroup.findings[].firstFoundOn |
|
vulnerabilities[].findingDetectionUrl |
findingGroup.findings[].findingDetectionURL |
|
vulnerabilities[].extended_information. |
findingGroup.findings[].solutionRecommendation |
|
vulnerabilities[].extended_information. |
findingGroup.findings[].attributes.jfrog_fullDescription |
|
vulnerabilities[].extended_information. |
findingGroup.findings[].attributes.jfrog_shortDescription |
|
vulnerabilities[].extended_information. |
findingGroup.findings[].attributes.jfrog_researchSeverity |
|
vulnerabilities[].provider |
findingGroup.findings[].attributes.jfrog_provider |
|
vulnerabilities[].impact_path |
findingGroup.findings[].attributes.jfrog_impactPath |
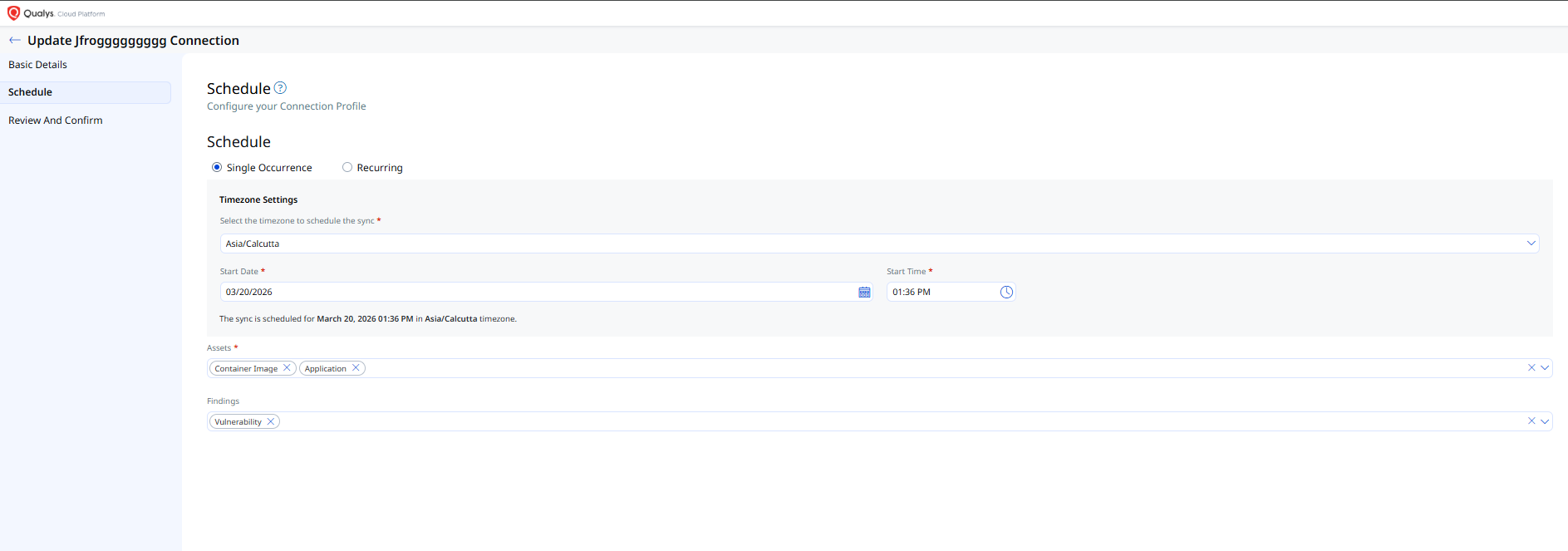
Schedule
Schedules control the execution of the connector, including scheduling and the data types that are synchronized.
- Click + to add a new profile.
- Provide a Name and Description.
- Select the required Transform Map.
- Select the findings type: Asset and/or Vulnerability.
- Set Status to Active or Inactive.
- Configure a Schedule: select Single Occurrence or Recurring, then set the start and end date and time.
- Click Next to proceed.
How Does a Connection Work?
The JFrog Artifactory & Xray Connector executes on a configured schedule or on demand, based on the active profile. On each execution, the connector authenticates to the JFrog REST API using the configured domain and access token, fetches the list of repositories and container images, retrieves vulnerability data from JFrog Xray for each asset, applies the configured transform map, and imports the results into ETM.
Each execution performs a full pull. Incremental (delta) synchronization is not supported. The connector transitions through the following states during execution:
- Registered – The connector has been created and registered to fetch data from JFrog.
- Scheduled – The connector is queued for its next execution.
- Processing – The connector is actively fetching asset and findings data from JFrog.
- Processed – Asset data has been fetched successfully. Findings processing may still be in progress; allow additional time for findings to appear in ETM.
The Processed state indicates the connector completed its asset fetch. Full import of assets and findings, particularly for large environments, may take up to 2 hours. Once complete, the imported data is available in ETM.
In the Connector screen, the configured connector will appear with the state Processed once execution completes.
Viewing Assets and Findings in ETM
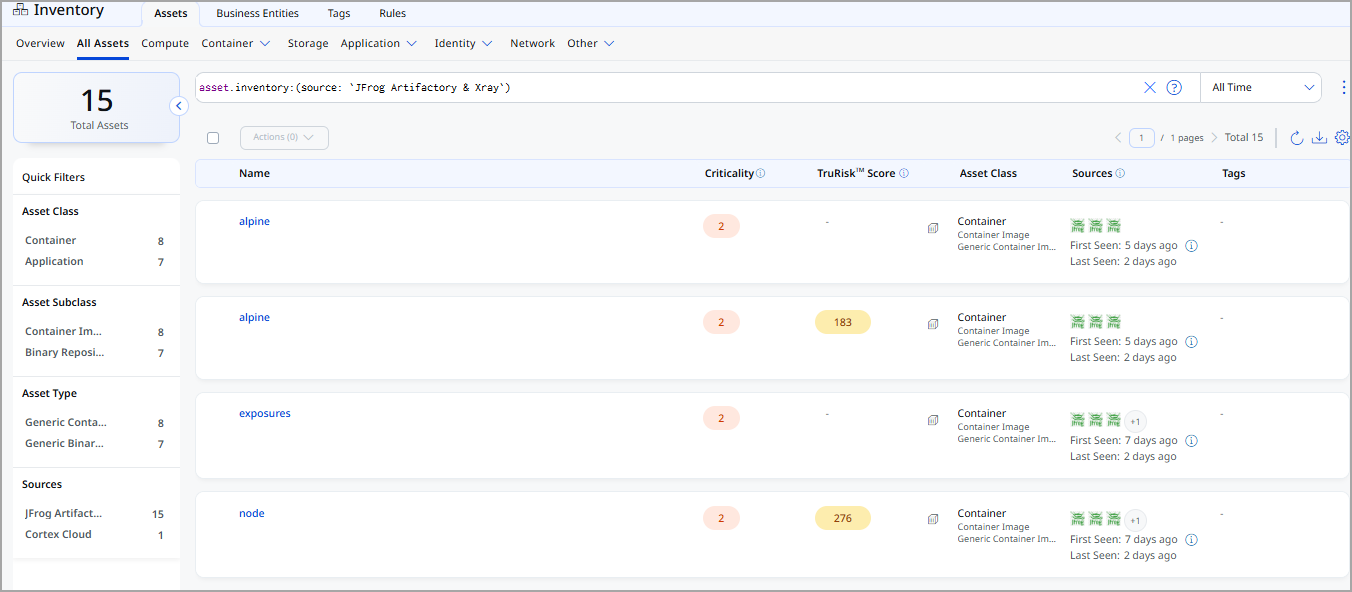
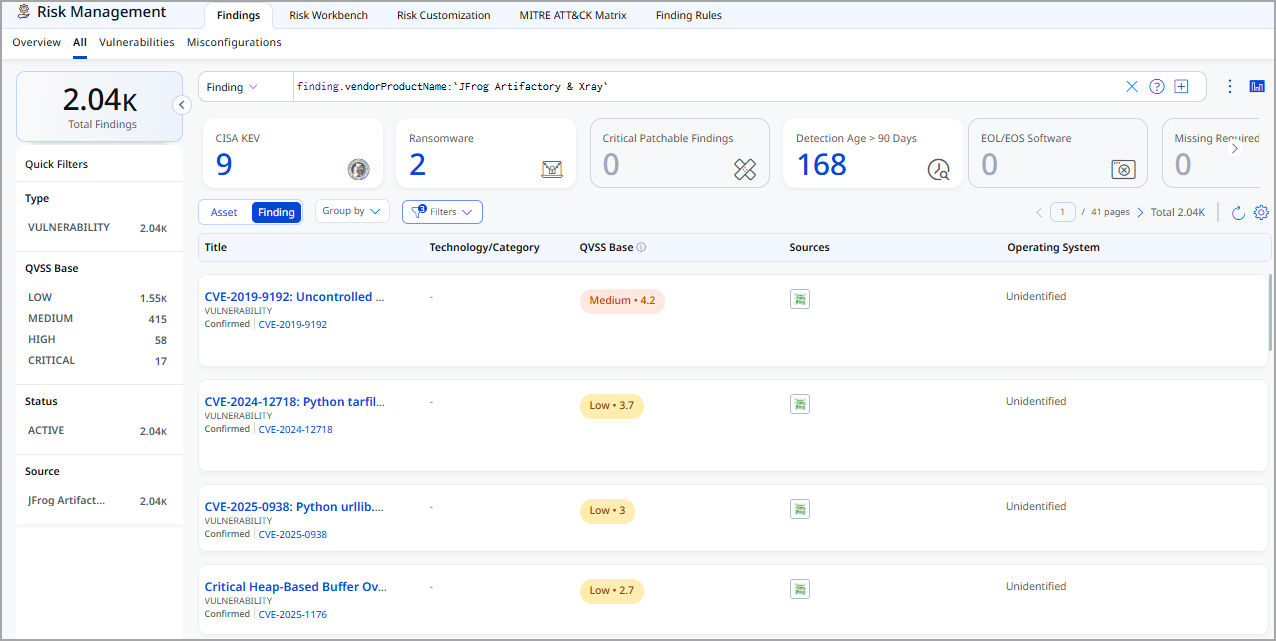
After a successful run, JFrog assets and findings appear in ETM as follows:
- Assets: Navigate to Inventory > Assets. Select the relevant asset type (for example, Container Image or Repository). Filter with
tags.name:"JFrog Artifactory & Xray"to list assets imported from this connector.
- Findings: Navigate to Risk Management > Findings > Vulnerability. Filter with
finding.vendorProductName:"JFrog Artifactory & Xray"to list vulnerability findings from this connector.
API Endpoints
The connector uses the following JFrog REST API endpoints to retrieve data.
|
Name |
Endpoint |
|
|---|---|---|
| Auth API | baseurl example https://qualysjfrog.jfrog.io | |
Fetch asset list |
https://qualysjfrog.jfrog.io/artifactory/api/repositories https://qualysjfrog.jfrog.io/artifactory/api/docker/${repoKey}/v2/${imageName}/blobs/${configDigest} |
|
Fetch asset details and vulns |
https://qualysjfrog.jfrog.io/xray/api/v1/summary/artifact' |