Okta Connector
The Okta Connector integrates identity data from Okta's Universal Directory into Qualys Enterprise TruRisk Management, enabling security teams to maintain a centralized inventory of users and groups. By synchronizing identity assets into the Unified Asset Inventory, security practitioners gain visibility into who has access to what resources and can correlate identity information with other security asset data. The connector supports delta pulls for efficient updates after the initial full synchronization, reducing the overhead of continuous identity reconciliation. This unified view helps security teams identify access control risks, enforce principle of least privilege, and respond more effectively to identity-related threats in cloud-first and hybrid environments where Okta serves as the primary identity provider.
Connector Details
The following table summarizes the capabilities and configuration characteristics of the Okta Connector.
|
Vendor |
Okta |
|
Product Name |
Okta |
|
Connector Category |
Identity & Access Managements |
|
Asset Types Supported |
Identity |
|
Finding Types Supported |
No |
|
Supported Version & Type |
v1.0.0 |
|
Integration Method |
API Integration (REST) |
|
Direction |
Unidirectional (Okta to Qualys) |
|
Incremental Sync (Delta) |
Supported |
|
Import of Installed Software |
Not Supported |
|
Import of Source Tags |
Not Supported |
|
Filters / Filter Query |
Not Supported |
Connection Settings
User Roles and Permissions
The Okta Connector uses an API token (SSWS) for authentication. OAuth is not supported for this connector. The admin account used to generate the API token must have the following permissions assigned via a custom role. To configure roles, go to Security > Admin > Roles in the Okta Admin Console, then assign the role to the API token owner.
OAuth-based authentication is not supported for this connector. Only SSWS API tokens are accepted.
|
Entity |
Required Permission |
Description |
|---|---|---|
|
Users |
|
Read user profiles and credentials (all users or scoped to groups). |
|
Groups |
|
Read groups and members (all or specific groups). |
|
Policies |
|
View policies. Requires Okta release 2025.05.0 or later. |
|
Applications |
|
Read applications and their members (all, type-specific, or a single app). |
|
Custom Roles |
|
View roles, resources, and role assignments. |
To generate an API token in Okta:
- Log in to the Okta Admin Console.
- Go to Security > API > Tokens.
- Click Create Token and provide a descriptive name.
- Copy the token value immediately — it is not shown again after the dialog is closed.
Authentication Details
Provide the following credentials in the connector configuration screen:
| Name | Key | Type | Description |
|---|---|---|---|
| Base URL | BaseURL |
String | The unique domain of your Okta organization (e.g., https://yourorg.okta.com). This acts as the root endpoint for all API requests. |
| API Token | API Token |
Encrypted | SSWS API token generated in the Okta Admin Console. Used to authorize all API requests made by the connector. |
Connector Configuration
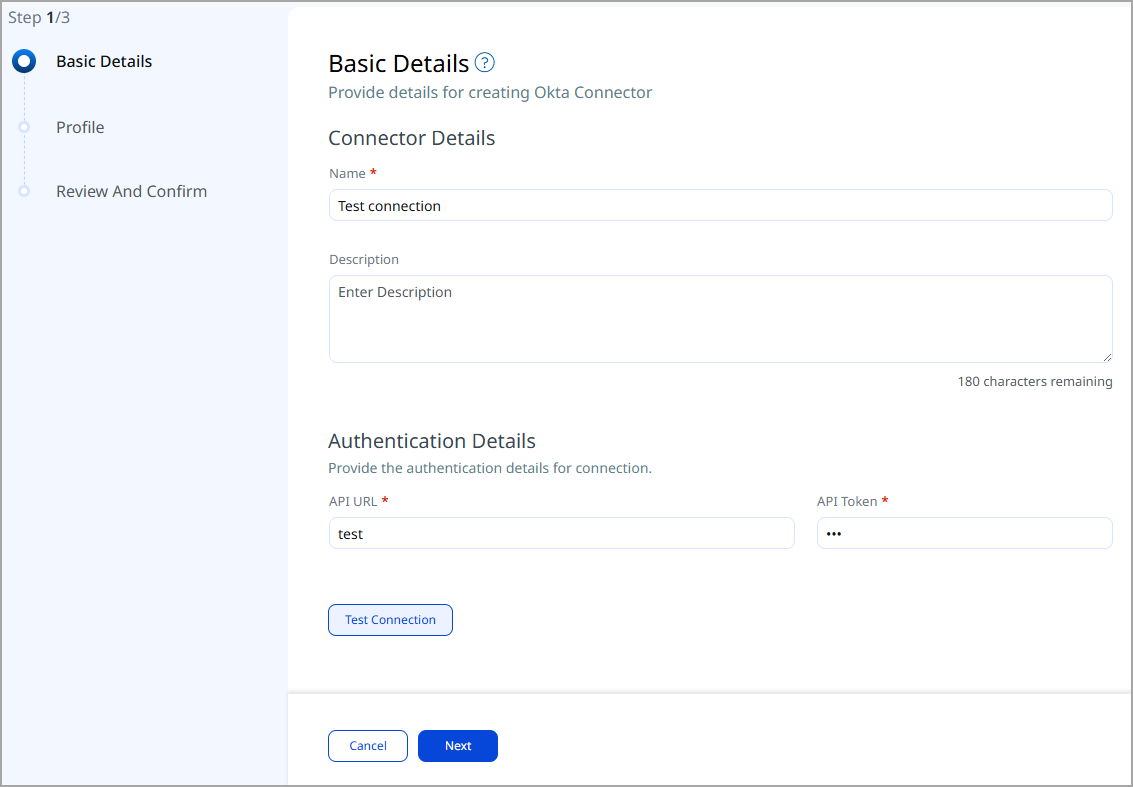
Basic Details
- Log in to Qualys ETM.
- Go to Connectors > Integration and locate the Okta Connector.
- Click Manage from the ellipsis menu.
- Provide a Name and Description for the connector.
- Enter the Base URL and API Token.
- Click Next to proceed to profile configuration.
Mapping Details
Data Model
The Okta Connector provides out-of-the-box data model mappings for identity asset types: Users, Groups, and Roles. No vulnerability finding mappings are provided. View the complete schema in ETM to understand all supported target fields.
Transform Maps
Default transform maps are provided for each asset type. You can create or clone maps to customize field transformations.
- Click Create New to add a new transform map.
- Provide a Transform Map Name, select a Source Data Model, and select a Target Data Model.
- Save the map.
- Alternatively, use Clone from the quick menu to copy and adjust an existing default transform map.
Data Model Mapping – Role Asset Transformation
|
Source Field |
Target Field |
|---|---|
|
id |
asset.assetHeader.externalAssetId (Required) |
|
id |
asset.assetHeader.vendorAssetId |
|
label |
asset.assetDetail.name |
|
id |
asset.assetDetail.roleAssetClass.id |
|
label |
asset.assetDetail.roleAssetClass.name |
|
label |
asset.assetDetail.roleAssetClass.displayName |
|
description |
asset.assetDetail.roleAssetClass.description |
|
permissions[].label |
asset.assetDetail.roleAssetClass.permissions[].id |
|
permissions[].label |
asset.assetDetail.roleAssetClass.permissions[].name |
|
created |
asset.assetDetail.sourceCreatedAt |
|
lastUpdated |
asset.assetDetail.sourceUpdatedAt |
|
permissions[].label |
asset.assetDetail.untypedAttributes.oktaRolePermissionLabels[] |
|
isCloneable |
asset.assetDetail.untypedAttributes.oktaRoleIsCloneable |
Data Model Mapping – User Asset Transformation
|
Source Field |
Target Field |
|---|---|
|
profile.login |
asset.assetHeader.externalAssetId (Required) |
|
id |
asset.assetHeader.vendorAssetId |
|
FUNCTION_PICKER |
asset.assetHeader.status |
|
id |
asset.assetDetail.userAssetClass.id |
|
FUNCTION_PICKER |
asset.assetDetail.userAssetClass.name |
|
FUNCTION_PICKER |
asset.assetDetail.name |
|
FUNCTION_PICKER |
asset.assetDetail.userAssetClass.status |
|
profile.email |
asset.assetDetail.userAssetClass.email |
|
profile.firstName |
asset.assetDetail.userAssetClass.firstName |
|
profile.lastName |
asset.assetDetail.userAssetClass.lastName |
|
FUNCTION_PICKER |
asset.assetDetail.userAssetClass.displayName |
|
activated |
asset.assetDetail.userAssetClass.activationDate |
|
lastLogin |
asset.assetDetail.userAssetClass.lastSuccessfulLoginAt |
|
passwordChanged |
asset.assetDetail.userAssetClass.passwordLastChangedAt |
|
FUNCTION_PICKER |
asset.assetDetail.userAssetClass.type |
|
created |
asset.assetDetail.sourceCreatedAt |
|
lastUpdated |
asset.assetDetail.sourceUpdatedAt |
|
memberOf[].id |
asset.assetRelations[].assetHeader.externalAssetId |
|
memberOf[].id |
asset.assetRelations[].assetHeader.vendorAssetId |
|
userEnrolledFactors[].factorType |
asset.assetDetail.untypedAttributes.oktaUserFactorTypes[] |
|
statusChanged |
asset.assetDetail.typedAttributes.oktaUserStatusChanged |
|
userRoleAssignments[].type |
asset.assetDetail.untypedAttributes.oktaUserRoleTypes[] |
|
userRoleAssignments[].assignmentType |
asset.assetDetail.untypedAttributes.oktaUserRoleAssignmentTypes[] |
|
profile.secondEmail |
asset.assetDetail.typedAttributes.oktaUserSecondEmail |
|
userEnrolledFactors[].provider |
asset.assetDetail.untypedAttributes.oktaUserEnrolledFactorsProviders[] |
|
type.id |
asset.assetDetail.typedAttributes.oktaUserTypeId |
Data Model Mapping – Group Asset Transformation
|
Source Field |
Target Field |
|---|---|
|
SCRIPT_BASE_FUNCTION |
asset.assetHeader.externalAssetId (Required) |
|
id |
asset.assetHeader.vendorAssetId |
|
profile.name |
asset.assetDetail.name |
|
created |
asset.assetDetail.sourceCreatedAt |
|
lastUpdated |
asset.assetDetail.sourceUpdatedAt |
|
id |
asset.assetDetail.groupAssetClass.id |
|
profile.name |
asset.assetDetail.groupAssetClass.name |
|
profile.name |
asset.assetDetail.groupAssetClass.displayName |
|
type |
asset.assetDetail.groupAssetClass.type |
|
profile.description |
asset.assetDetail.groupAssetClass.description |
|
hasRole[].id |
asset.assetRelations[].assetHeader.externalAssetId |
|
hasRole[].id |
asset.assetRelations[].assetHeader.vendorAssetId |
|
FUNCTION_PICKER |
asset.assetRelations[].assetHeader.status |
|
hasRole[].label |
asset.assetRelations[].assetDetail.name |
|
hasRole[].id |
asset.assetRelations[].assetDetail.roleAssetClass.id |
|
hasRole[].label |
asset.assetRelations[].assetDetail.roleAssetClass.name |
|
hasRole[].label |
asset.assetRelations[].assetDetail.roleAssetClass.displayName |
|
hasRole[].label |
asset.assetRelations[].assetDetail.roleAssetClass.description |
|
FUNCTION_PICKER |
asset.assetRelations[].assetDetail.roleAssetClass.type |
|
FUNCTION_PICKER |
asset.assetRelations[].assetDetail.roleAssetClass.scope |
|
hasRole[].created |
asset.assetRelations[].assetDetail.sourceCreatedAt |
|
hasRole[].lastUpdated |
asset.assetRelations[].assetDetail.sourceUpdatedAt |
|
FUNCTION_PICKER |
asset.assetRelations[].relationshipStatus |
|
profile.groupType |
asset.assetDetail.typedAttributes.oktaGroupProfileGroupType |
|
profile.samAccountName |
asset.assetDetail.typedAttributes.oktaGroupProfileSamAccountName |
|
lastMembershipUpdated |
asset.assetDetail.typedAttributes.oktaGroupLastMembershipUpdated |
|
profile.groupScope |
asset.assetDetail.typedAttributes.oktaGroupProfileGroupScope |
|
profile.dn |
asset.assetDetail.typedAttributes.oktaGroupProfileDN |
|
objectClass |
asset.assetDetail.untypedAttributes.oktaGroupObjectClass |
|
profile.windowsDomainQualifiedName |
asset.assetDetail.typedAttributes.oktaGroupProfileWindowsDomainQualifiedName |
Policies - Transformation map:
|
Source Field |
Target Field |
|---|---|
| * | thirdPartyObject.content.& |
Applications - Transformation map:
|
Source Field |
Target Field |
|---|---|
| * | thirdPartyObject.content.& |
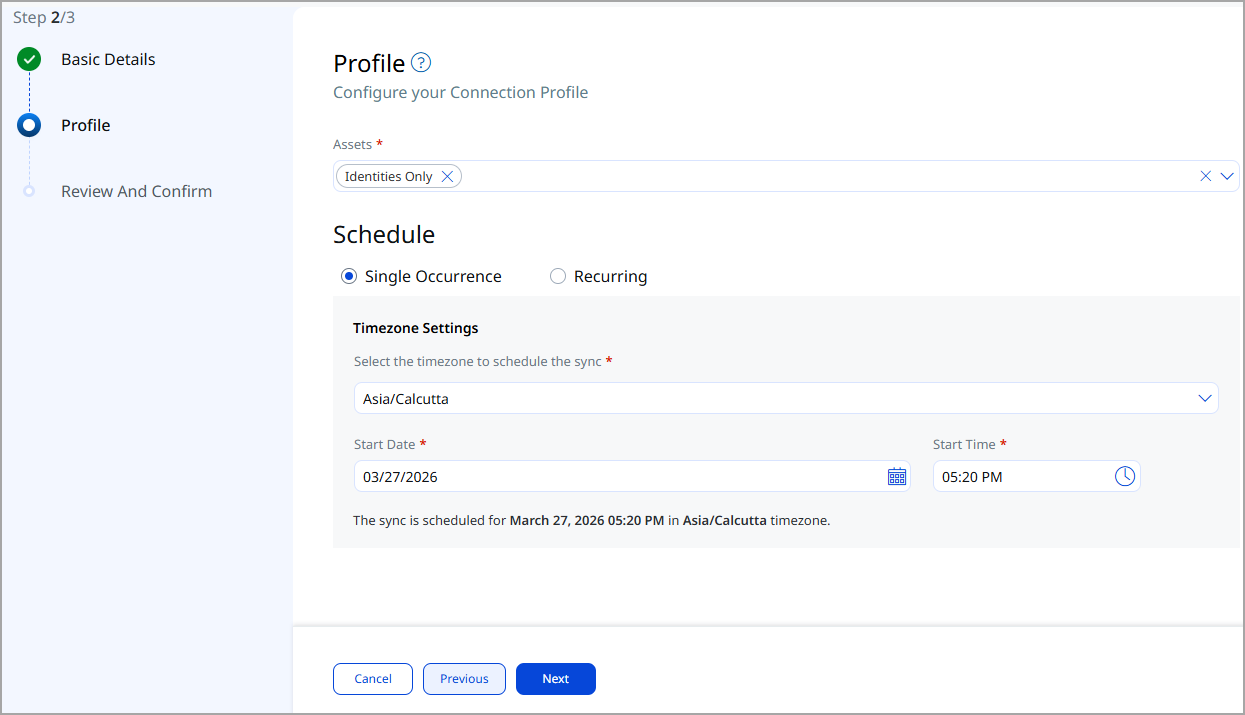
Profiles
Profiles control when and how the connector executes. Each profile is associated with one or more transform maps and defines the asset scope and schedule.
- Click + to add a new profile.
- Provide a Name and Description.
- Select the required Transform Map.
- Set the Asset Target: select Core Repo or Generic Application as appropriate.
- Set Status to Active or Inactive.
- Configure a Schedule: select Single Occurrence or Recurring, then set start and end dates and times.
- Click Next to proceed.
How Does a Connection Work?
The Okta Connector executes on schedule or on demand based on the configured profile. On first execution, a full pull of all configured Okta asset types is performed. On subsequent executions, only delta changes are fetched, reducing import volume and processing time.
The connector fetches data from Okta via REST API, applies the configured transform map, and imports identity assets into ETM. A successfully configured connector transitions through the following states:
- Registered — The connector is created and registered to fetch data from Okta.
- Scheduled — The connector is queued and scheduled for execution.
- Processing — A connection is active and the connector is retrieving asset data.
- Processed — The connector has completed data retrieval and import into ETM.
The full import process, including asset correlation, may take up to 2 hours to complete depending on the volume of identity data in the Okta organization.
Viewing Assets in ETM
After a successful run, Okta identity assets appear in ETM's Inventory:
- Assets: Go to Inventory > Assets. Filter with
tags.name:"Okta".
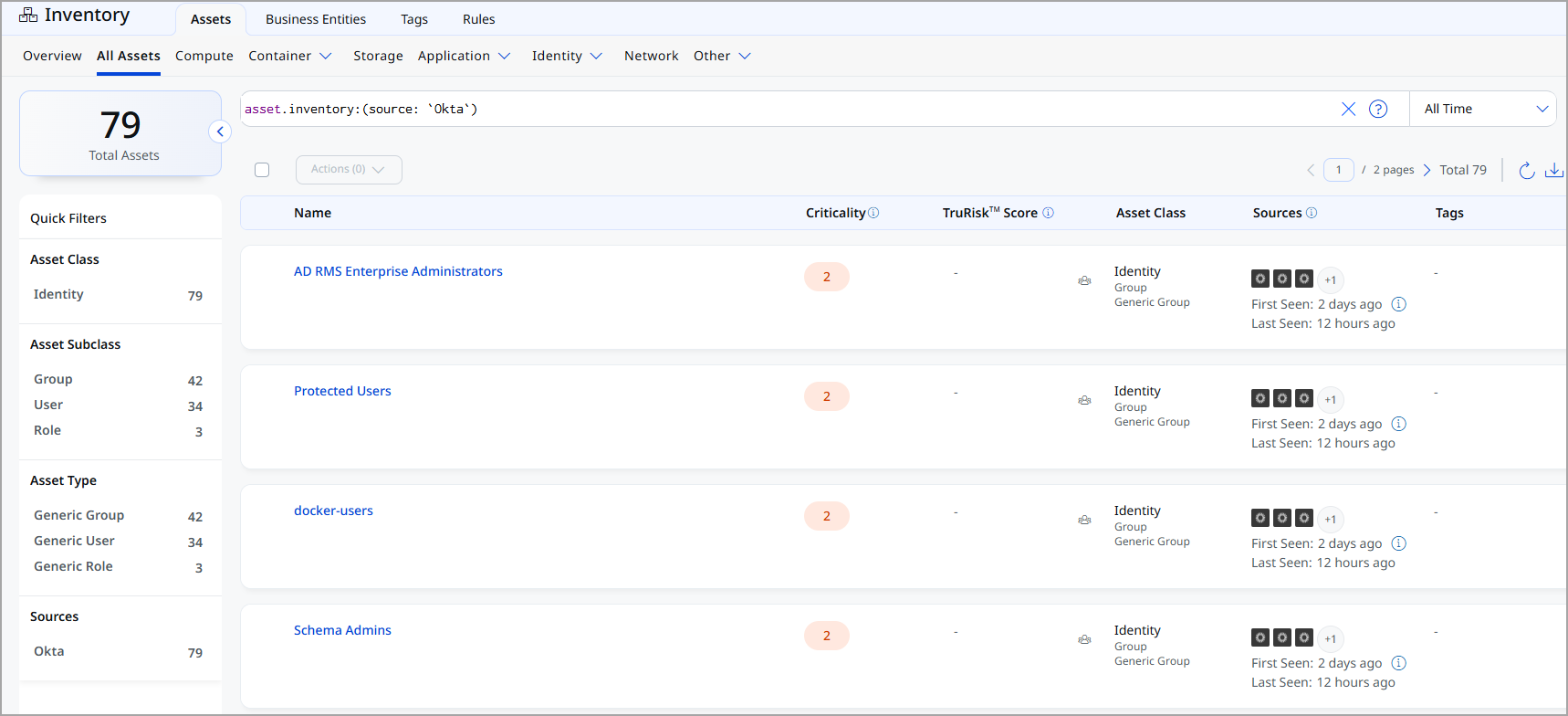
The Okta Connector does not import vulnerability findings. The Findings view is not applicable for this connector.
API Endpoints
The connector uses the following Okta REST API endpoints to retrieve identity asset data:
| API Function | Endpoint |
|---|---|
|
List Users API |
https://qualys-ssf-admin.oktapreview.com/api/v1/users |
|
List Groups API |
https://qualys-ssf-admin.oktapreview.com/api/v1/groups |
|
List Custom Role API |
https://qualys-ssf-admin.oktapreview.com/api/v1/iam/roles |
|
List of Applications |
https://qualys-ssf-admin.oktapreview.com/api/v1/apps?limit=10 |
|
List of Policies |
https://qualys-ssf-admin.oktapreview.com/api/v1/policies?limit=200&type=OKTA_SIGN_ON |