Orca Cloud Security Connector
The Orca Cloud Security Connector bridges Orca's CNAPP platform with Qualys' Enterprise TruRisk Platform by automatically ingesting cloud asset inventory and vulnerability findings through scheduled API calls.
The connector covers a range of workload types including Compute, Container Instances, Container Images, and Serverless environments. Security teams gain unified visibility across multi-cloud environments by consolidating Orca's agentless detection data with Qualys' risk scoring capabilities into a single asset inventory.
This integration removes the need for manual data translation between platforms, allowing SecOps teams to focus on remediating the most critical vulnerabilities rather than managing separate vendor consoles. By delivering enhanced risk context and prioritization through Qualys TruRisk, the connector supports more efficient resource allocation across modern cloud workloads.
Connector Details
Here is a comprehensive overview of what the Orca Cloud Security connector supports.
| Vendor | Orca |
| Product Name | Orca Cloud Security |
| Category | Cloud Security |
| Asset Types Supported |
Compute: AwsEc2Instance, GcpVmInstance, OciVMInstance Container Instances: AWS Container, GCP CloudRun Container Images: GCPGcrImage, AWSEcrImage, AzureAcrImage Serverless: AWSLambdaFunction, GCPCloudFunction, AzureFunction |
| Findings Supported | Yes |
| Supported Version & Type | SaaS (Latest) |
| Integration Type | API Integration (REST / GraphQL) |
| Direction | Unidirectional (Orca to Qualys) |
| Incremental Sync (Delta) | Not Supported |
| Import of Installed Software | Not Supported |
| Import of Source Tags | Not Supported |
Connection Settings
User Roles and Permissions
To retrieve assets and vulnerability findings, the Orca Cloud Security connector uses the Orca Serving-layer APIs.
You must generate an API token with sufficient permissions before configuring the connector.
- You can use the built-in Viewer role provided by Orca.
- Alternatively, you can create a custom role with the minimum permissions required to access: HostAssets and VulnerabilitiesV2.
Reference: Default Roles and Permissions (Orca)
How to create an API token for Orca Cloud Security connector:
- Login to Orca account using the domain URL specific to your region.
- Navigate to Settings > Users & Permissions > API.
- Click Create API Token.
- Define the following API token settings:
- Name: Enter a unique name for the API token.
- Description: Describe the API token.
- Never Expire: To create a token that is permanently valid, select this checkbox.
- Expiration: Set the token's expiration date. This option is available if the Never Expire checkbox is deselected. The expired tokens are still available but invalid, and the integrations that use them do not work.
- Service Token: If applicable, select this checkbox to indicate that the created token is a service token.
Service tokens are not linked to a specific user. They are scoped according to the user who created them. Even if the user is removed, service tokens can still be used, but they are invalid for the organization. - Role: Select the role that best defines the permissions required by the token.
See Default Roles and Permissions (Requires Orca support login).
You need the following permissions before creating the API token.
Authentication Details
Provide the following values on the connector configuration screen.
| Name | Key | Type | Description |
|---|---|---|---|
| API Token | api_token |
Encrypted String | API token generated from Orca Cloud Security |
| Domain | domain |
String | Orca API domain based on region (for example: api.orcasecurity.io, app.eu.orcasecurity.io) |
Use the domain based on your region. See supported domains below:
|
US (Default) |
https://api.orcasecurity.io/api/ |
|
Europe |
https://app.eu.orcasecurity.io/api/ |
|
Australia |
https://app.au.orcasecurity.io/api/ |
|
India |
https://app.in.orcasecurity.io/api/ |
|
Israel |
https://api.il.orcasecurity.io/api/ |
|
Brazil (SA) |
https://api.sa.orcasecurity.io/api/ |
Connector Configuration
Basic Details
- Log in to Qualys ETM.
- Navigate to Connectors > Integration.
- Locate the Orca Cloud Security Connector and click Manage.
- Provide a connector Name and Description.
- Enter the required authentication details.
Schedule
Schedules control when the connector executes and what data is ingested.
- Select the execution frequency.
- Select the supported Asset Types.
- Select Vulnerability findings for ingestion.
Asset Identification Rules
Identification Rules are predefined precedence rules provided by Qualys CSAM. These rules determine how imported findings are associated with assets in ETM.
Identification Rules apply only to compute assets. Other asset classes are not affected.
You can proceed without modifying these rules.
How Does the Connection Work?
On schedule (or on demand), the Orca Cloud Security connector retrieves supported cloud asset classes and vulnerability findings from Orca and imports them into ETM Unified Asset Inventory.
Each execution performs a full data pull.
In the Connector screen, the connector transitions through the following states:
- Registered – Connector is created.
- Scheduled – Connector is queued for execution.
- Processing – Assets and findings are being fetched.
- Processed – Assets are imported; findings may continue processing.
The full ingestion process may take several hours depending on data volume.
Viewing Assets and Findings in ETM
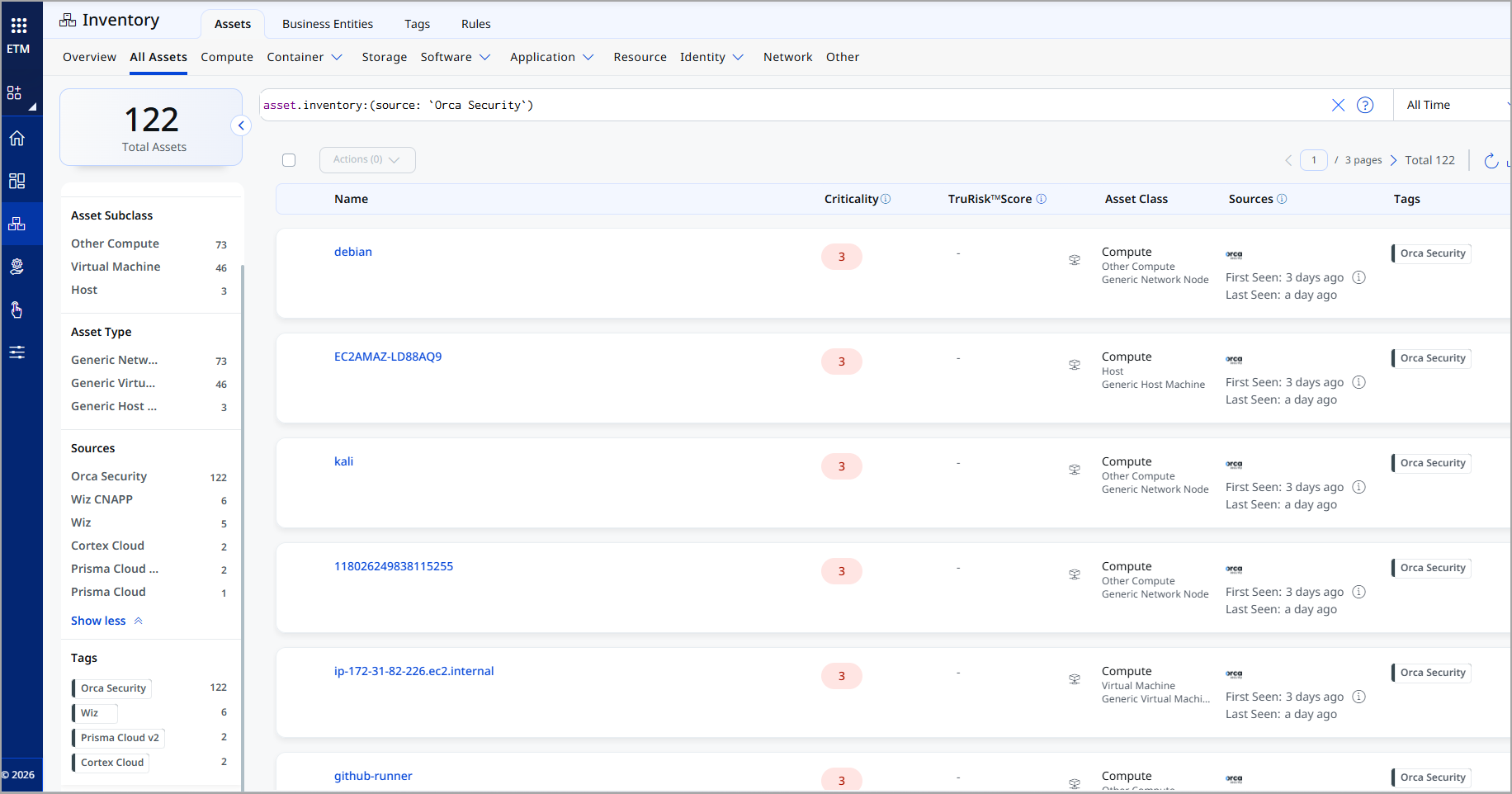
After ingestion, view Orca Cloud assets in ETM Unified Asset Inventory.
- Assets: Enterprise TruRisk Management > Inventory > Assets > All Assets.
Use the tag or asset filter:tags.name:"Orca Security"orasset.inventory:"Orca Cloud Security".
- Findings: Enterprise TruRisk Management > Risk Management > Findings > Vulnerability.
Use the vendor filter:findings.vendorProductname:".Orca Cloud Security"
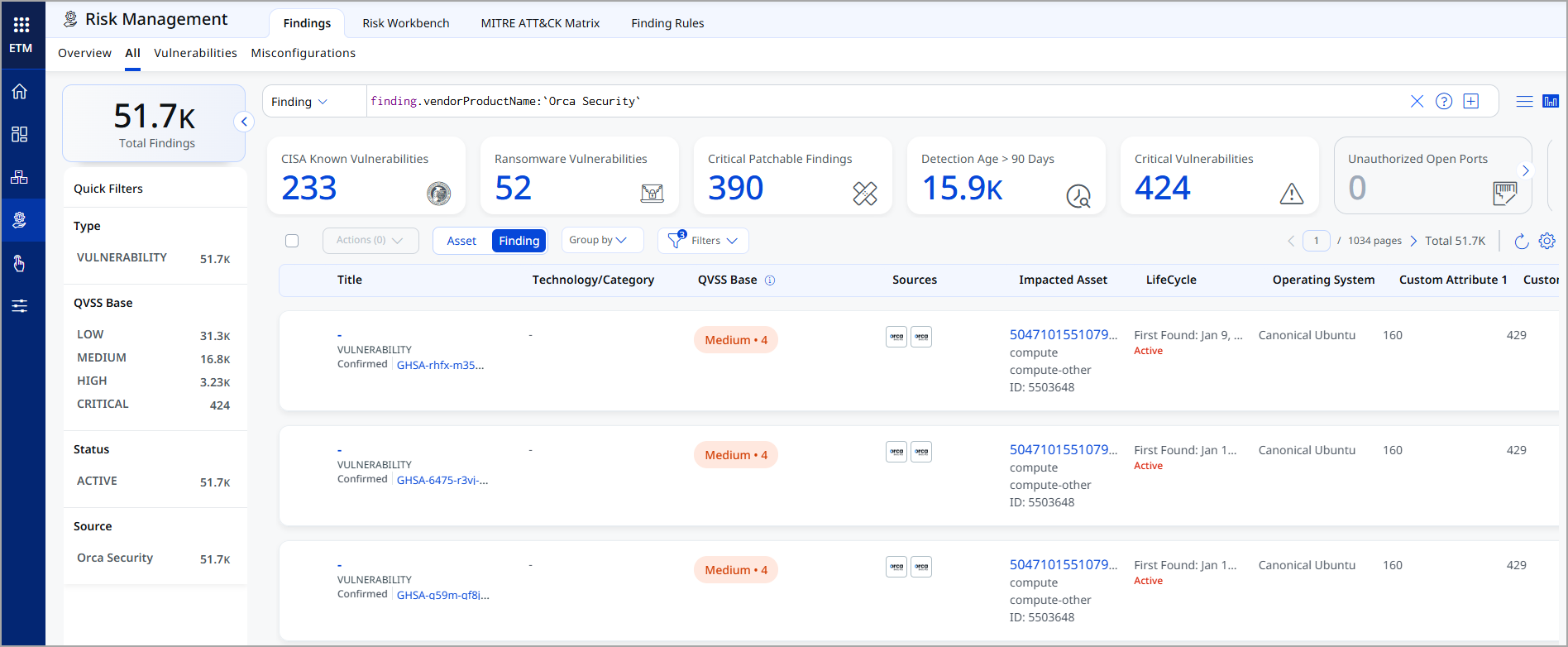
You can click on any findings to open a detailed view.
Orca Cloud Security - Transformation Map
The default transformation map for different asset classes, configured for the Orca Cloud Security connector is fetched from the database and utilized during the execution of the connector profile to perform data transformation.
Compute
AWS EC2 instanceAWS EC2 instance
| SourceField | TargetField |
|---|---|
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| data.Tags.value.Name | asset.assetDetail.externalTags[].value |
| data.Region.value | asset.assetDetail.cloudInfo.region |
| data.Memory.value | asset.assetDetail.computeAssetClass.memory.sizeInBytes |
| data.InstanceType.value | asset.assetDetail.computeAssetClass.cloudInstance.type |
| data.InstanceId.value | asset.assetDetail.computeAssetClass.cloudInstance.id |
| data.Hostname.value | asset.assetDetail.computeAssetClass.cloudInstance.hostname |
| data.PublicIpAddress.value | asset.assetDetail.computeAssetClass.cloudInstance.publicIpv4Address |
| data.PrivateIpAddress.value | asset.assetDetail.computeAssetClass.cloudInstance.privateIpv4Address |
| data.State.value | asset.assetDetail.computeAssetClass.cloudInstance.state |
| asset_unique_id | asset.assetDetail.typedAttributes.asset_unique_id |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.Hostname.value | asset.assetDetail.hostIdentity.fqdn |
| data.Hostname.value | asset.assetDetail.hostIdentity.hostname |
| data.PrivateIps.value[] | asset.assetDetail.network[].ipv4Addresses[] |
| data.Hostname.value | asset.assetDetail.network[].hostname |
| data.RiskLevel.value | asset.assetDetail.typedAttributes.RiskLevel |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.CloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.CloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.CloudAccount.data.CloudProvider.value (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| data.FirstSeen.value (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| data.LastSeen.value (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
GCP VM InstanceGCP VM Instance
| SourceField | TargetField |
|---|---|
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| type | asset.assetHeader.assetTypeName |
| data.CanIpForward.value | asset.assetDetail.typedAttributes.CanIpForward |
| data.DeletionProtection.value | asset.assetDetail.typedAttributes.DeletionProtection |
| data.IsInternetFacing.value | asset.assetDetail.typedAttributes.IsInternetFacing |
| data.FirstSeen.value (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| data.LastSeen.value (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| data.Region.value | asset.assetDetail.cloudInfo.region |
| data.Memory.value | asset.assetDetail.computeAssetClass.memory.sizeInBytes |
| data.ImageId.value | asset.assetDetail.computeAssetClass.cloudInstance.imageId |
| data.InstanceType.value | asset.assetDetail.computeAssetClass.cloudInstance.type |
| data.Hostname.value | asset.assetDetail.computeAssetClass.cloudInstance.hostname |
| data.Hostname.value | asset.assetDetail.hostIdentity.hostname |
| data.State.value | asset.assetDetail.computeAssetClass.cloudInstance.state |
| data.PublicIpAddress.value | asset.assetDetail.computeAssetClass.cloudInstance.publicIpv4Address |
| data.PrivateIpAddress.value | asset.assetDetail.computeAssetClass.cloudInstance.privateIpv4Address |
| data.PrivateIps.value[] | asset.assetDetail.network[].ipv4Addresses[] |
| data.Hostname.value | asset.assetDetail.network[].hostname |
| asset_unique_id | asset.assetDetail.typedAttributes.asset_unique_id |
| data.Tags.value.Name | asset.assetDetail.externalTags[].value |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.OrcaScore.value | asset.assetDetail.typedAttributes.OrcaScore |
| data.RiskLevel.value | asset.assetDetail.typedAttributes.RiskLevel |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.CloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.cloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.CloudAccount.data.CloudProvider.value (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
OCI VM InstanceOCI VM Instance
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| data.IsInternetFacing.value | asset.assetDetail.typedAttributes.IsInternetFacing |
| data.HasSensitiveKeys.value | asset.assetDetail.typedAttributes.HasSensitiveKeys |
| data.FirstSeen.value (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| data.LastSeen.value (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| data.Region.value | asset.assetDetail.cloudInfo.region |
| data.AvailabilityZones.value | asset.assetDetail.cloudInfo.availabilityZone |
| data.ImageId.value | asset.assetDetail.computeAssetClass.cloudInstance.imageId |
| data.InstanceId.value | asset.assetDetail.computeAssetClass.cloudInstance.id |
| data.InstanceType.value | asset.assetDetail.computeAssetClass.cloudInstance.type |
| data.Hostname.value | asset.assetDetail.computeAssetClass.cloudInstance.hostname |
| data.Hostname.value | asset.assetDetail.hostIdentity.fqdn |
| data.Hostname.value | asset.assetDetail.hostIdentity.hostname |
| data.Hostname.value | asset.assetDetail.network[].hostname |
| data.State.value | asset.assetDetail.computeAssetClass.cloudInstance.state |
| data.PublicIps.value | asset.assetDetail.network[].publicIpv4Addresses |
| data.PrivateIps.value | asset.assetDetail.network[].ipv4Addresses |
| data.VCpuCount.value | asset.assetDetail.processor.numberOfCpu |
| data.Memory.value | asset.assetDetail.computeAssetClass.memory.sizeInBytes |
| data.DistributionVersion.value | asset.assetDetail.operatingSystem.version |
| data.DistributionName.value | asset.assetDetail.operatingSystem.publisher |
| data.TotalDisksBytes.value | asset.assetDetail.computeAssetClass.storage[].totalSizeInBytes |
| asset_unique_id | asset.assetDetail.typedAttributes.asset_unique_id |
| data.OsEndOfSupport.value | asset.assetDetail.typedAttributes.OsEndOfSupport |
| data.CpuFamily.value | asset.assetDetail.typedAttributes.CpuFamily |
| data.CpuType.value | asset.assetDetail.typedAttributes.CpuType |
| data.IngressPorts.value | asset.assetDetail.typedAttributes.IngressPorts |
| data.KernelVersion.value | asset.assetDetail.typedAttributes.KernelVersion |
| data.Tags.value.Name | asset.assetDetail.externalTags[].value |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.OrcaScore.value | asset.assetDetail.typedAttributes.OrcaScore |
| data.RiskLevel.value | asset.assetDetail.typedAttributes.RiskLevel |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.CloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.CloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.CloudAccount.data.CloudProvider.value (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value (FUNCTION_PICKER REGEX) | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
Container ImageContainer Image
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| asset_unique_id | asset.assetDetail.typedAttributes.& |
| data.ImageName.value | asset.assetDetail.containerImageAssetClass.name |
| data.CloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.CloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.ImageName.value | asset.assetDetail.containerImageAssetClass.imageTagReferences[].name |
| data.RepositoryName.value | asset.assetDetail.containerImageAssetClass.repository |
| data.RepositoryName.value | asset.assetDetail.containerImageAssetClass.imageTagReferences[].repository |
| data.ImageDigest.value | asset.assetDetail.containerImageAssetClass.digest |
| data.ImageSize.value | asset.assetDetail.containerImageAssetClass.sizeInBytes |
| data.ImageSize.value | asset.assetDetail.containerImageAssetClass.layers[].sizeInBytes |
| data.RepositoryUri.value | asset.assetDetail.containerImageAssetClass.registry |
| data.ImageTags.value | asset.assetDetail.containerImageAssetClass.tag |
| data.RepositoryUri.value | asset.assetDetail.containerImageAssetClass.imageTagReferences[].registry |
| data.ImageTags.value | asset.assetDetail.containerImageAssetClass.imageTagReferences[].tag |
| data.ImageDigest.value | asset.assetDetail.containerImageAssetClass.layers[].digest |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.FirstSeen.value (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| data.LastSeen.value (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value (FUNCTION_PICKER REGEX) | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
| FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |
Container Instance
| SourceField | TargetField |
|---|---|
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| asset_unique_id | asset.assetDetail.typedAttributes.asset_unique_id |
| data.RiskLevel.value | asset.assetDetail.typedAttributes.RiskLevel |
| data.OrcaScore.value | asset.assetDetail.typedAttributes.OrcaScore |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.cloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.CloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.Arn.value | asset.assetDetail.containerInstanceAssetClass.id |
| data.Status.value | asset.assetDetail.containerInstanceAssetClass.status |
| data.ImageName.value | asset.assetDetail.containerInstanceAssetClass.Image.name |
| data.FirstSeen.value (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| data.LastSeen.value (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value (FUNCTION_PICKER REGEX_MATCH_RETURN) | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
| SourceField | TargetField |
|---|---|
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| asset_unique_id | asset.assetDetail.typedAttributes.asset_unique_id |
| data.RiskLevel.value | asset.assetDetail.typedAttributes.RiskLevel |
| data.OrcaScore.value | asset.assetDetail.typedAttributes.OrcaScore |
| data.AssetUniqueId.value | asset.assetDetail.containerInstanceAssetClass.id |
| data.CloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.CloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.Status.value | asset.assetDetail.containerInstanceAssetClass.status |
| data.Name.value | asset.assetDetail.containerInstanceAssetClass.host.name |
| data.PrivateClusterConfig.value.privateEndpoint | asset.assetDetail.containerInstanceAssetClass.host.ipAddress |
| data.ImageName.value | asset.assetDetail.containerInstanceAssetClass.Image.name |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.FirstSeen.value (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| data.LastSeen.value (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
Serverless
AWS Lambda FunctionAWS Lambda Function
| SourceField | TargetField |
|---|---|
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| type | asset.assetDetail.serverlessAssetClass.serviceName |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.CloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.CloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.FunctionName.value | asset.assetDetail.serverlessAssetClass.functionName |
| data.CloudAccount.data.CloudProvider.value (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
GCP Cloud FunctionGCP Cloud Function
| SourceField | TargetField |
|---|---|
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| type | asset.assetDetail.serverlessAssetClass.serviceName |
| data.AssetUniqueId.value | asset.assetHeader.externalAssetId |
| data.CloudAccount.id | asset.assetDetail.cloudInfo.accountId |
| data.CloudAccount.name | asset.assetDetail.cloudInfo.accountName |
| data.FunctionName.value | asset.assetDetail.serverlessAssetClass.functionName |
| data.CloudAccount.data.CloudProvider.value (FUNCTION_PICKER LOOKUP) | asset.assetDetail.cloudInfo.provider |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingDetectionURL |
Azure Function AppAzure Function App
| name | asset.assetDetail.name |
| id | asset.assetHeader.vendorAssetId |
| type | asset.assetDetail.serverlessAssetClass.serviceName |
| data.Arn.value | asset.assetHeader.externalAssetId |
| data.Name.value | asset.assetDetail.serverlessAssetClass.functionName |
| data.EnvVars.value | asset.assetDetail.serverlessAssetClass.environmentVariables |
| data.IsInternetFacing.value | asset.assetDetail.typedAttributes.IsInternetFacing |
| data.FirstSeen.value (DATE_FORMAT) | asset.assetDetail.sourceCreatedAt |
| data.LastSeen.value (DATE_FORMAT) | asset.assetDetail.sourceUpdatedAt |
| data.OrcaScore.value | asset.assetDetail.typedAttributes.OrcaScore |
| data.RiskLevel.value | asset.assetDetail.typedAttributes.RiskLevel |
| data.ConsoleUrlLink.value | asset.assetDetail.cloudInfo.providerUrl |
| data.Tags.value.Name | asset.assetDetail.externalTags[].value |
| vulnerabilities[].data.Inventory.name | findingGroup.findings[].asset.assetName |
| vulnerabilities[].data.Inventory.asset_unique_id | findingGroup.findings[].asset.externalAssetId |
| vulnerabilities[].data.CVE.data.PublicName.value | findingGroup.findings[].name |
| vulnerabilities[].data.CVE.data.Id.value | findingGroup.findings[].externalFindingId |
| vulnerabilities[].data.SourceLink.value | findingGroup.findings[].findingURL |
| vulnerabilities[].data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].firstFoundOn |
| vulnerabilities[].data.CVE.data.LastModifiedDate.value (DATE_FORMAT) | findingGroup.findings[].lastFoundOn |
| vulnerabilities[].data.data.FirstSeen.value (DATE_FORMAT) | findingGroup.findings[].ingestedOn |
| vulnerabilities[].data.CveId.value (FUNCTION_PICKER REGEX) | findingGroup.findings[].findingType.vulnerability.cveId |
| vulnerabilities[].data.HasExploit.value | findingGroup.findings[].findingType.vulnerability.isExploitAvailable |
| vulnerabilities[].data.Description.value | findingGroup.findings[].description |
| vulnerabilities[].data.PatchAvailable.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].findingType.vulnerability.isPatchAvailable |
| vulnerabilities[].data.CvssVector.value | findingGroup.findings[].cvss.vector |
| vulnerabilities[].data.CvssSeverity.value (FUNCTION_PICKER LOOKUP) | findingGroup.findings[].severity |
| vulnerabilities[].data.CvssScore.value | findingGroup.findings[].riskScore |
| FUNCTION_PICKER (DEFAULT_VALUE) | asset.assetHeader.assetTypeName |