Snyk Code (SAST) Connector
The Snyk Code (SAST) connector bridges application security scanning and enterprise risk management by importing static code analysis findings from Snyk into Qualys Enterprise TruRisk Management (ETM). This integration eliminates the fragmentation problem where security teams must manually correlate code vulnerabilities across separate platforms, enabling centralized risk visibility, impact assessment, and remediation prioritization.
By consolidating SAST results for both code repositories and generic applications into a unified platform, security practitioners gain comprehensive visibility into application-layer risks and can prioritize remediation efforts based on business impact rather than managing multiple disconnected tools.
Connector Details
High-level reference information for the Snyk Code (SAST) connector.
| Vendor | Snyk |
| Product Name | Snyk SAST |
| Category | Application Security |
| Findings Support | Supported |
| Supported Assets | Code Repository |
| Version | 1.0.0 |
| Integration Type | API Integration (REST) |
| Direction | Unidirectional (Snyk to Qualys) |
| Delta Support | Supported |
Configure the Connector
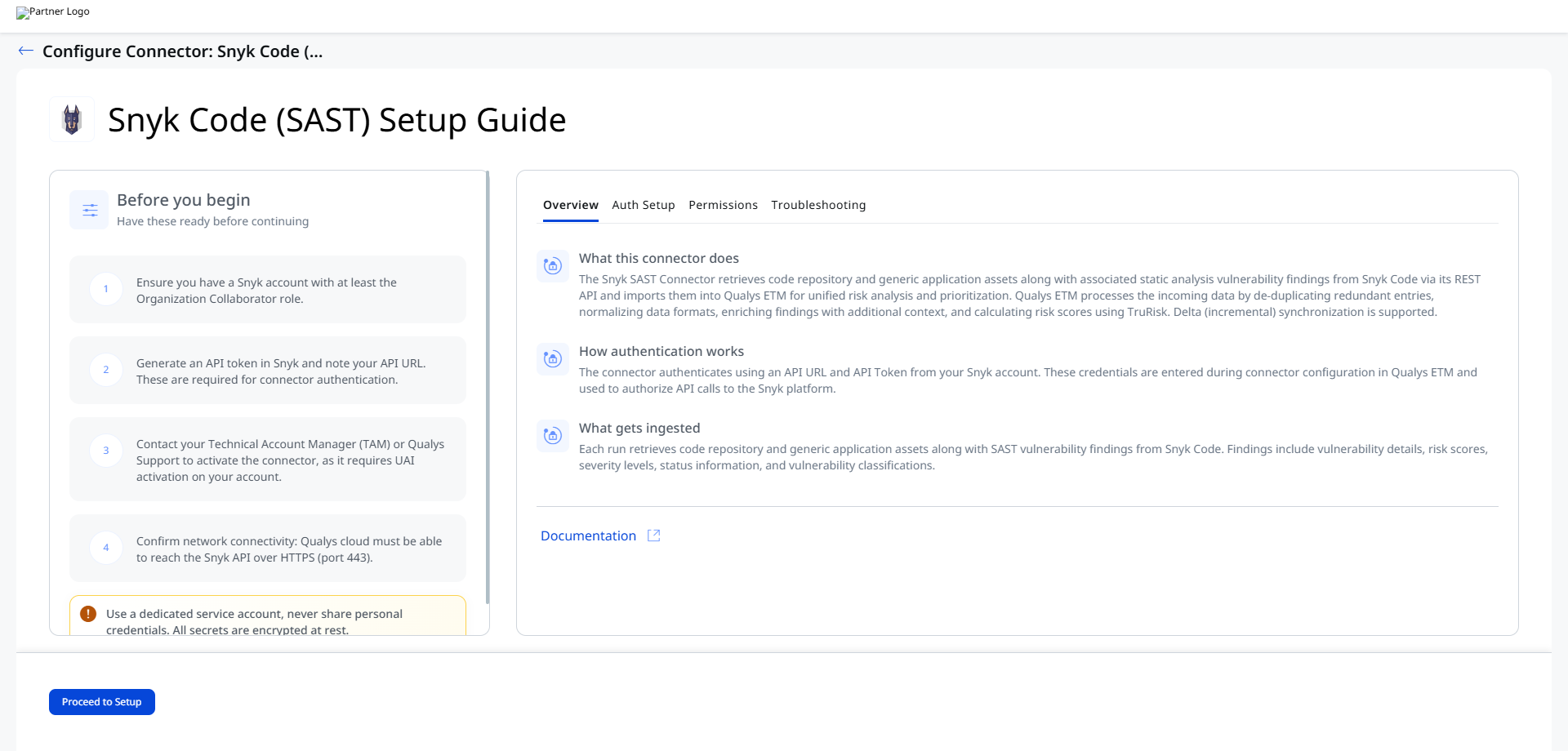
Before You Begin - AuthenticationBefore You Begin - Authentication
Complete the following preparation steps before configuring the connector in Qualys ETM.
- Ensure you have a Snyk account with at least the Organization Collaborator role.
- Generate an API Token in Snyk and note your API URL. These are required for connector authentication.
- Confirm network connectivity: Qualys cloud must be able to reach the Snyk API over HTTPS (port 443).
Obtaining API Credentials from Snyk
Follow these steps to retrieve your API Token and API URL from Snyk:
- Log in to your Snyk account.
- Navigate to your Account Settings.
- Locate and copy your API Token.
- Note your Snyk API URL, which varies based on your Snyk deployment region (for example,
https://api.us.snyk.iofor the US region).
Token Security: Treat your API Token as a secret. If the token is compromised or rotated, update the connector credential immediately via the Edit Connector option in Qualys ETM.
Permissions Required
The Snyk account used for the connector must have the Organization Collaborator role for both supported asset types.
| Asset Type | Required Role |
|---|---|
| Code Repository | Organization Collaborator |
| Generic Application | Organization Collaborator |
Scope and Data Access
The connector retrieves SAST findings from Snyk Code with comprehensive transformation mappings covering metadata, business criticality, vulnerability classifications, and exception details. The connector queries the following Snyk REST API endpoints:
| Name | Endpoint |
|---|---|
| List Orgs API | https://api.us.snyk.io/rest/orgs?version=2025-11-10 |
| Get Project Per Org API | https://api.us.snyk.io/rest/orgs/<id>/projects?version=2025-11-10 |
| Get Issues Per Project API | https://api.us.snyk.io/rest/orgs/<id>/issues?version=2025-11-18&type=package_vulnerability&scan_item.type=project&scan_item.id=<id> |
The API URL base (for example, api.us.snyk.io) varies by Snyk deployment region. Confirm the correct base URL for your environment in your Snyk account settings.
Key Rotation
When rotating the API token, generate a new token in your Snyk account settings. Then update the credential in Qualys ETM by navigating to the connector, selecting Edit Connector, and entering the new API Token in the authentication fields.
Create a Profile & ConnectionCreate a Profile & Connection
- Log in to Qualys Enterprise TruRisk Management (ETM).
- Navigate to Connectors > Integration.
- Locate the Snyk SAST Connector and click Manage.
If the connector does not appear in the integrations list, the activation has not been completed. Contact your TAM or Qualys Support to activate it.
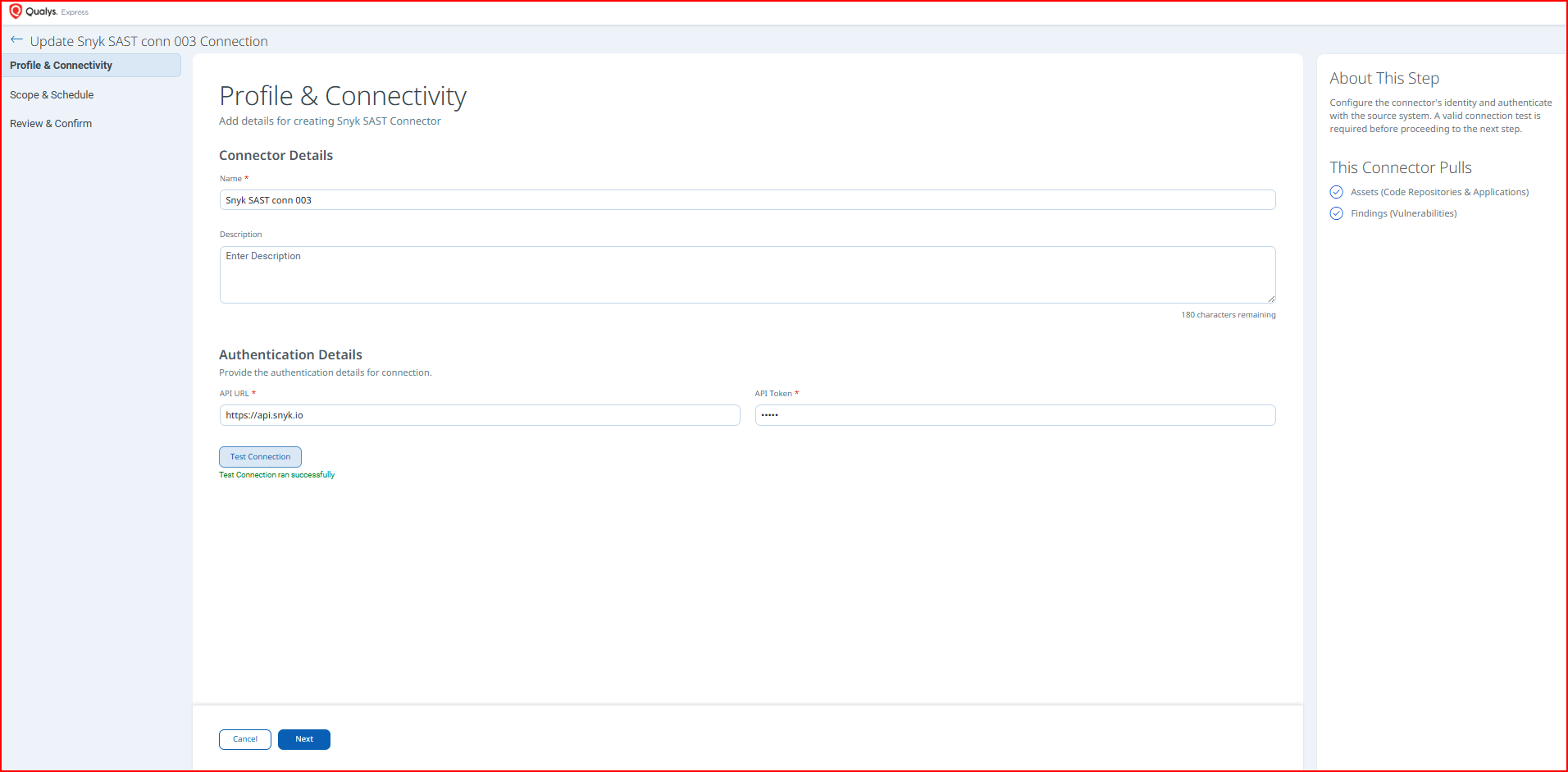
- Complete the Connector Details fields as described below.
- Complete the Authentication Details fields as described below.
- Click Test Connection to validate the credentials before proceeding.
- Click Next to continue.
Connector Details
| Name | A unique, descriptive name for this connector instance. |
| Description | Optional. A brief description of the connector's purpose or scope. |
Authentication Details
| Field | Type | Description |
|---|---|---|
| API URL | String | The base API URL for your Snyk account, which varies by deployment region. Example: https://api.us.snyk.io |
| API Token | Encrypted String | The API token generated from your Snyk account settings. Used to authenticate all API calls to the Snyk platform. |
Test Connection validates the following checks before allowing you to proceed:
- Network Reachability — Verifies the API endpoint is reachable.
- TLS Handshake — Confirms a secure connection can be established.
- Authentication Credential Check — Validates the Client ID, Client Secret, and Token URL.
- Authorization Scope Check — Confirms the service account has the required permissions.
- Data Fetch — Verifies that data can be retrieved from the Snyk Code API.
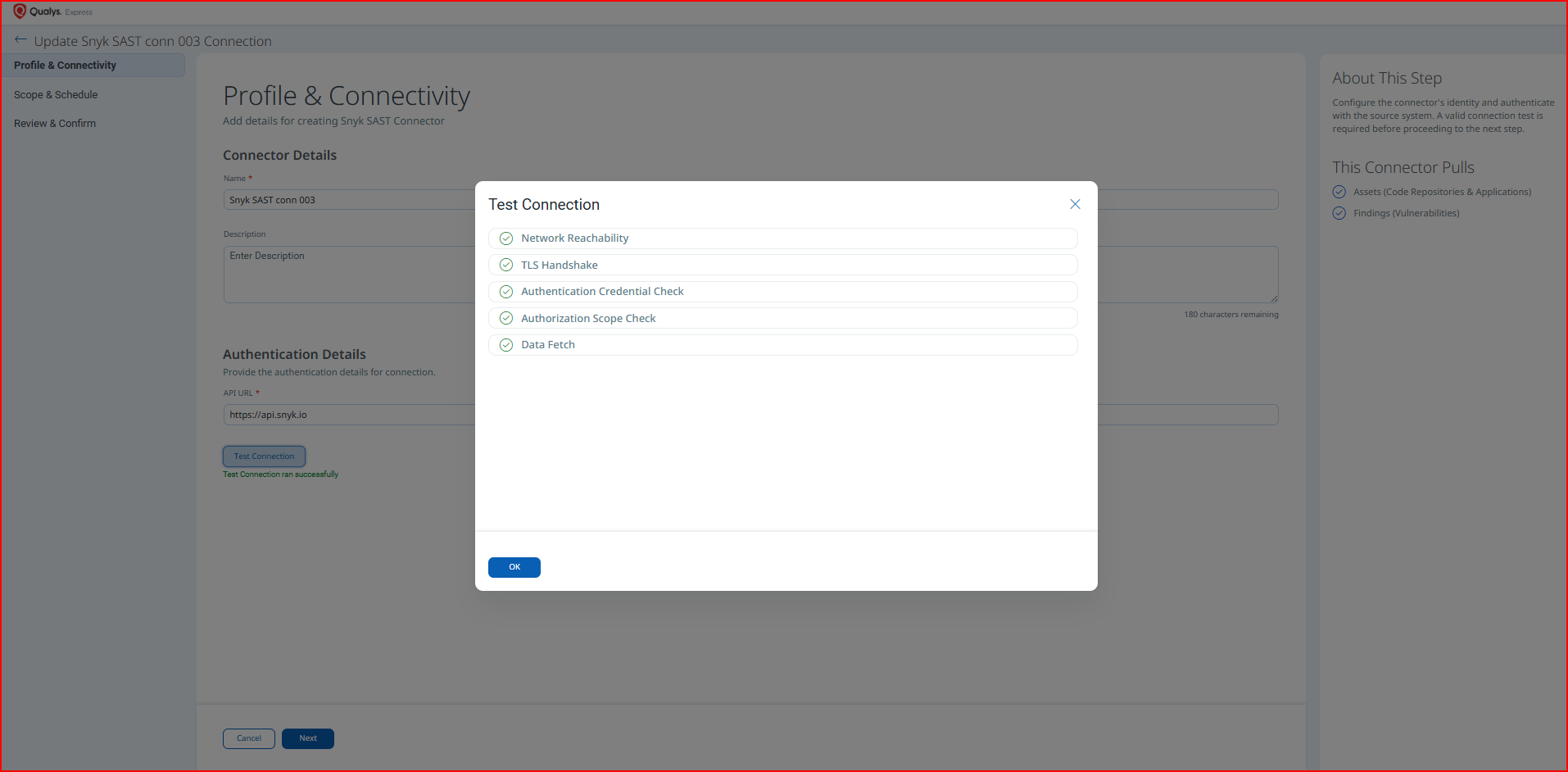
If the Authentication Credential Check fails, verify that the API URL and API Token entered in Qualys ETM are correct, and confirm the Snyk account has the Organization Collaborator role.
Set the Scope & ScheduleSet the Scope & Schedule
- Select the Asset Type to sync:
- Code Repository
- Generic Application.
- Configure the Schedule:
- Occurs - Set to Daily, Weekly, or Monthly.
- Single Occurrence – runs once at the specified date and time.
- Recurring – runs on a repeating schedule; set the start date, end date, and recurrence interval.
- Click Next to proceed to the review step.
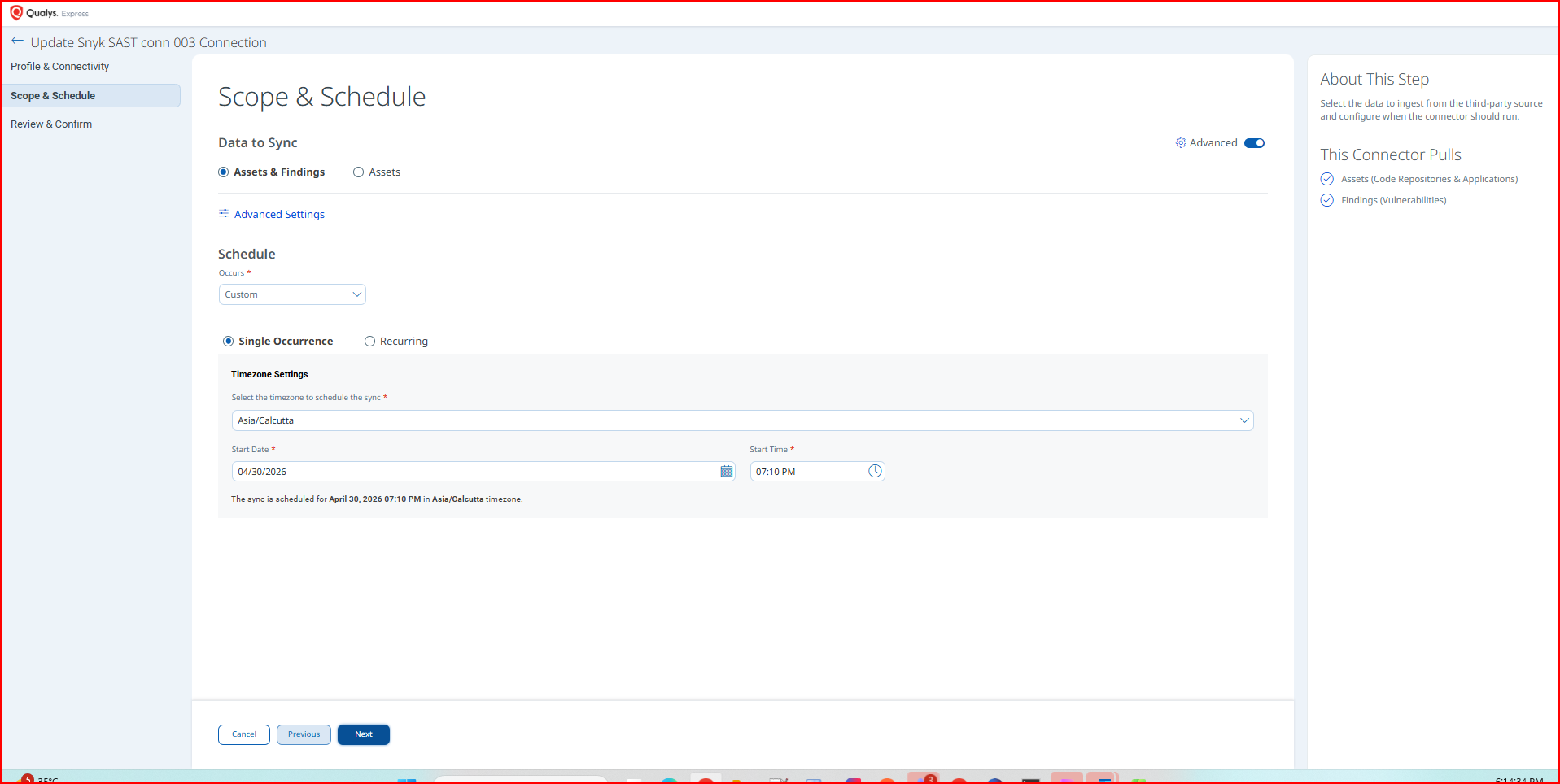
Schedule times are evaluated in the timezone configured for your Qualys account. For recurring schedules, a maximum duration of 5 years is supported.
Advanced Settings
Changes made in Advanced Settings take effect on the next connector run. Click Save after making any changes.
Filters Tab
The Filters tab is present in the connector configuration; however, custom filter queries are not currently supported for the Snyk Code (SAST) connector. All available assets within the scope of the authenticated Snyk account are retrieved on each run.
Transform Map Tab
The Transform Map tab displays the active transformation maps applied when ingesting data from Snyk into Qualys ETM. The following maps are active for this connector:
- Code Repo – Transformation Map
- Generic Application – Transformation Map
Code Repo – Transformation MapCode Repo – Transformation Map
| Source Field | Target Field |
|---|---|
SCRIPT_BASE_FUNCTION |
asset.assetHeader.externalAssetId (Required) |
FUNCTION_PICKER |
asset.assetHeader.status (Required) |
relationships.target.data.meta.integration_data.owner |
asset.assetDetail.repositoryAssetClass.owner |
id |
asset.assetHeader.vendorAssetId (Required) |
attributes.name |
asset.assetDetail.name (Required) |
attributes.created |
asset.assetDetail.sourceCreatedAt |
attributes.created |
asset.assetDetail.sourceUpdatedAt |
FUNCTION_PICKER |
asset.assetDetail.repositoryAssetClass.type |
relationships.target.data.attributes.url |
asset.assetDetail.repositoryAssetClass.repoUrl |
attributes.business_criticality.0 |
asset.assetDetail.businessInfo.businessCriticality |
attributes.settings.recurring_tests.frequency |
asset.assetDetail.typedAttributes.snykSASTSettingsRecurringFrequency |
issues[].attributes.title |
findingGroup.findings[].name (Required) |
issues[].attributes.description |
findingGroup.findings[].description |
issues[].id |
findingGroup.findings[].externalFindingId (Required) |
FUNCTION_PICKER |
findingGroup.findings[].severity |
FUNCTION_PICKER |
findingGroup.findings[].findingStatus |
issues[].attributes.created_at |
findingGroup.findings[].firstFoundOn |
issues[].attributes.updated_at |
findingGroup.findings[].lastFoundOn |
issues[].attributes.classes.0.id |
findingGroup.findings[].findingType.vulnerability.cweId |
issues[].attributes.ignored |
findingGroup.findings[].riskAcceptance.ignored |
attributes.target_reference |
asset.assetDetail.typedAttributes.snykSASTTargetReference |
org.id |
asset.assetDetail.typedAttributes.snykSASTOrganizationId |
org.attributes.name |
asset.assetDetail.typedAttributes.snykSASTOrganizationName |
org.attributes.group_id |
asset.assetDetail.typedAttributes.snykSASTGroupId |
org.attributes.updated_at |
asset.assetDetail.typedAttributes.snykSASTOrgUpdatedAt |
org.attributes.created_at |
asset.assetDetail.typedAttributes.snykSASTOrgCreatedAt |
attributes.target_file |
asset.assetDetail.typedAttributes.snykSASTTargetFile |
attributes.type |
asset.assetDetail.typedAttributes.snykSASTType |
issues[].findingDetectionUrl |
findingGroup.findings[].findingDetectionURL |
issues[].findingUrl |
findingGroup.findings[].findingURL |
Generic Application – Transformation MapGeneric Application – Transformation Map
| Source Field | Target Field |
|---|---|
attributes.name |
asset.assetDetail.genericApplicationAssetClass.name (Required) |
id |
asset.assetHeader.externalAssetId (Required) |
FUNCTION_PICKER |
asset.assetHeader.status (Required) |
id |
asset.assetHeader.vendorAssetId (Required) |
attributes.name |
asset.assetDetail.name (Required) |
attributes.created |
asset.assetDetail.sourceCreatedAt |
attributes.created |
asset.assetDetail.sourceUpdatedAt |
attributes.business_criticality.0 |
asset.assetDetail.businessInfo.businessCriticality |
attributes.settings.recurring_tests.frequency |
asset.assetDetail.typedAttributes.snykSASTSettingsRecurringFrequency |
issues[].attributes.title |
findingGroup.findings[].name (Required) |
issues[].attributes.description |
findingGroup.findings[].description |
issues[].id |
findingGroup.findings[].externalFindingId (Required) |
FUNCTION_PICKER |
findingGroup.findings[].findingStatus |
FUNCTION_PICKER |
findingGroup.findings[].severity |
issues[].attributes.created_at |
findingGroup.findings[].firstFoundOn |
issues[].attributes.updated_at |
findingGroup.findings[].lastFoundOn |
issues[].attributes.classes.0.id |
findingGroup.findings[].findingType.vulnerability.cweId |
issues[].attributes.ignored |
findingGroup.findings[].riskAcceptance.ignored |
attributes.target_reference |
asset.assetDetail.typedAttributes.snykSASTTargetReference |
org.id |
asset.assetDetail.typedAttributes.snykSASTOrganizationId |
org.attributes.name |
asset.assetDetail.typedAttributes.snykSASTOrganizationName |
org.attributes.group_id |
asset.assetDetail.typedAttributes.snykSASTGroupId |
org.attributes.updated_at |
asset.assetDetail.typedAttributes.snykSASTOrgUpdatedAt |
org.attributes.created_at |
asset.assetDetail.typedAttributes.snykSASTOrgCreatedAt |
attributes.target_file |
asset.assetDetail.typedAttributes.snykSASTTargetFile |
attributes.type |
asset.assetDetail.typedAttributes.snykSASTType |
issues[].findingDetectionUrl |
findingGroup.findings[].findingDetectionURL |
issues[].findingUrl |
findingGroup.findings[].findingURL |
How the Connection Works
The Snyk SAST connector retrieves code repository and generic application assets along with associated static analysis vulnerability findings from Snyk Code via its REST API and imports them into Qualys ETM for unified risk analysis and prioritization.
Qualys ETM processes the incoming data by de-duplicating redundant entries, normalizing data formats, enriching findings with additional context, and calculating risk scores using TruRisk. Delta (incremental) synchronization is supported, meaning subsequent runs retrieve only changes since the last sync rather than re-importing all data.
Each run retrieves the following data from Snyk:
- Code repository and generic application assets
- SAST vulnerability findings, including vulnerability details, risk scores, severity levels, status information, and vulnerability classifications
Connector States
The connector transitions through the following states during a run:
| Registered | The connector has been created and registered in Qualys ETM. It is awaiting its first scheduled run. |
| Scheduled | The connector is queued and scheduled to run at the configured time. |
| Processing | Data is actively being fetched from Snyk and imported into ETM. |
| Processed | Asset import is complete. Findings ingestion may continue after assets are marked as processed. |
| Errored | The connector encountered an error during the run. Review the error details and see the Troubleshooting section for resolution steps. |
The complete import process for the first run may take up to 2 hours depending on data volume. If no findings appear immediately after the connector reaches the Processed state, allow additional time for findings ingestion to complete.
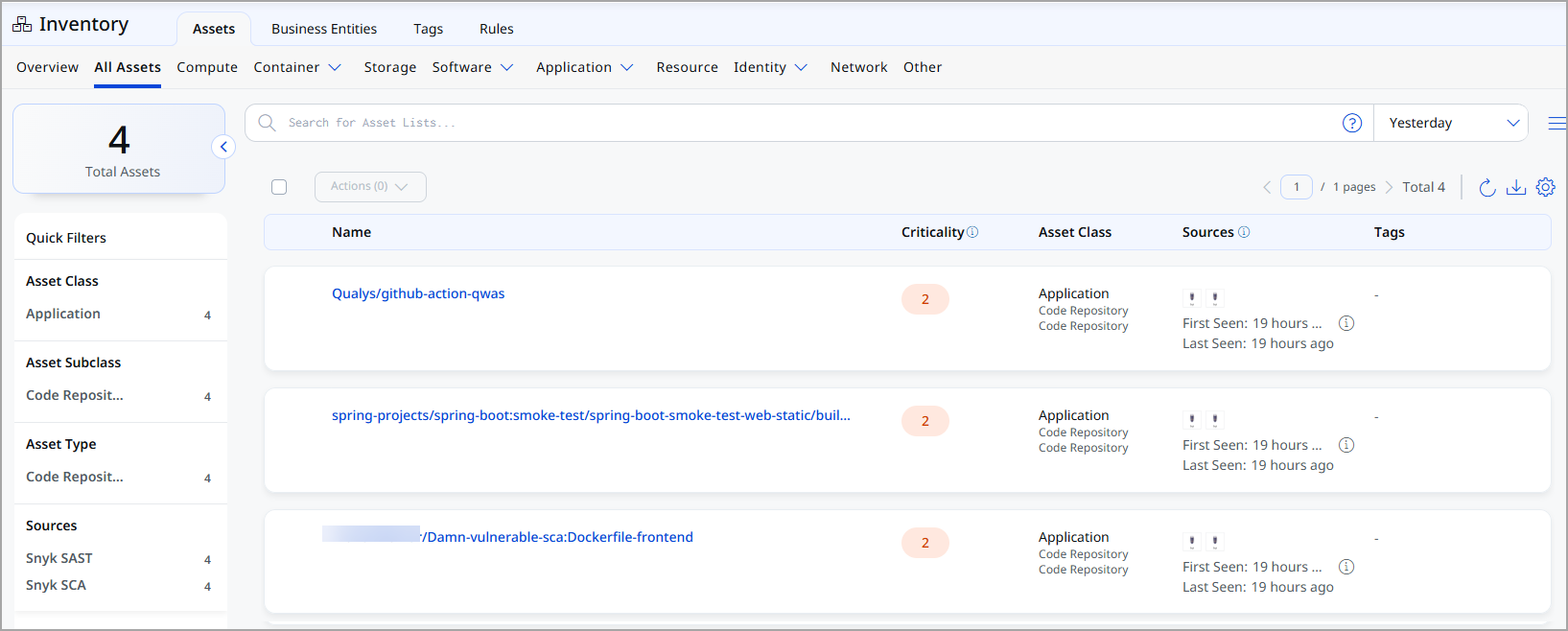
Viewing Assets and Findings in ETM
After a successful connector run, imported data is available in Qualys ETM as follows:
Assets – Navigate to Enterprise TruRisk Management > Inventory and apply the following filter:
inventory:(source:"Snyk")
Troubleshooting
| Issue | Resolution |
|---|---|
| Authentication failure on connector run | Verify the API URL and API Token entered in Qualys ETM are correct. Confirm the Snyk account has the Organization Collaborator role for both Code Repository and Generic Application asset types. |
| No findings imported after first run | The connector transitions through Registered, Scheduled, Processing, and Processed states. The complete import process may take up to 2 hours depending on data volume. Findings ingestion may continue after asset processing completes; allow additional time before investigating further. |
| Connector not available in the integrations list | The connector requires activation on your Qualys account. Contact your TAM or Qualys Support to activate it. |
Additional Information
API Reference
The connector uses the following Snyk REST API endpoints to retrieve data:
| Name | Endpoint |
|---|---|
| List Orgs API | https://api.us.snyk.io/rest/orgs?version=2025-11-10 |
| Get Project Per Org API | https://api.us.snyk.io/rest/orgs/<id>/projects?version=2025-11-10 |
| Get Issues Per Project API | https://api.us.snyk.io/rest/orgs/<id>/issues?version=2025-11-18&type=package_vulnerability&scan_item.type=project&scan_item.id=<id> |
The API base URL (api.us.snyk.io) shown above is for the US region. Substitute the correct regional base URL for your Snyk deployment.