Snyk Open Source (SCA)
The Snyk SCA Connector bridges software composition analysis findings from Snyk into Qualys Enterprise TruRisk Management, enabling security teams to achieve centralized risk visibility and prioritization using TruRisk Insights across their code repositories and applications. By automatically importing vulnerability data alongside asset information, organizations gain a unified view of their software supply chain risks rather than managing security findings in isolated tools.
This integration supports delta data pulls on configurable schedules, allowing teams to maintain current vulnerability posture without manual data synchronization. For practitioners juggling multiple security platforms, the connector eliminates the friction of context-switching between systems while enabling faster risk-based decision making through consolidated visibility.
Connector Details
High-level details for the Snyk SCA connector.
| Vendor | Snyk |
| Product Name | Snyk SCA |
| Category | Application Security |
| Findings Supported | Yes |
| Assets Supported | Code Repository |
| Version | 1.0.0 |
| Integration Type | API Integration (REST) |
| Direction | Unidirectional (Snyk to Qualys) |
| Delta Support | Supported |
Connection Settings
User Roles and Permissions
The following permissions are required in Snyk to configure and run the connector:
| Entity Type | Required Permission |
|---|---|
| Code Repository | Organization Collaborator |
| Generic Application | Organization Collaborator |
Authentication Details
Provide the following credentials while configuring the connector:
| Name | Key | Type | Description |
|---|---|---|---|
| API URL | api_id |
String | API URL for the Snyk user profile |
| API Token | api_key |
Encrypted String | API token for authenticating to Snyk |
Connector Configuration
Basic Details
- Log in to Qualys ETM.
- Navigate to Connectors > Integration.
- Locate the Snyk SCA Connector and click Manage.
- Provide a Name and Description for the connector.
- Enter the required authentication details.
Profiles
Profiles control how and when the connector executes.
- Create a new profile using the + option.
- Provide a Name and Description.
- Select the Assets value:
- Core Repository
- Generic Application
- Configure a Schedule:
- Single Occurrence
- Recurring (with start and end date/time)
- Click Next and proceed to review.
Review and Confirm
Review the configuration details and click Create to activate the connector.
How Does the Connection Work?
Based on the configured schedule or on-demand execution, the Snyk SCA connector fetches asset and findings data from Snyk and imports it into ETM.
The connection execution performs a full data pull. Once execution completes, the connector is displayed in the Processed state in the Connectors screen. Findings ingestion may continue after assets are processed.
Connector States
A successfully configured connector transitions through the following states:
- Registered – Connector created and registered
- Scheduled – Execution scheduled
- Processing – Data ingestion in progress
- Processed – Assets imported; findings may still be processing
The complete ingestion process may take up to 2 hours, depending on data volume.
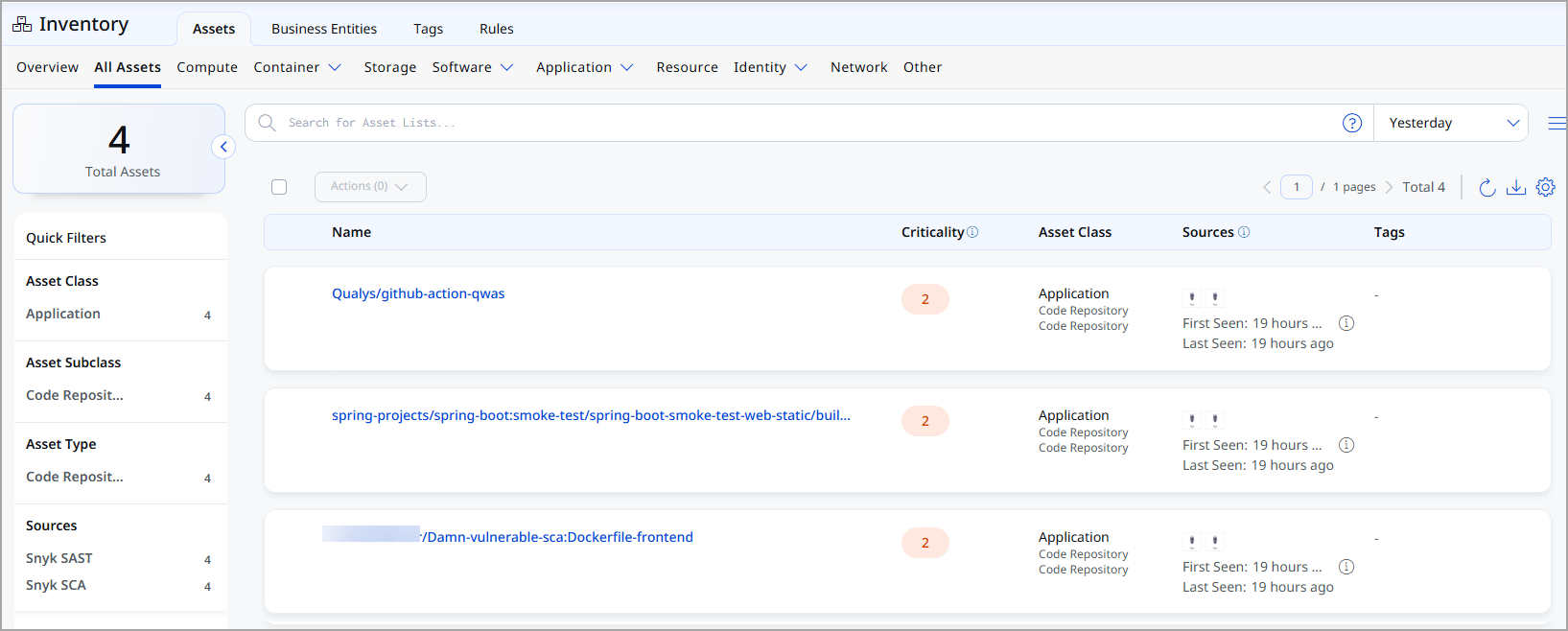
Viewing Assets and Findings in ETM
After a successful run, navigate to:
- Enterprise TruRisk Management > Inventory to view imported assets
Transformation Map Details
Here is the Snyk SCA to Qualys Transformation map.
Code Repo - Transformation map:
| Source Field | Target Field |
|---|---|
| SCRIPT_BASE_FUNCTION | asset.assetHeader.externalAssetId |
| FUNCTION_PICKER | asset.assetHeader.status |
| id | asset.assetHeader.vendorAssetId |
| attributes.created | asset.assetDetail.sourceCreatedAt |
| attributes.created | asset.assetDetail.sourceUpdatedAt |
| attributes.name | asset.assetDetail.name |
| attributes.tags[].key | asset.assetDetail.externalTags[].key |
| attributes.tags[].value | asset.assetDetail.externalTags[].value |
| FUNCTION_PICKER | asset.assetDetail.repositoryAssetClass.type |
| relationships.target.data.attributes.url | asset.assetDetail.repositoryAssetClass.repoUrl |
| relationships.target.data.meta.integration_data.owner | asset.assetDetail.repositoryAssetClass.owner |
| attributes.business_criticality.0 | asset.assetDetail.businessInfo.businessCriticality |
| attributes.settings.recurring_tests.frequency | asset.assetDetail.typedAttributes.snykSCASettingsRecurringFrequency |
| issues[].attributes.title | findingGroup.findings[].name |
| issues[].attributes.title | findingGroup.findings[].description |
| issues[].id | findingGroup.findings[].externalFindingId |
| FUNCTION_PICKER | findingGroup.findings[].severity |
| FUNCTION_PICKER | findingGroup.findings[].findingStatus |
| issues[].attributes.created_at | findingGroup.findings[].firstFoundOn |
| issues[].attributes.updated_at | findingGroup.findings[].lastFoundOn |
| issues[].attributes.classes.0.id | findingGroup.findings[].findingType.vulnerability.cweId |
| issues[].attributes.exploit_details.sources[] | findingGroup.findings[].findingType.vulnerability.exploitedByList[] |
| issues[].attributes.ignored | findingGroup.findings[].riskAcceptance.ignored |
| issues[].attributes.snykScaCveId | findingGroup.findings[].findingType.vulnerability.cveId |
| attributes.target_reference | asset.assetDetail.typedAttributes.snykSCATargetReference |
| org.id | asset.assetDetail.typedAttributes.snykSCAOrganizationId |
| org.attributes.name | asset.assetDetail.typedAttributes.snykSCAOrganizationName |
| org.attributes.group_id | asset.assetDetail.typedAttributes.snykSCAGroupId |
| org.attributes.updated_at | asset.assetDetail.typedAttributes.snykSCAOrgUpdatedAt |
| org.attributes.created_at | asset.assetDetail.typedAttributes.snykSCAOrgCreatedAt |
| attributes.target_file | asset.assetDetail.typedAttributes.snykSCATargetFile |
| attributes.type | asset.assetDetail.typedAttributes.snykSCAType |
| issues[].findingDetectionUrl | findingGroup.findings[].findingDetectionURL |
| issues[].findingUrl | findingGroup.findings[].findingURL |
Generic Application - Transformation map:
| Source Field | Target Field |
|---|---|
| attributes.name | asset.assetDetail.genericApplicationAssetClass.name |
| id | asset.assetHeader.externalAssetId |
| FUNCTION_PICKER | asset.assetHeader.status |
| id | asset.assetHeader.vendorAssetId |
| attributes.created | asset.assetDetail.sourceCreatedAt |
| attributes.created | asset.assetDetail.sourceUpdatedAt |
| attributes.name | asset.assetDetail.name |
| attributes.tags[].key | asset.assetDetail.externalTags[].key |
| attributes.tags[].value | asset.assetDetail.externalTags[].value |
| attributes.business_criticality.0 | asset.assetDetail.businessInfo.businessCriticality |
| attributes.settings.recurring_tests.frequency | asset.assetDetail.typedAttributes.snykSCASettingsRecurringFrequency |
| issues[].attributes.title | findingGroup.findings[].name |
| issues[].attributes.title | findingGroup.findings[].description |
| issues[].id | findingGroup.findings[].externalFindingId |
| FUNCTION_PICKER | findingGroup.findings[].severity |
| FUNCTION_PICKER | findingGroup.findings[].findingStatus |
| issues[].attributes.created_at | findingGroup.findings[].firstFoundOn |
| issues[].attributes.updated_at | findingGroup.findings[].lastFoundOn |
| issues[].attributes.classes.0.id | findingGroup.findings[].findingType.vulnerability.cweId |
| issues[].attributes.exploit_details.sources[] | findingGroup.findings[].findingType.vulnerability.exploitedByList[] |
| issues[].attributes.ignored | findingGroup.findings[].riskAcceptance.ignored |
| issues[].attributes.snykScaCveId | findingGroup.findings[].findingType.vulnerability.cveId |
| attributes.target_reference | asset.assetDetail.typedAttributes.snykSCATargetReference |
| org.id | asset.assetDetail.typedAttributes.snykSCAOrganizationId |
| org.attributes.name | asset.assetDetail.typedAttributes.snykSCAOrganizationName |
| org.attributes.group_id | asset.assetDetail.typedAttributes.snykSCAGroupId |
| org.attributes.updated_at | asset.assetDetail.typedAttributes.snykSCAOrgUpdatedAt |
| org.attributes.created_at | asset.assetDetail.typedAttributes.snykSCAOrgCreatedAt |
| attributes.target_file | asset.assetDetail.typedAttributes.snykSCATargetFile |
| attributes.type | asset.assetDetail.typedAttributes.snykSCAType |
| issues[].findingDetectionUrl | findingGroup.findings[].findingDetectionURL |
| issues[].findingUrl | findingGroup.findings[].findingURL |
API Endpoints
The connector uses the following Snyk SCA REST API endpoints to retrieve data
|
Name |
Endpoint |
|---|---|
|
List Orgs API |
https://api.us.snyk.io/rest/orgs?version=2025-11-10 |
|
Get Project Per Org API |
https://api.us.snyk.io/rest/orgs/<id>/projects?version=2025-11-10 |
|
Get Issues Per Project API |
https://api.us.snyk.io/rest/orgs/<id>/issues?version=2025-11-18&type=package_vulnerability&scan_item.type=project&scan_item.id=<id> |