Veracode SCA
The Veracode SCA connector bridges the gap between Veracode's software composition analysis platform and Qualys Enterprise TruRisk Management, enabling security teams to centralize code repository vulnerabilities alongside other enterprise findings. By automating the ingestion of application security SCA findings from Veracode into Qualys ETM, the connector eliminates manual data transfer and provides a unified view of supply chain risks across the organization.
This integration is particularly valuable for teams managing open source dependencies and third-party code risks, as it surfaces vulnerability data within the broader risk management context. The connector performs comprehensive pulls of vulnerable assets and findings, making threat prioritization and remediation planning more efficient across development and security operations.
Connector Details
|
Vendor |
Veracode |
|
Product Name |
Veracode SCA |
|
Category |
Application Security |
|
Findings Supported |
Yes |
|
Assets Supported |
Code Repository |
|
Version |
1.0.0 |
|
Integration Type |
API Integration (REST) |
|
Direction |
Unidirectional (Veracode to Qualys) |
|
Delta Support |
Not Supported |
Authentication
|
Name |
Key |
Type |
Description |
|---|---|---|---|
|
API ID |
api_id |
String |
API Id for the user profile |
|
API KEY |
api_key |
String |
API Key for the user profile |
Setting Up API Credential
Reference: Veracode Documentation
You must generate API credentials before you can use the APIs and some integrations.
If you use single sign-on with SAML, you can use the ID and key credentials instead of having to use a separate Veracode Platform API service account to access the APIs.
You can also generate Veracode API credentials with the Identity API.
To complete this task:
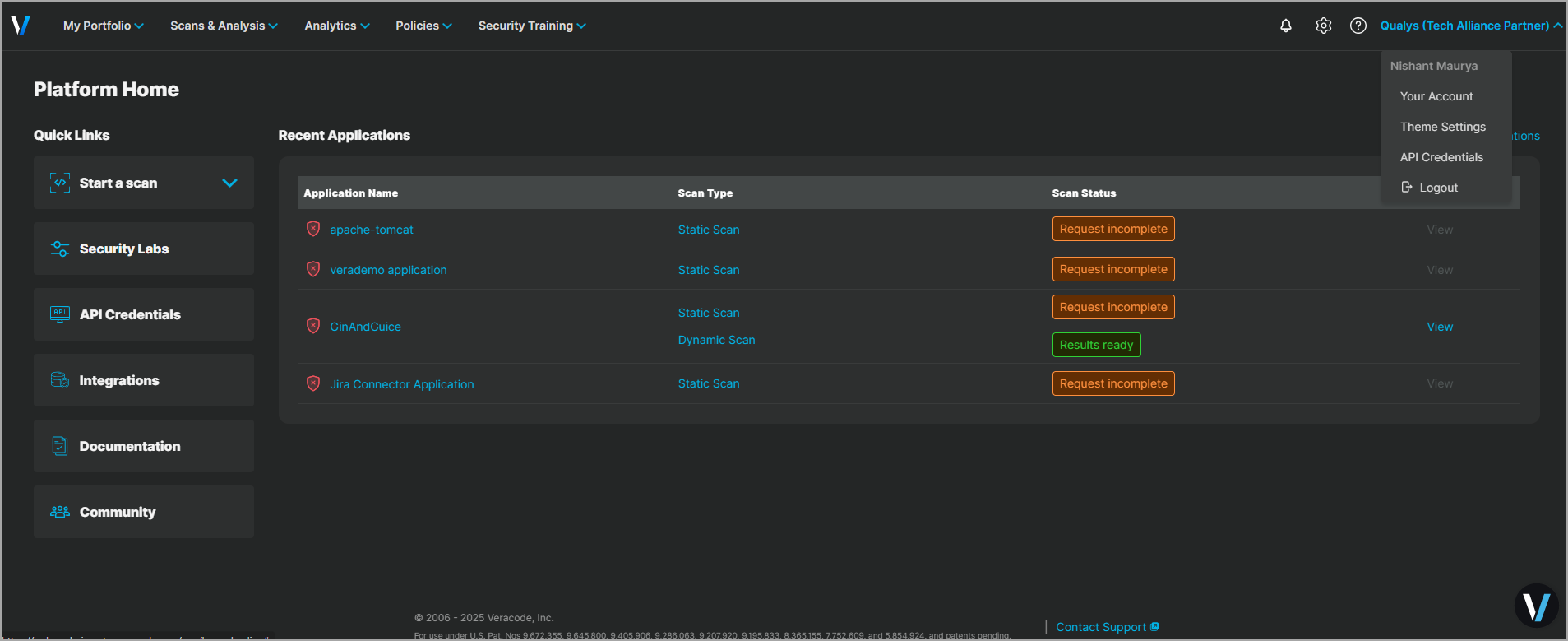
- Sign in to the Veracode Platform.
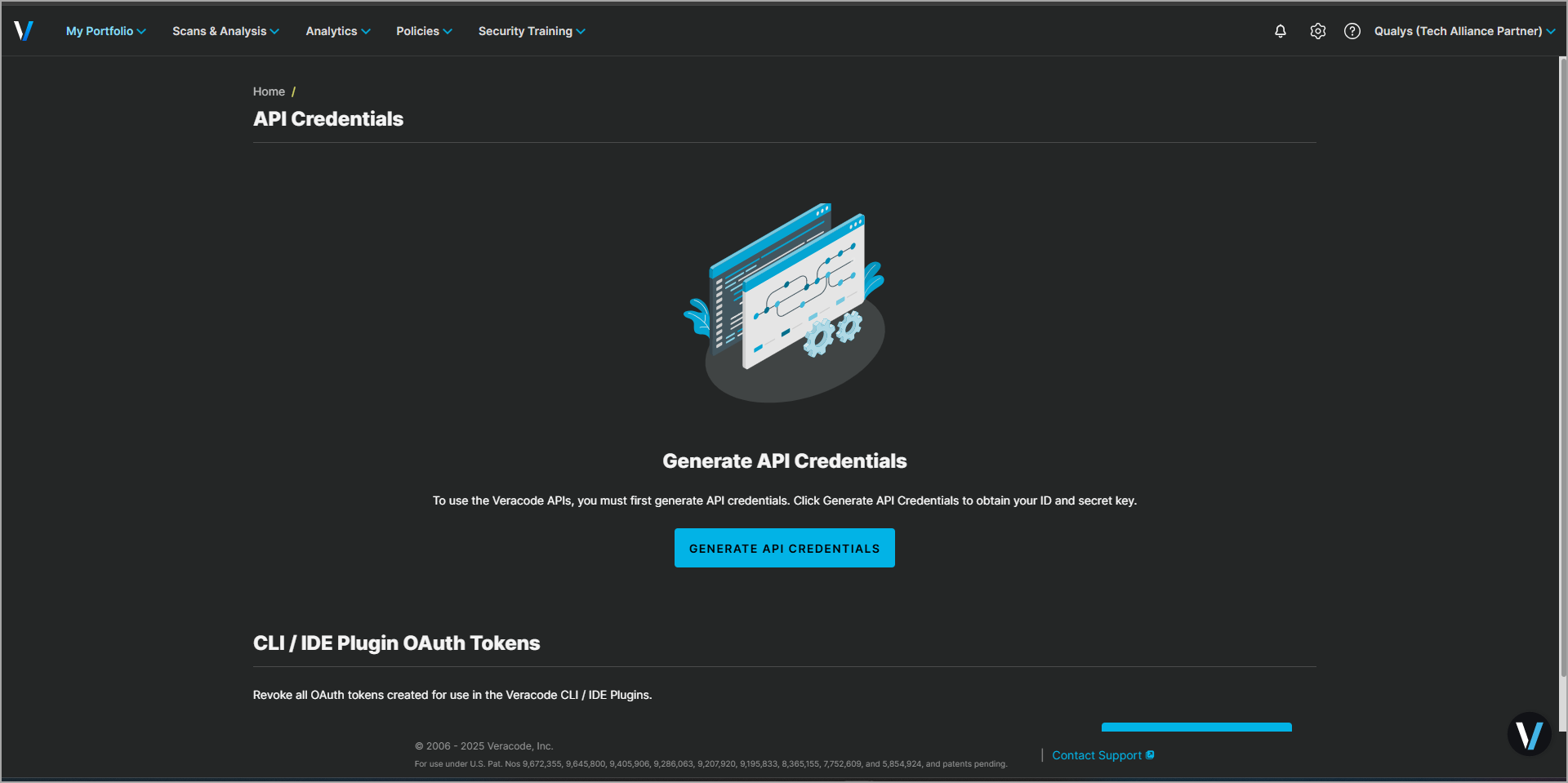
- From the user account dropdown, select API Credentials.
- Select Generate API Credentials.
- Copy the ID and secret key to a secure place.
Required Permissions:
|
Entity Type |
Permissions |
|---|---|
|
VulnerabilityFindings |
read: vulnerabilities |
API Endpoints
|
Name |
Endpoint |
Example |
|---|---|---|
|
Get Applications |
https://api.veracode.com/appsec/v1/applications |
|
|
Get Applications Findings |
https://api.veracode.com/appsec/v2/applications/ |
Example guid : f84d8ef9-6695-4342-9321-983e1e048315 |
We will only fetch vulnerable assets of the past 6 months as per the API limitations
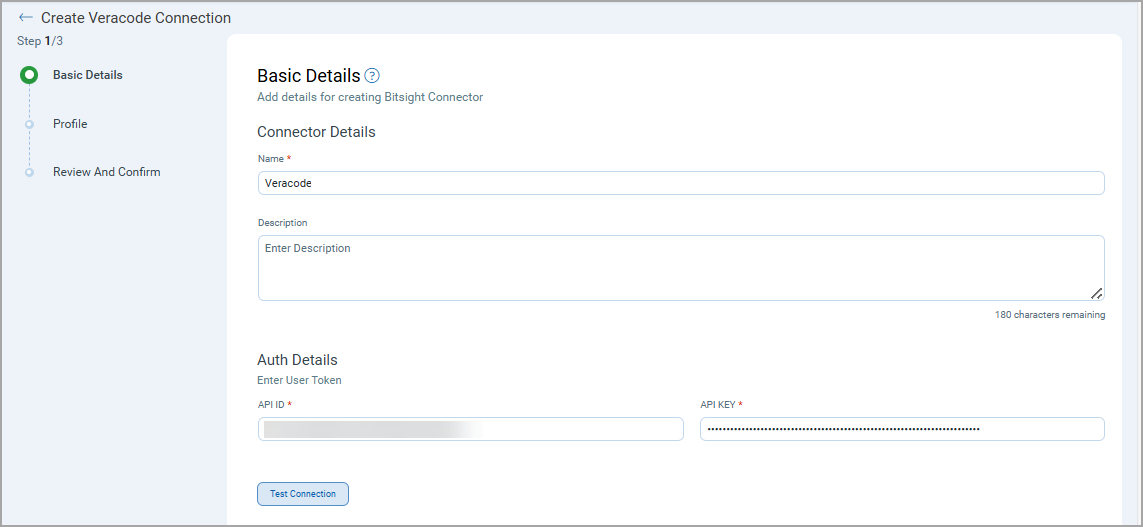
Configure Veracode SCA Connector
Basic Details
Provide the following details
- Connector Name and Description
- Authentication details (API ID & API KEY)
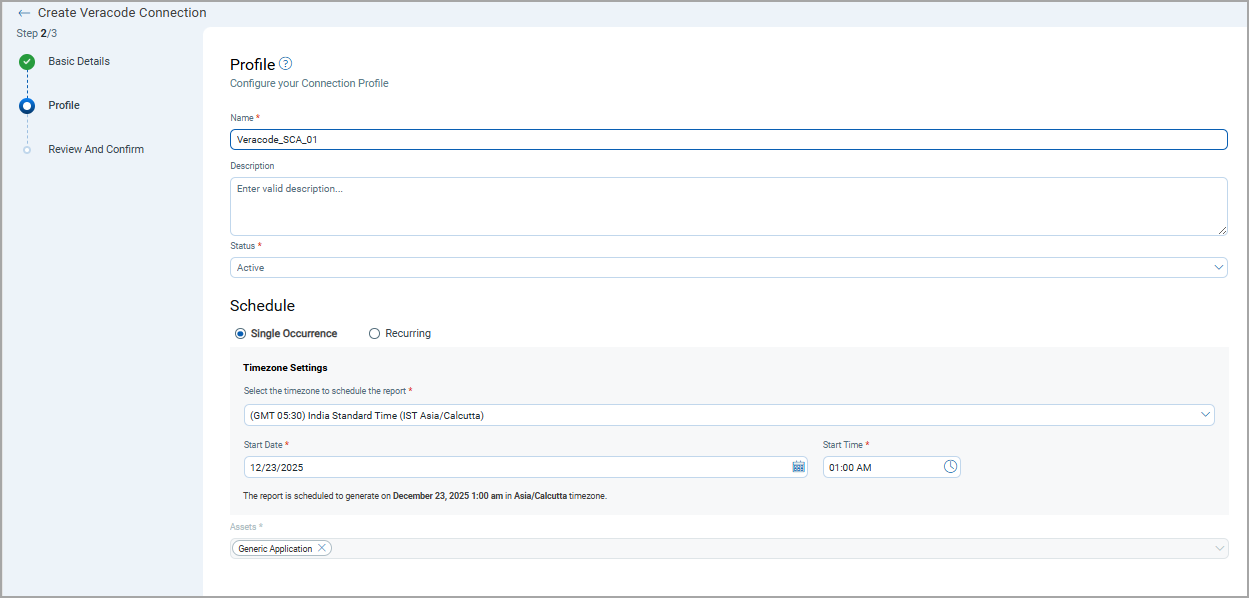
Profile
Profiles control the execution of the connector.
- Provide a Name and Description.
- Set Status (Active or Inactive).
- Configure a Schedule: Single Occurrence or Recurring with start and end dates/times.
- Assets value will be "CODE_REPO" by default for Veracode SCA connector
- Click Next.
Review and Confirm
Review the connection and click Create.
How Does the Connection Work?
On schedule (or on-demand), the connector fetches Veracode SCA findings and imports them into ETM. Profiles define what is synchronized and when. The Veracode SCA connector performs a full pull on each execution.
In the Connector screen, you can find your newly configured connector listed and marked in the Processed state.
Connector States
A successfully configured connector goes through 4 states.
- Registered - The connector is successfully created and registered to fetch data from the vendor.
- Scheduled - The connector is scheduled to execute a connection with the vendor.
- Processing - A connection is executed and the connector is fetching the asset and findings data.
- Processed - The connector has successfully fetched the assets; it may still be under process of fetching the findings. Wait for some more time for the connector to fetch the findings completely.
The Processed state indicates that the Connector is successfully configured but it is under the process of importing all your assets and findings. This process (specifically for findings) may take some time.
This entire process may take up to 2 hours for completion. Once it is done, you can find the imported data in Enterprise TruRisk Management (ETM).
Viewing Assets and Findings in ETM
- Navigate to Enterprise TruRisk Management > Inventory.
- Go to Assets to view imported Veracode assets/applications.
Assets > Application > Other Applications
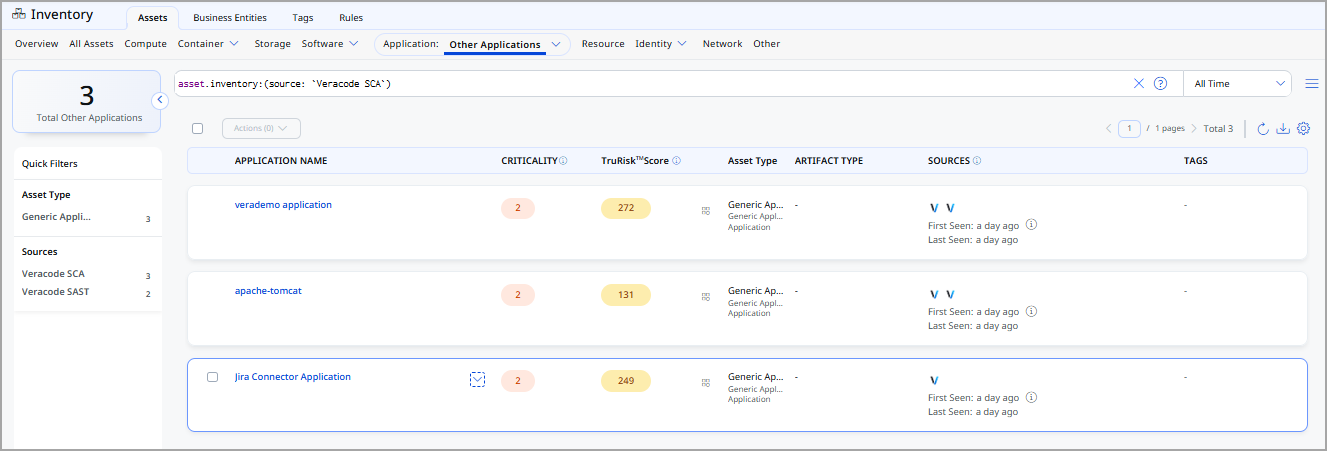
- Go to Assets to view imported Veracode assets/applications.
- Navigate to Risk Management > Findings > Vulnerability.
- Use filter: finding.vendorProductName:"Veracode" to list Veracode findings.
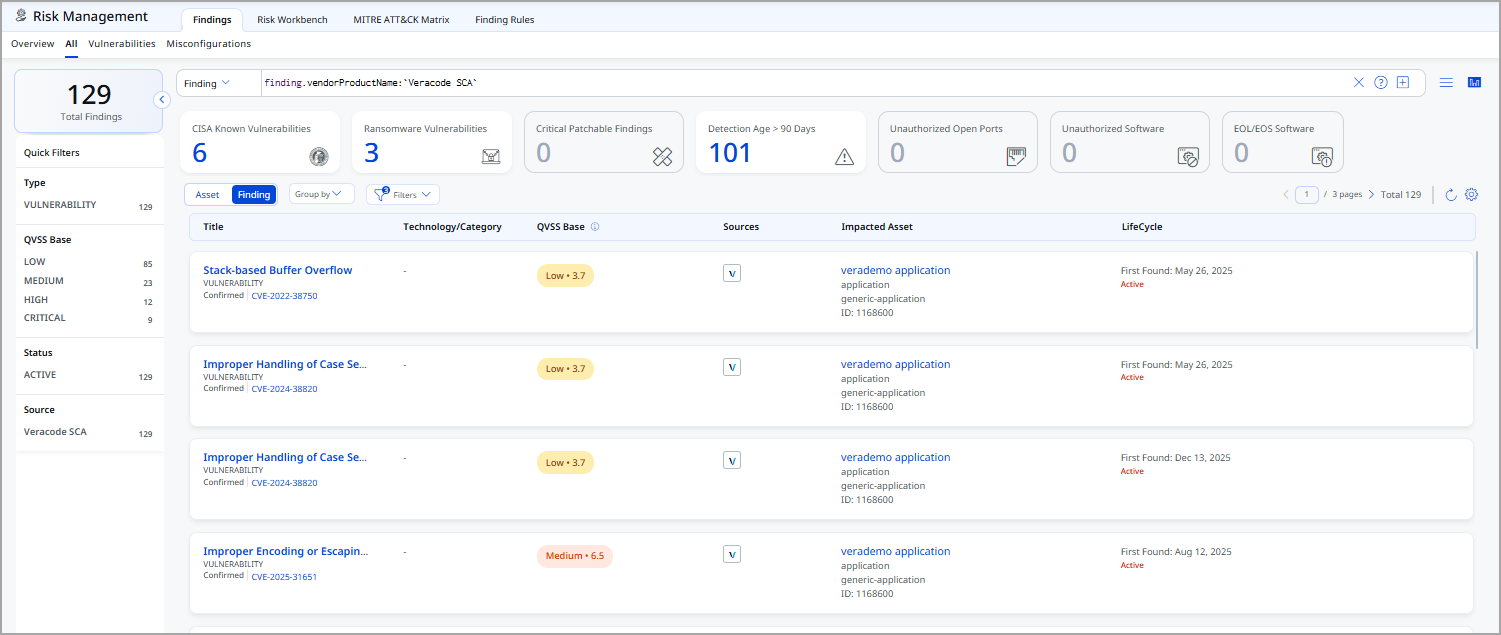
- Use filter: finding.vendorProductName:"Veracode" to list Veracode findings.
Veracode SCA - UAI Transformation Map:
The default transformation map configured for the Veracode SCA-UAI connector is fetched from the database and utilized during the execution of the connector profile to perform data transformation.
|
Source Field |
Target Field |
|---|---|
|
id |
externalAssetId |
|
oid |
vendorAssetId |
|
profile.name |
assetDetail.name |
|
git_repo_url |
repoUrl |
|
findings[].finding_details.cve.name |
findings[].name |
|
findings[].finding_details.cve.exploitability.full_cve |
findings[].externalFindingId |
|
findings[].finding_details.cwe.id |
findings[].findingType.vulnerability.cweId |
|
findings[].finding_details.cve.name |
findings[].findingType.vulnerability.cveId |
|
findings[].finding_details.cve.cvss3.score |
findings[].findingType.vulnerability.cvss.cvss3Base |
|
findings[].finding_details.cve.cvss3.vector |
findings[].findingType.vulnerability.cvss.vector |
|
findings[].description |
findings[].description |
|
findings[].finding_status.first_found_date |
findings[].firstFoundOn |
|
findings[].finding_status.status |
findings[].findingStatus |
|
findings[].finding_status.last_seen_date |
findings[].lastFoundOn |
|
findings[].finding_details.severity |
findings[].severity |