Release 1.33
June 12, 2024 (Updated on September 24, 2024)
What’s New?
Cluster Sensor & Kubernetes Cluster Inventory
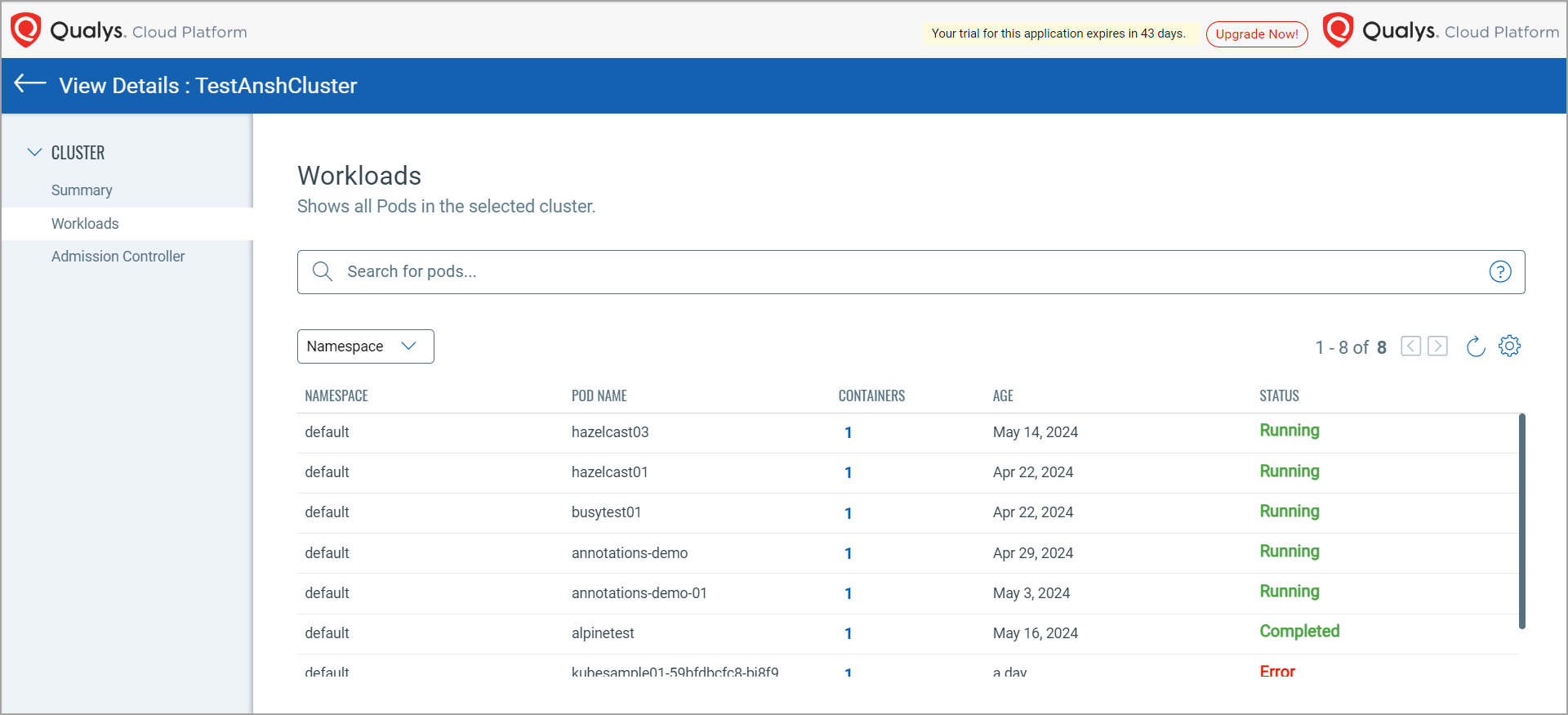
With this release, Qualys has introduced a new sensor type—Cluster Sensor 1.1.0—which collects Kubernetes (K8s) inventory data of resources such as PODs and Namespaces present in your clusters. Cluster sensor fetches the details of a POD, such as its 'State' and inventory, such as 'annotation' or 'labels'. You can filter the POD list using 'namespace' to check the running pods in your cluster.
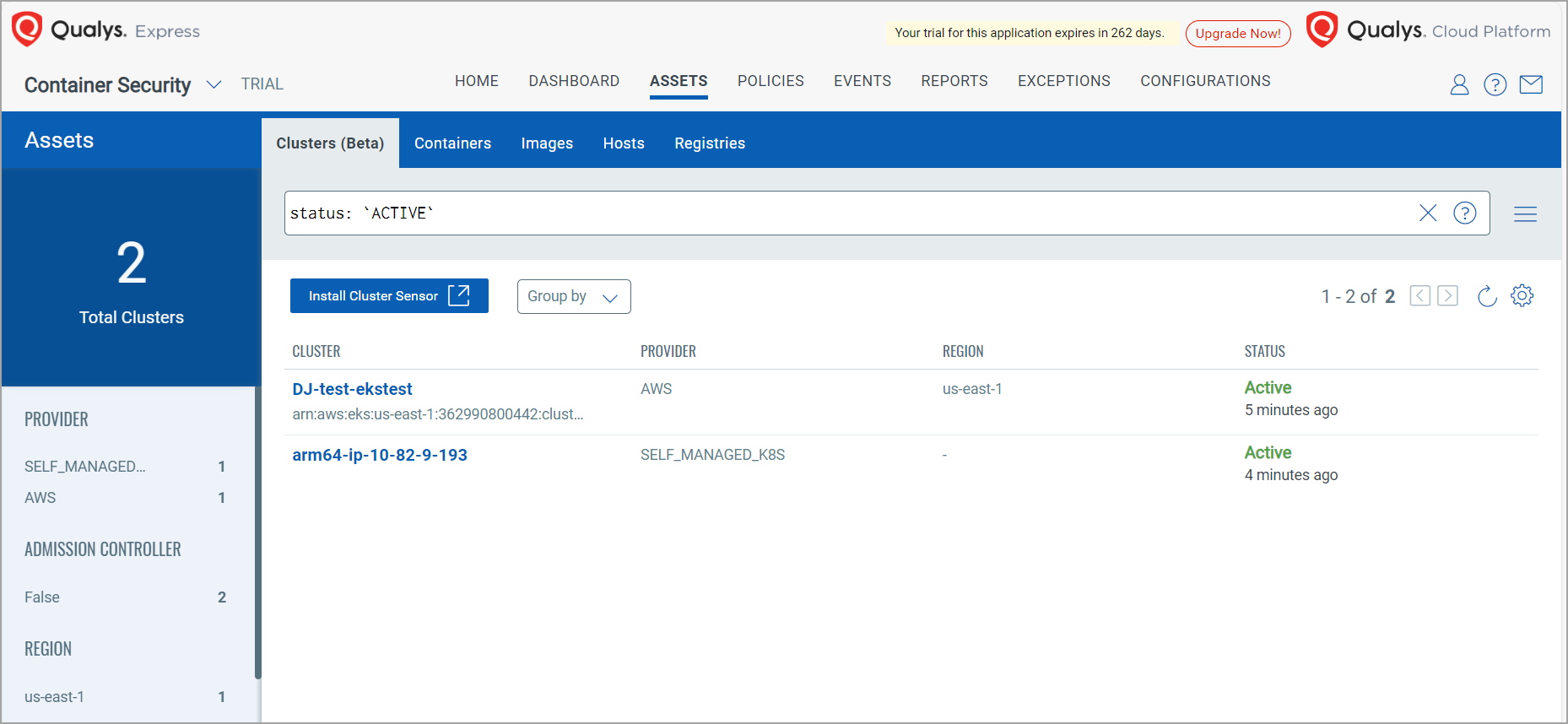
Currently, Qualys Cluster Sensor does not scan any containers. Instead, it focuses on data collection.
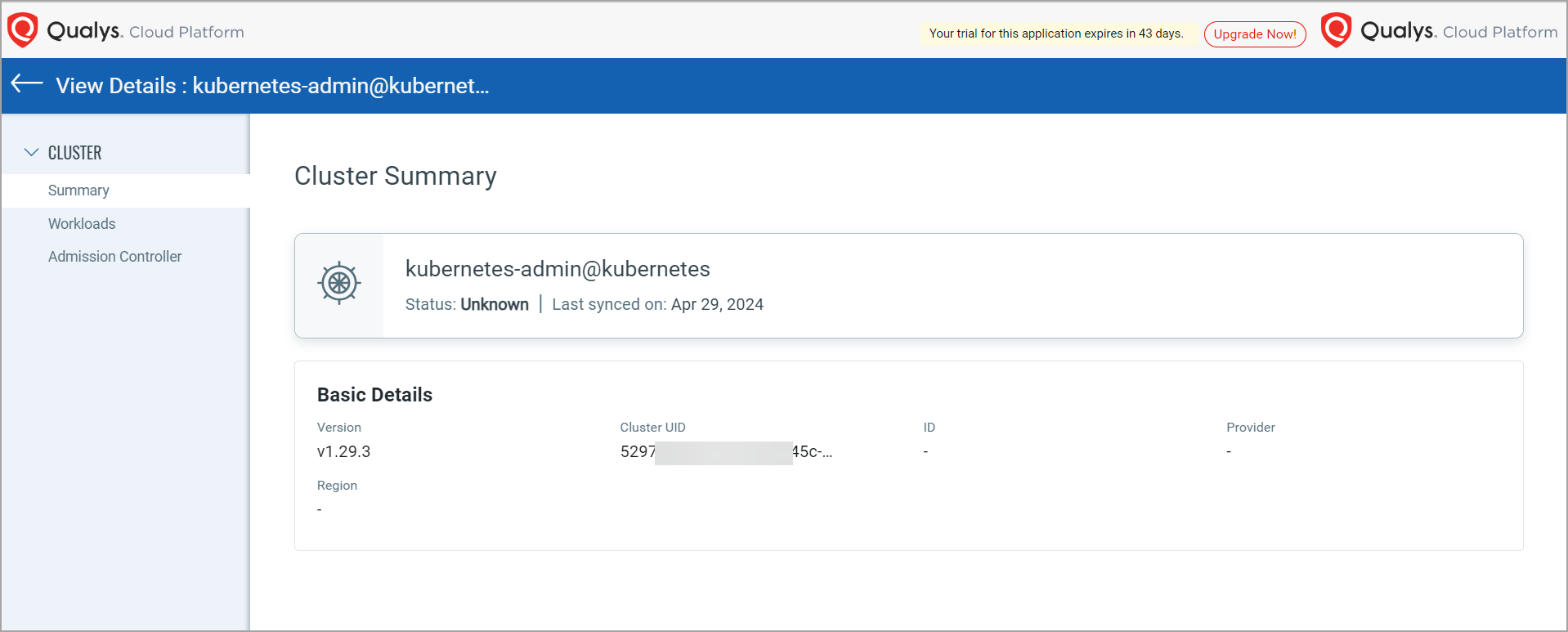
The Summary page provides the cluster summary.
The Workloads page displays all PODs associated with the cluster.
To know more about Cluster Sensor, refer to Cluster Sensor Online Help.
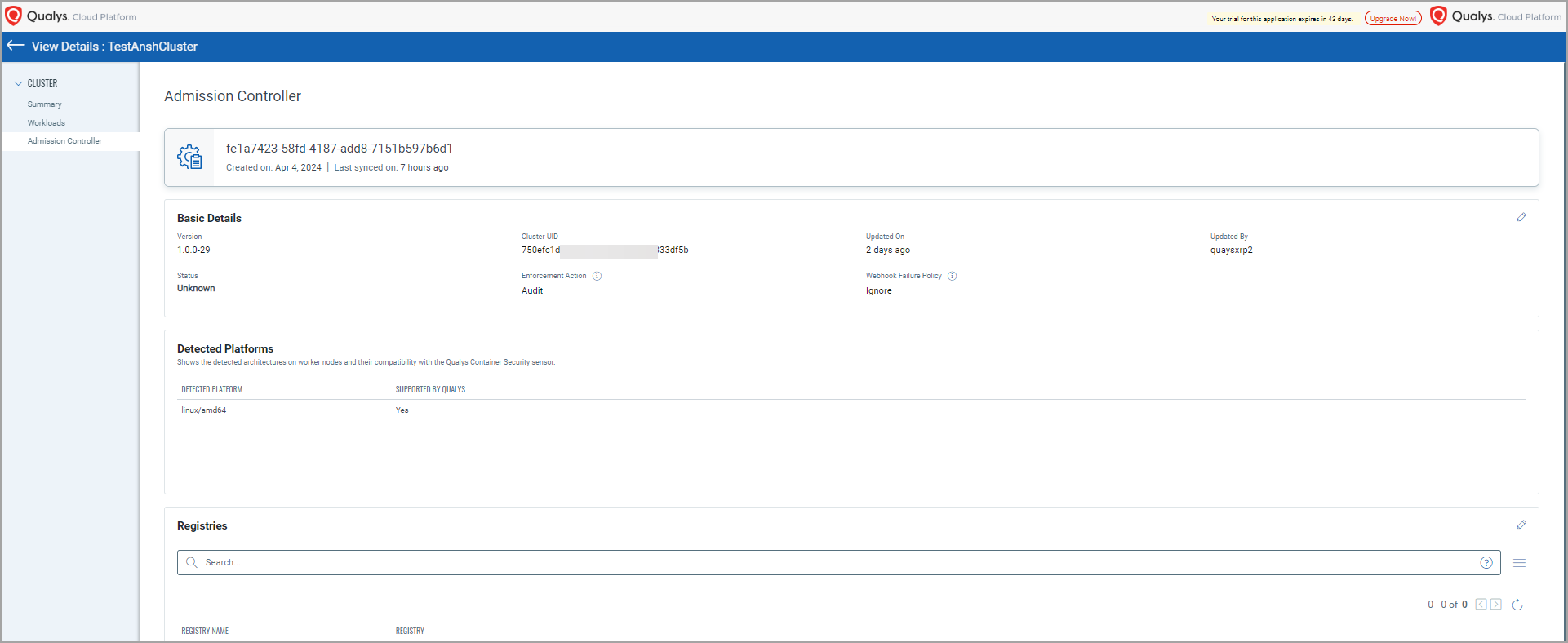
K8s Admission Controller & Centralized Policy Management
With this release, Qualys introduces K8s Admission Controller, which controls the K8s cluster admission. The K8s Admission Controller scans the requests coming from your K8s cluster, authenticating and authorizing them based on the K8s admission policy. The K8s Admission Controller is deployed in your environment using the Unified Helm chart hosted on Artifacthub. Admission to your cluster depends on the Centralized policies enforced on the cluster. The Centralized policy validates the K8s Cluster admissions.
The Centralized Policy evaluates the images linked to Qualys Cloud Platform, and the 'lastscanned' date of the images is 'not null'.
The Admission Controller page (ASSETS > Clusters (Beta) > View Details) displays all the configured details for the admission controller in the cluster. It also shows the detected platforms supported by Qualys and the list of registries added to the admission controller.
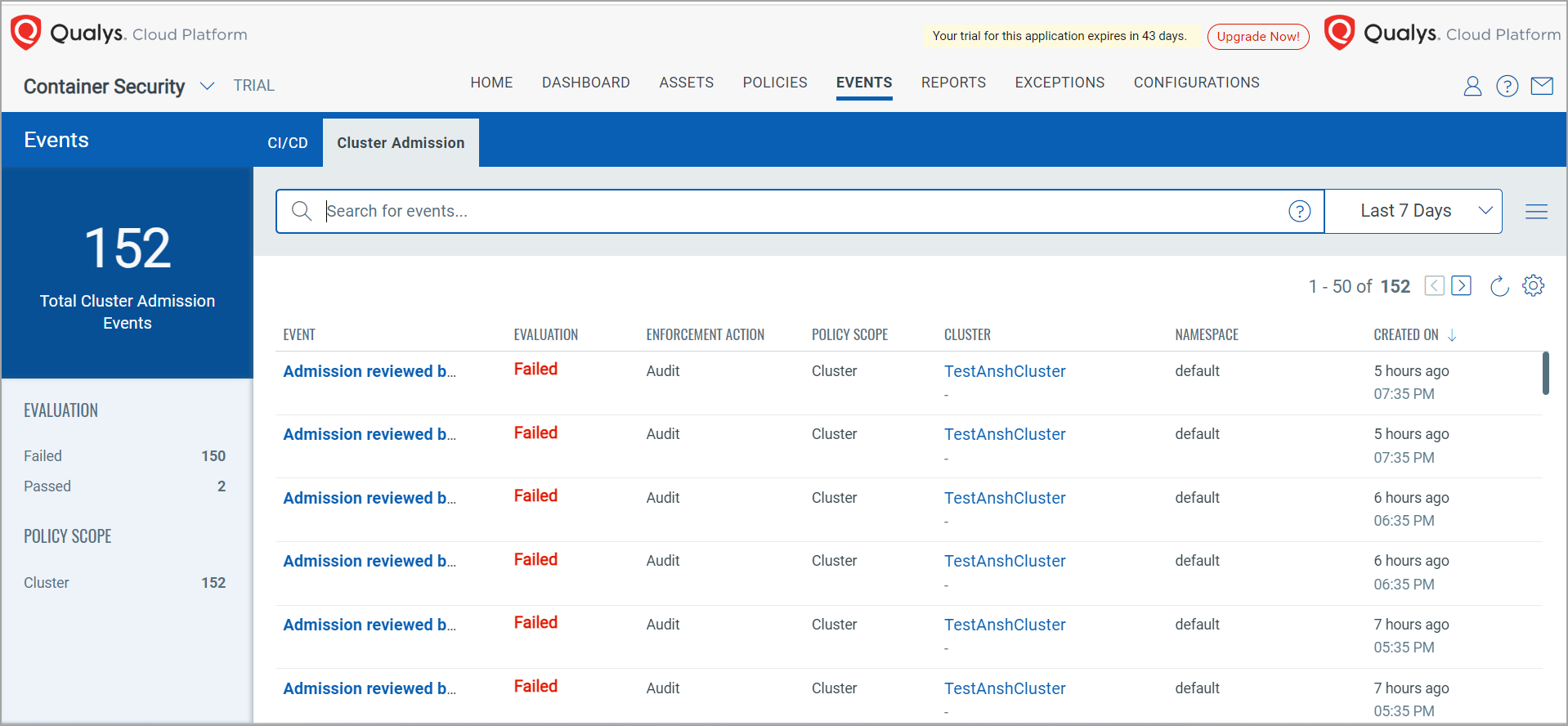
A new tab called Cluster Admission is available under the Events page. This page lists all cluster admission events in your account and provides event details such as evaluation, enforcement action, policy scope, cluster, namespace, and creation time.
When the Centralized policy receives the cluster admission request, it evaluates the policy associated with the resource and either allows or denies the admission depending on the rules set against that policy. The admission controller has a configurable field - Enforcement action - which inspects the incoming requests, and it has the following values
- AUDIT: Irrespective of the policy enforced, your admission request is always allowed.
- BLOCK: The cluster admission event will be validated, and based on the evaluation, your action will be either allowed or denied.
If the resources (namespace or the cluster) are not assigned any policy, then the evaluation result will be shown in the event as 'Not evaluated', and the Policy Scope column will show 'No policy'.
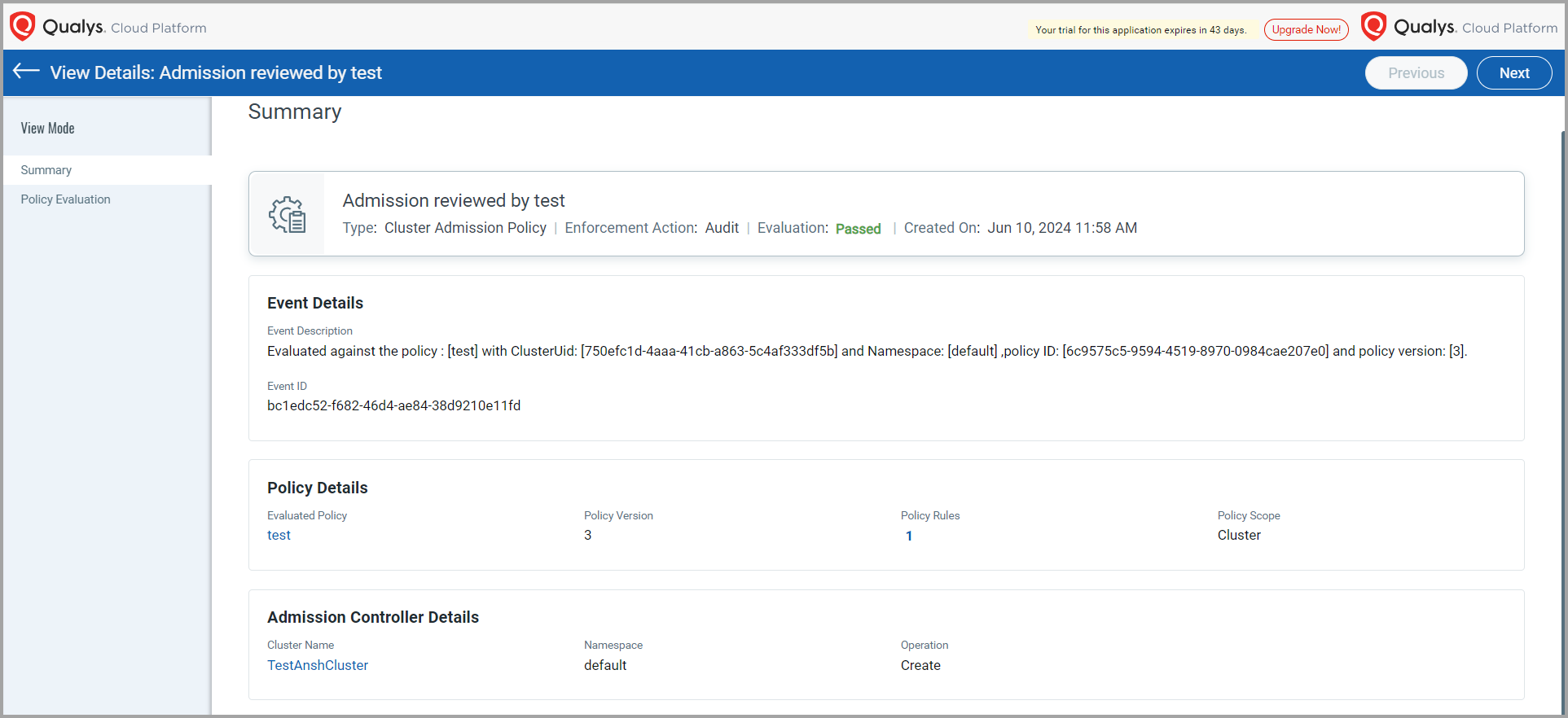
The Cluster Admission Summary page gives you event, policy, and admission controller details.
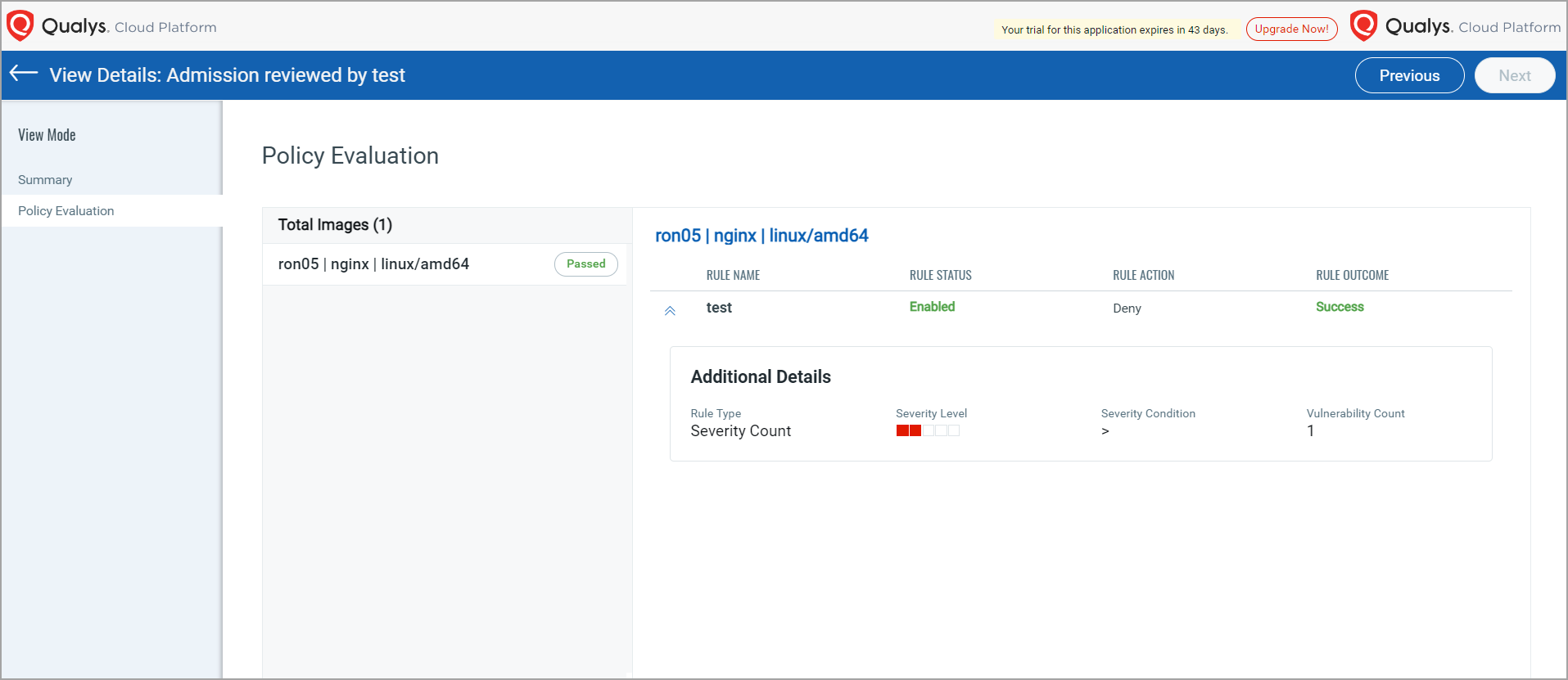
The Policy Evaluation page displays the total images associated with that policy along with image details.
To create a cluster admission policy, refer to Container Security 1.33 Online Help.
Asset State Management
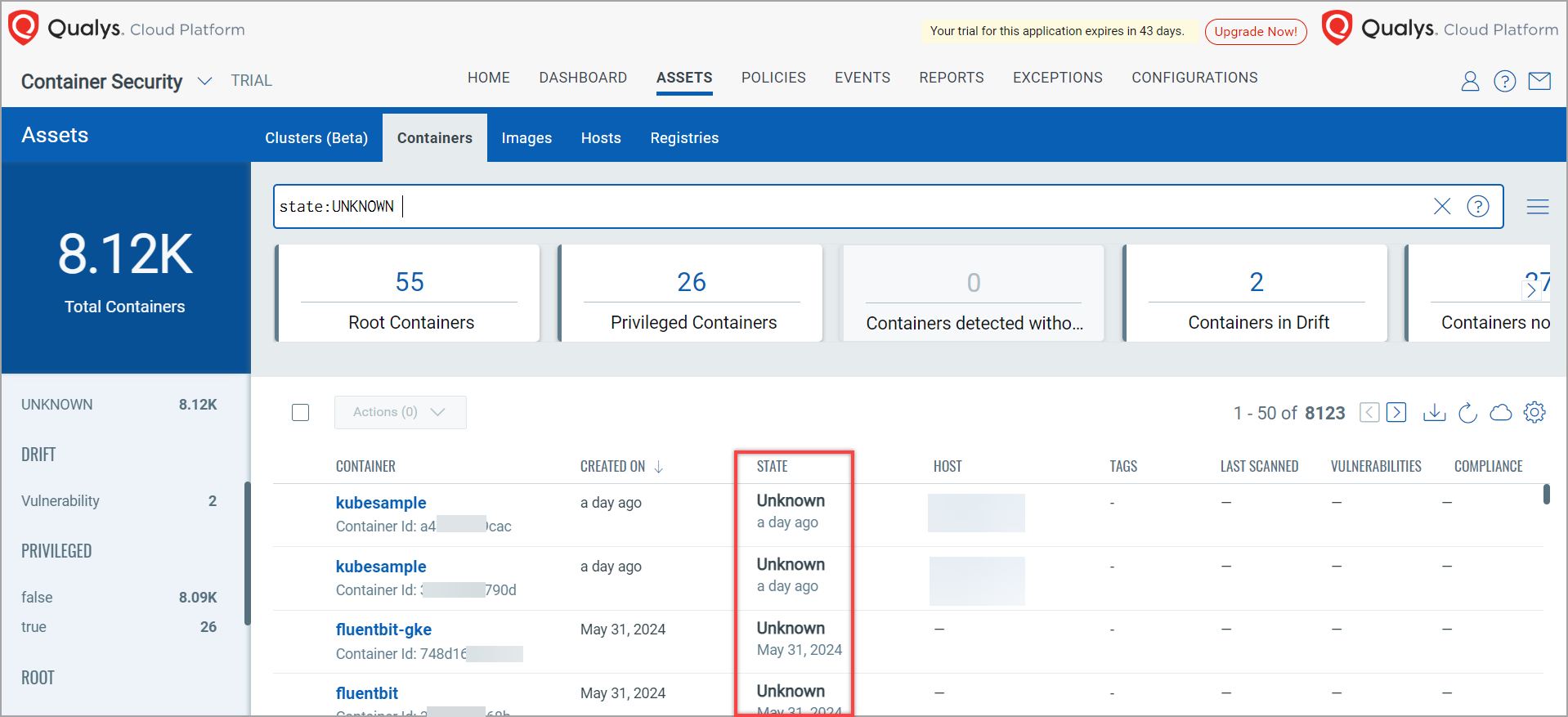
Asset State Management handles the Dangling containers. Dangling containers are the containers whose Container Security sensor is not present on the Qualys Cloud Platform. This may happen when the CS sensor is deleted, but it's respective containers still appear as 'RUNNING' on Qualys Cloud Platform under ASSETS > Containers. As the containers are still displaying a RUNNING state, these containers will never be picked for the Retention service. Such containers need to be cleaned up. With this release, Asset State Management ensures if your container's updated date is older than 7 days and less than 13 months, Qulays marks such container's state as 'unknown'. Whereas, the containers whose updated date is older than 13 months will get deleted.
Change in Data Retention Policy
The data retention policy specifically removes your account data from Qualys Cloud Platform when the time period over which the data is retained exceeds the stated data retention policy period. Earlier, you were able to set the retention periods for various asset types, such as Images, Sensors, and Containers, to 1 Day, 1 Week, 1 Month, 6 Months, or 13 Months. With this release, the 1 Day option is removed. By removing the 1-Day option, we aim to streamline the data management and reduce redundancy. So, going forward, you can set the data retention period to 1 Week, 1 Month, 6 Months, or 13 Months only. Along with this, the Unknown checkbox is checked by default to delete the containers having unknown state. Also, a new setting to retain K8s Admission Controller data is introduced. Using this, you can retain the K8s admission controller data for 1 week, 1 month, 6 months, or 1 year.
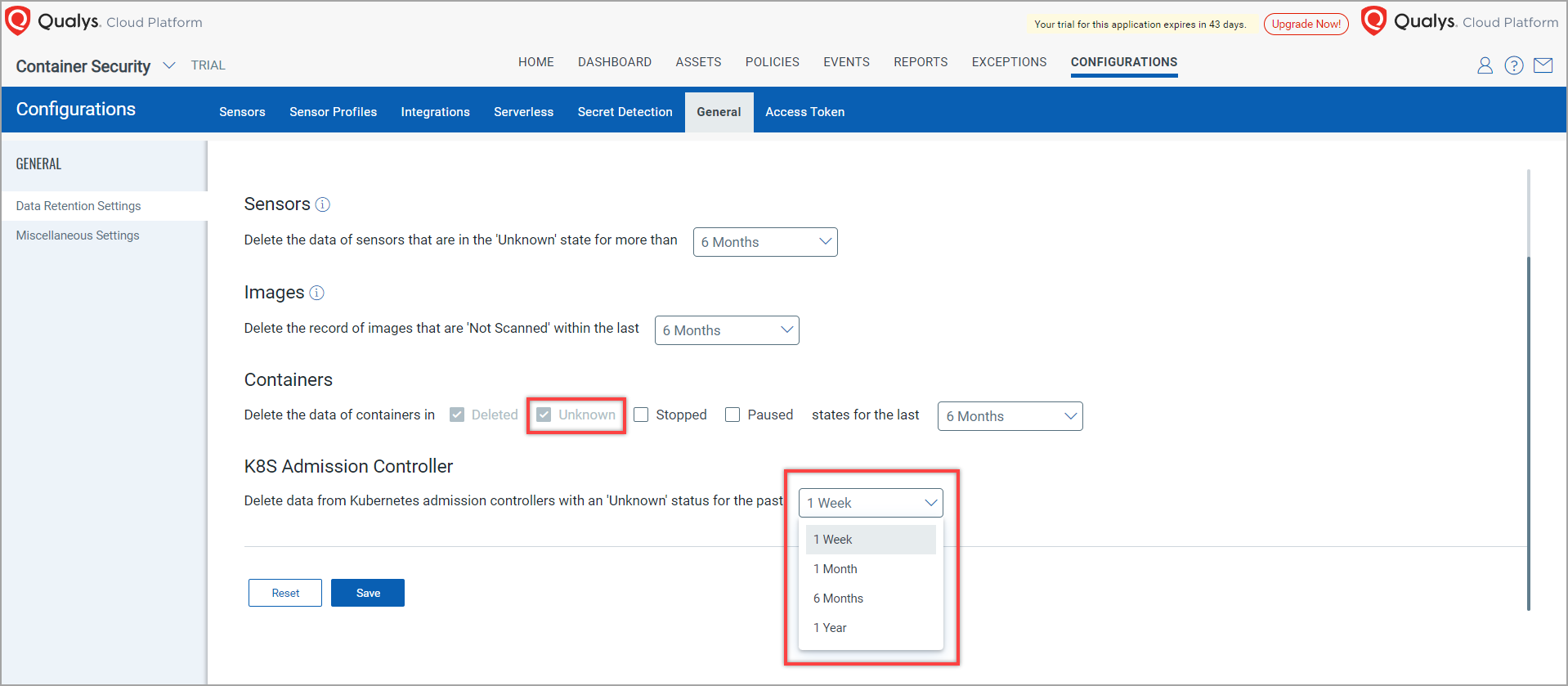
For more information, refer to Data Retention Policy for Container Security in Container Security Online Help.
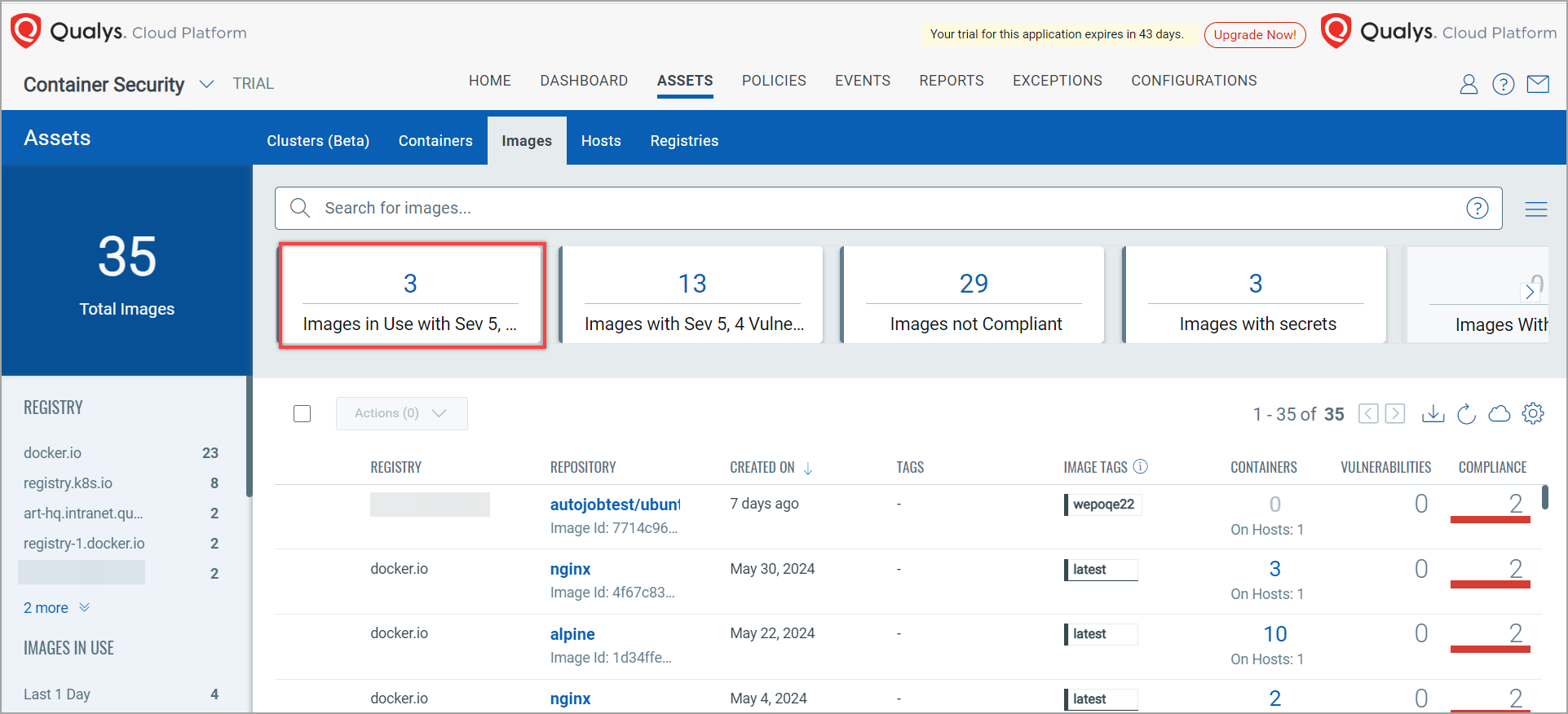
Active Images Detected using Cluster Sensor
With this release, a new tile - Image In Use - is introduced. This tile shows the images detected by Cluster Sensor that are in use and which have vulnerabilities rated as 4 or 5. This will also be helpful to show the containers or PODs that are generated using such images.
CRS 1.0 End of Life
Qualys has deprecated Container Runtime Security (CRS) 1.0 and is revamping the product. CRS 2.0 will be available from a couple of upcoming Container Security releases onwards. With this change, the Runtime tab under Events will no longer be available.
You will also no longer be able to see 'Instrumented' images, containers, and their policies.
See CRS 1.0 deprecation notification here - https://notifications.qualys.com/product/2024/04/18/important-announcement-container-runtime-security-crs-v1-0-end-of-life