Container Security Release 1.37
March 11, 2025
What’s New?
Support Red Hat Scanner Vulnerability Details
With this release, the Qualys Container Security is now 'Red Hat Vulnerability Scanner' Certified enabling you to secure your Red Hat environment. With this change, you can choose to see 'Red Hat Security Advisory (RHSA)' information in Image and Container reports. To support these changes, a few new options are introduced in the 'Image Vulnerability' and 'Container Vulnerability' report templates. To select these new options, go to Container Security > Reports > Create Report > Report Source (Image Vulnerability or Container Vulnerability Report Template) > Report Schedule > Report Display.
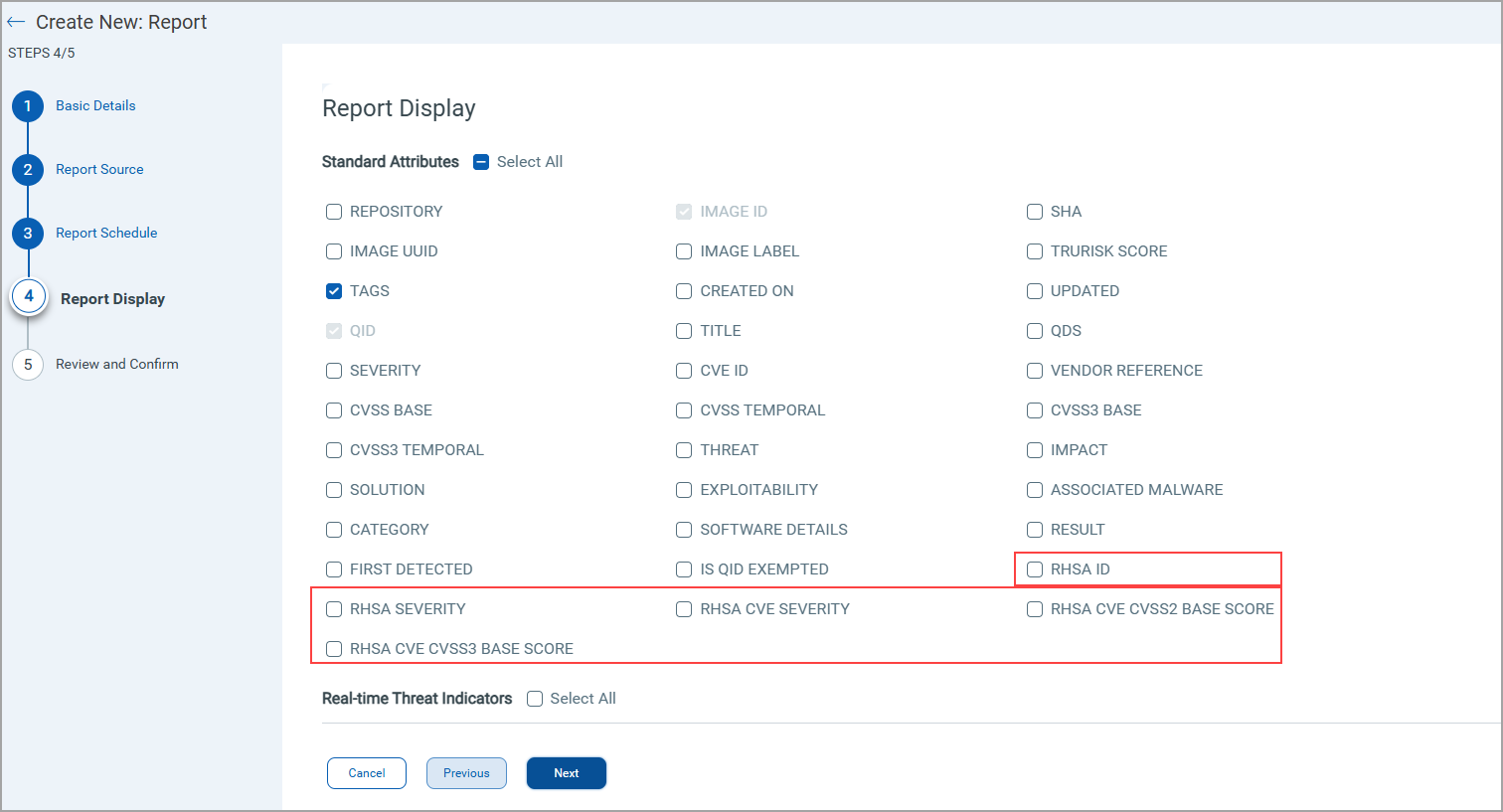
Image Vulnerability Report Display page showing RedHat Scanner options
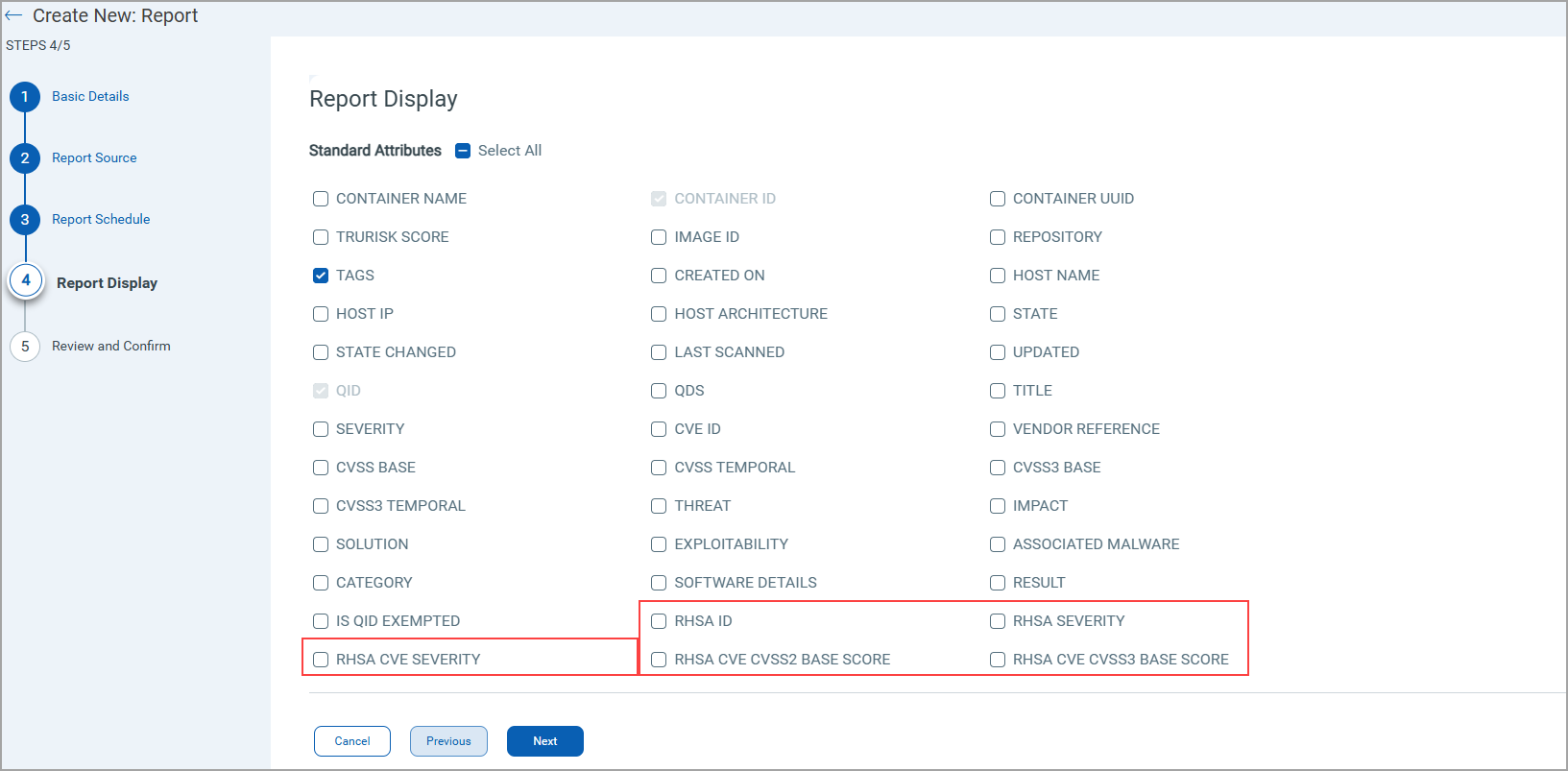
Container Vulnerability Report Display page showing RedHat Scanner options
The table below provides information about the new options introduced for RHSA support.
| Report Template | New Option | Description |
|
Image Vulnerability |
||
| RHSA ID | Generates a column to show Red Hat Security Advisory (RHSA) ID. | |
| RHSA SEVERITY | Generates a column to show RHSA Severity. Valid values - Low, Moderate, Important, or Critical. |
|
| RHSA CVE SEVERITY | Generates a column to indicate the Common Vulnerability Scoring System (CVSS) score ranging from '0' to '10'. | |
| RHSA CVE CVSS2 BASE SCORE | Generates a column to show CVSS version 2 base score ranging from '0' to '10'. | |
| RHSA CVE CVSS3 BASE SCORE | Generates a column to show CVSS version 3 base score ranging from '0' to '10'. |
After opting for the RHSA options, the resultant report shows the RHSA columns.
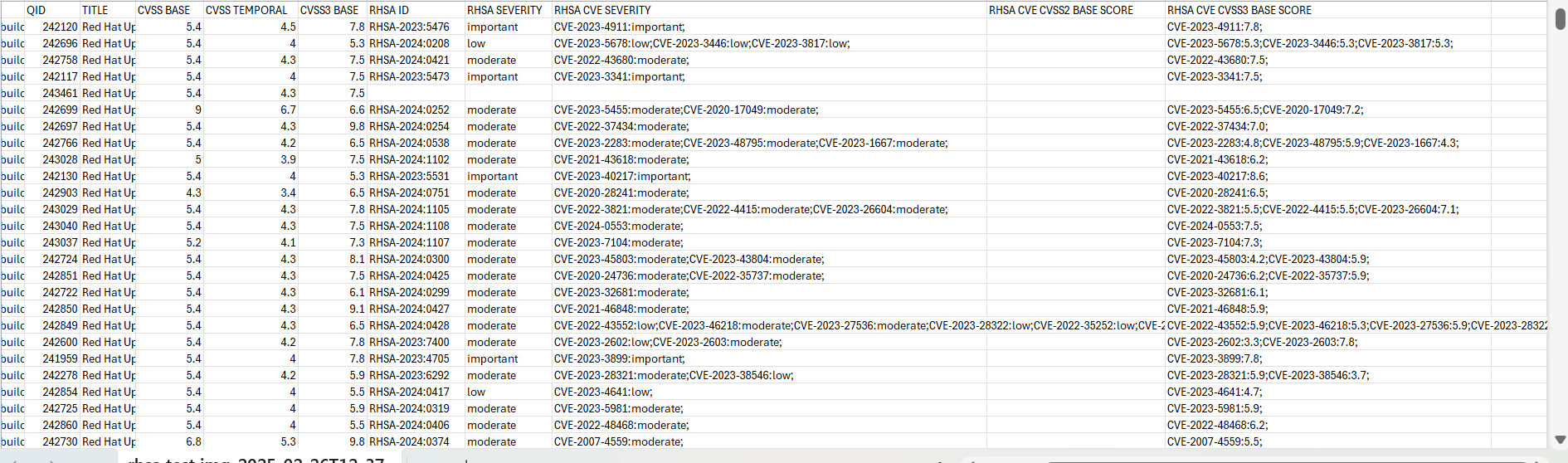
- If a QID has more than one RHSA ID, the first RHSA ID will be considered and ignoring the others.
- In the absence of RHSA ID or RHSA CVE Severity, the QID shows RHSA ID or RHSA CVE Severity as 'Null'.
QQL Token Updates
With the RedHat certification, the Container Security has introduced the following QQLs.
QQL Page on Qualys Enterprise TruRisk™ Platform: Container Security > Assets > Images
- vulnerabilities.vendorData.rhsa.severity
- vulnerabilities.vendorData.rhsa.id
- vulnerabilities.vendorData.rhsa.cve.severity
- vulnerabilities.vendorData.rhsa.cve.cvss2.baseScore
- vulnerabilities.vendorData.rhsa.cve.cvss3.baseScore
QQL Page on Qualys Enterprise TruRisk™ Platform: Container Security > Assets > Image > View Details
- vendorData.rhsa.severity
- vendorData.rhsa.id
- vendorData.rhsa.cve.severity
- vendorData.rhsa.cve.cvss2.baseScore
- vendorData.rhsa.cve.cvss3.baseScore
To know more about the QQLs and their usage, refer to CS Online Help.
To know more about Qualys Red Hat Scanner Certification, refer to
- Red Hat Catalog - https://catalog.redhat.com/software/vulnerability-scanner/detail/267277
- Qualys Blog on Red Hat Certification - https://blog.qualys.com/product-tech/2025/02/25/qualys-totalcloud-kcs-achieves-red-hat-vulnerability-scanner-certification
Support Host Architecture Information in Container Vulnerability Report
Containers are built using specific architecture types, such as x86_64, or ARM, and so on. Understanding the host architecture is essential for determining whether it affects your environment, applying appropriate patches, and ensuring that your containerized applications are properly secured. It also helps you to ensure that vulnerability management strategies are aligned with the specific characteristics and requirements of the underlying hardware architecture.
The container vulnerability reports can now show the information about the host architecture used in the containers. To support this change, a new option 'HOST ARCHITECTURE' is introduced in the 'Container Vulnerability' report display. To select this new option, go to Container Security > Reports > Create Report > Report Source (Container Vulnerability Report Template) > Report Schedule > Report Display.
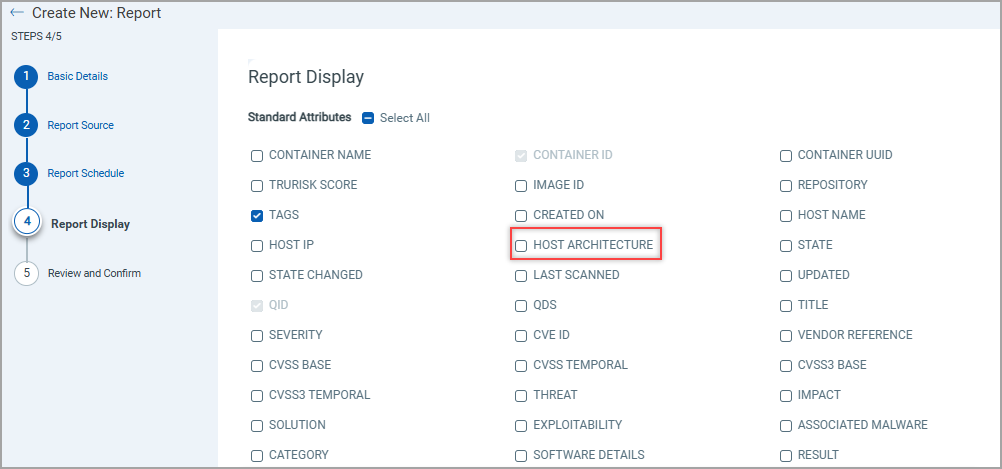
The table below provides information about the new option.
| Report Template | New Option | Description |
| Container Vulnerability | Host Architecture | Generates the Host Architecture column in the Container report. The column shows the host architecture used. Valid values: amd64, arm64, or x86_64 |
Select the 'HOST ARCHITECTURE' option to add a new column in the respective container vulnerability report. 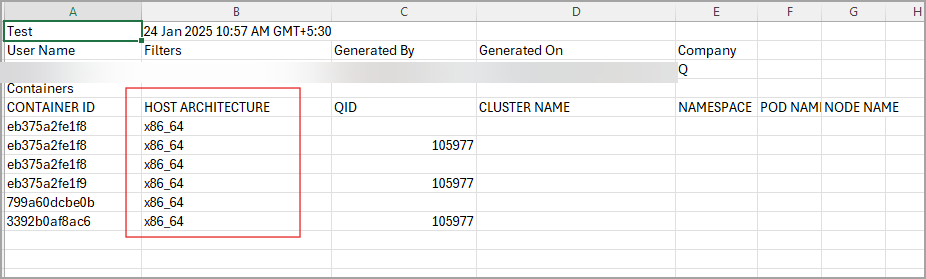
Ability to Enable or Disable the Vulnerability Exception
You now have an option to enable or disable the Vulnerability Exception. Along with this, you can see exempted vulnerabilities in Vulnerabilities list pages of Images, and Containers.
A new option called Include exempted vulnerabilities is available under Assets > Images/Containers > Image/Container details > Vulnerabilities. When you enable 'Include exempted vulnerabilities' toggle you will see new column 'EXEMPTED' in the vulnerabilities list to show if a QID is exempted. It carries either True (Exempted vulnerability) or False (non-exempted vulnerability) value.
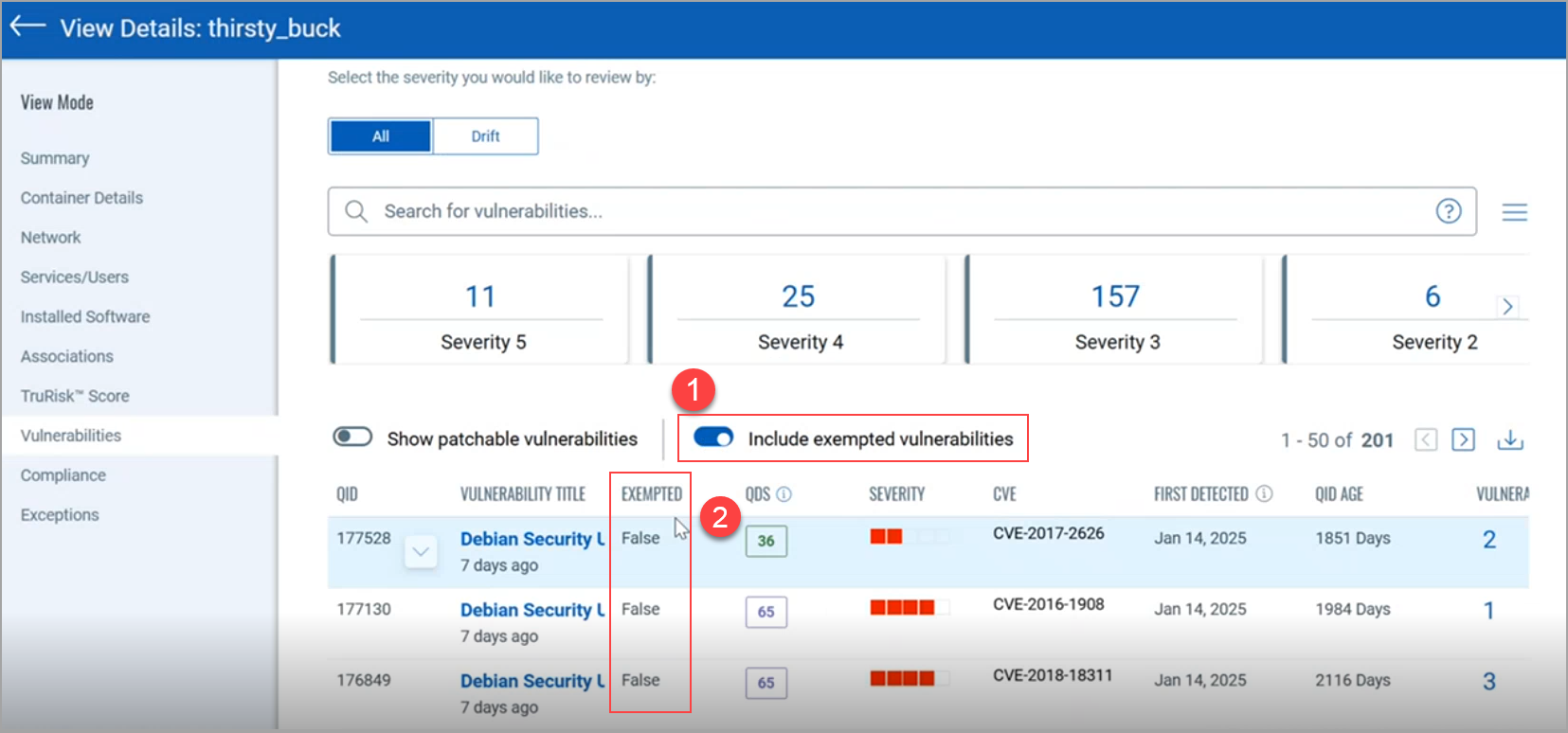
You can get a list of all exempted QIDs by filtering the container or image vulnerability CSV report (Assets > Images/Containers > Image/Container Details > Vulnerabilities).
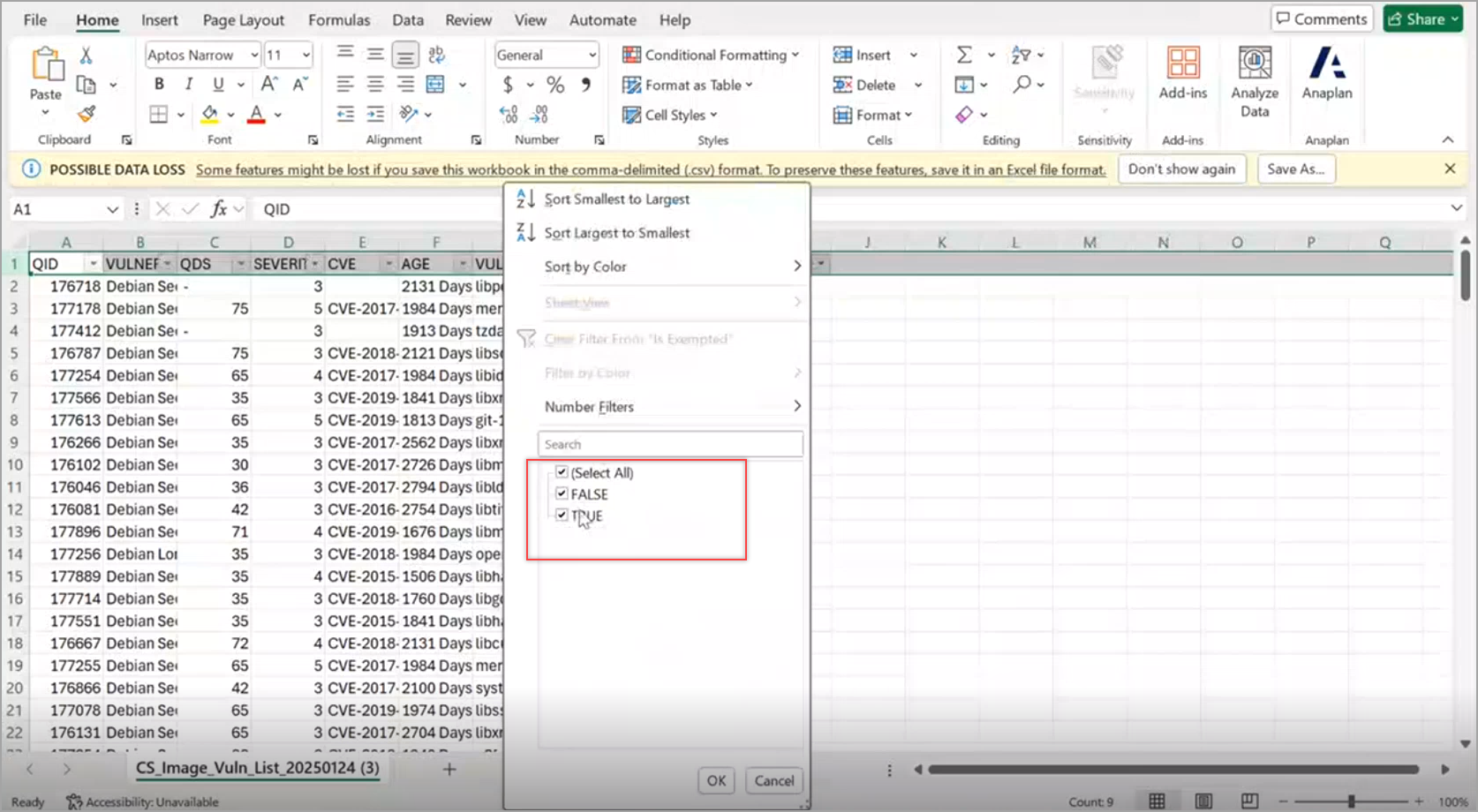
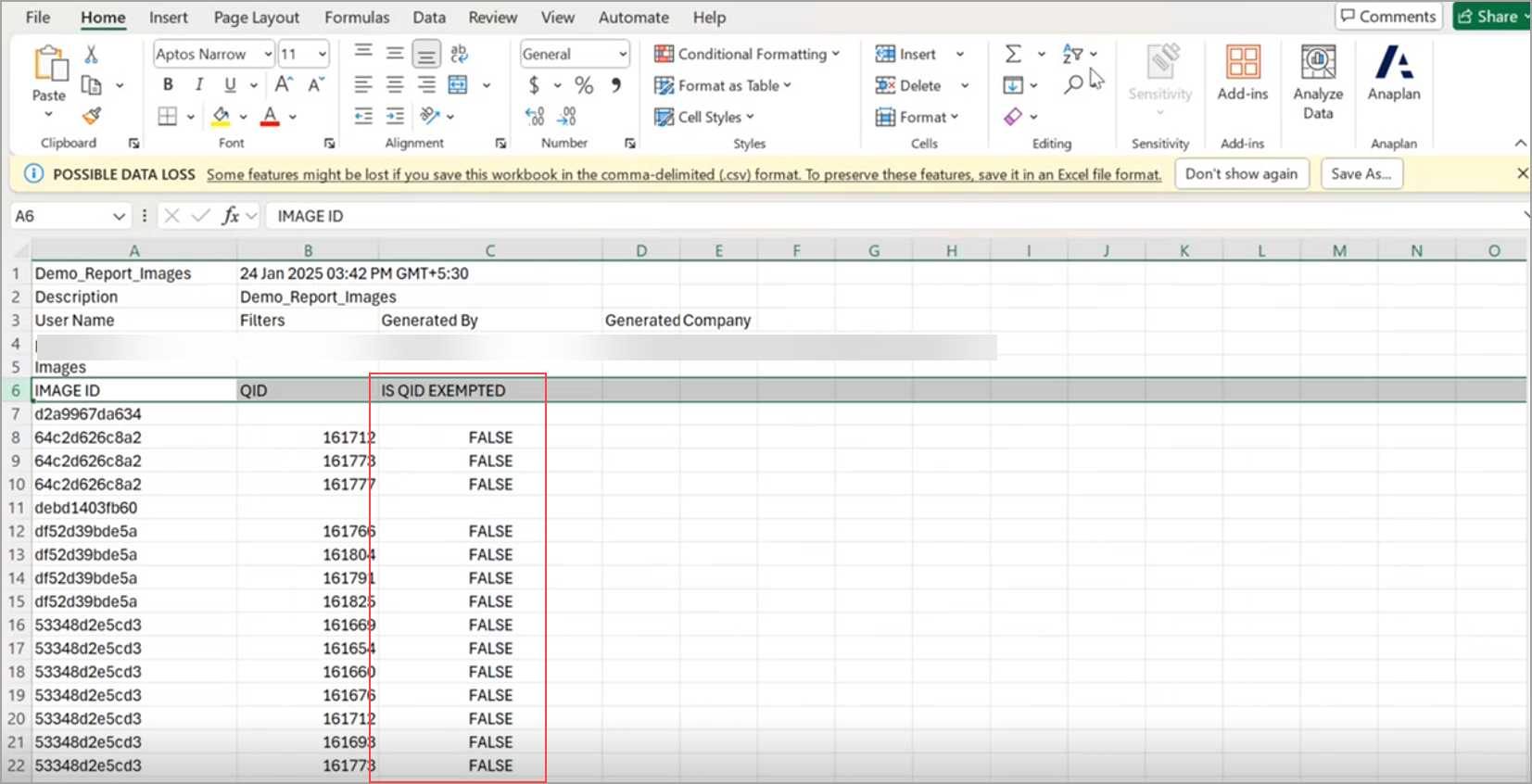
Similarly, you can also see the exempted QIDs in the 'Image Vulnerability' and 'Container Vulnerability' reports. To show such exempted vulnerabilities, a new option 'IS QID EXEMPTED' is introduced in the Report Display page.
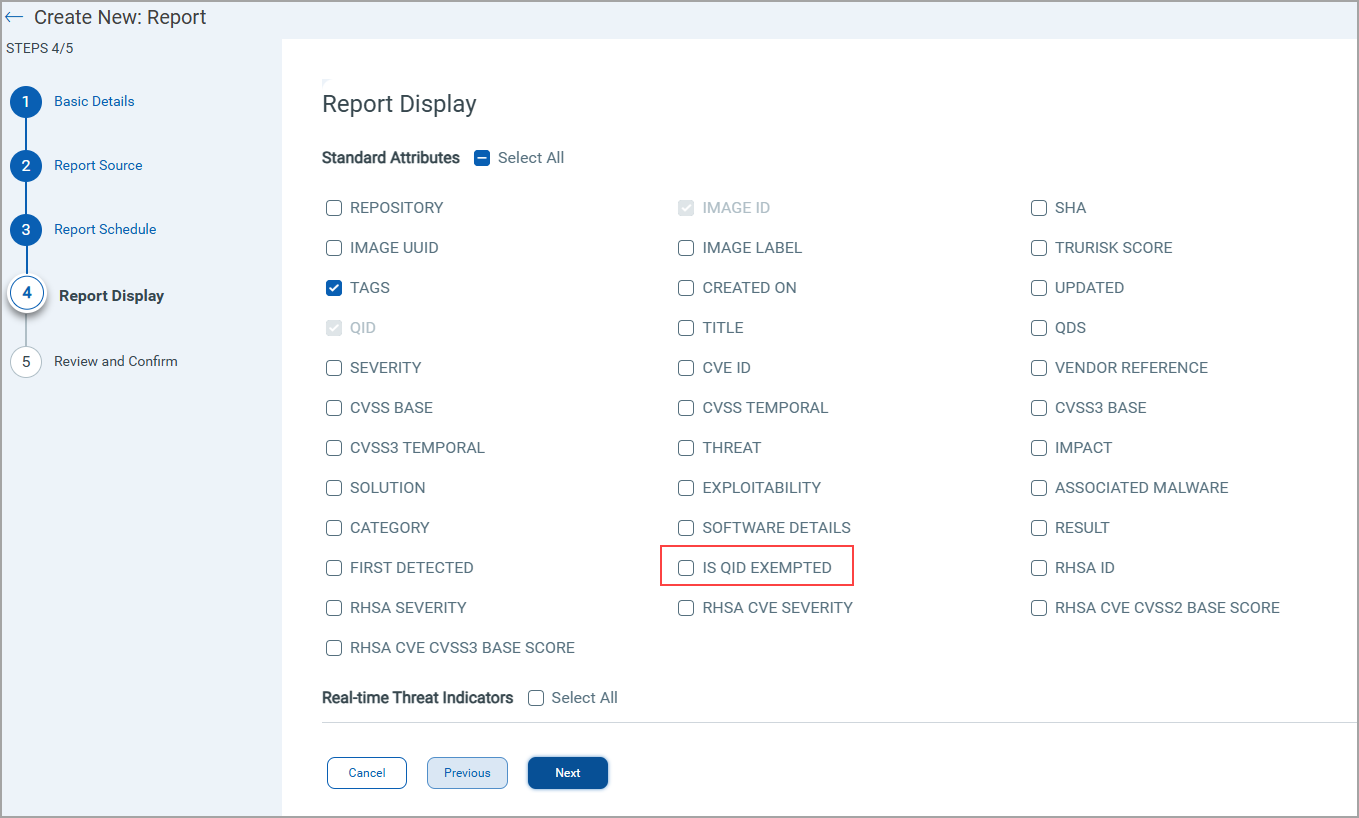
Image Vulnerability Report Display
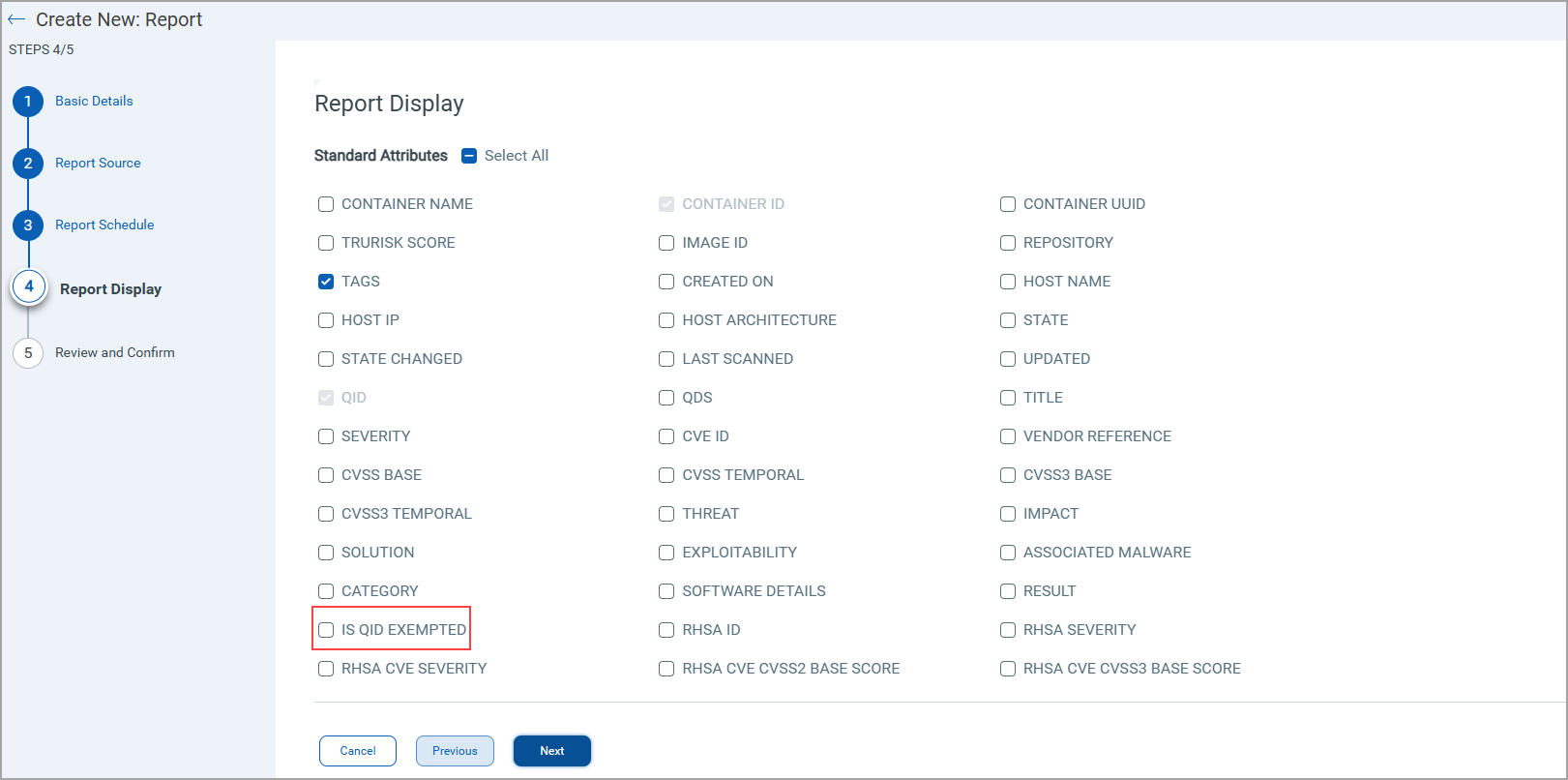
Container Vulnerability Report Display
The table below provides information about the new options.
| Report Template | New Option | Description |
| Image Vulnerability And Container Vulnerability |
IS QID EXEMPTED | Generates the IS EXEMPTED column to indicate if any QID is exempted. Valid values: True or False. |
Select the 'IS QID EXEMPTED' option to add a new column in the respective image or container vulnerability report. See the Image vulnerabilities report shown below that shows the IS QID EXEMPTED column. A similar column is displayed in a Container Vulnerabilities report. You can also use filter option to display exempted (True) and non-exempted (False) QIDs.
Ability to Detect Per Layer Vulnerability
Container images are built up in layers, and each layer can introduce specific security risks or vulnerabilities. Understanding vulnerabilities at the layer level provides granular insights and helps you manage security risks more effectively.
Earlier, Qualys Container Security used to show Image SHA of the base image. With this release, under Images > Image Details > Layers, you can see details of each layer present in your image. These details include Layer ID, Command used while creating the layer, layer creation date, and vulnerabilities found in that layer along with its severity level. Qualys Container Security has introduced a new tag - Base to indicate Base layers present in your image. You can also use Base Layer option from the Layer Type drop-down to quickly filter out Base layers present in that image. Select Application Layer to see only Application layers present in that image. The Show only vulnerable layers toggle bar shows layers having vulnerabilities.
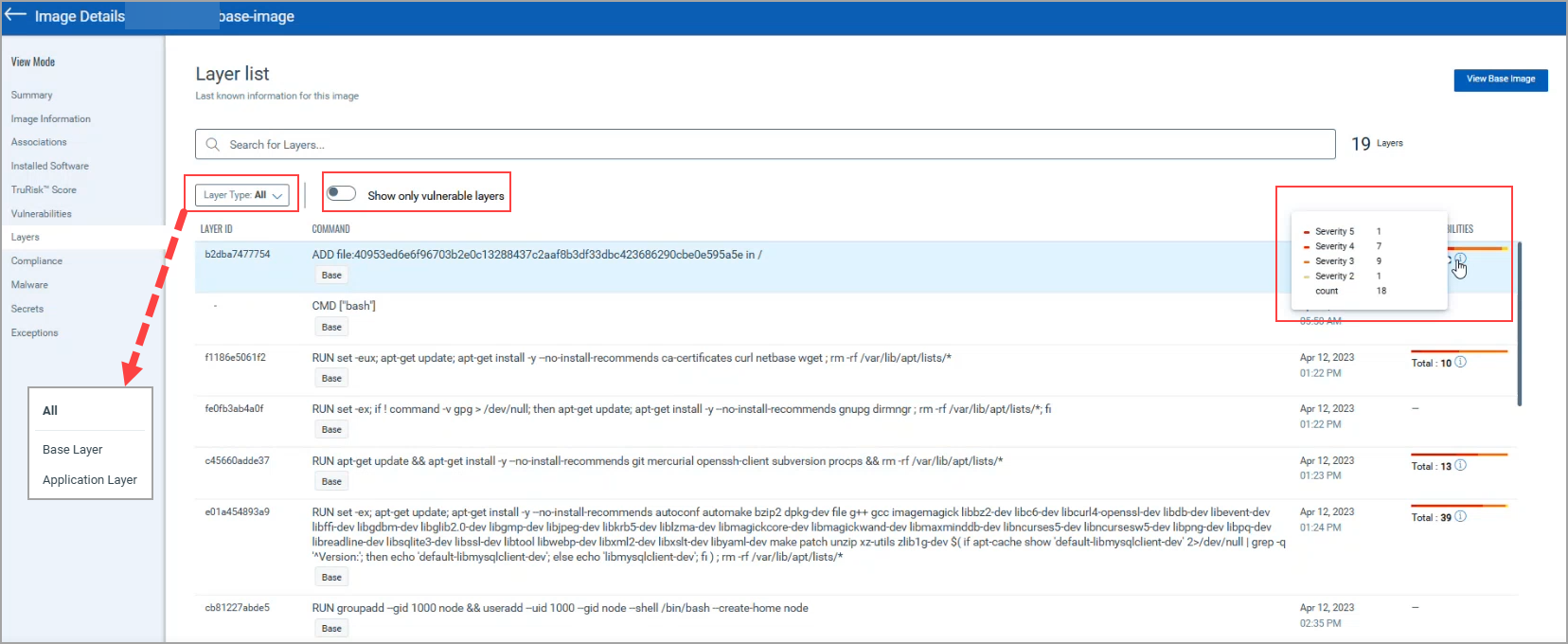
Click the Vulnerabilities present in an layer to go to the Vulnerabilities page that shows vulnerabilities present in that layer along with their details.
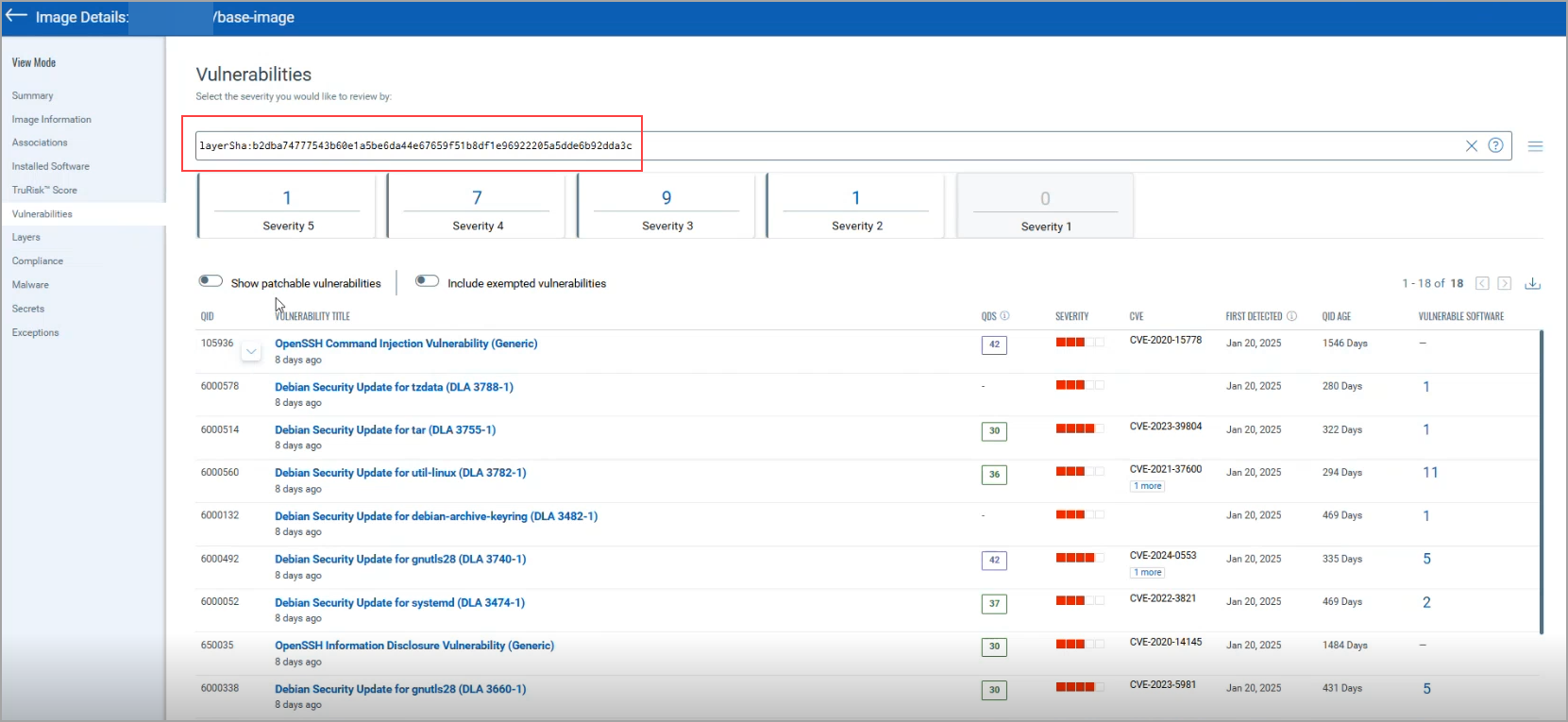
QQL Token Updates
With the Per layer Vulnerability, the Container Security has introduced the following QQLs.
QQL on Qualys Enterprise TruRisk™ Platform: Container Security > Assets > Images
- vulnerabilities.layerSha
QQL on Qualys Enterprise TruRisk™ Platform: Container Security > Assets > Images > Image Details > Vulnerabilities
- layerSha
To know more about the QQLs and their usage, refer to CS Online Help.