Define Filter Criteria in External Attack Surface Management (EASM) Configuration Profile
Let us understand the filter criteria that enable you to discover externally exposed hosts. When you configure EASM for the first time, verify the Organization and the Domain details.
Explore the following to understand more about filter criteria for an EASM configuration profile:
- Important to Know
- Know More about Include and Exclude Types and Filters
- Domain and Organization Validation
- Add Filters
- Add Section
- Add Exclusion
- Import Seed Values in Bulk from CSV File
- Optional Settings
Important to Know!
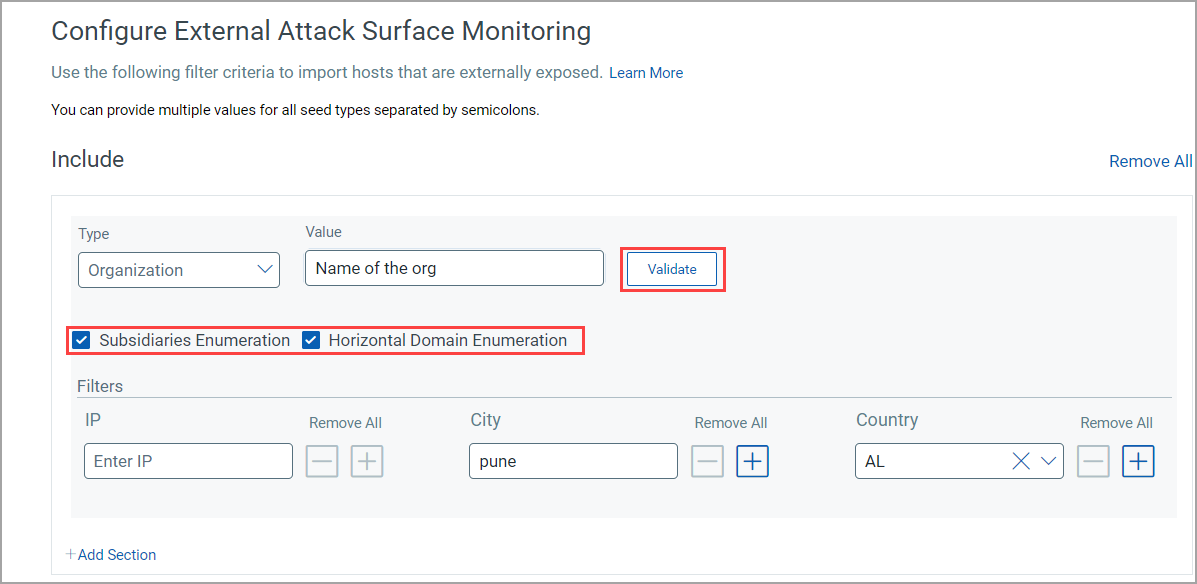
- Subsidiaries Enumeration and Horizontal Domain Enumeration are selected by default for Organization and Domain seed types only. If cleared, they are not included in the configuration.
- You can provide multiple values for all seed types by separating them with semicolons. You can also import seed values in bulk from CSV.
- If the same IP address is included and excluded, the exclusion takes precedence.
Know More about Include and Exclude Types and Filters
Seed Type for Include
| Filter | Description | Examples |
|---|---|---|
| Organization | Name of the organization that owns the IP space. The correct legal entity name should be used. | Google LLC |
| Domain/Subdomain | Domain or Subdomain of the assets. Only top-level domain expected. Autocomplete helps quickly configure by showing top 5 suggestions after typing three characters. | google.com |
| IP/Netblock | Alias for net filter string | 34.120.218.237 |
| Certification Subject | Certificate subject name | cadz02.canadadz.com |
| ASN | Autonomous System Numbers. Including ASN discovers netblocks in Shodan and active assets during sync. | AS123456 (must start with "AS" followed by up to 6 digits) |
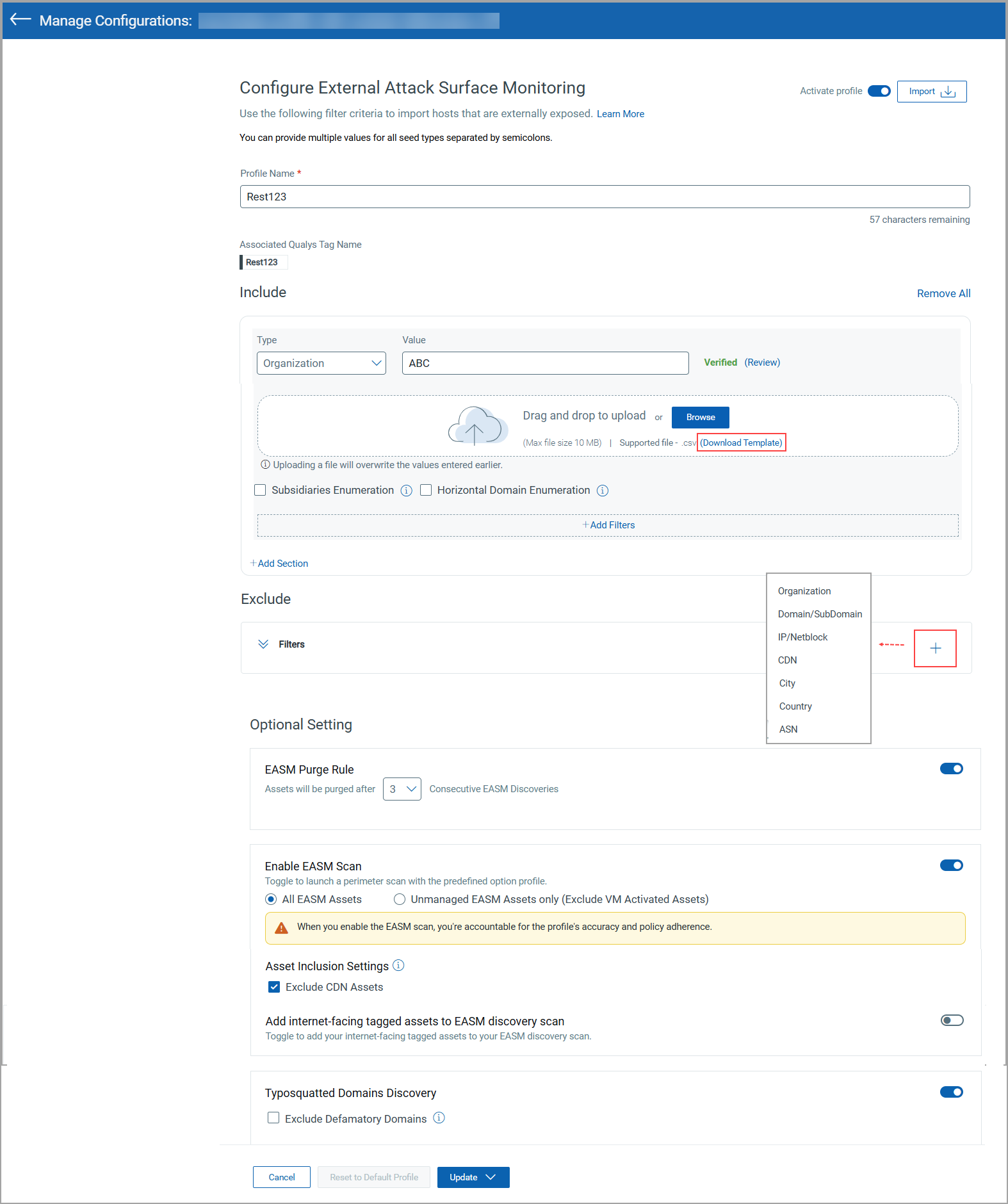
Seed Type for Exclude
You can add Exclude filters while creating or modifying the profile. Values can also be imported from CSV.
![]()
| Filter | Description | Examples |
|---|---|---|
| Organization | Name of the organization that owns the IP space | Google LLC |
| Domain/Subdomain | Domain or Subdomain of assets | qualys.com, doc.qualys.com |
| IP/Netblock | Alias for net filter string | 34.120.218.237 |
| City | Name of the city | Kansas City |
| Country | 2-letter country code | US |
| CDN | Default is True. Cannot be added multiple times. | - |
| ASN | Autonomous System Numbers. Excluding ASN prevents associated netblocks discovery in Shodan and sync. | AS123456 |
Domain and Organization Validation
You can validate a domain or organization to fetch subsidiaries based on the value entered.
Validation is not supported for multiple values. The Validate button appears only after entering a value.
Vertical Enumeration for EASM Discovery
Allows discovery of sibling subdomains of included subdomains.
- If Vertical Enumeration is not selected, validation is not done after clicking Check Catalog.
- If selected, validation occurs only if the primary domain exists in the catalog.
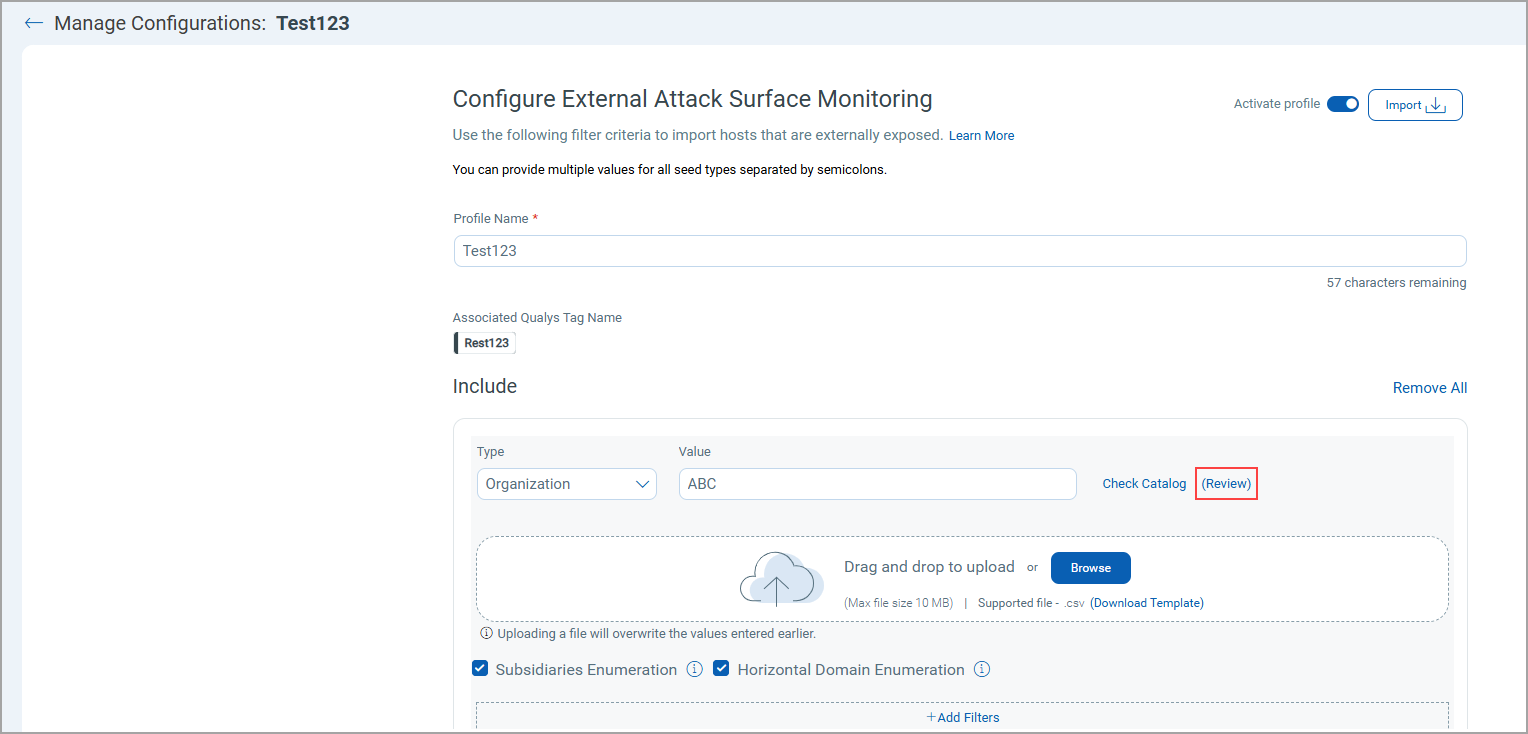
Insight into User-defined, Catalog, and Enumerated Data
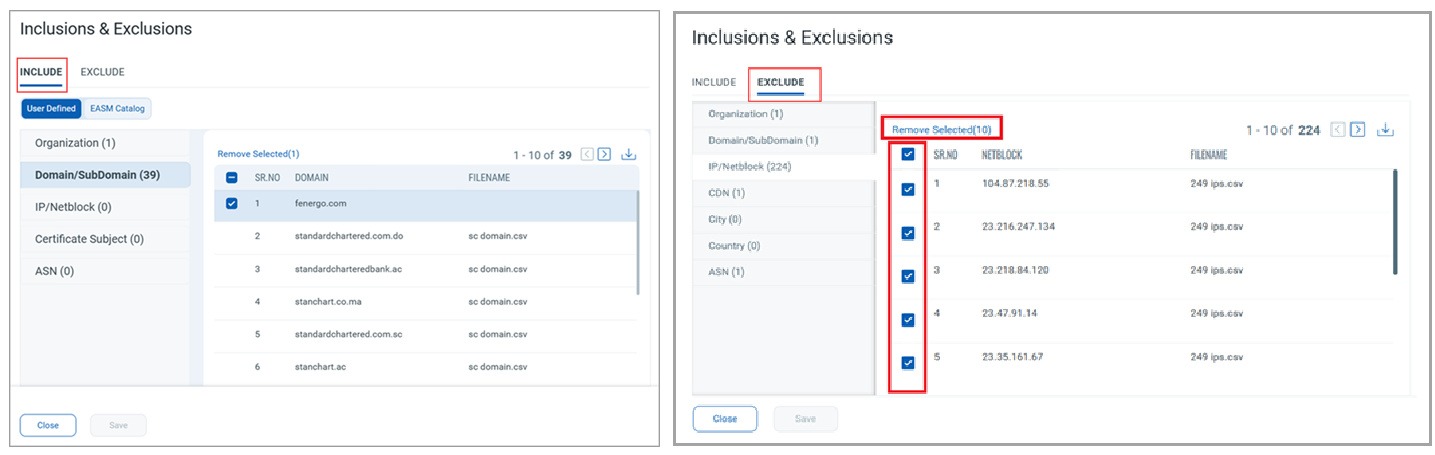
- Review shows user-defined and catalog data, including file names if imported via CSV.
- Pagination is supported for large data sets.
- You can download data in CSV, HTML, or XML formats.
- You can remove uploaded include/exclude values during edit.
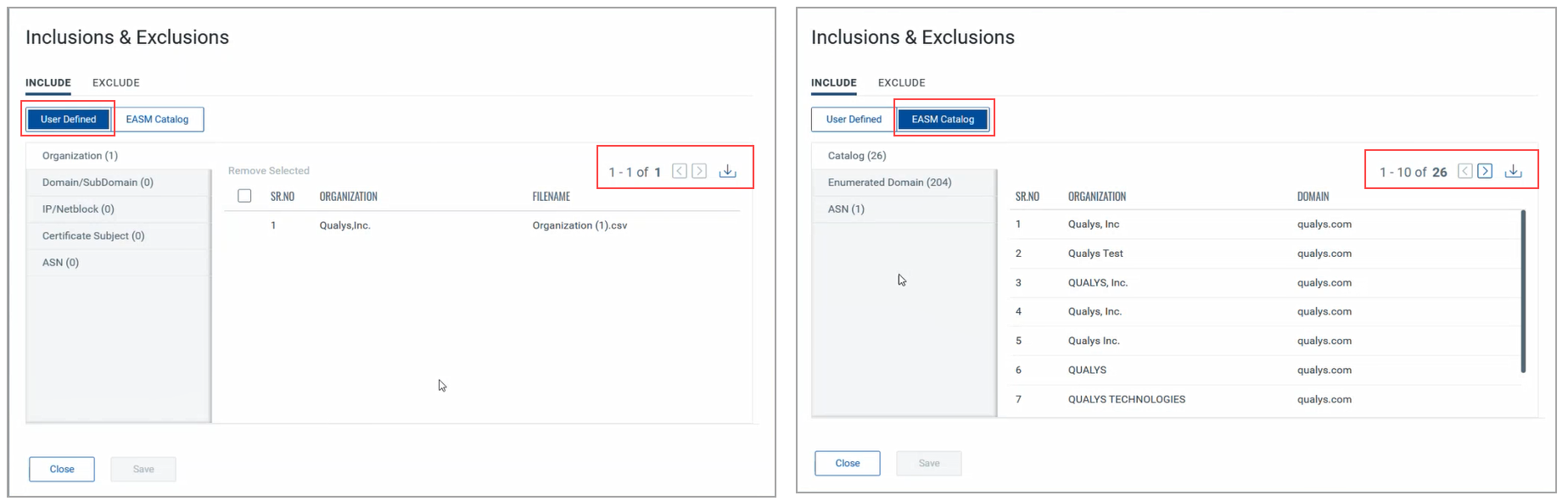
Subsidiary data syncs only if Subsidiaries Enumeration and Horizontal Domain Enumeration are selected.
Scenarios
Scenario 1 (Validation Successful): Validation succeeds for the entered domain or organization.
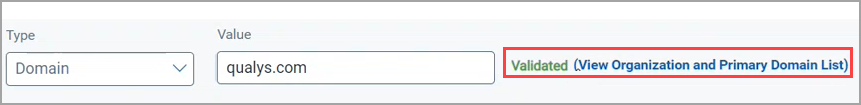
Scenario 2 (Validation Pending): Value not found in catalog, marked as "Pending Validation".
If reviewed and added to the catalog later, the status changes to Validated.
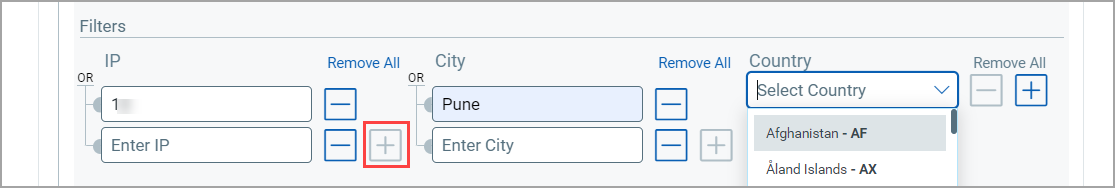
Add Filters
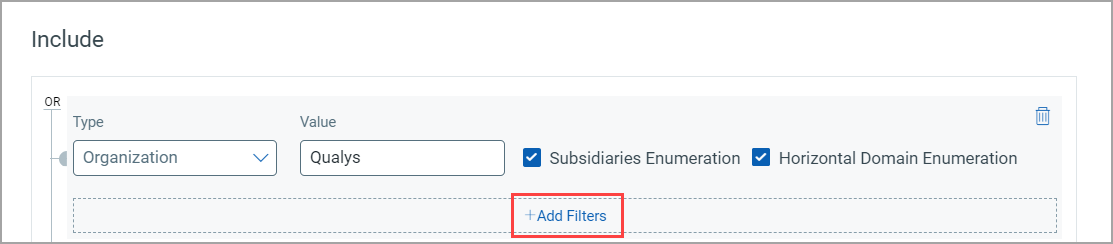
Click Add Filters to add multiple seed filters with an AND relation.
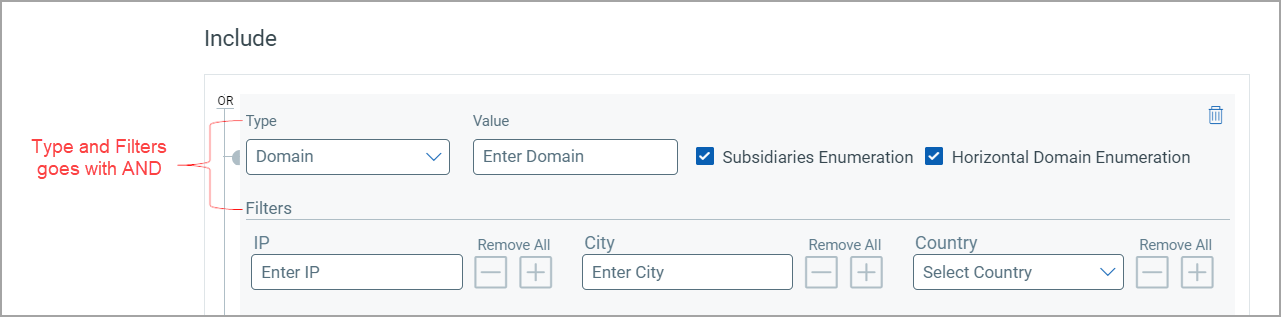
- Use the plus icon to add multiple IPs and cities, or enter them as semicolon-separated values.
- Select countries from the list; the 2-letter code is auto-selected.
Character limit is 4000 for IP and Country filters; 100 for City filter.
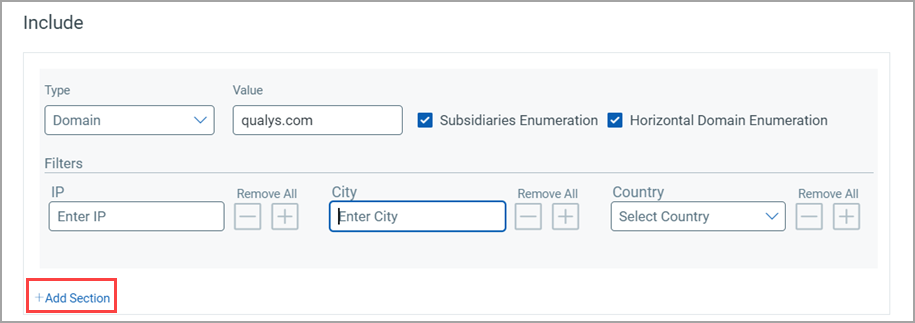
Add Section
Click Add Section to create a new filter section for each seed type.
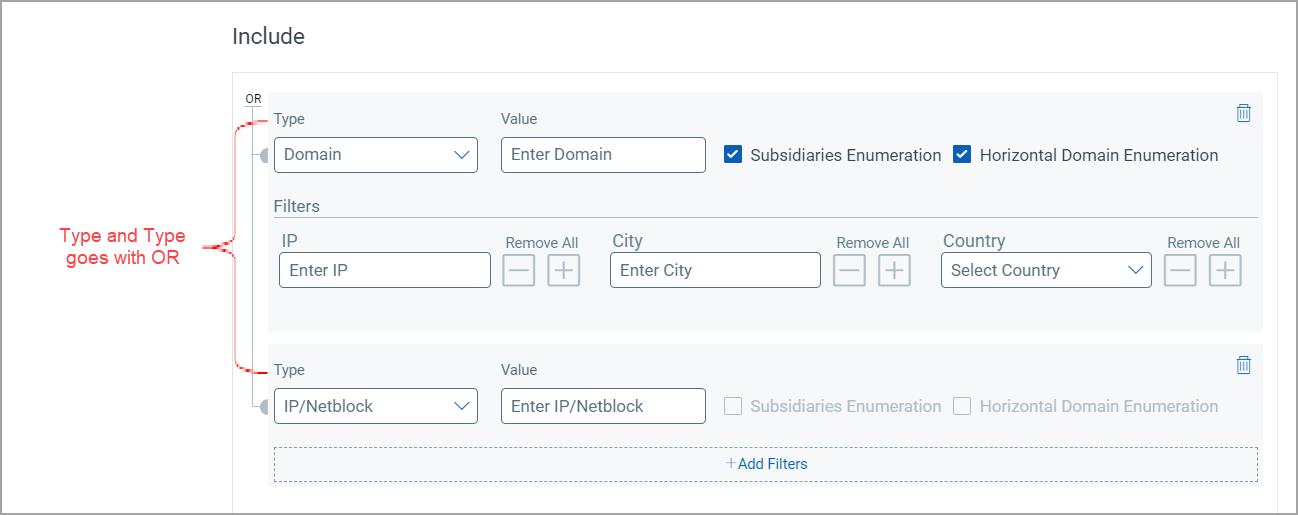
Add Exclusion
The Exclude section is combined with Include using an AND relation.
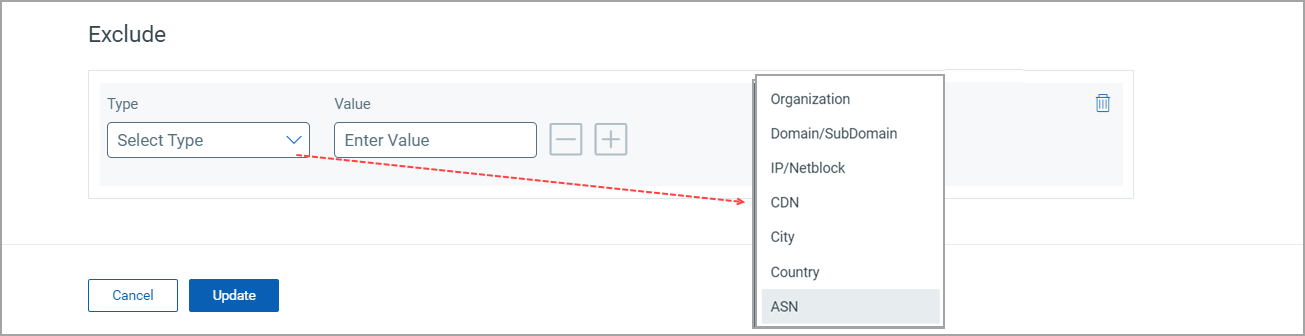
You can also exclude IP addresses from discovery.
Import Seed Values in Bulk from CSV File
You can import Include/Exclude seed values in bulk by uploading a CSV file instead of entering them manually.
- Download the provided template for the correct format.
- CSV import supported for Domains, Subdomains, Organizations, IP/Netblocks, and ASN.
- Semicolon/comma-separated strings are not supported.
- Incorrect file type (e.g., Organization CSV uploaded for Domain) is rejected.
Optional Settings
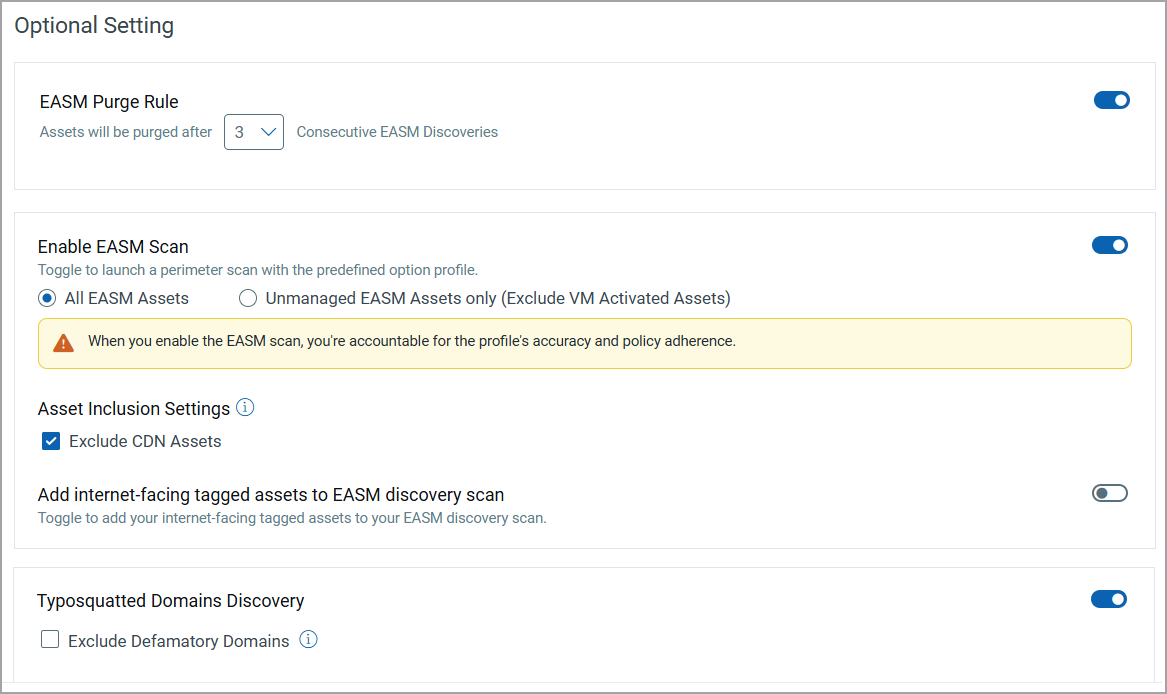
EASM Purge Rule
Automates purging of assets not discovered after a specified number of discoveries (0–10, default 3).
Enable EASM Scan
Starts the EASM lightweight scan. Configure the scan using the options below.
When you save or update a profile, the system follows a predefined sequence of operations to discover assets and reflect the associated data in the EASM view. The following sequence is followed:
- After saving/updating the profile, the discovery process is triggered 1 hour later.
- Scans are triggered 24 hours after the discovery process is completed.
- Data starts appearing once the scans are completed.
The vulnerabilities discovered through the scan are displayed on the EASM > Vulnerabilities tab.
All EASM Assets
Includes VM-activated assets and managed assets with the EASM source.
Unmanaged EASM Assets only (Exclude VM Activated Assets)
Includes only unmanaged assets.
Tag-based Scope for EASM Scan
The EASM lightweight scan can be configured to perform the scan on selective assets. Instead of scanning all your EASM assets, you can limit the scan scope by including or excluding assets using asset tags. Use the Add Tags or Exclude tags option as required.
When specifying tags, you can choose one of the following conditions:
- ANY: Includes assets that have any of the specified tags.
- ALL: Includes assets that have all of the specified tags.
If you exclude assets from the EASM scan, the vulnerabilities discovered on those previously scanned assets are not deleted. They are still visible on the EASM > Vulnerabilities tab.
Asset Inclusion Settings
Your CDN assets are included in the EASM scan by default. You can select the Exclude CDN Assets checkbox to exclude your CDN assets from scans.
Add Internet-facing Tagged Assets
Toggle to include Internet-facing tagged assets (VM and cloud agent) in discovery. If disabled, related info is removed from the Asset Details page.
Add Internet-facing tagged assets to EASM discovery scan
Use this optional setting to add Internet-facing tagged assets to the EASM discovery scan, in addition to Organization and Domain, etc. Your Internet-facing tagged assets, including scanned and cloud agent assets, are picked up as input to EASM. After the sync, you can see the External Attack Surface details on the “Asset Details” page.
Typosquatted Domains Discovery
Toggle to detect typosquatted domains.
If the Exclude Defamatory Domains checkbox is
- Selected, the scan excludes defamatory domains.
- Not selected, the scan includes defamatory domains.
View results in Inventory > Domains tab. For more information, refer to View Domain Details.
Domain Security
Toggle to enable the monitoring of DomainKeys Identified Mail (DKIM) and Sender Policy Framework (SPF) records of your internet-facing domains.
For more information, refer to EASM Domain Security.