Viewing Inventory of External Attack Surface Discovered Assets from EASM Toggle
When you toggle the CSAM EASM toggle to see the EASM assets, you can see the metadata of externally exposed assets, such as domains, subdomains, ports, etc.
You can find detailed information about the externally exposed assets that facilitate you to take desired actions on these assets.
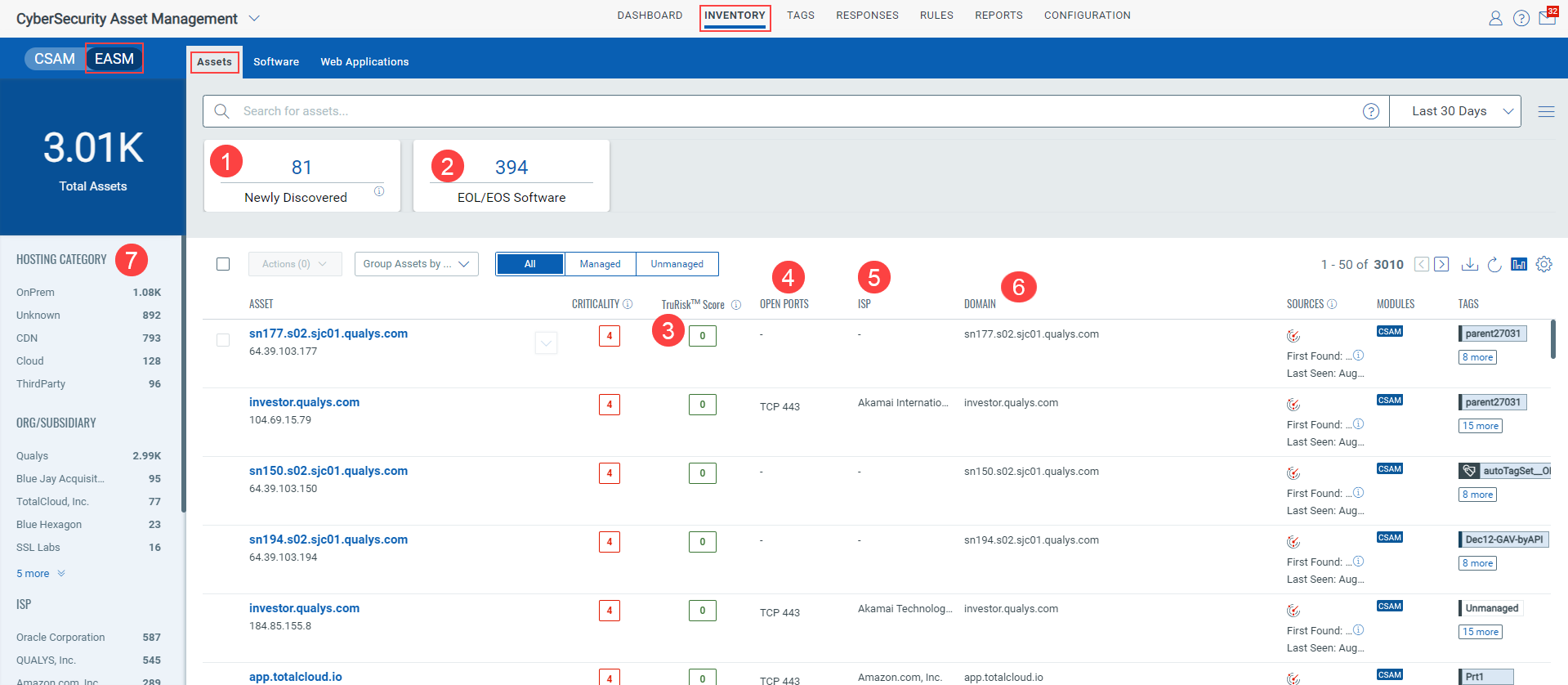
(1) On the Newly Discovered tile, you can see the newly discovered externally exposed assets from the latest scan.
(2) On the EOL/EOS Software tile, you can see the count of EOL and EOS software for externally exposed assets. Upon clicking the EOL/EOS count, you are navigated to Inventory > Software.
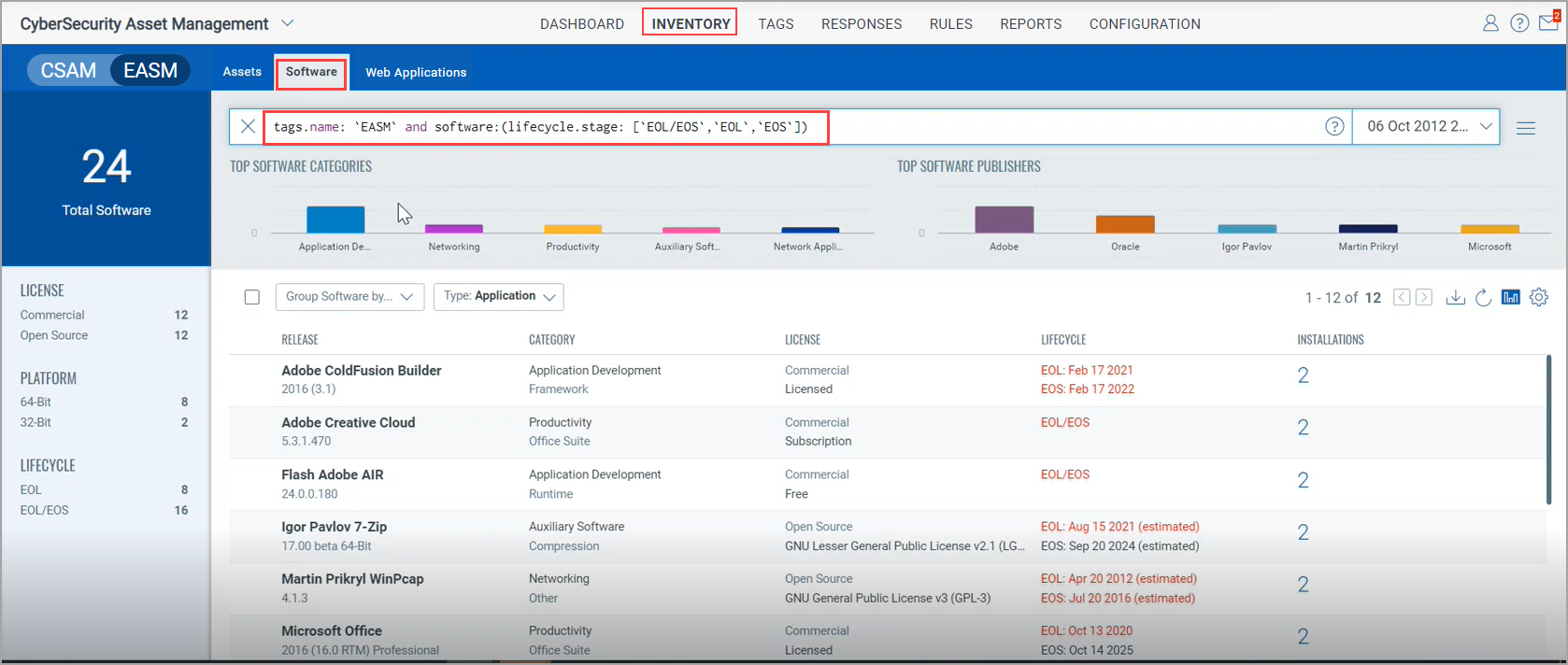
Note:
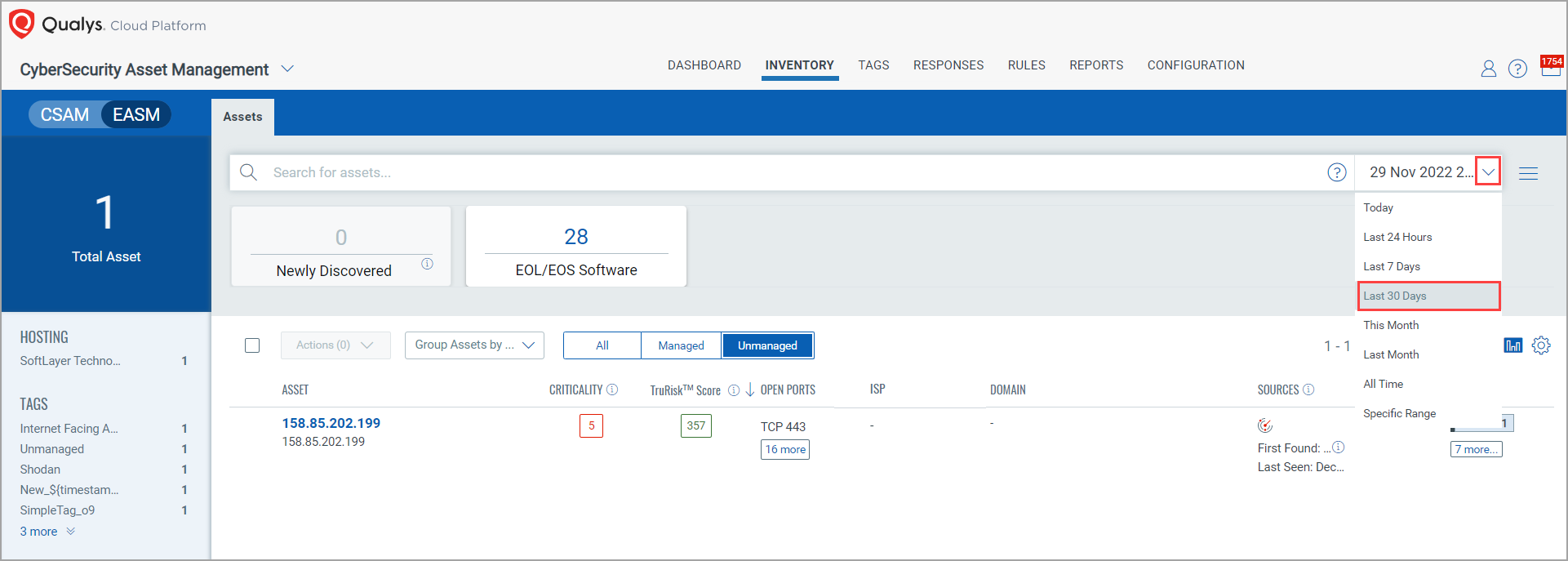
- The counts on the Newly Discovered and EOL/EOS Software tiles are shown based on the days, hours, or days range option that you select. These counts don’t change until you change the option that you selected.
See the following screen capture that shows the changed count on the Newly Discovered tile after changing the filter option.
- Also, the counts don’t change though you run any QQL.
(3) TruRisk Score: You can see the TruRisk Score for assets on which vulnerabilities are detected.
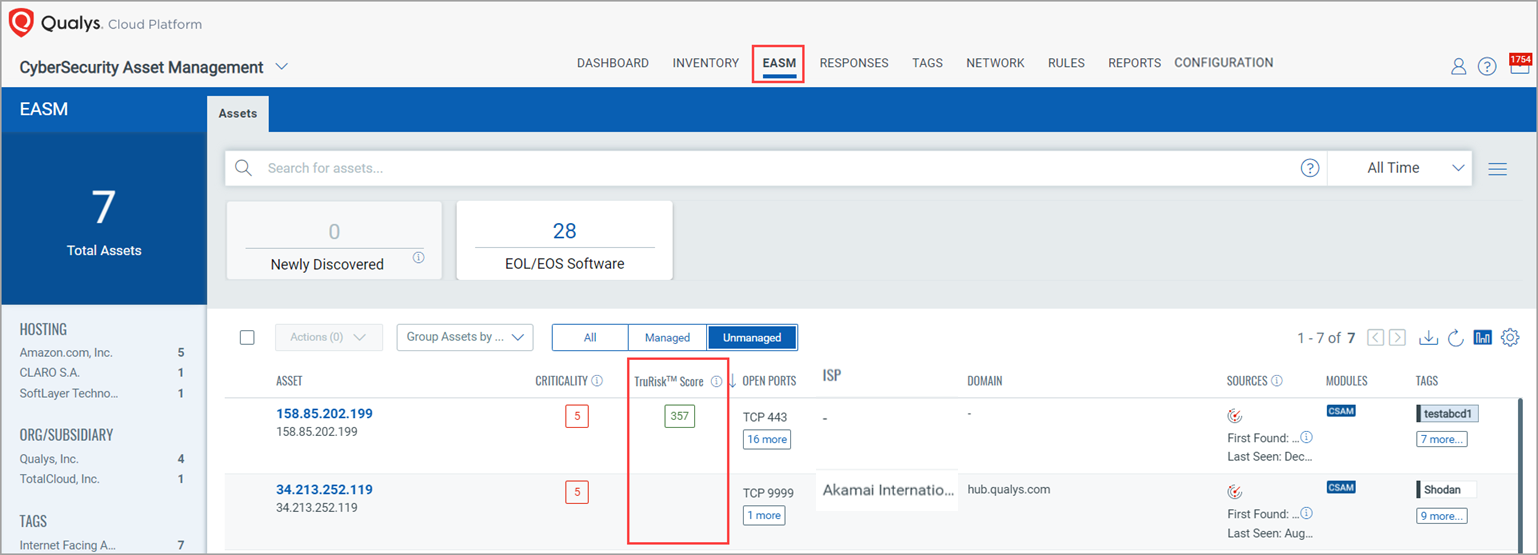
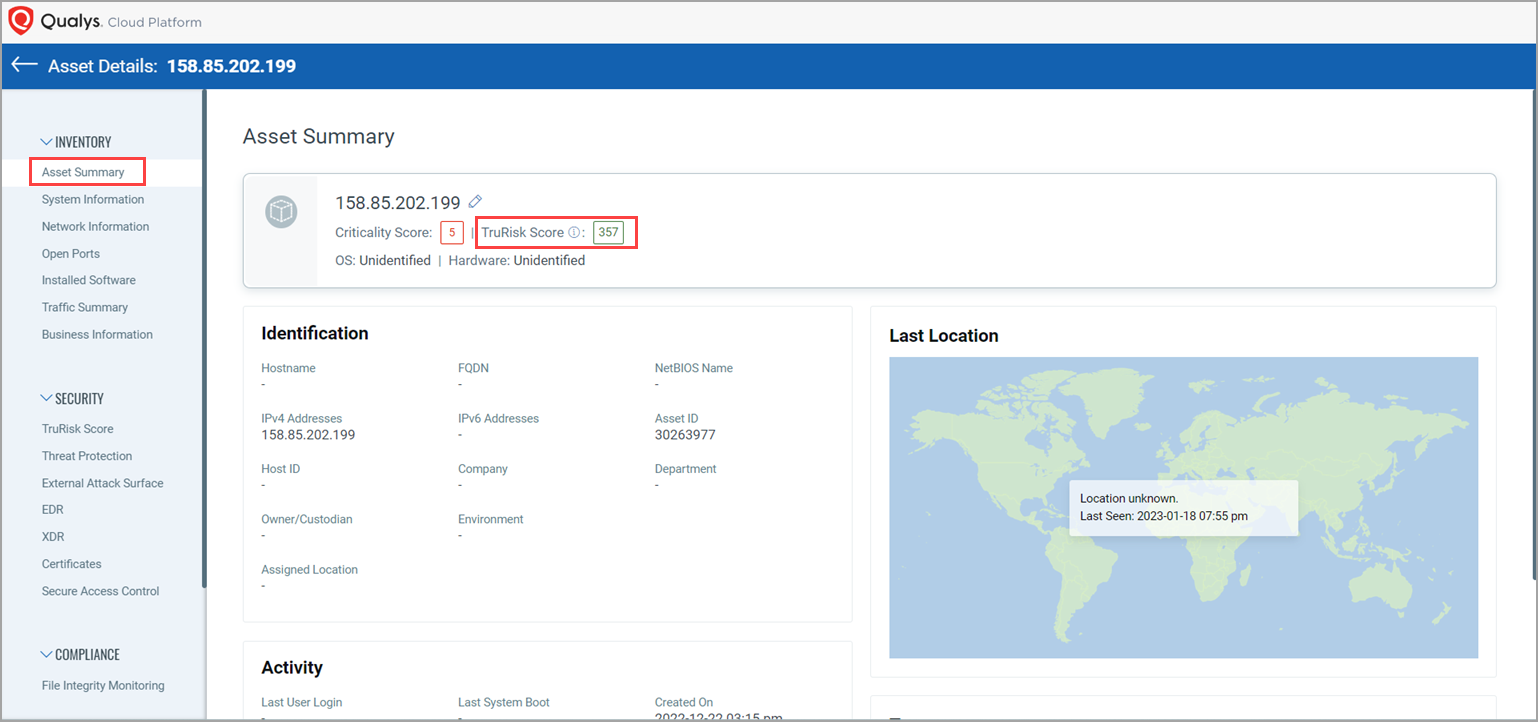
Note: When you see asset details of an individual asset that is exposed to vulnerabilities, on the ‘Asset Summary’ page, you can see the TruRisk Score for that asset.
In the case of externally exposed unmanaged assets, when you click the TruRisk Score count, you are navigated to the TruRisk Score page. You can see the TruRisk Score and its contributing factors, and a detailed summary of vulnerabilities detected.
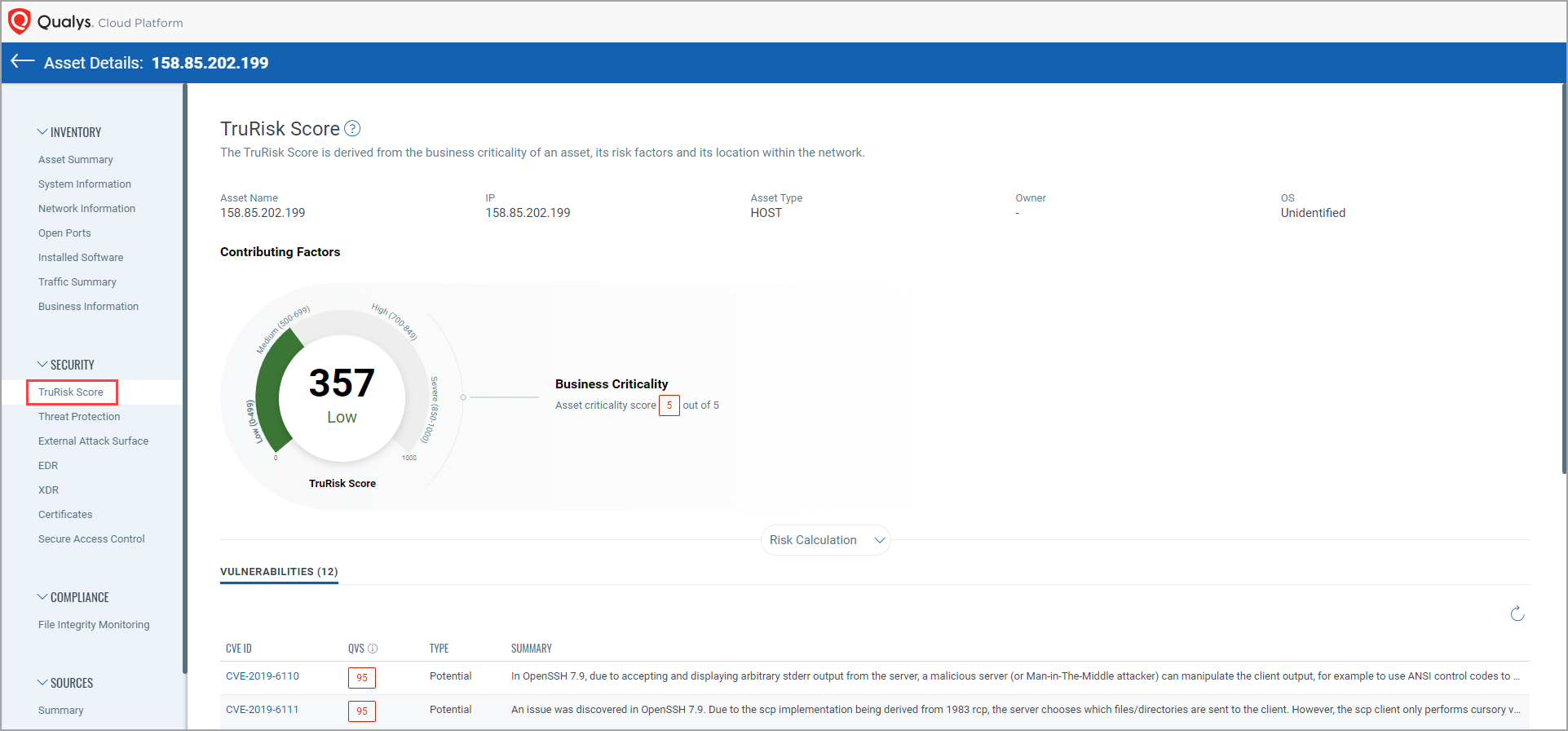
When you click the QVS count from the Vulnerabilities summary, you can see the Qualys Vulnerability Score (QVS) Details for that QVS.
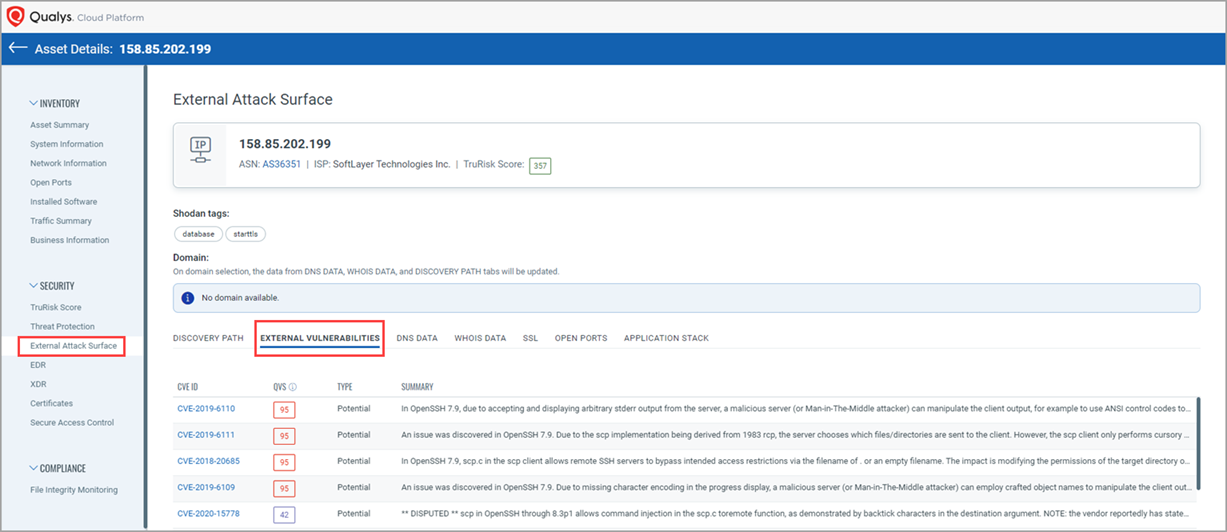
Alternatively, you can click the External Attack Surface tab to see a summary of vulnerabilities detected for an asset.
(4) Open Ports: You can see the protocol type and count of open ports for the externally exposed assets.
Important to Know!
In the Sources column, you can see two distinct icons for assets scanned through the EASM scan and VM scans.
- For an asset that is scanned only through an EASM scan:
When you go to its "Asset Details" page and navigate to the Security Section > External Attack Surface > OPEN PORTS tab, the open ports discovered by the EASM scan are shown. If you go to Inventory > Open Ports tab, you can see the same open ports listed there and on the asset listing page in the Open Ports column.
- For an asset that is scanned through both an EASM and VM scan:
When you go to its "Asset Details" page and navigate to the Security Section > External Attack Surface > OPEN PORTS tab, the open ports discovered by the EASM scan are shown. If you go to the Inventory > Open Ports tab, those open ports are not listed there, but you can see a different set of open ports discovered through the VM scan there and on the asset listing page in the Open Ports column.
(5) ISP: You can see the Internet Services Provider for an IP that is present on Shodan.
(6) Domain: You can see domain and subdomain details of the externally exposed assets.
(7) EASM-specific quick filters: In the left pane, you can see the EASM-specific quick filters, such as HOSTING, ORG/SUBSIDIARY, and TAGS.
Note: The inventory of externally exposed assets gets refreshed after every 48 hours.