Viewing Inventory of External Attack Surface Discovered Assets from the CSAM Toggle
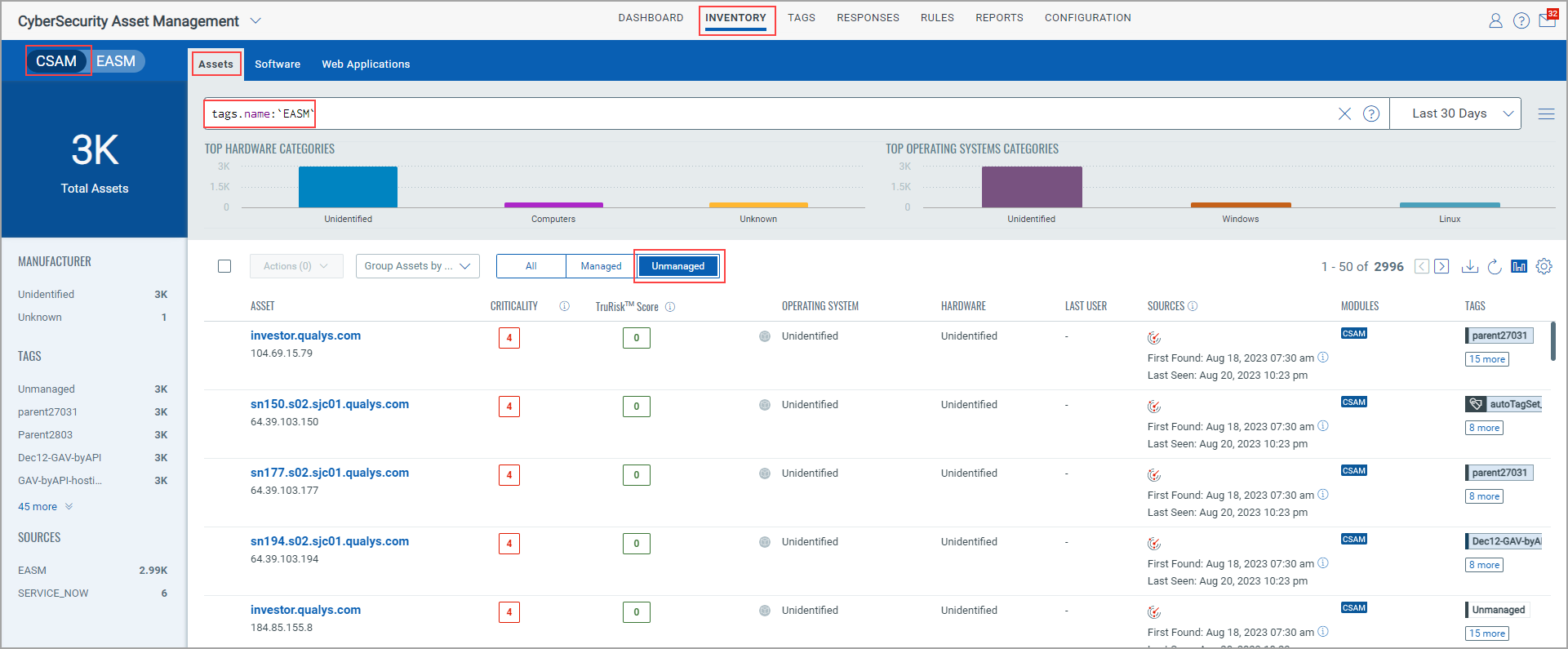
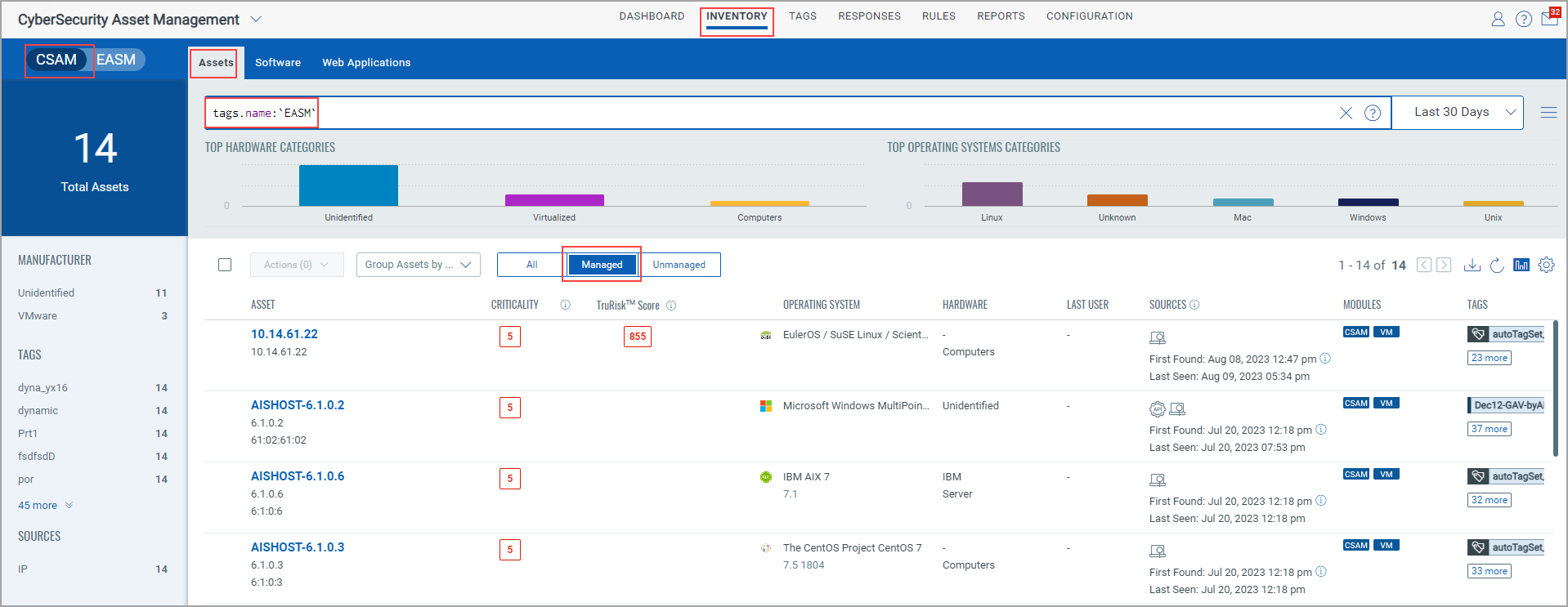
Go to the Inventory > Assets tab, and turn the CSAM EASM toggle to show the CSAM assets. Enter tags.name:`EASM`in the search bar.
- When you select All: You can see assets that are tagged with an EASM tag.
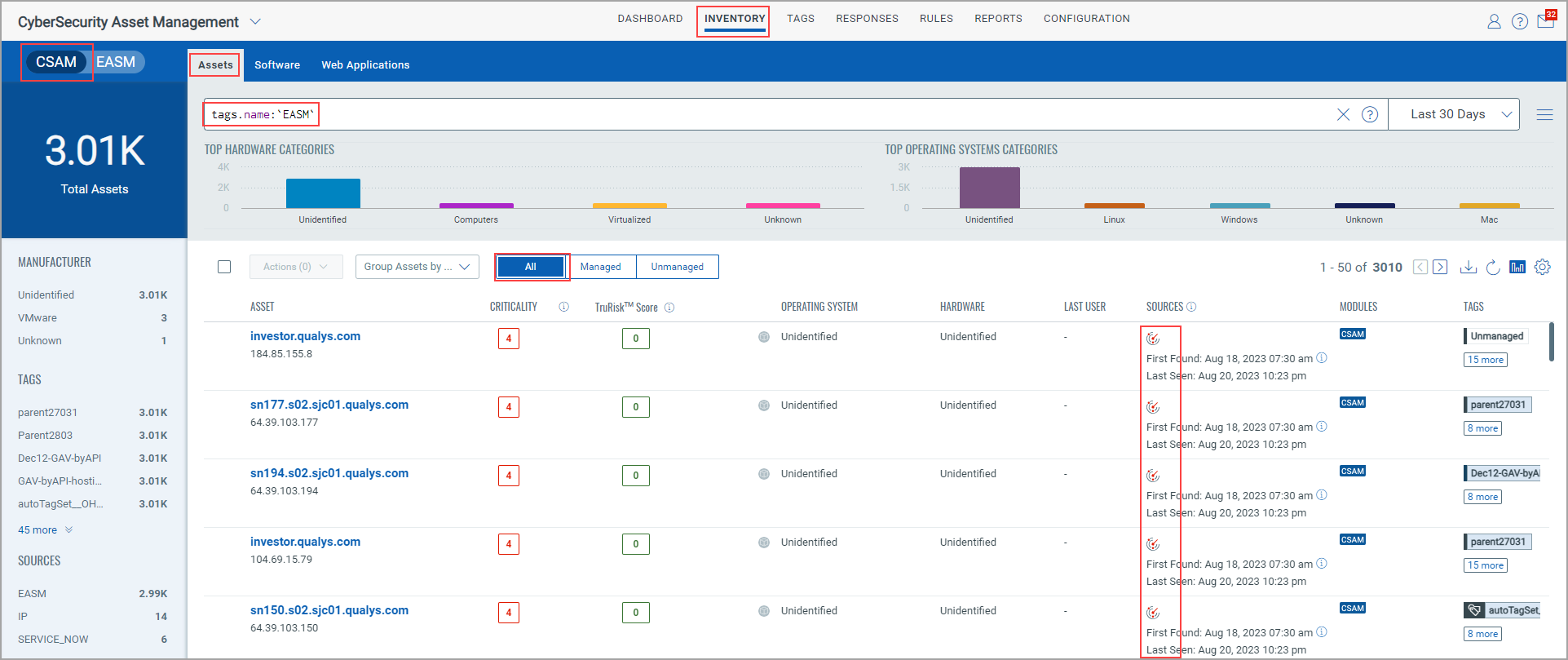
- When you select Unamanged: You can see the unmanaged assets that are discovered by EASM. In the Sources column, you can see EASM as the inventory source.
- When you select Managed: You can see the managed assets that are already discovered by other Qualys inventory sources, such as IP Scanner.
Note: The 'Shodan' tag is retained but the 'EASM' tag is added for all these discovered assets.
Important to Know!
In the Sources column, you can see two distinct icons for assets scanned through the EASM scan and VM scans.
- For an asset that is scanned only through an EASM scan:
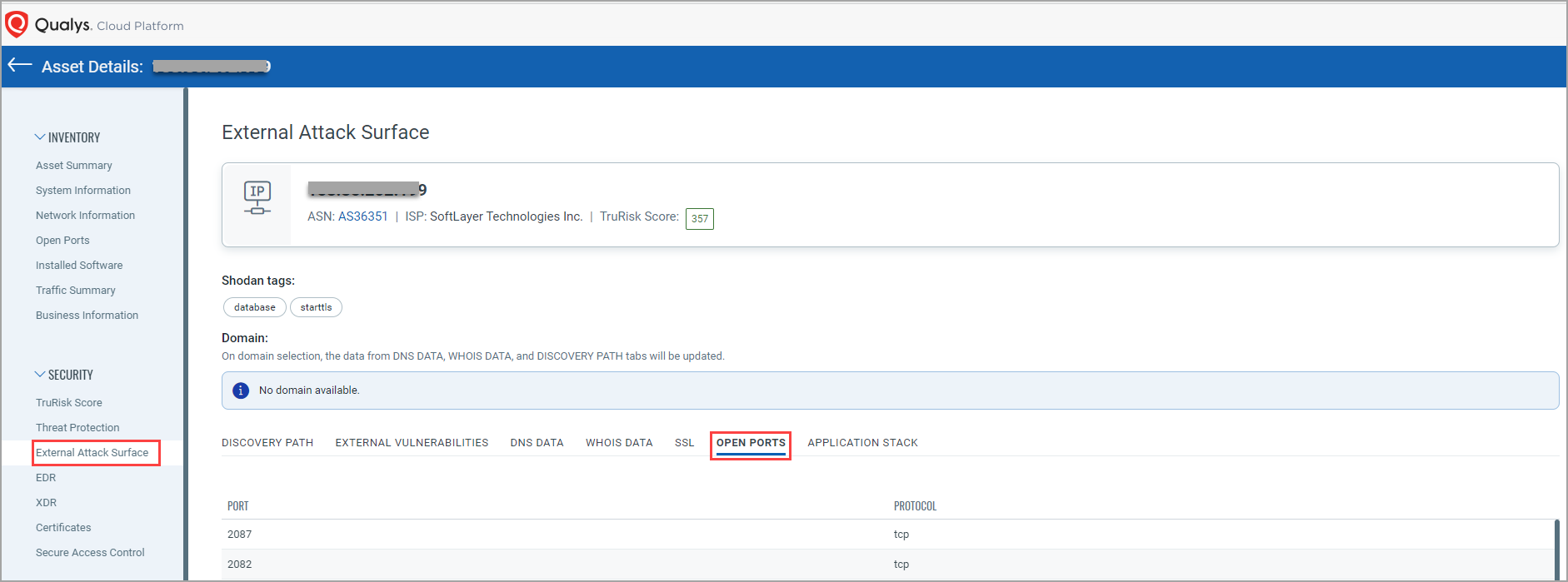
When you go to its "Asset Details" page and navigate to the Security Section > External Attack Surface > OPEN PORTS tab, the open ports discovered by the EASM scan are shown. If you go to Inventory > Open Ports tab, you can see the same open ports listed there and on the asset listing page in the Open Ports column.
- For an asset that is scanned through both an EASM and VM scan:
When you go to its "Asset Details" page and navigate to the Security Section > External Attack Surface > OPEN PORTS tab, the open ports discovered by the EASM scan are shown. If you go to the Inventory > Open Ports tab, those open ports are not listed there, but you can see a different set of open ports discovered through the VM scan there and on the asset listing page in the Open Ports column.
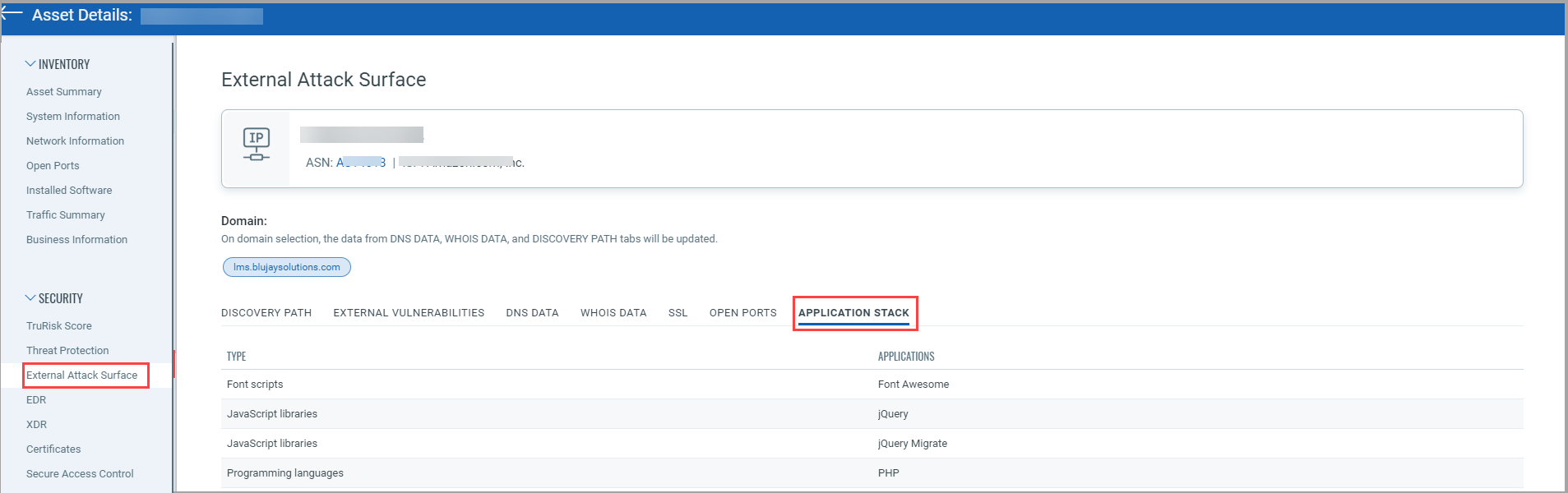
External Attack Surface Details of an Asset
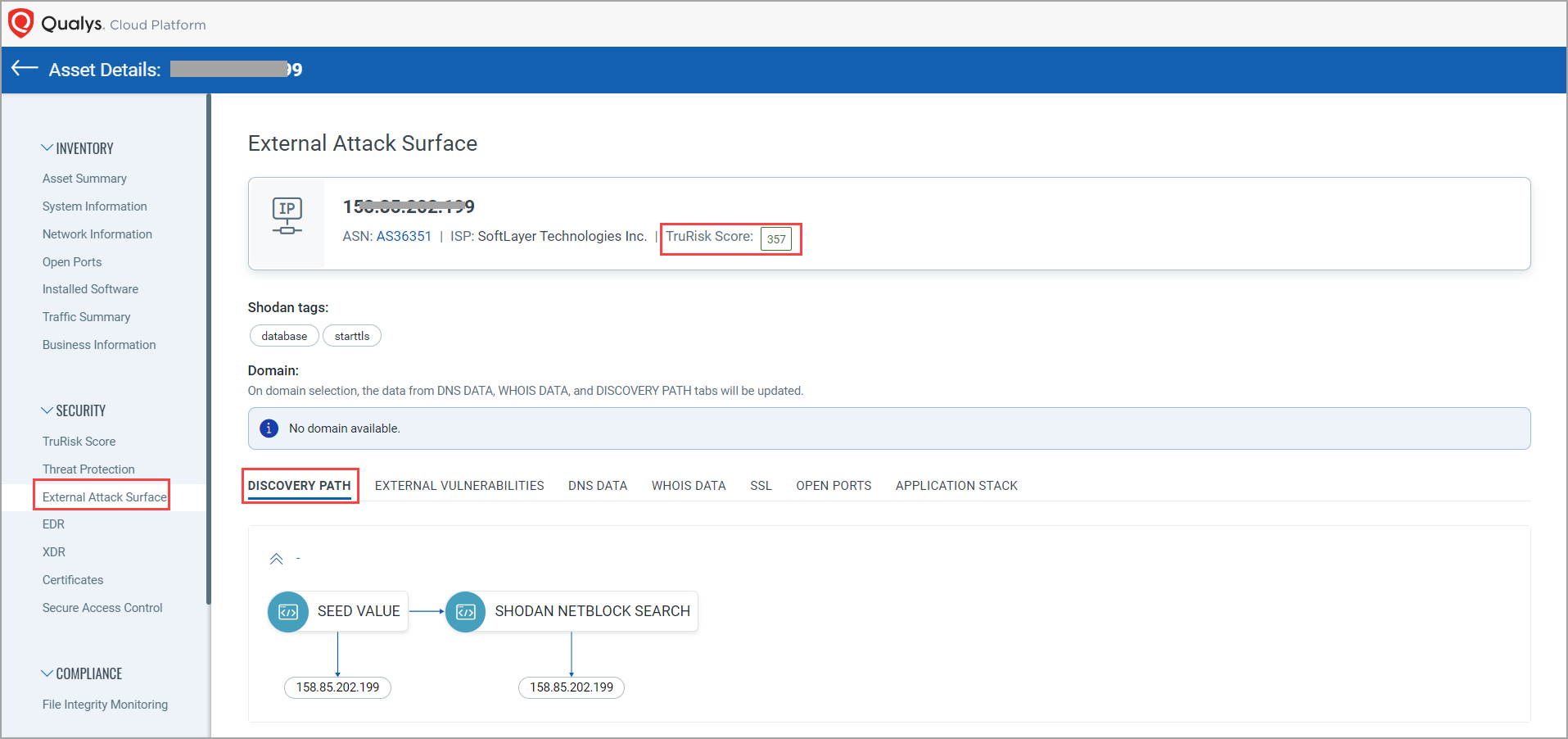
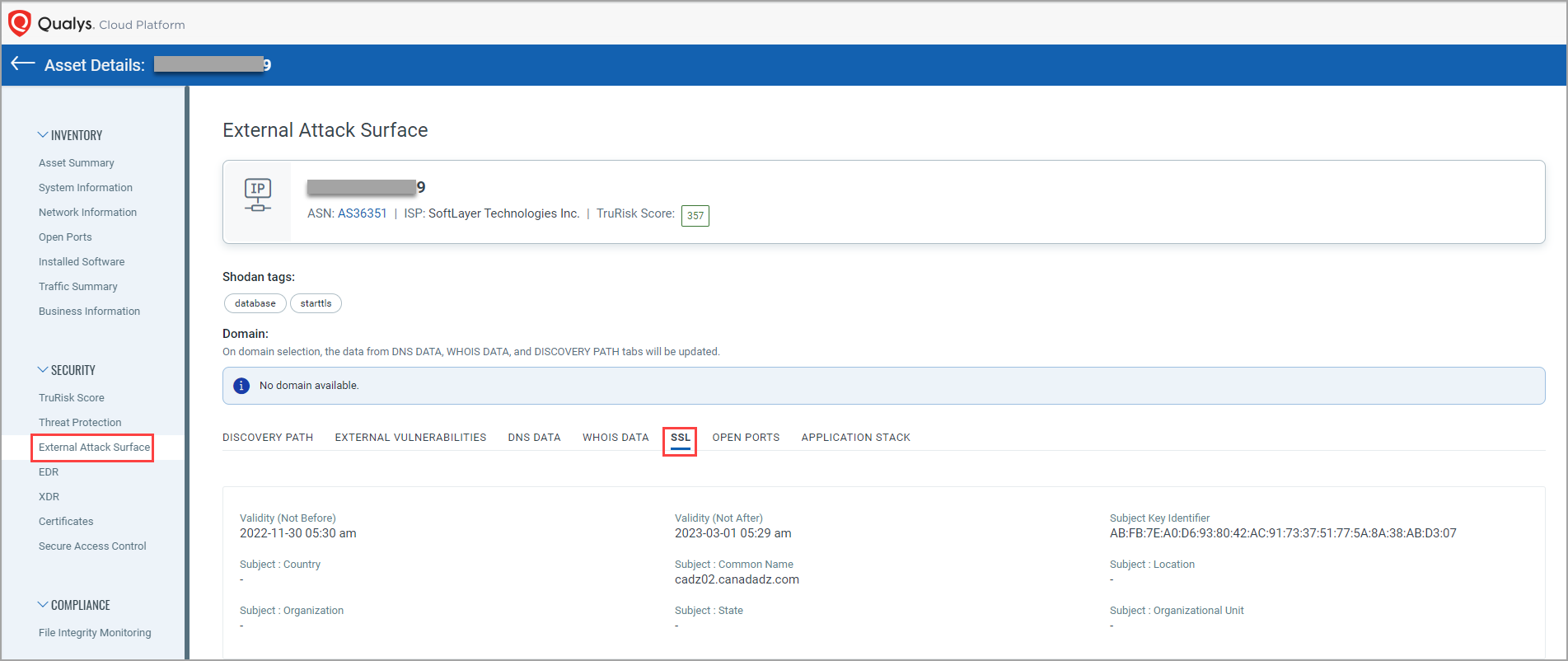
After you click an asset, you are redirected to the 'Asset Details' page. From the left pane, click External Attack Surface to view the EASM details.
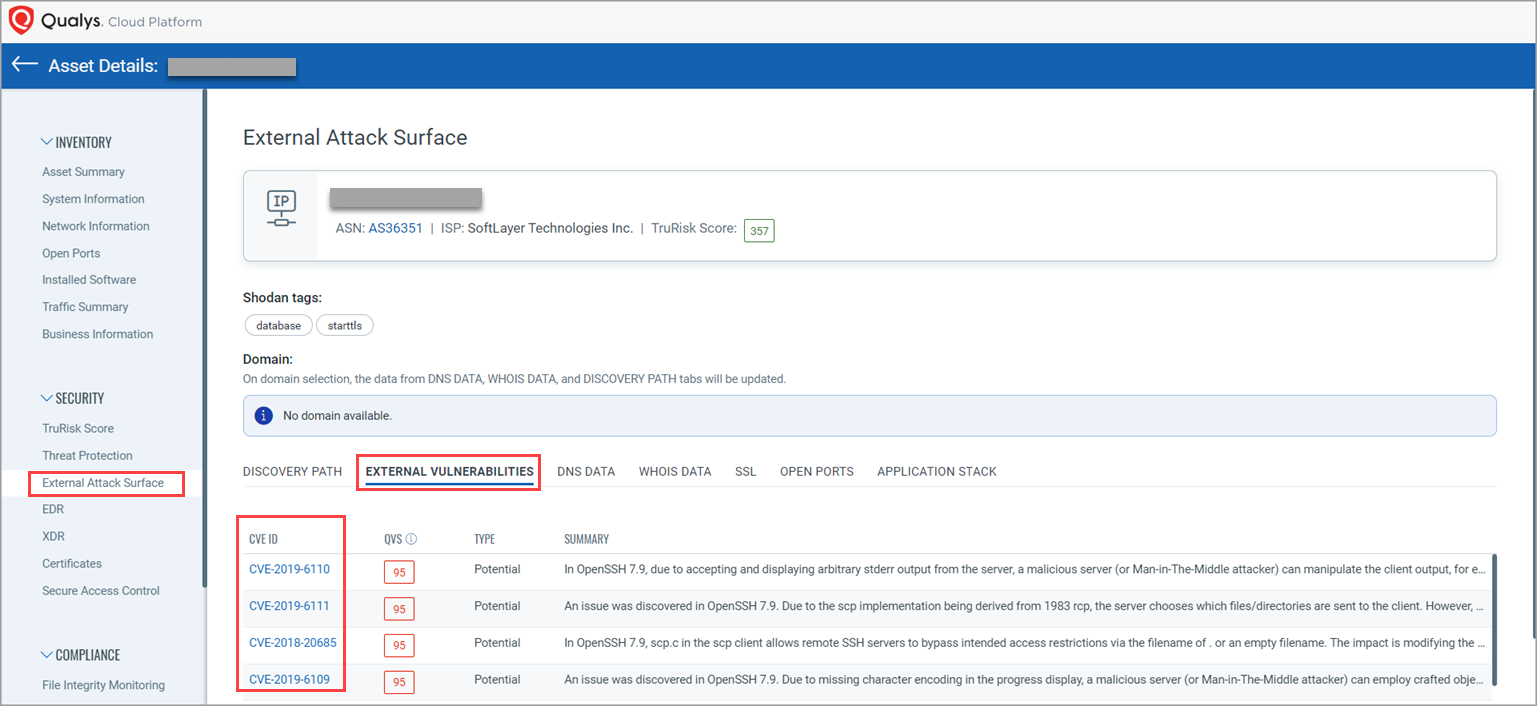
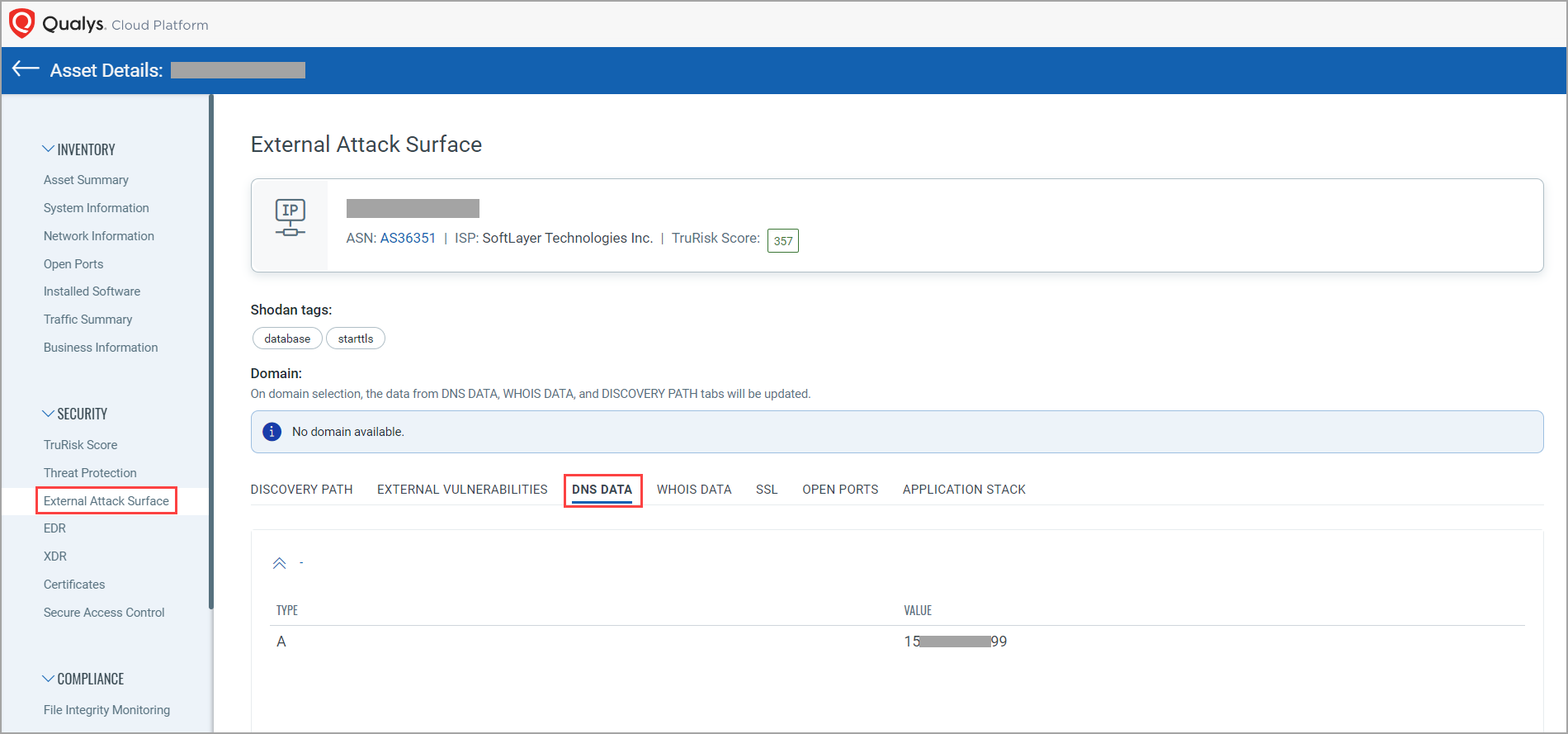
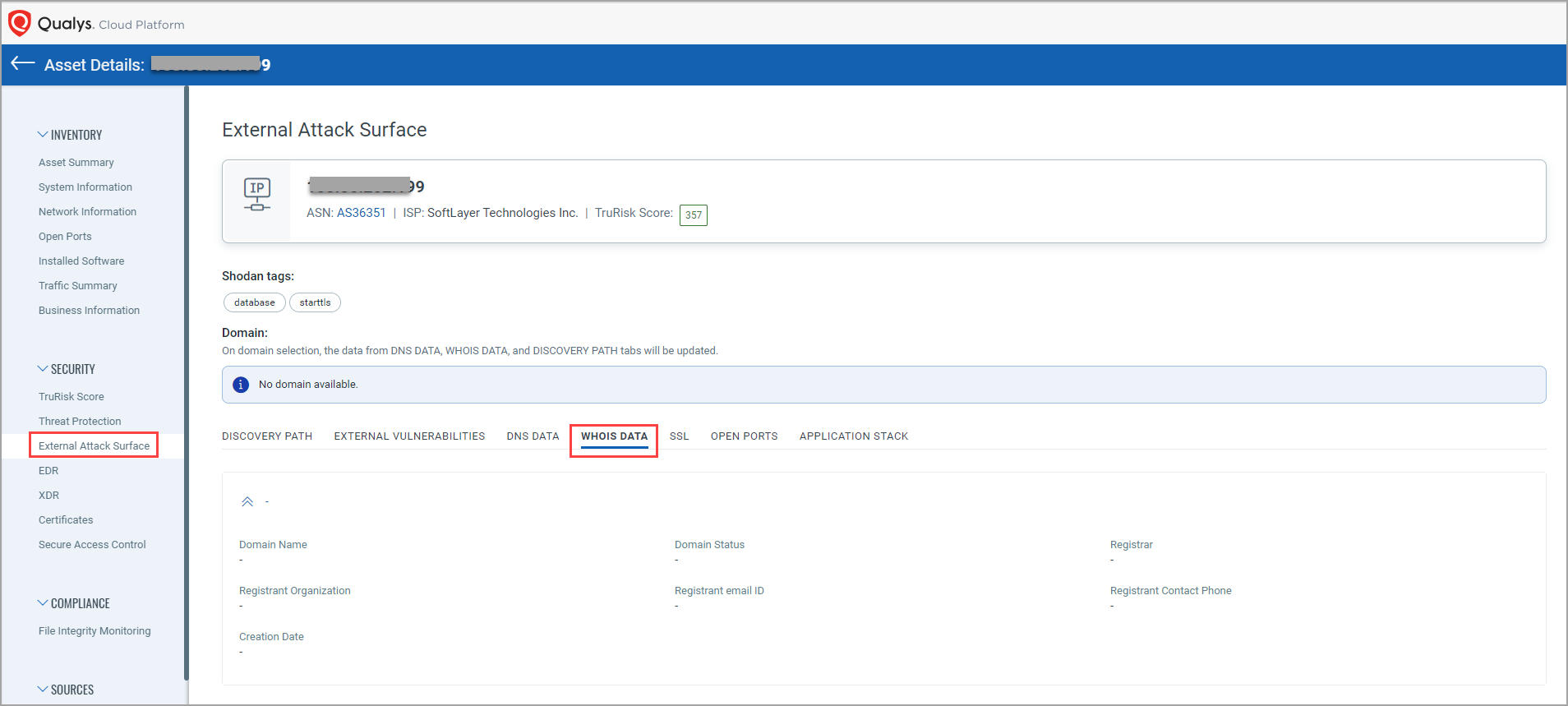
You can click the following tabs to find the External Attack Surface Details of that asset.
- DISCOVERY PATH: The asset IP shown can include multiple domains or subdomain. You can understand how the asset is attributed to your organization. The TruRisk Score for the asset is also shown.
- EXTERNAL VULNERABILITIES: You can see the vulnerability data for that particular IP. The vulnerability data includes vulnerability name, vulnerability score that is shown in descending order, vulnerability type, such as Unverified and Verified, and vulnerability summary. The vulnerabilities shown in the CVE ID column are clickable. Upon clicking a particular vulnerability, you are pointed to the National Vulnerability Database, wherein detailed information about that vulnerability is mentioned.
- DNS DATA: You an see the DNS data for a particular IP.
- WHOIS DATA: You can see details about who created the asset, such as Creation date, Domain Name, Registrant email ID, Registrar, and so on.
- SSL: You can see the certificate details, such as whether it's valid, expired, or expiring.
- OPEN PORTS: You can find the details about unsanctioned services, if any, such as SSH or RDP are running on the asset.
- APPLICATION STACK: You can see the details about if the asset is using any unapproved legacy application stack or the application stack you moved away from.