Appendix: Exploitability and Exposure Metrics
We introduced a new card on the CVE Details page to provide deeper insights into vulnerability exploitability and remediation efficiency. This enhancement helps security teams better understand attacker behavior and assess the effectiveness of their responses. This appendix explains the vulnerability exposure concepts AWE, WOW, and REG, along with how they relate to attacker behavior and defender response. It is designed for product, engineering, security, and data teams who work with vulnerability life cycle metrics.
Key benefits are:
- Understand attacker timelines with real-world exploit data
- Measure remediation performance across assets
- Identify exposure gaps and prioritize patching efforts
- Improve risk posture with actionable metrics
Modern security programs must quantify not only how quickly defenders respond but also how fast attackers move.
The three new metrics are:
- Window of Weaponization: How fast the attacker moved
- Average Window of Exposure: How long the defender remained exposed:
- Remediation Efficiency Gap: How many days were both true: attacker armed + defender unpatched
These metrics map onto the life cycle of each CVE across an organization’s assets.
Glossary Summary
This table gives a quick view of which terms used in exposure metrics.
|
Term |
Description |
|---|---|
|
AWE |
AWE is the average time taken to remediate (patch) affected assets in your environment. |
|
WOW |
Days from CVE published. First working exploit observed. Represents attacker speed (global). |
|
REG |
AWE − WOW. Days during which the attacker had an exploit, and the defender was still unpatched. |
|
Open AWE |
Asset is unpatched; exposure window is still accumulating. |
|
Zero‑day |
Exploit observed before CVE publication; WOW is negative. |
|
CISA KEV |
Cybersecurity and Infrastructure Security Agency Known Exploited vulnerabilities. |
| CVE |
Common Vulnerabilities and Exposures. Assigns unique IDs to specific vulnerabilities. |
|
CPE |
Common Platform Enumeration. It is a standardized, machine-readable format used in cybersecurity to uniquely identify and name hardware, operating systems, and software applications. Managed by NIST, it allows security tools to automatically scan, inventory, and map assets to known vulnerabilities (CVEs). |
| CVSS | Common Vulnerability Scoring System. Scores vulnerability severity from 0.0 to 10.0. |
| NVD | National Vulnerability Database. Enriches CVEs with scores, classifications, and references. |
| CWE | Common Weakness Enumeration. CWE catalogs the types of software weaknesses that cause those vulnerabilities |
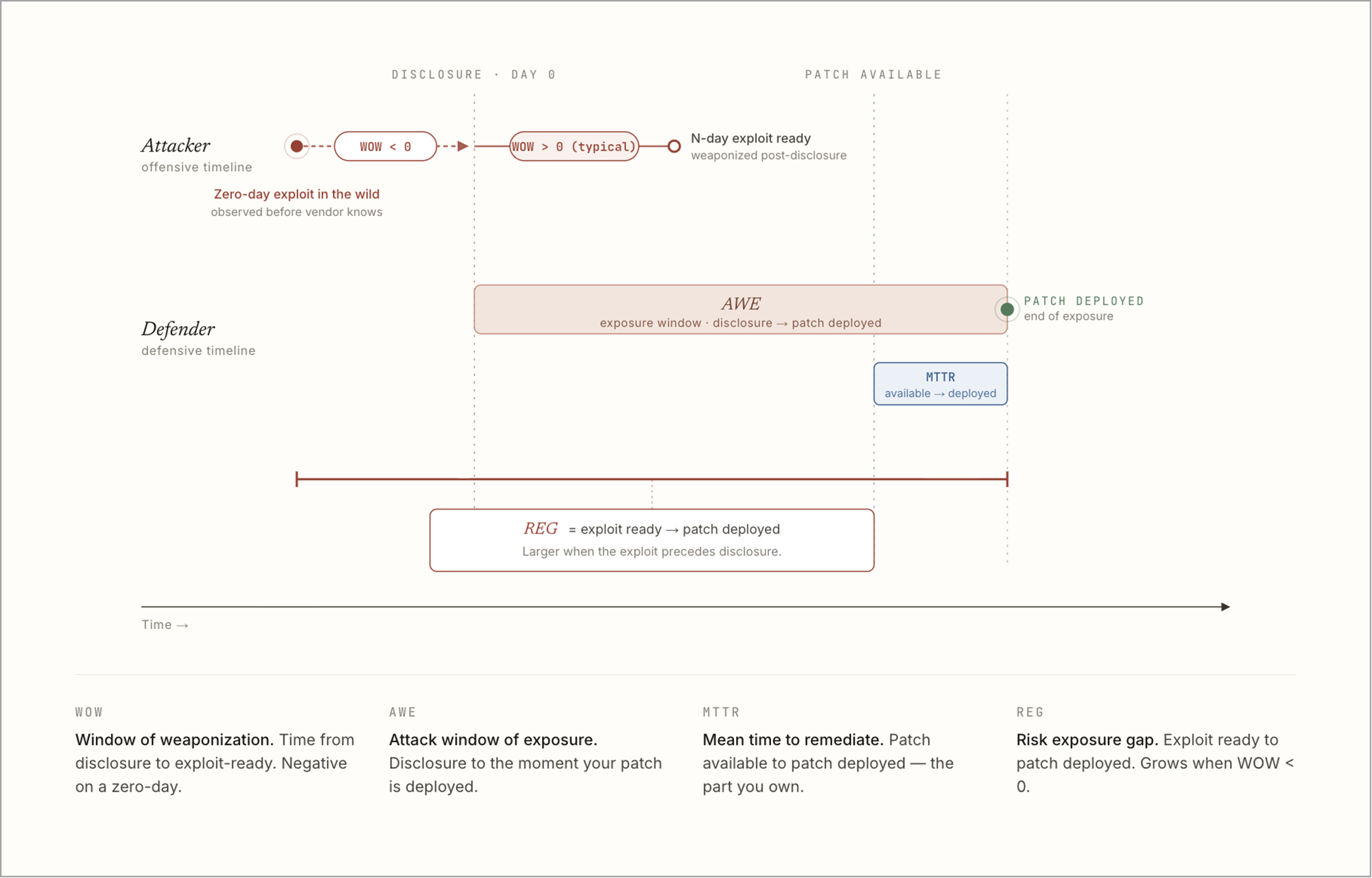
The following diagram represents various vulnerability and remediation terminologies for a given CVE.
Metric Definitions
Window of Weaponization (WOW)
The time taken by attackers to develop an exploit after a CVE is publicly disclosed.
Calculated as the number of days between CVE publication and the first known exploit availability.
Formula: WOW = First Exploit Observed Date − CVE Published Date
The WOW can be:
- Positive: Exploit created after disclosure
- Negative: Exploit existed before public disclosure (indicating early attacker awareness)
Example:
If a CVE was published on May 12 and an exploit appeared on May 14, WOW, it's 2 days.
If exploitation occurred before publication, WOW may be negative.
Average Window of Exposure (AWE)
The average time taken to remediate (patch) affected assets in your environment. AWE represents defender speed and operational discipline.
The AWE is calculated across all impacted assets for a given CVE. It reflects how long systems remained vulnerable before being patched. If remediation is still in progress, the value is marked as open and growing.
Formula: AWE = Patch Applied Date − CVE Published Date
Example:
If multiple assets are patched over different durations, AWE represents the average remediation time.
Remediation Efficiency Gap (REG)
A comparative metric showing how your remediation speed aligns with attacker activity.
Formula: REG = AWE − WOW
- Positive REG indicates attackers are faster, indicating higher exposure risk
- Negative REG indicates you are mitigating vulnerabilities faster than attackers can weaponize them
- Zero REG indicates you are mitigating vulnerabilities at the same time as attackers weaponize them
Use cases
Use Case 1: Prioritising Patch Deployment Based on REG
Scenario:A security team observed:
AWE = 25 days per asset
WOW = 5 days
REG = 20 days (High Risk)
Outcome:The team prioritizes the affected assets because attackers have had a functional exploit for 20 days while the organisation remained unpatched.
This directly drives patch acceleration and SLA breach alerts.
Use Case 2: Zero-Day Exploit Response Planning
Scenario:Threat intelligence detects that an exploit was active before CVE publication:
WOW = –4 days (zero day)
AWE is open (patch not yet applied)
Outcome:The CISO receives an immediate zero-day alert. Since WOW < 0, every single day of exposure counts as armed exposure, increasing urgency for compensating controls, isolation, or emergency patch rollout.
Use Case 3: Benchmarking Defender Speed Against Industry Peers
Scenario:For a high-impact CVE:
Organisation AWE = 40 days
Peer cohort AWE median = 10 days
WOW = 3 days
REG (org) = 37 days
Outcome:Risk teams interpret this as a structural operational lag compared to peers.
The organisation uses this to: justify investment in patch automation, Add staff to vulnerability management, engage product teams for configuration hardening.
This supports governance reporting to leadership and audit committees.