Qualys Vulnerability Scoring System (QVSS)
Qualys Vulnerability Scoring System (QVSS) is the scoring framework used in Variable "short_product_name" is not defined to measure the severity of all security exposures, both vulnerabilities and misconfigurations, on a 0.0–10.0 scale. It is powered by Qualys Threat Intelligence (TruLens) and TruRisk™ context.
Currently, the QVSS score is displayed on the Vulnerabilities page, while QDS details will continue to be shown on the Misconfiguration Details page.
Why QVSS?
QVSS addresses two common issues customers encountered:
- Different scoring scales (CVSS 0–10 vs QDS 1–100) made comparison and communication difficult.
- Customers wanted the intuitive CVSS-style scale but without losing Qualys’ threat intelligence advantages.
QVSS = QDS ÷ 10 (normalized) + CVSS-like severity mapping. QDS continues to be supported for existing automation.
- Preserves intelligence: Includes threat signals such as CISA KEV, exploit availability, and Qualys RTIs.
- Improves readability: Uses 0–10 scale so teams can quickly interpret severity (e.g., 9.5 feels like a critical issue).
- Consistent across findings: Applies to both CVEs and misconfigurations so prioritization is unified.
Scope of QVSS
QVSS is applied to every finding Variable "short_product_name" is not defined manages, Vulnerabilities (CVEs) from Qualys VMDR and third-party scanners.
Conceptual Model QVSS
QVSS has two layers: Base (global, KB-level) and Environmental (customer-specific). The final score combines both.
QVSS Base Score
Represents the inherent risk of a CVE or misconfiguration in the global ecosystem. Calculated per signature and stored in the knowledge base.
- Technical inputs: CVSS base vector, attack complexity, privileges required
- Threat signals: KEV, public exploit, active attacks, EPSS, actor targeting
- Temporal signals: trending, new exploit emergence, age
QVSS Environmental Score
Adjusts Base based on customer context: asset attributes, control posture, and business impact.
- Risk factors (increase score): internet-facing, crown-jewel, industry-targeted
- Compensatory controls (decrease score): EDR, segmentation, WAF, mitigations
QVSS Score = QVSS Base ± Environmental Adjustments
QVSS Base - It is a global inherent risk of an exposure. It utilizes real-world threat signals, including known exploits, CISA KEV data, Malware and ransomware activity, Threat actor TTPs, trending activity, and EPSS.
Environmental Adjustments - It adjusts the score for your environment using risk factors, business context, and compensatory controls.
This is the value is displayed in Variable "short_product_name" is not defined and used for prioritization, SLAs, and reporting.
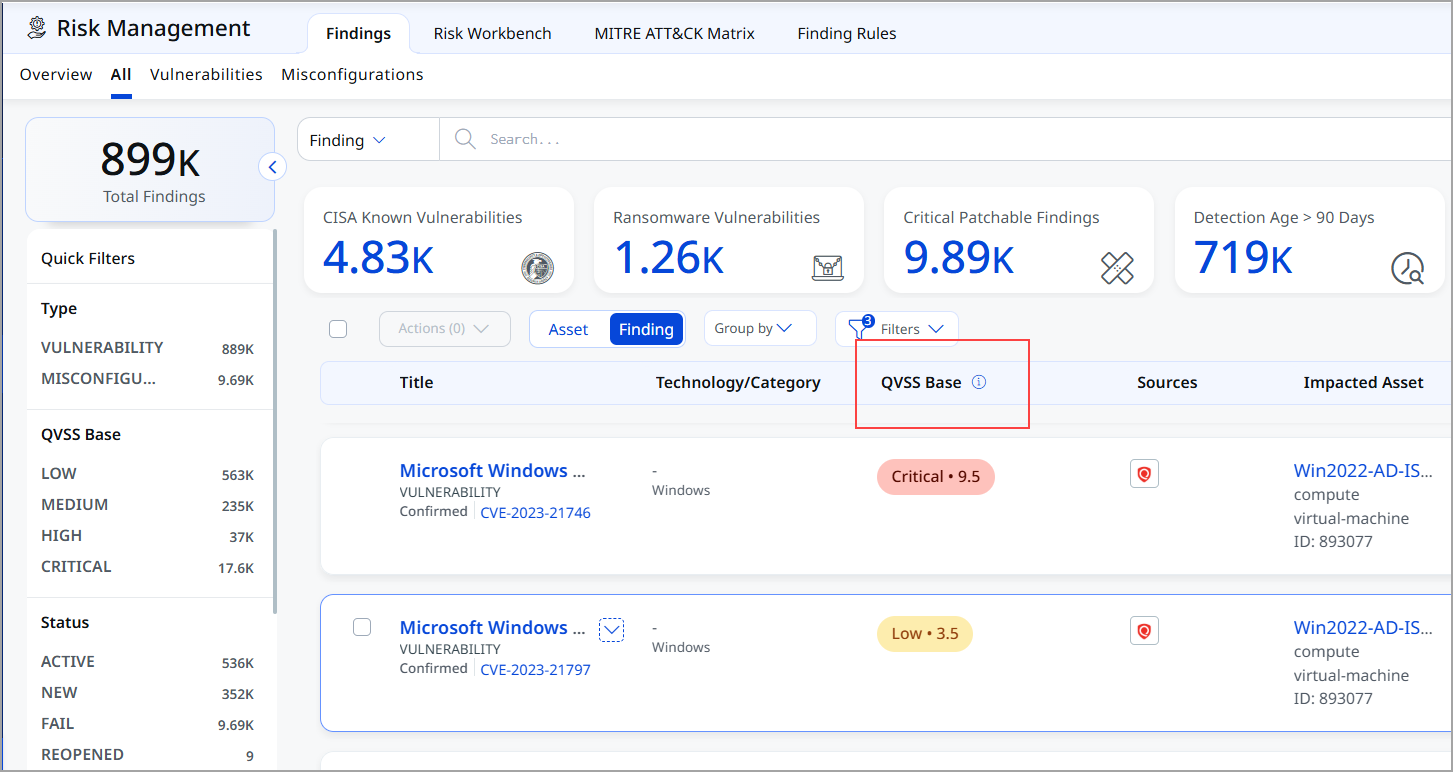
You can view the QVSS score column on the the Findings listing page.
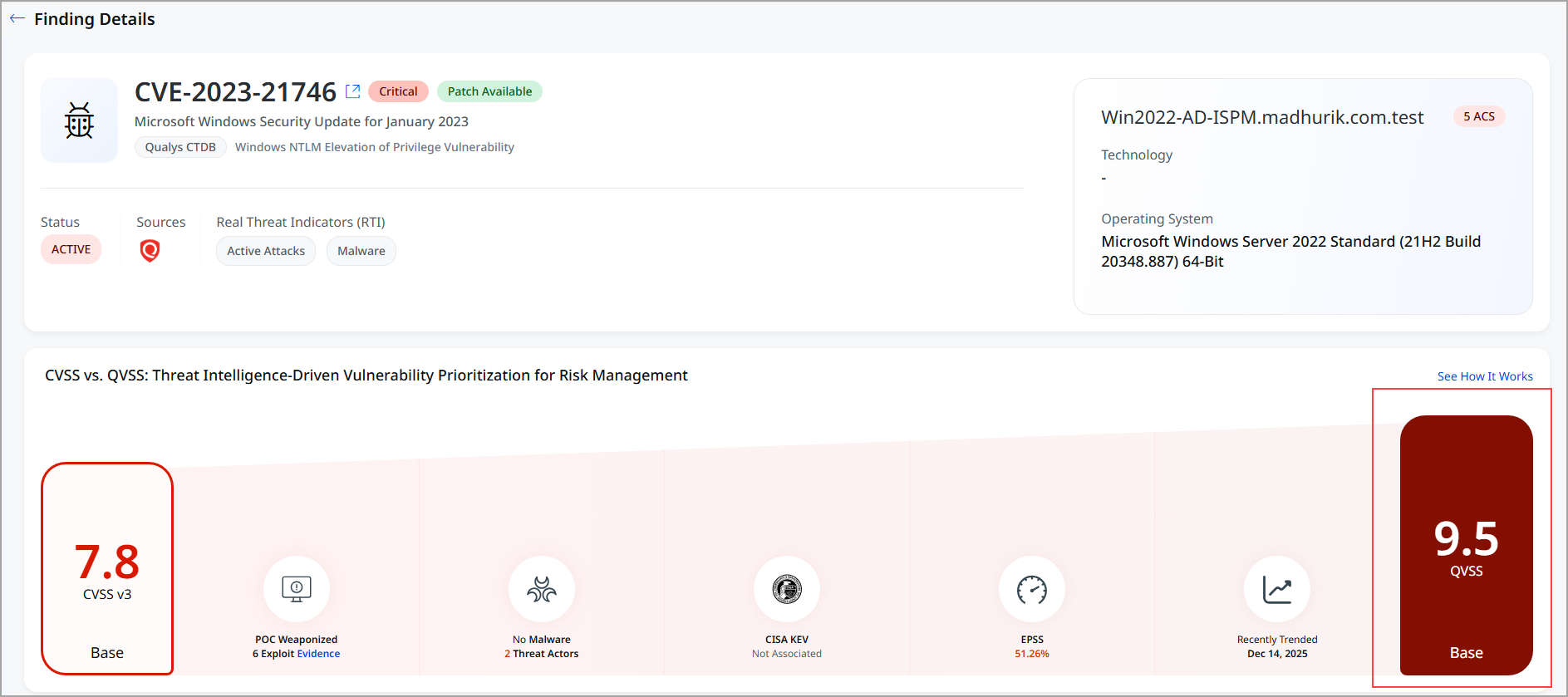
You can view QVSS score on details of the findings as shown in the following screenshot.
QVSS Scale and Severity Mapping
|
QVSS Range |
Severity |
|---|---|
|
0.0 – 3.9 |
Low |
|
4.0 – 6.9 |
Medium |
|
7.0 – 8.9 |
High |
|
9.0 – 10.0 |
Critical |
Relationship with QDS
QVSS is backward compatible: it preserves the QDS logic and expresses it on a 0–10 scale (QDS ÷ 10). Existing QDS-driven automations and APIs continue to work.
Score Display
- Findings listing and details
- Home page top contributors
- TruLens exposure tables
- Business Entity views and Risk Workbench
- Dashboards, widgets and reports
Tips for Users
- Use QVSS for visual reporting and communication; use QDS for automation that already depends on it.
- Watch environmental factors — they can significantly change prioritization.
- Leverage Variable "short_product_name" is not defined compensatory controls to reflect real-world mitigations.
Usecases
Following are the couple of examples which reflect hw QVSS can be more useful.
Use case – CVSS Moderate, QVSS Critical
Consider the example of CVE-2024-50302. This example shows how QVSS can upgrade the severity of a vulnerability when there is real-world attacker activity, even if the traditional CVSS score is displayed as moderate.
The table represents the risk attributes and scoring details for the specific vulnerability CVE-2024-50302.
|
Attribute |
Value |
|---|---|
|
CVSS Score |
5.5 (Medium) |
|
EPSS |
0.02777 |
|
CISA KEV |
No |
|
Exploit Availability |
Weaponized exploit available |
|
Threat Actors |
1 active threat actor |
|
Trending |
Actively trending from Nov 9 to Dec 6 |
|
Malware Association |
Present |
|
QVSS Base |
High |
|
QVSS Score (Effective) |
9.5 – Critical |
Observation and interpretation from the above table:
- CVSS Score: 5.5 represents Medium severity
CVSS only looks at the technical characteristics of the vulnerability, not what attackers are doing.
- What QVSS Sees (Real Threat Signals)
QVSS factors in actual malicious activity happening in the wild. For this vulnerability, QVSS detects:
| Real-World Signal | What It Means |
|---|---|
| Weaponized exploit available | Attackers already have a working tool to exploit it. |
| Trending exploitation discussions | It is being actively talked about and used between Nov 9–Dec 6. |
| Active threat actor | At least one known threat actor is exploiting it. |
| Malware association | Malware campaigns are using this vulnerability. |
| EPSS > 0 | There is a measurable probability of exploitation. |
| CISA KEV = No | Not in KEV yet—but other evidence shows active risk. |
QVSS Evaluation: QVSS Base: High, QVSS Effective Score: 9.5 – Critical
QVSS elevates the score because attackers are already exploiting it, creating significantly higher real-world risk than CVSS indicates.
CVSS labels this vulnerability as Medium, but QVSS detects multiple signs of active exploitation:
- Attackers have a weaponized exploit
- It is actively trending in the threat community
- Real threat actors are using it
- It is linked to malware campaigns
Conclusion: QVSS raises the severity to Critical (9.5) because attackers are actively targeting this vulnerability right now.
Use case 2: CVSS 6.0, QVSS Critical
This example shows why CVE-2024-20359, even though it has a moderate CVSS score, is marked as Critical by QVSS.
The table represents the risk attributes and scoring details for the specific vulnerability CVE-2024-20359.
|
Attribute |
Value |
|---|---|
|
CVSS Score |
6.0 |
|
EPSS |
0.0008 |
|
CISA KEV |
Yes |
|
Exploit Availability |
Weaponized + POC |
|
Threat Actors |
2 active (incl. UAT-4356) |
|
Trending |
Multiple spikes; recent dark-web chatter |
|
Malware Association |
Ransomware linkage |
|
QVSS Score |
9.5 – Critical |
Observation and interpretation from the above table:
- CVSS Score: 6.0 represents Moderate severity
- CVSS only considers the technical details of the vulnerability, not real-world usage.
Frequently Asked Questions
Is QDS removed?
No. QDS continues to be supported for APIs and automations. QVSS is the recommended display score for dashboards and reporting.
Can I show both QDS and QVSS?
Yes, advanced views can show both. QVSS is the primary severity shown to users in Variable "short_product_name" is not defined.
How are compensating controls validated?
Controls are consumed via asset and control posture data; customers can declare specific mitigations as compensating controls in Variable "short_product_name" is not defined rules.
How precise is QVSS?
Decimals are preserved for granularity. The combined Base + Environmental result is the effective score used for prioritization and SLAs.