View Findings with MITRE Tactics and Techniques Using the Group By Field
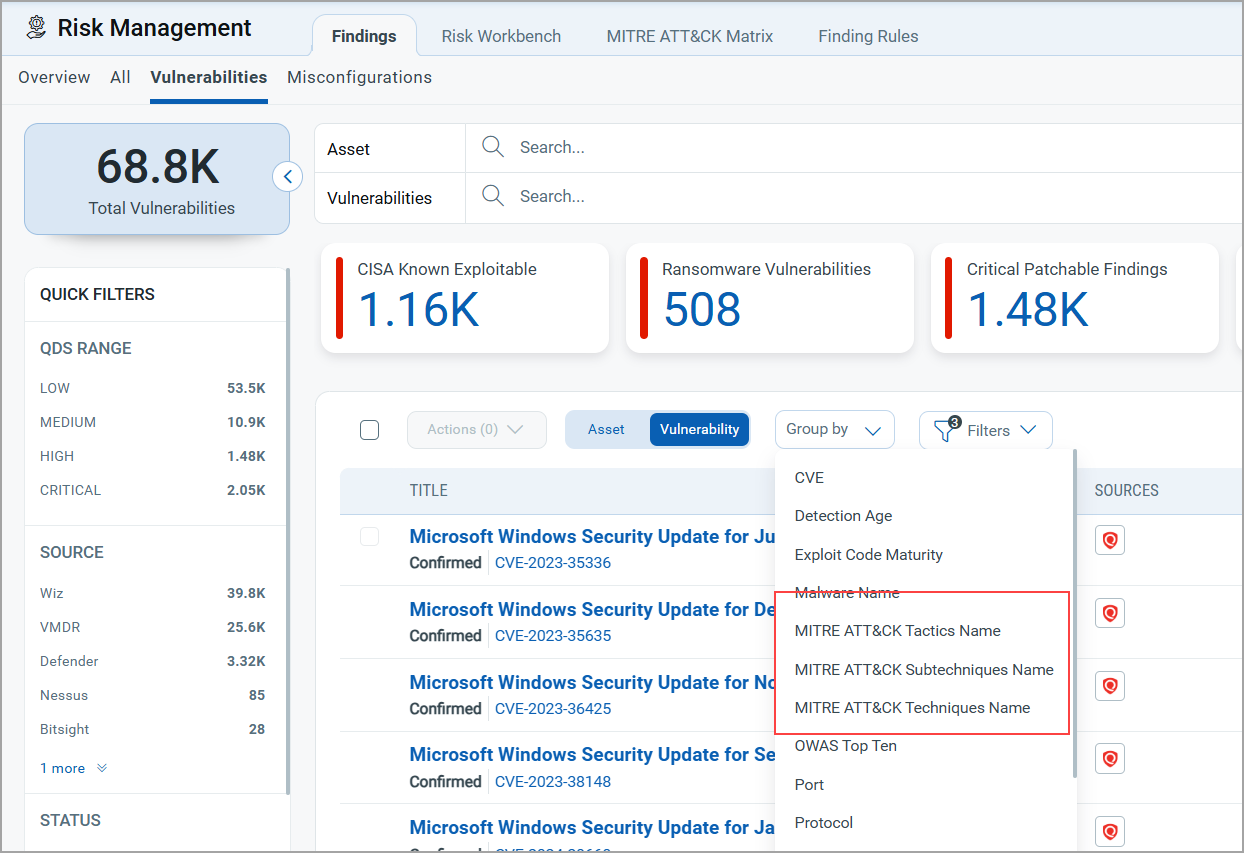
The Group By field in the Findings tab allows you to categorize findings based on your criteria. You can group the data by MITRE ATT&CK Tactic Name, MITRE ATT&CK Subtechnique Name, or MITRE ATT&CK Technique Name from the Group By drop-down menu. The following screenshot is an example of the Group by field that lists all three types of MITRE.
You can also use this Group By option in the All and Misconfiguration tabs. For demonstration purposes, we have provided screenshots from the Vulnerabilities tab.
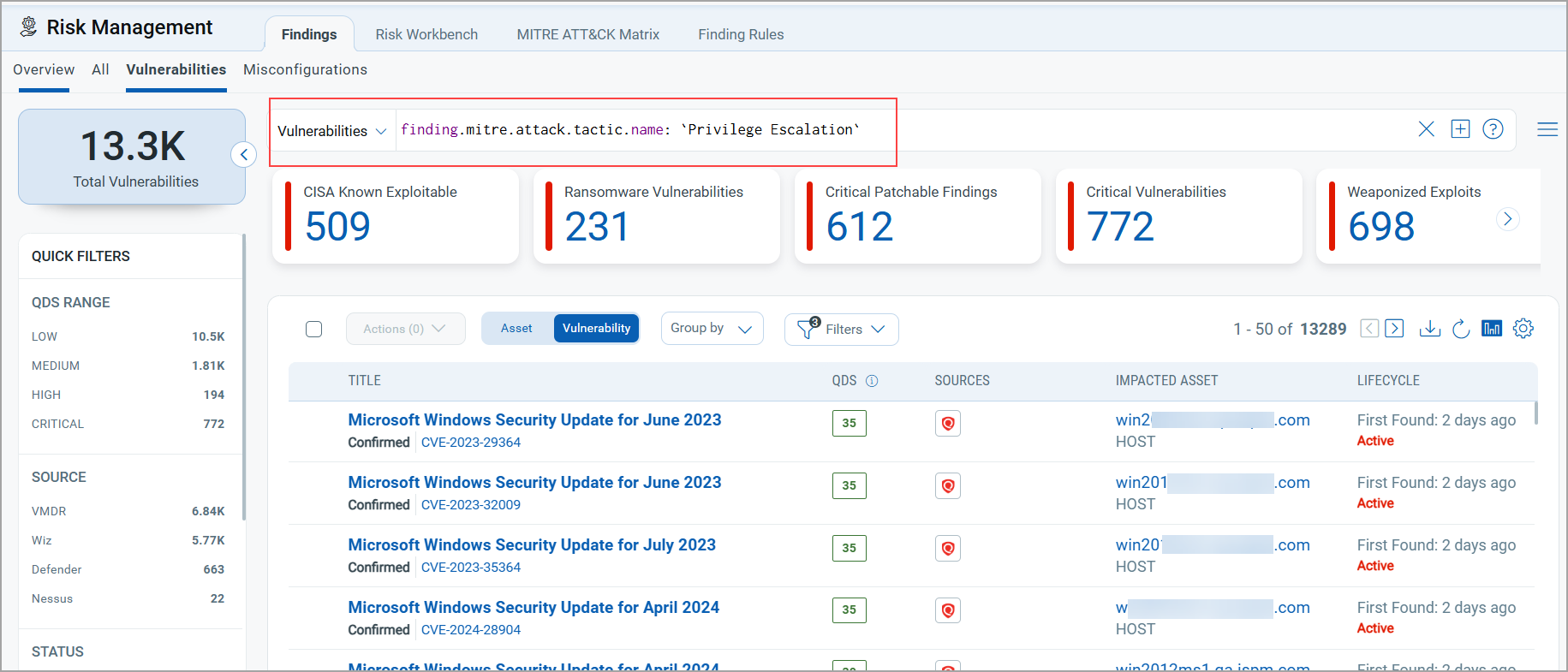
Group By MITRE ATT&CK Tactic Name
Select the Group By MITRE ATT&CK Tactic Name to retrieve a list of all Tactic Names and the total detection count.
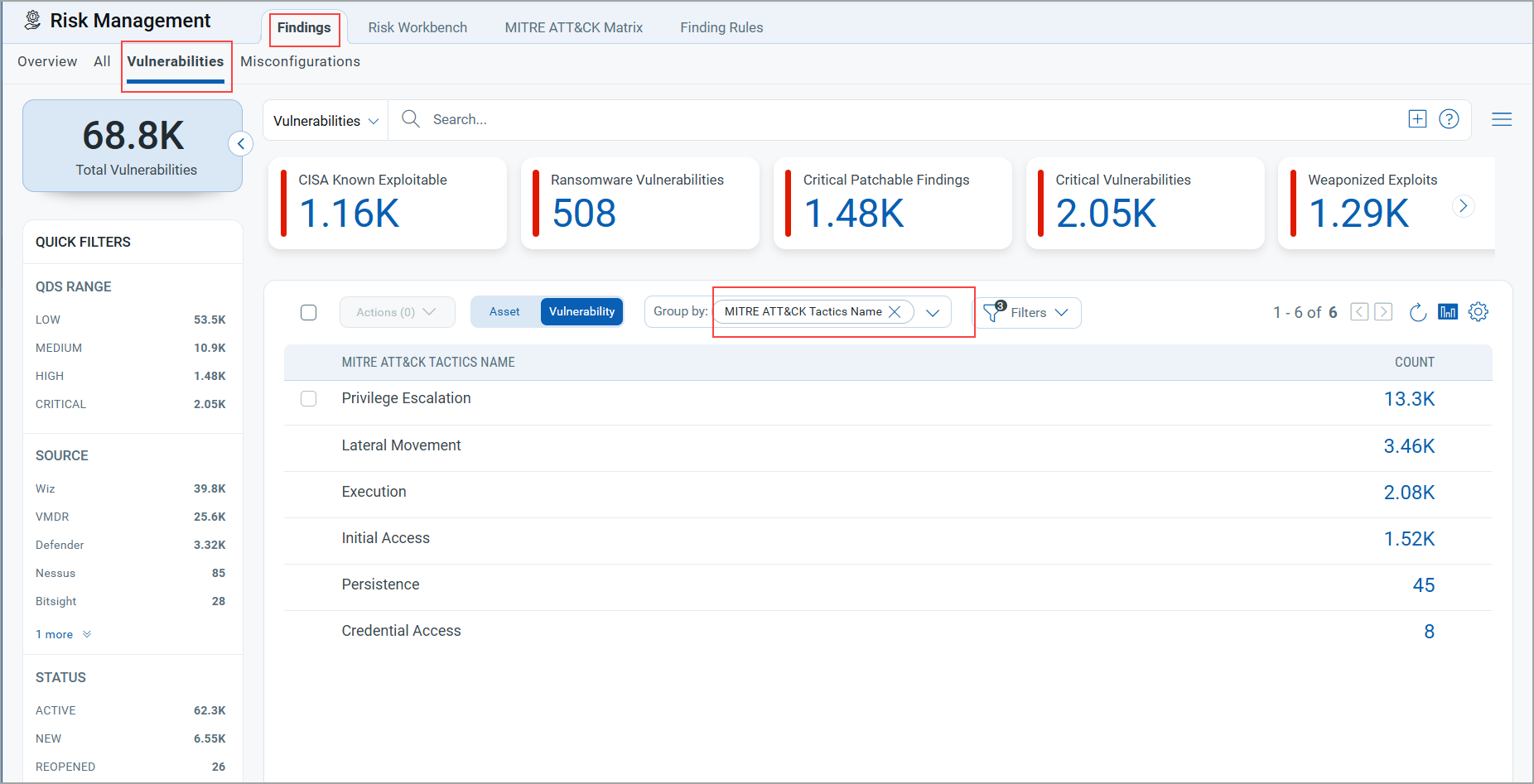
After generating the list, click the Count of a Tactic Name to view the details. For example, clicking the Privilege Escalation Tactic Count displays a list of findings associated with the Privilege Escalation Tactic Name and its related query in the Vulnerabilities query search bar. Refer to the following screenshot for reference.
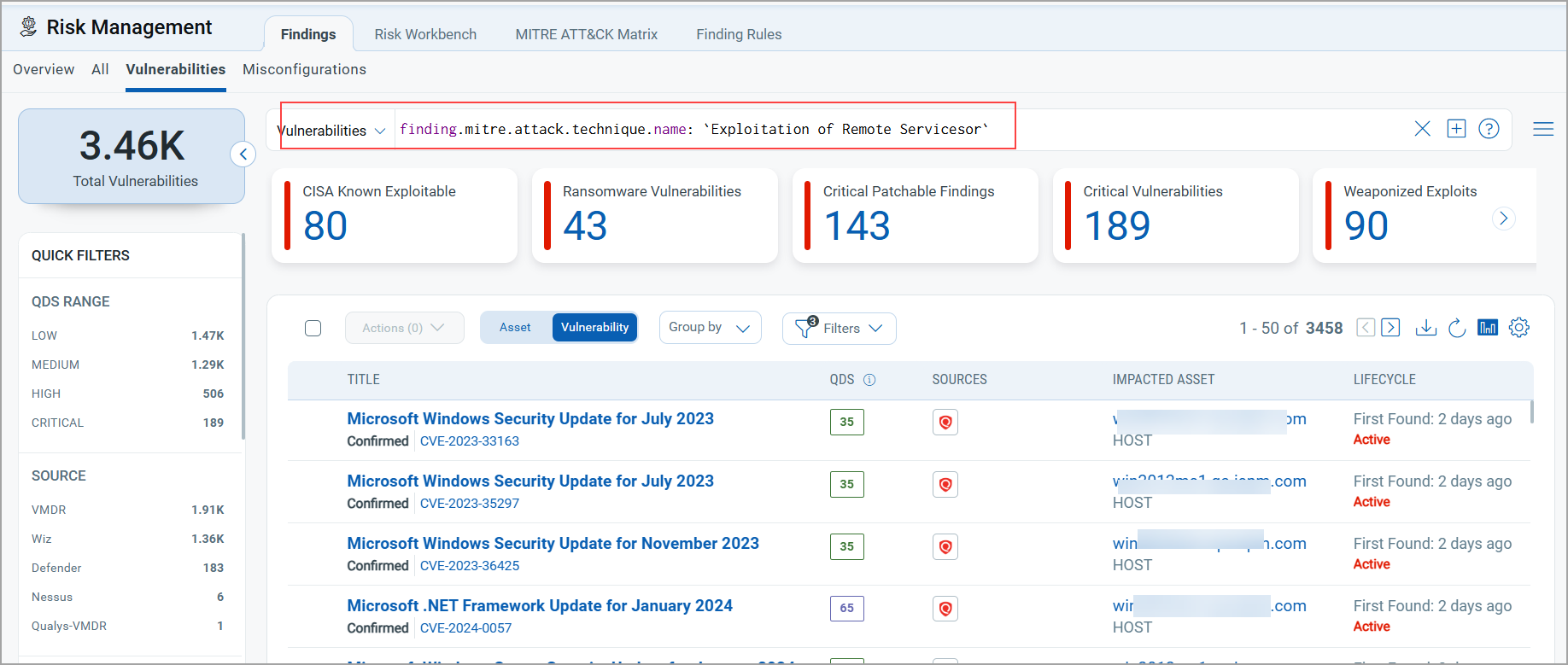
Group By MITRE ATT&CK Technique Name
Select the MITRE ATT&CK Technique Name to retrieve a list of all Technique Names and the total detection count.
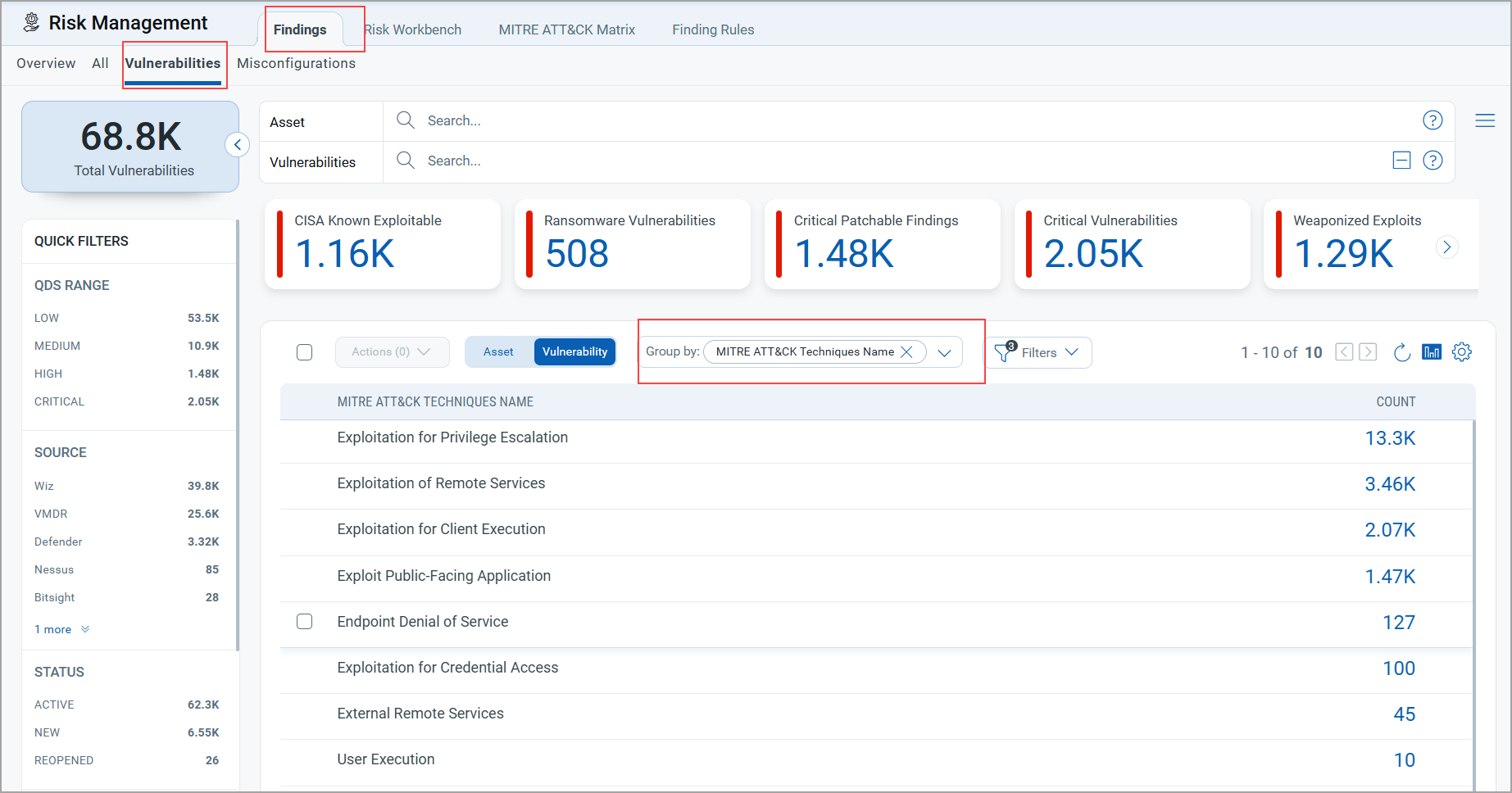
After generating the list, click the Count of a Technique Name to view the details. For example, clicking the Exploitation of Remote Services Technique count displays a list of findings associated with the Remote Services Technique Name and its related query in the Vulnerabilities query search bar. Refer to the following screenshot for reference.
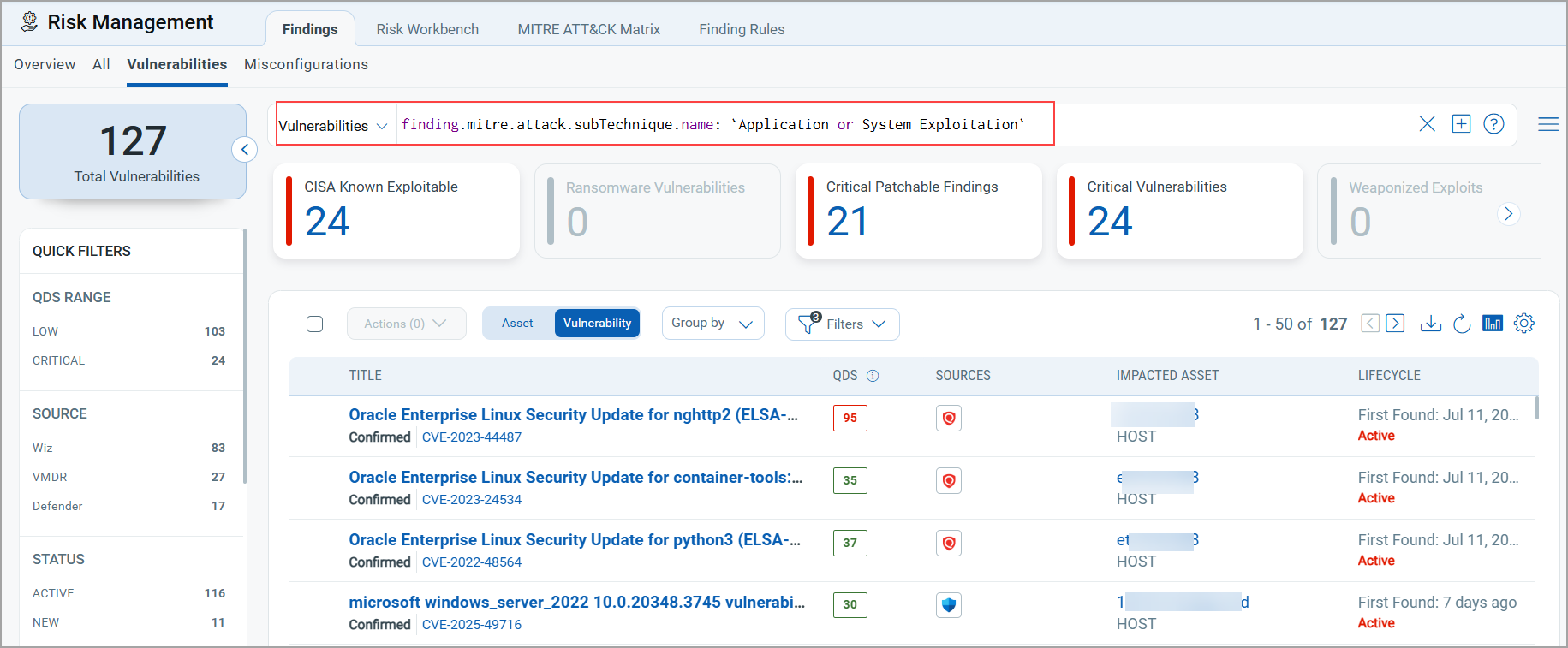
Group By MITRE ATT&CK Subtechnique Name
Select the MITRE ATT&CK Subtechnique Name to retrieve a list of all Subtechnique Names and the total detection count.
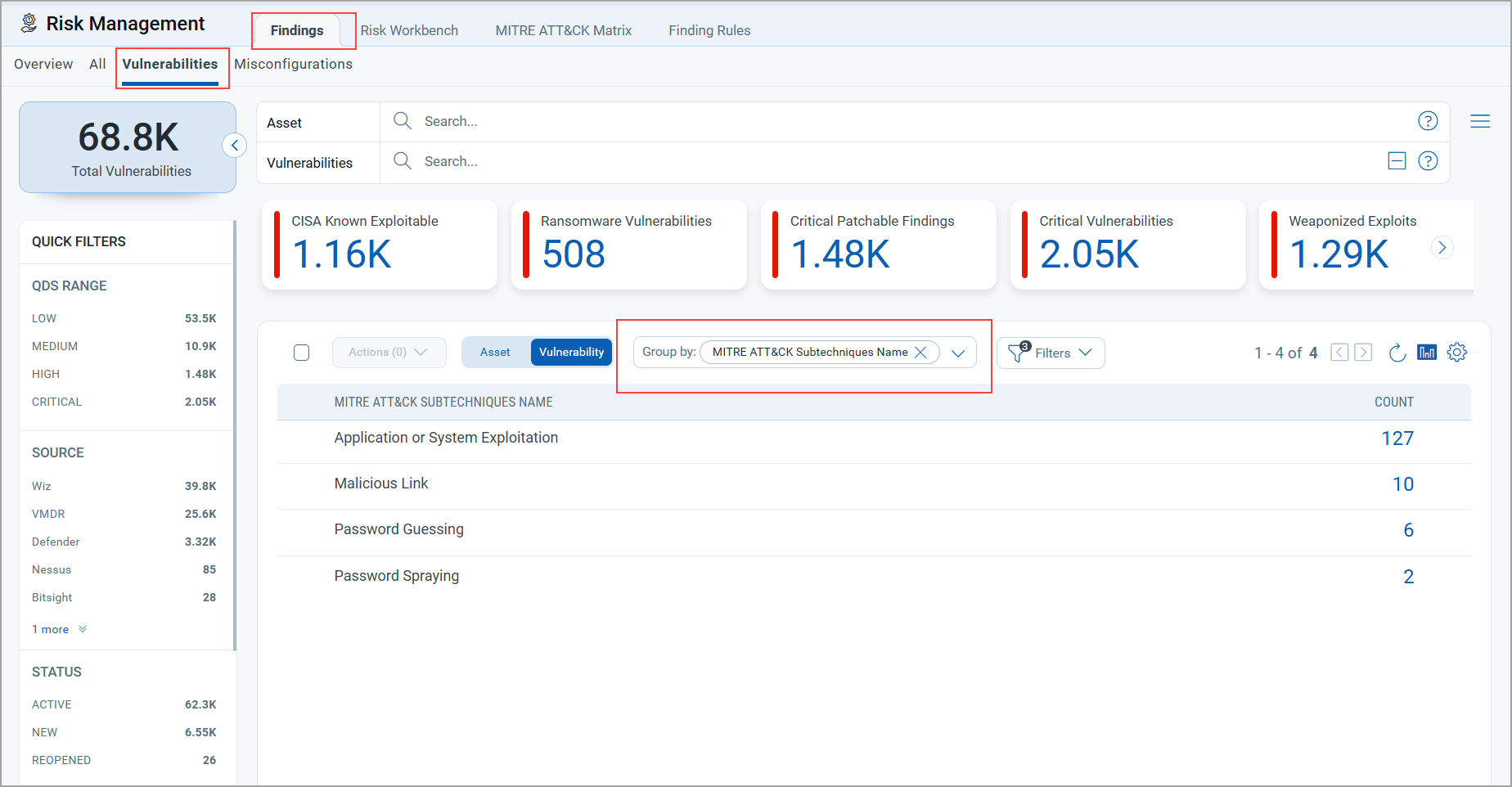
After generating the list, click the Count of a Subtechnique Name to view the details. For example, clicking the Application or System Exploitation Subtechnique count displays a list of findings associated with the Application or System Exploitation Subtechnique Name and its related query in the Vulnerabilities query search bar. Refer to the following screenshot for reference.