Enterprise TruRisk Management Release 1.4
August 28, 2025
Introduced Prioritization Using MITRE ATT&CK Matrix
The MITRE ATT&CK Matrix is a framework created by the non-profit organization MITRE. It helps organizations understand and respond to cyber attacks by describing how attackers behave. This tool gives the cyber security community a common way to talk about and analyze threats so they can better protect against them.
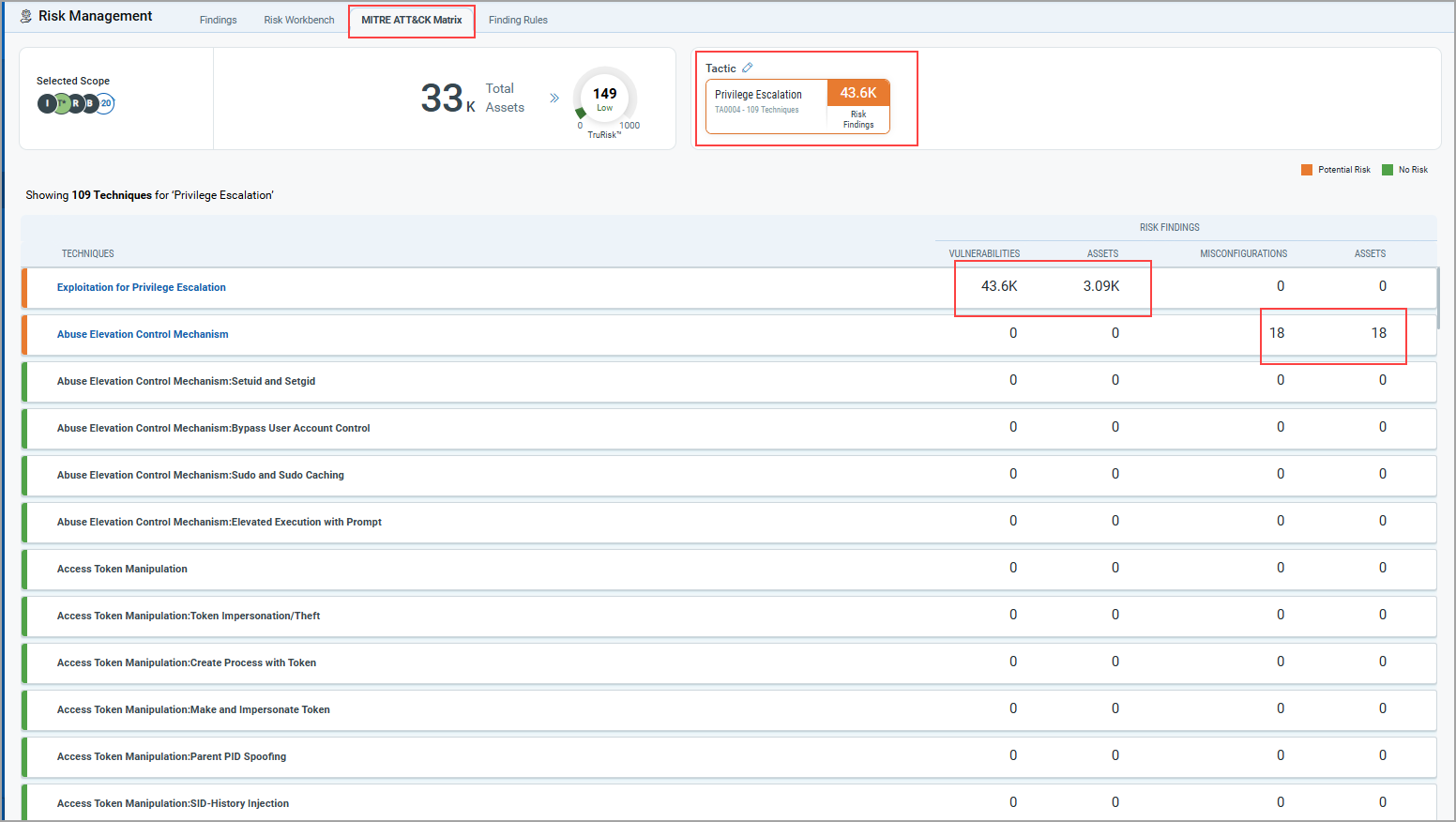
Using Qualys provisioned Enterprise MITRE ATT&CK Matrix, you can identify the gaps in the security architecture, instantly contain the threat, and protect your organization from new attacks. You can select the Business Entities or asset tags as required. The following pictorial representation of the matrix depicts the Tactics and Techniques based on vulnerabilities and misconfigurations.
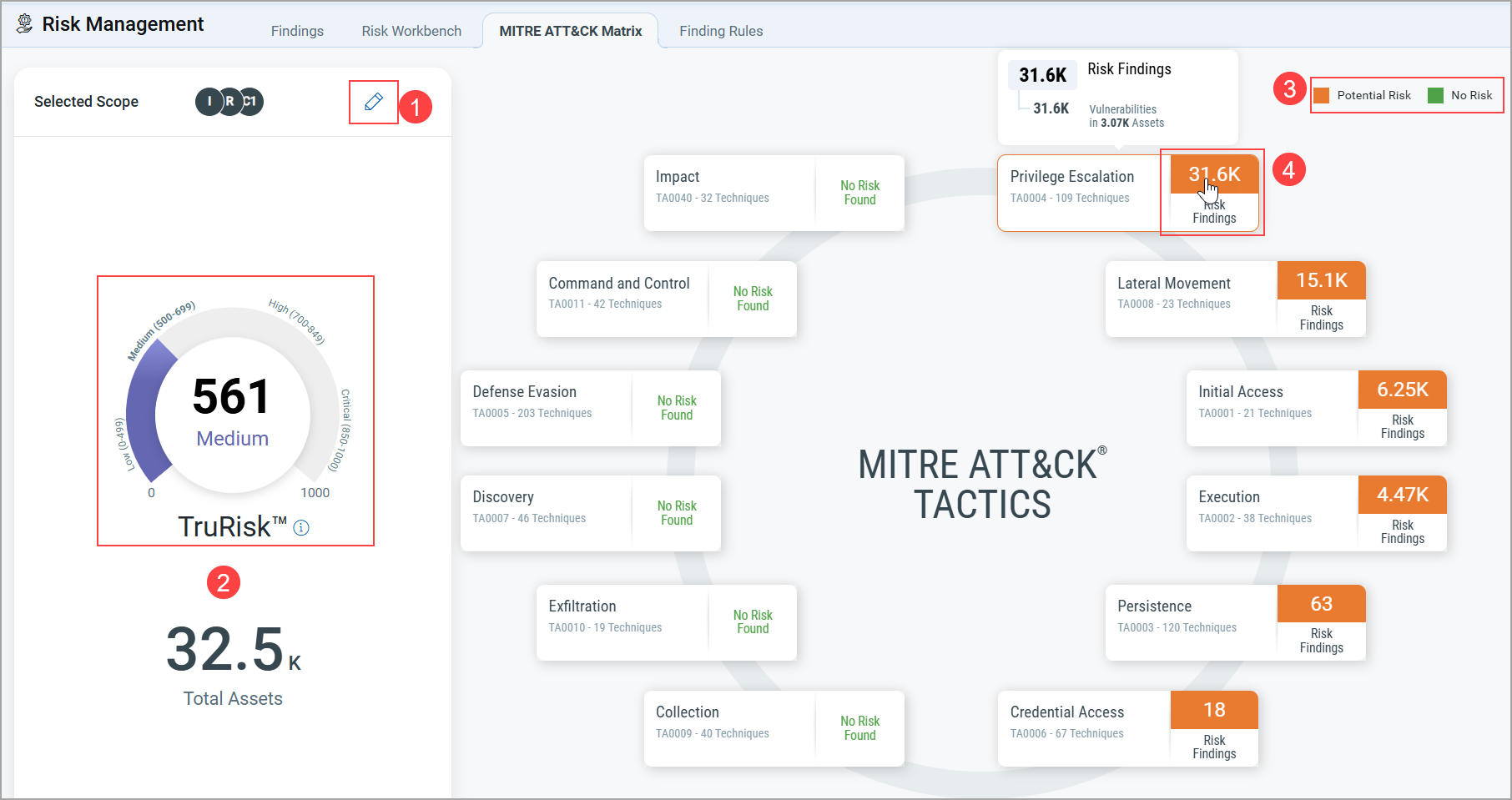
- (1) Editable Scope: Click the pencil icon to modify the scope.
- (2) TruRisk™ Score Graph: Visualizes risk levels through an interactive graph.
- (3) Color-Coded Legend:
- Amber: Potential risk
- Green: No risk
- (4) Interactive Matrix:
- Hover over a Tactic Name to view associated vulnerabilities and techniques.
- Hover over a Technique Name to see related risk findings, including: Total vulnerabilities, Affected assets
- Detailed Technique Insights: Click any Technique Name (e.g., Exploitation for Privilege Escalation) to view full details of associated findings.
For more details, refer to ETM Online Help.
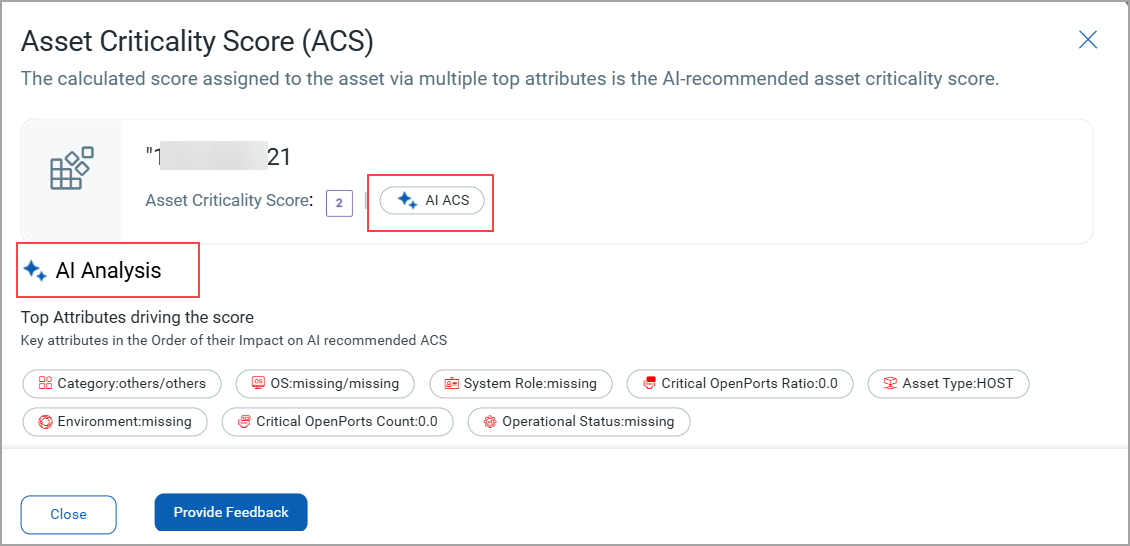
Introduced Asset Criticality Score Prediction by AI
ETM provides an innovative solution for asset criticality assessment: a cutting-edge automated system designed to enhance accuracy and objectivity. The current manual processes can be prone to inconsistencies and may overlook critical assets, leading to potential risks for organizations.
By leveraging advanced AI technology, we provide a dynamic and reliable method for identifying and prioritizing critical assets, ensuring that your organization can effectively safeguard its most vital resources.
This feature is available on request. Contact Qualys support to enable this feature.
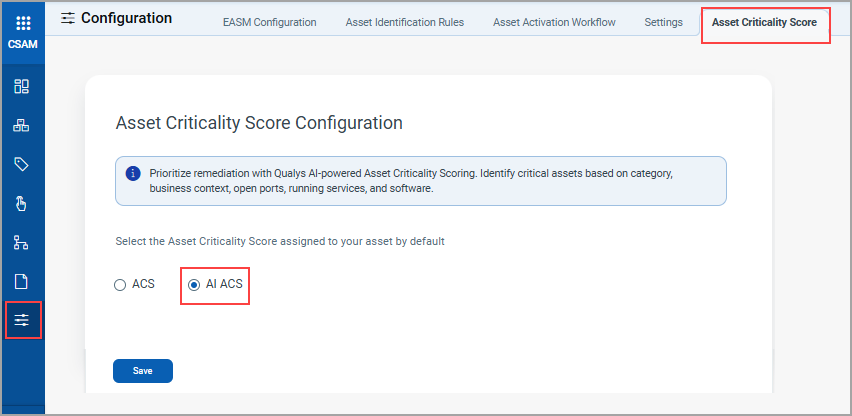
You can access AI ACS in ETM by configuring AI ACS in the CSAM application for the assets. Currently, the AI ACS feature supports assets that are not tagged. Once you enable this feature, you can see that the score is powered by AI ACS.
To configure this feature, go to the CSAM application > Configuration > Asset Criticality Score tab > choose AI ACS.
To view the score in ETM, navigate to ETM application > Inventory tab > Assets > Host. Select the asset for which you would like to view the ACS score and click the score mentioned in front of the asset.
For more information, refer to ETM Online help.
Enhanced Risk Acceptance Rules for Finding Exceptions
Risk acceptance allows organizations to make informed decisions to tolerate specific vulnerabilities without immediate remediation. Common reasons include:
- No available patch
- Downtime constraints
- Application compatibility issues
This decision is usually made when the cost of remediation outweighs the risk or the vulnerability falls within the organization's acceptable risk threshold. After consulting with internal stakeholders, you may categorize certain vulnerabilities as false positives or conclude that specific findings cannot be addressed.
Prerequisites
This feature is available on request; contact support to activate this feature.
The following are the benefits:
- Resource Optimization: Focus resources on higher-priority vulnerabilities.
- Strategic Alignment: Align risk acceptance with business goals and risk appetite.
Now, you can create your risk acceptance rule and define the period when it is in effect or how long specific vulnerabilities or findings are excluded from remediation and TruRisk™ Score calculation. Once the exception period expires, the previously exempted findings may be flagged again for review or remediation. You can define expiry notification settings to configure when and to whom expiry notifications should be sent.
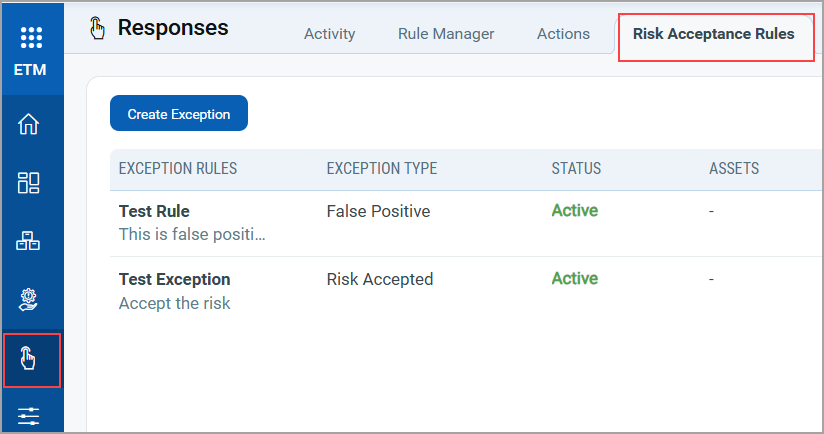
To learn more about the risk acceptance rule and how to use it, refer to ETM Online Help.
Introduced Improved TruRisk™ v2 Formula for Tags and Business Entities
We have a new and improved TruRisk™ v2 formula for Tags and Business Entities, designed to address the limitations of the existing tag-level risk scoring methodology and provide a more accurate and transparent representation of risk.
The current TruRisk™ scoring is based on averaging across assets within a tag. This may result in:
- Risk scores skewing toward low/medium even when critical assets are present
- Risk scores decrease as more high-risk assets are added
- Risk scores increasing after fixing minor issues, giving a false sense of security
The v2 TruRisk™ formula for Tags and Business Entities introduces a more intuitive, risk-aware approach:
- Risk score increases with every added risk element, no matter how small.
- Risk score decreases when any risk is mitigated.
- The formula is explainable, providing transparency into how scores are calculated.
- It is risk-averse by design: if a tag contains critical assets, the overall score leans higher, even if low-risk assets are also present.
The v2 formula is now available wherever TruRisk™ Scores are displayed. For example, Home Page TruRisk™ Score, Business Entity details page, ETM Prioritization Plan, and ETM TruRisk widget.
In the case of v1, you can see the basic definition: 'What is TruRisk™ Score'
This feature is available on request. Contact Qualys support to get this feature enabled.
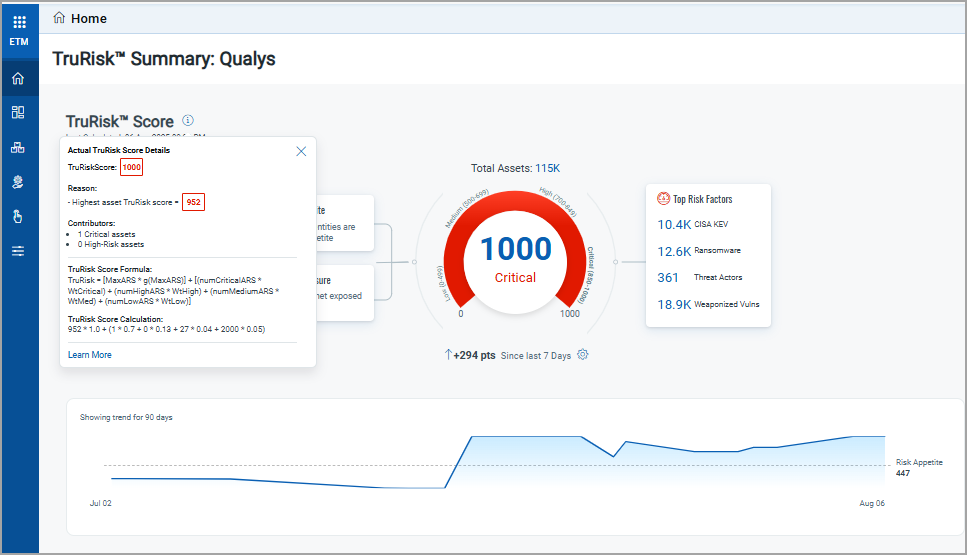
To learn more details, refer to the appendix section of the ETM Online Help.
Added New Tokens for Risk Management Tab
| Token | Description |
|---|---|
|
finding.riskAcceptance.reasonType |
Select the token value as the reason to identify vulnerabilities that have been accepted.
|
|
finding.riskAcceptance.type |
Select token value as RISK_ACCEPTED or FALSE_POSITIVE to identify vulnerabilities that have been accepted.
|
|
finding.riskAcceptance.ruleId |
Use the token value as the risk acceptance rule ID to identify vulnerabilities that have been accepted.
|
|
finding.riskAcceptance.createdDate |
Use the date range or specific creation date of the risk acceptance rule to identify vulnerabilities that have been accepted.
|
|
finding.riskAcceptance.startDate |
Use the date range or specific start date of the risk acceptance rule to identify vulnerabilities that have been accepted.
|
|
finding.riskAcceptance.endDate |
Use the date range or specific end date of the risk acceptance rule to identify vulnerabilities that have been accepted.
|
|
finding.technologyVendor |
Use the token to search the findings based on the technology vendor.
|
Extended Support for Authentication ID Client Management from UI
With this release, we have extended our support for OpenID Connect Authentication Client Management capabilities from the UI. This update allows for secure authentication and authorization of API access directly from the user interface. Our API interactions are now authenticated with enhanced security measures.
ID tokens are generated and validated with utmost security. This seamless integration requires minimal changes to the existing infrastructure, allowing for the maintenance of the highest level of security for APIs.
Access Control
Users can create clients based on access requirements:
User Level Clients
These are associated directly with individual user accounts, making them ideal for user-specific access tracking and control scenarios. The token generated by the user-level client becomes invalid if the user is deactivated.
With the Auth ID Client Management from UI, you can:
- Manage authentication and authorization processes more intuitively, providing a smoother user experience.
- Easily handle API access permissions directly from the UI, simplifying the process of granting and revoking access when needed.
- Maintain your existing workflows with minimal changes, enabling you to continue your tasks without learning new processes extensively.
These settings can be found in the profile settings. To access them, navigate to your profile icon at the top right corner, click View Profile, and then go to the Auth ID Client Management tab.
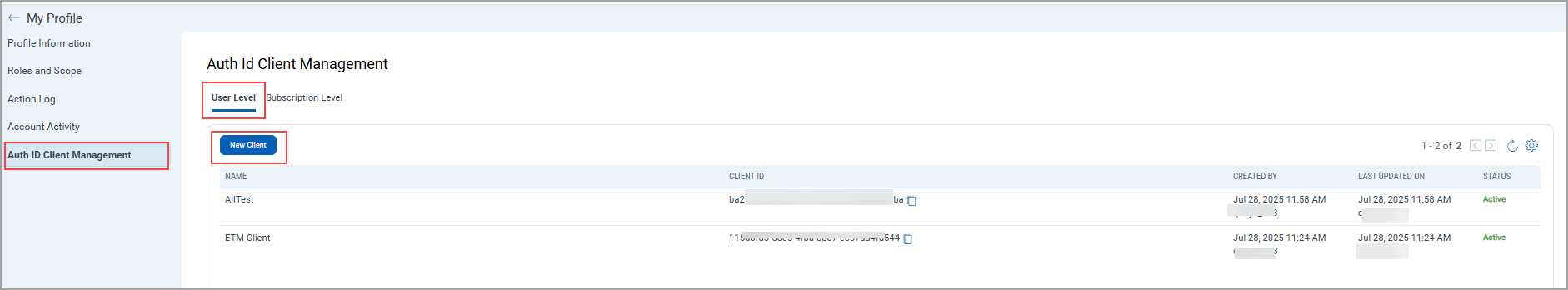
For Client Creation, click New Client.
While creating a client, you can select all modules at once or individual modules. You can also choose global permissions, dashboard permissions, tagging permissions, API, and UI access.
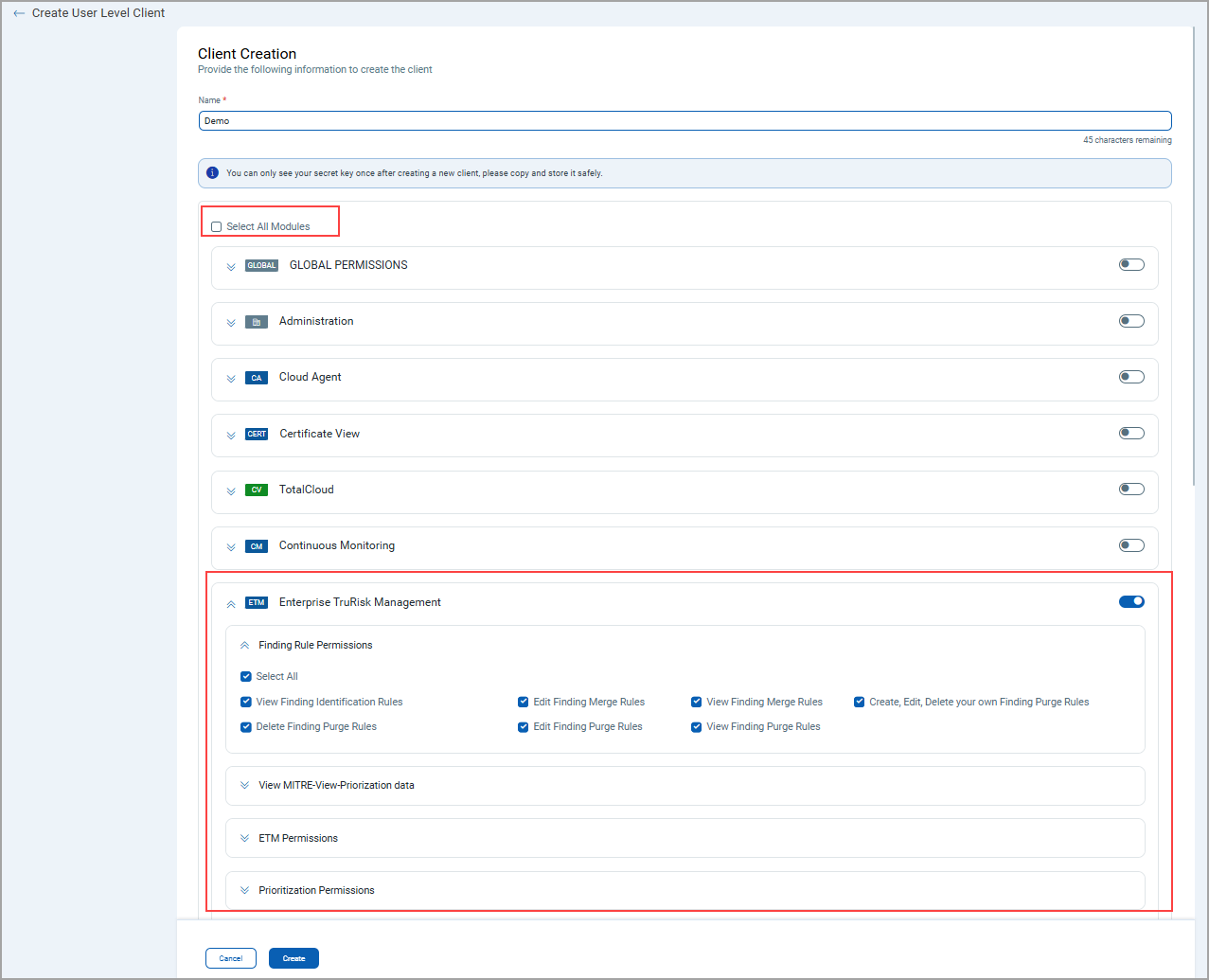
Based on the permissions you select:
If the API Access permission is not enabled under Global Permissions > Access, the API returns a response with this message:
The user does not have permission to access the API module.
Introduced Multigrouped Table and Bar Widgets in Widget Builder
We have updated our widget builder to create multigrouped table and bar widgets. You can now consolidate various data points and group them using a multi-parameter multi-grouped widget. This multigrouped option is available for Findings.
This enhancement significantly improves how you visualize, organize, and communicate multiple data points:
- Helps in uncovering patterns or trends across multiple dimensions (e.g., severity, asset group, status).
- Reduces the need to create and manage multiple separate widgets for complex data comparisons.
- Enhances dashboard efficiency and clarity, especially when working with large data sets in Findings.
Table Widget
You can visualize, consolidate, and communicate multiple data points through a single widget using a multi-grouped table widget. The Table Widget supports up to three Group By levels, allowing for a more granular and organized view of your data. Tables now support Expanded and Collapsed views under the Multigrouped option for easier navigation and readability.
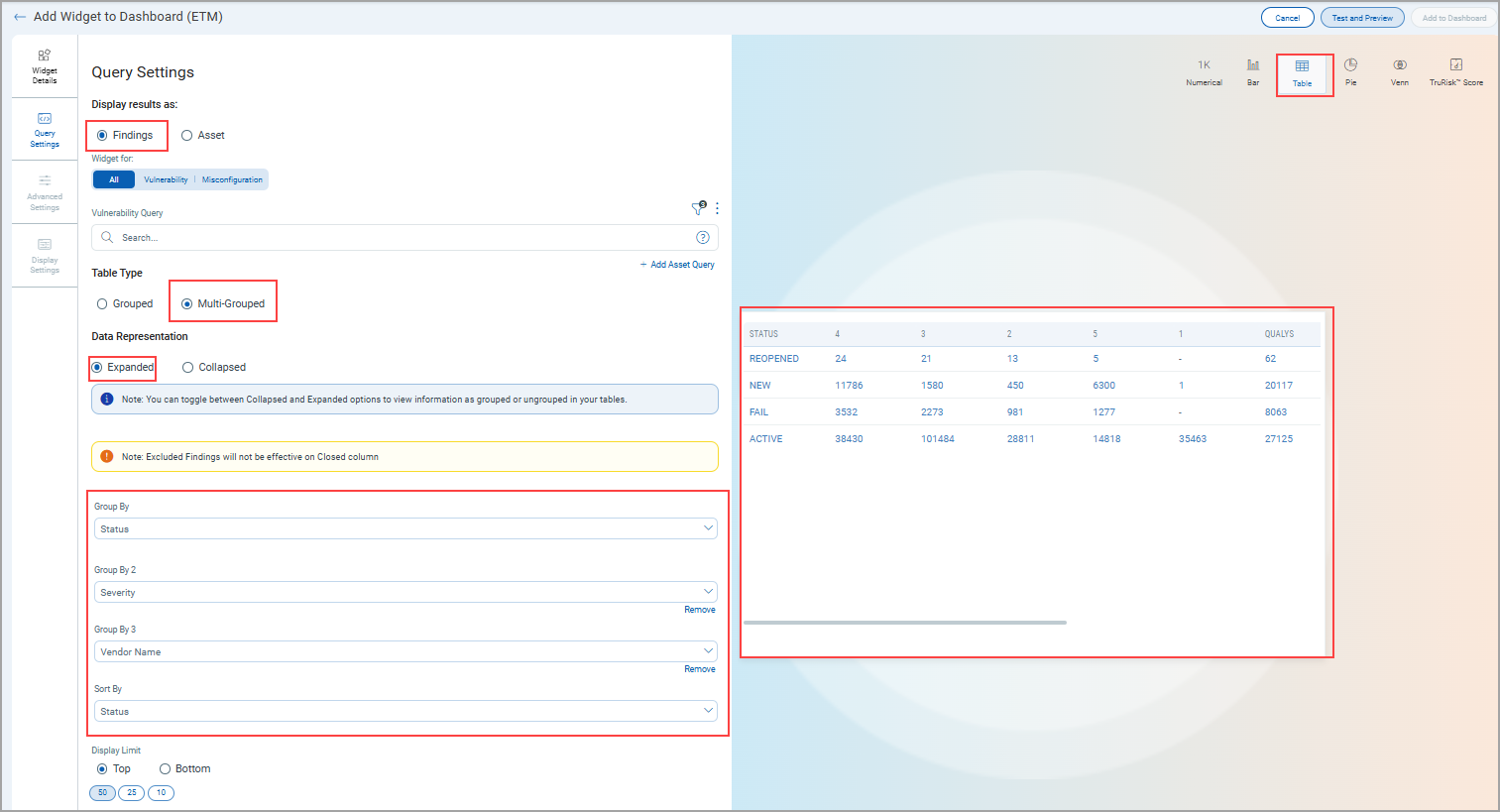
The following screenshot displays the Multigroup option in Expanded mode.
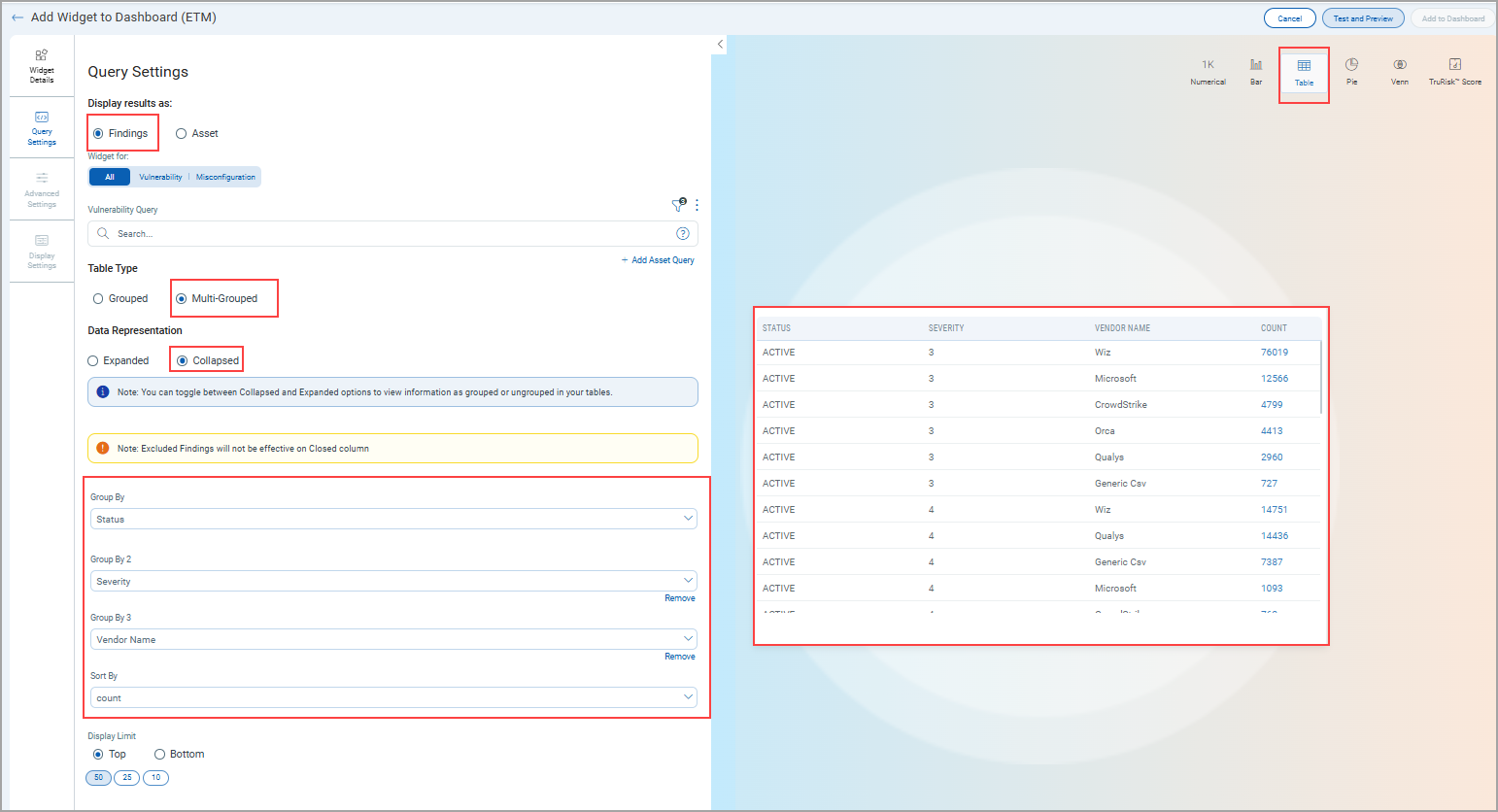
The following screenshot displays the Multigrouped option in Collapsed mode.
Bar Widget
You can visualize, consolidate, and communicate multiple data points through a single widget using a multigrouped Bar widget. The Bar Widget supports up to three Group By levels, allowing for a more granular and organized view of your data.
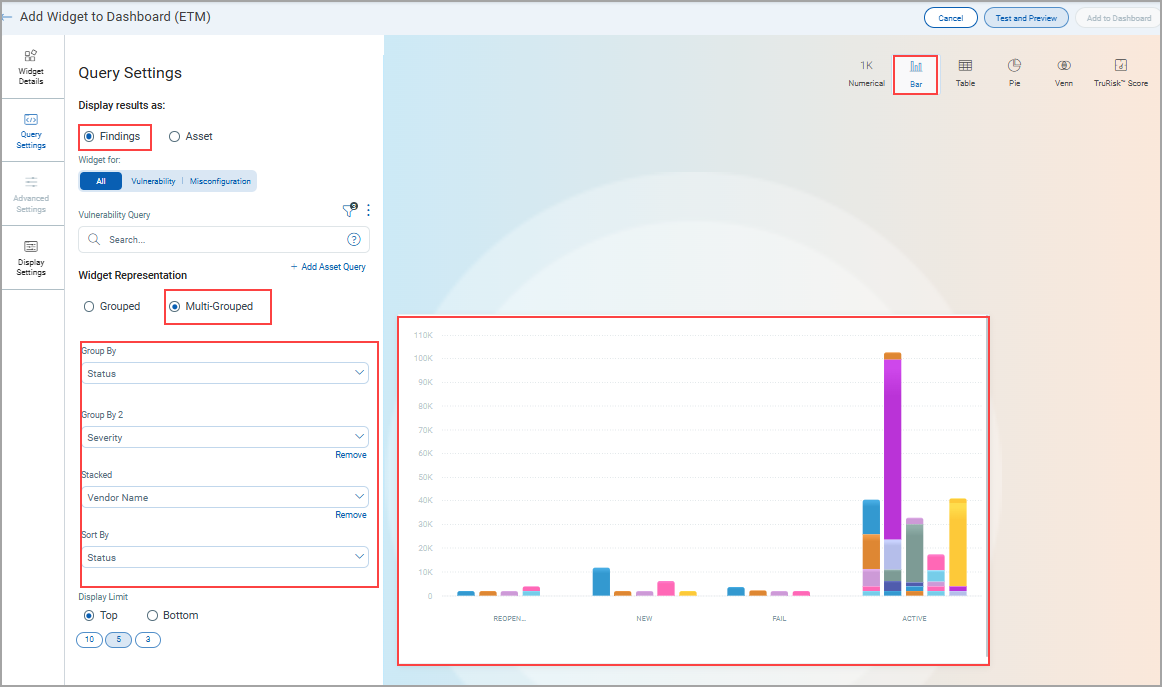
The following screenshot displays the Multigrouped option in the Bar Widget.
Enhanced Misconfiguration Tab for TruRisk™ Score Page
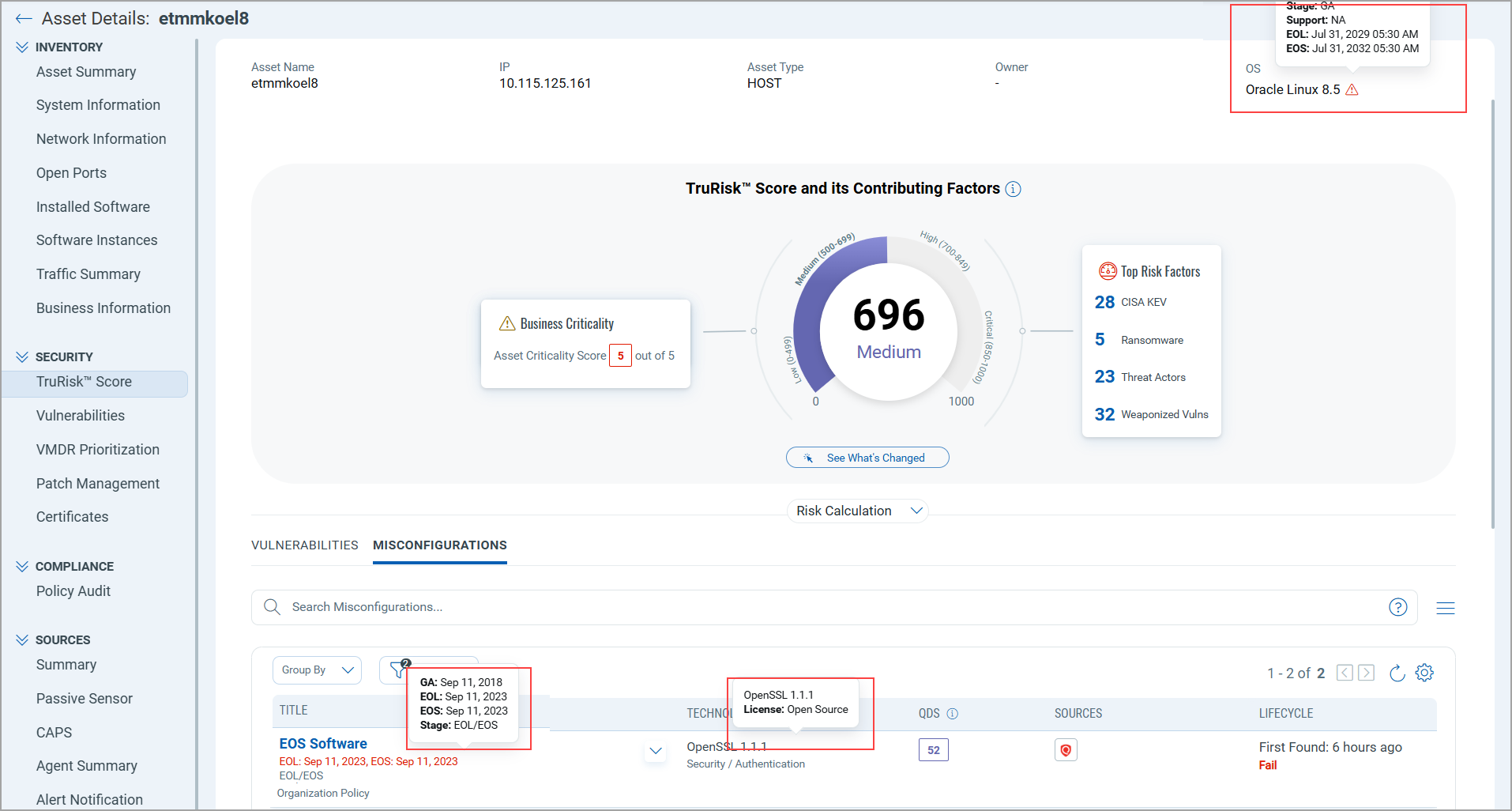
With this release, you can now view End of Support (EOS) and End of Life (EOL) GA release dates for products by hovering over the EOS Software entries in the Misconfiguration tab of the TruRisk™ Score page. Additionally, when you hover over a Technology entry, you can view its name and license details for better clarity and context.
To view this detail, navigate to the Inventory tab, select View Details from the Quick Action menu of the selected asset, and go to the TruRisk™ Score page.
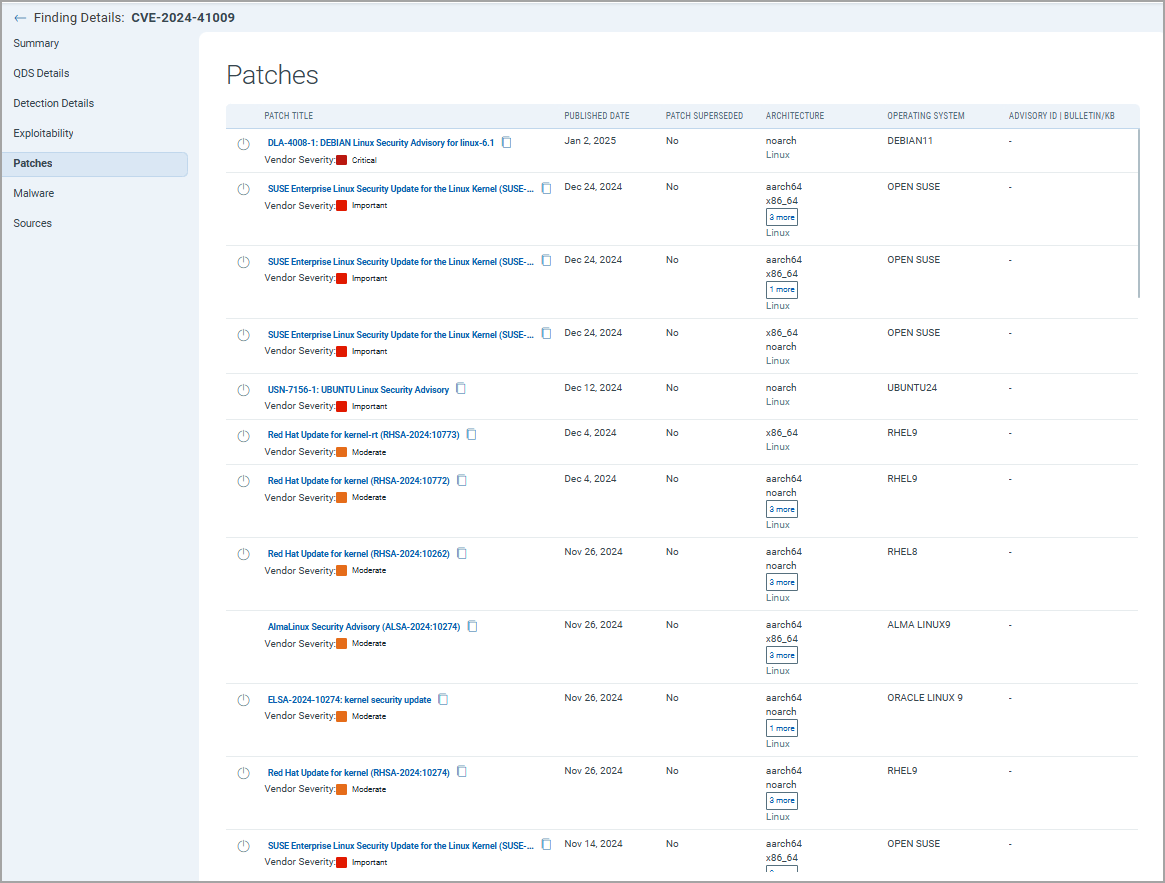
Introduced Patch Details for Vulnerabilities
We have introduced Patch details for vulnerabilities. You can now view Patches available for CVE on the Finding details page.
Patching software vulnerabilities is crucial for system security. It helps prevent cyberattacks by fixing exploitable bugs and improving software performance. Many regulations mandate updates to protect sensitive data. Unpatched systems are vulnerable, risking sensitive and financial information. Regular patching is essential for both security and efficiency.
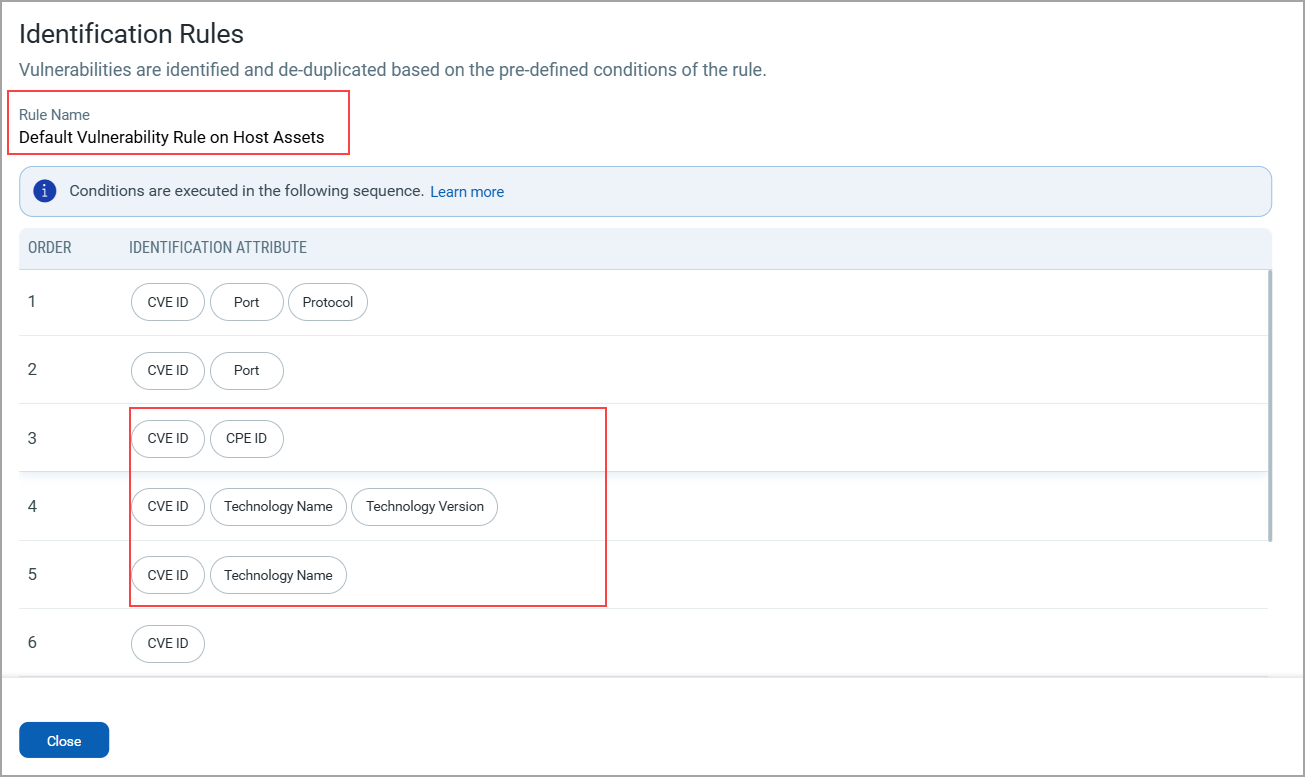
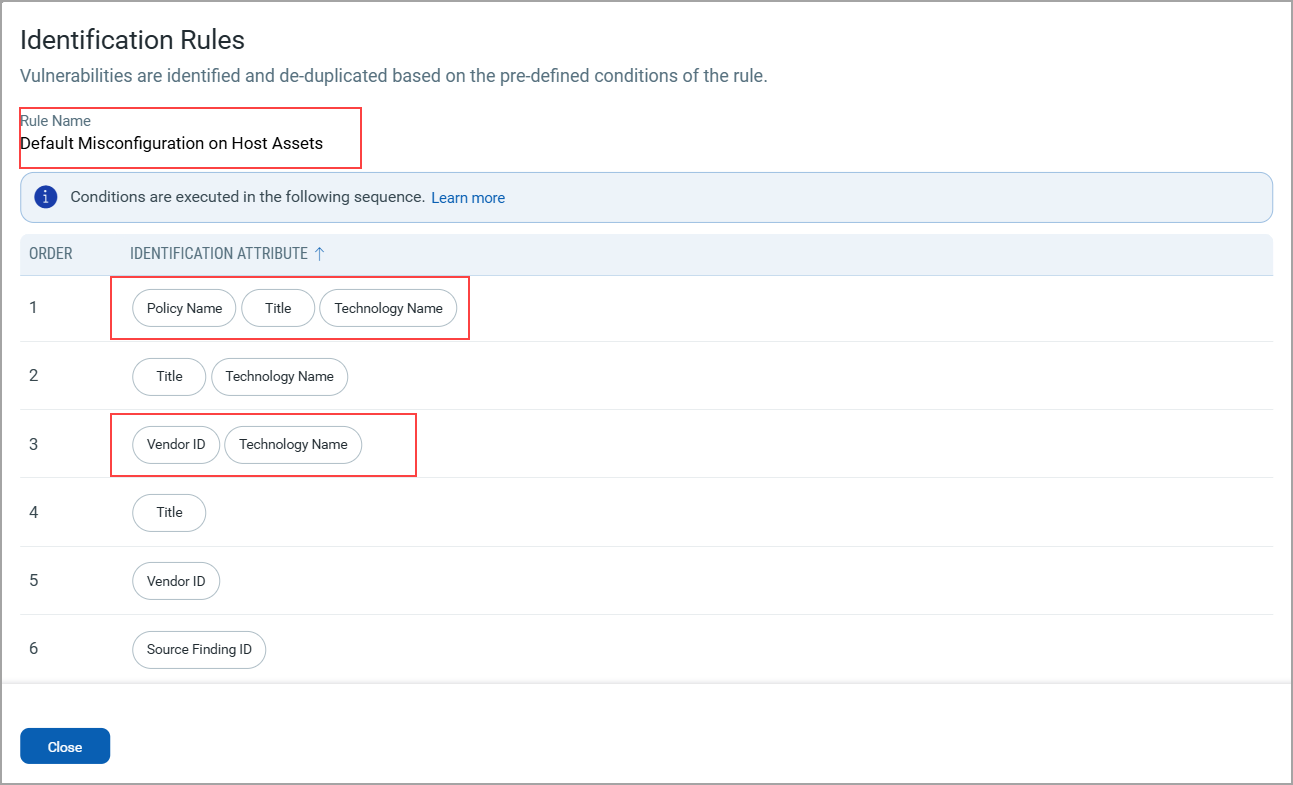
Enhanced Identification Rules
In ETM, vulnerability data is derived from multiple sources, so there is a chance that data may overlap (for example, identical CVEs with asset context). To prevent duplicates, predefined Vulnerability Rule conditions use unique identification attributes from the Common Data Model.
Vulnerability Identification Rule on Host Assets
With this release, we have now added [CVE ID, CPE ID], [CVE ID, Technology Name, Technology Version], [CVE ID, Technology Name]. Adding CPE ID enhances the precision of vulnerability identification by providing a standardized product reference. This reduces false positives, ensures consistent mapping across sources, and improves the accuracy of merging vulnerabilities from different data feeds.
Misconfiguration Identification Rule on Host Assets
With this release, we have added [Policy Name, Title, Technology Name] and [Vendor ID, Technology Name]. Adding Policy Name, Title, Technology Name, and Vendor ID strengthens vulnerability identification by capturing more unique context for each finding. This ensures more accurate matching, reduces duplication, and improves consistency when correlating data from multiple sources.
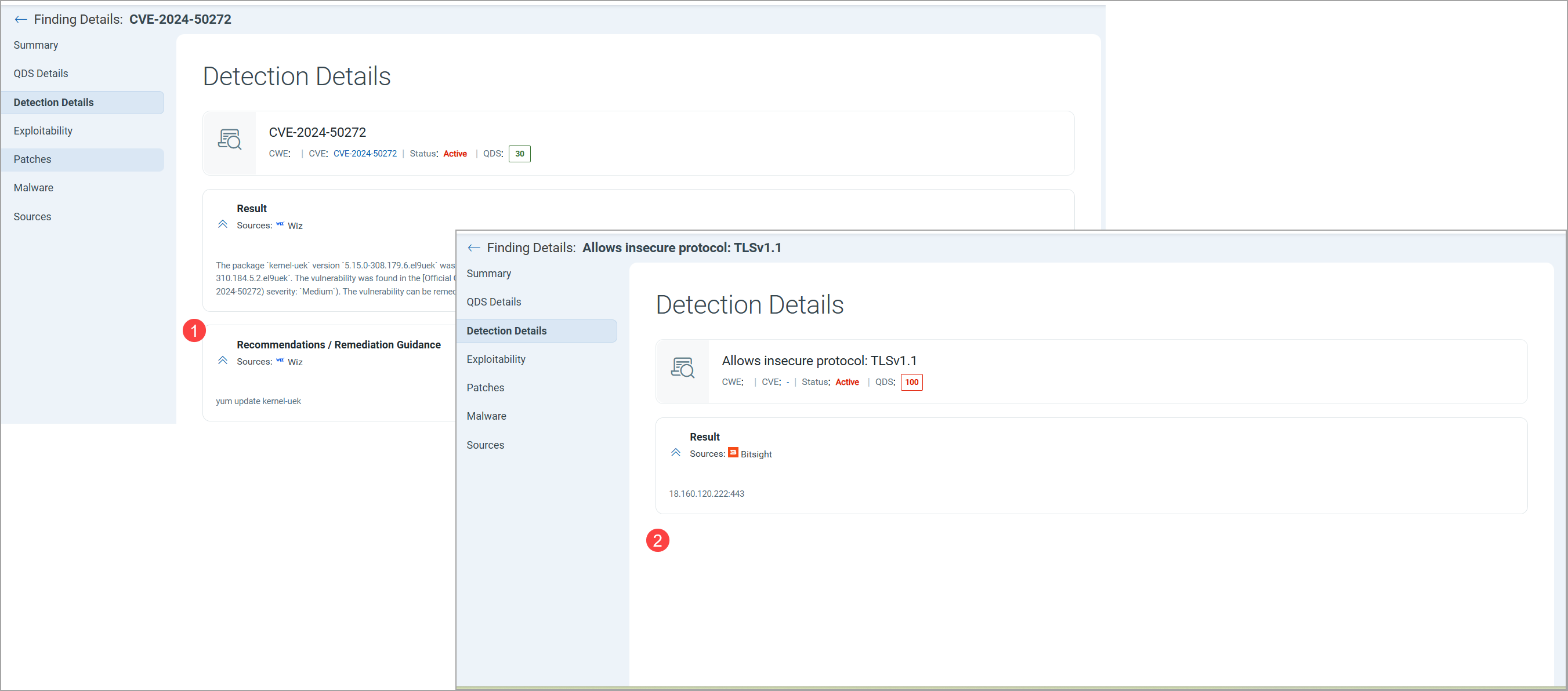
Improved UI Detection Details Page
With this release, the Detection Details section of the Finding Details page has been improved. Fields with NA values are now hidden, resulting in a cleaner, more focused interface. This helps users quickly locate relevant information without distraction from non-applicable fields, improving readability and efficiency in reviewing findings.
The following screenshots are taken from two different findings. In the first screenshot, we have a recommendation, so the field reflects this information. In the second screenshot, the recommendation information is missing, hence the field is not seen in the screenshot.
To view the Detection Details page from Findings, navigate to Risk Management > Findings > Vulnerabilities> select the Finding.
Issues Addressed
There are no notable customer issues in this release.