Enterprise TruRisk Management Release 1.6.1
February 20, 2026
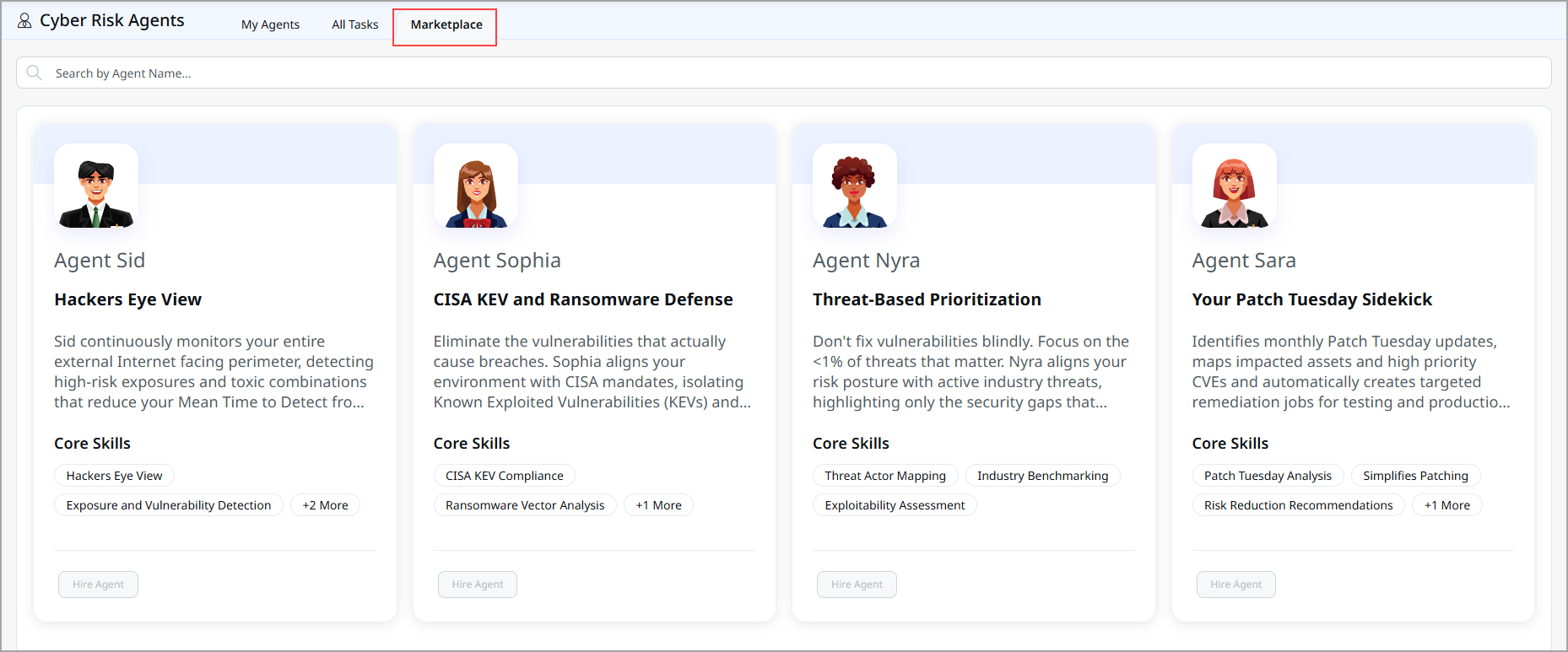
Introduced New Autonomous Security Partners (Agentic AI)
We have introduced the new Agentic AI Suite, a groundbreaking collection of four intelligent, autonomous agents designed to transform how your organization manages cybersecurity risk. Built to function with intelligence and autonomy, these agents automate complex security operations while maintaining human oversight and control at every critical decision point.
The Agentic AI Suite comprises four specialized agents: Agent Nyra, Agent Sara, Agent Sid, and Agent Sophia. Each agent is engineered to excel in specific domains, working collaboratively to strengthen your security posture across threat prioritization, patch management, external asset discovery, and exploit-driven vulnerability remediation.
This update is a significant step forward in autonomous security operations, allowing your teams to work more intelligently, efficiently, and strategically.
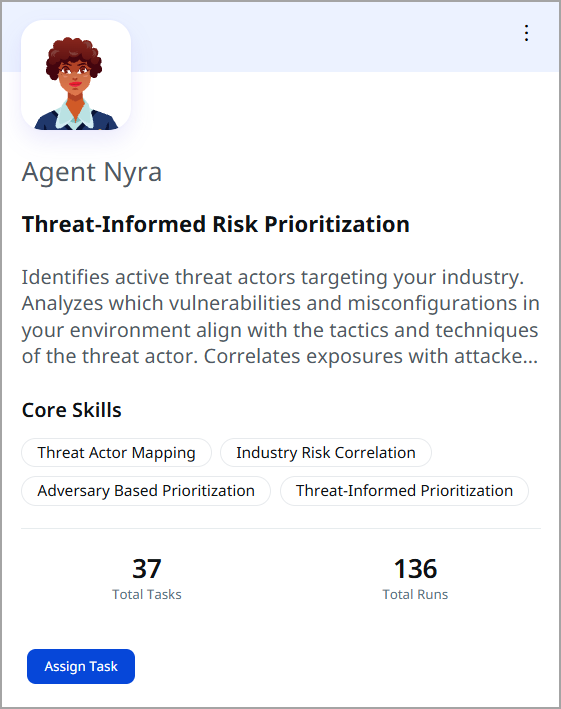
Agent Nyra: Threat-Informed Risk Prioritization
Agent Nyra transforms how you prioritize security remediation by analyzing vulnerabilities through the lens of actual threat actors targeting your industry. Rather than relying on generic CVSS scores, Nyra identifies which vulnerabilities and misconfigurations adversaries in your sector are actively exploiting, delivering threat-aligned prioritization grounded in real attacker behavior.
The Problem Nyra Solves
Traditional vulnerability management relies on standardized risk scoring that treats all organizations equally. This approach often leads to wasted remediation effort on vulnerabilities with high theoretical scores that attackers in your industry may never target. Meanwhile, vulnerabilities actively being exploited by your actual threat actors may be overlooked.
Agent Nyra changes this equation by bridging threat intelligence and vulnerability management.
Key Capabilities of Agent Nyra
Nyra has the following key capabilities:
- Identifies your industry context
Nyra understands your organization's industry classification and analyzes threat landscapes specific to your sector, ensuring all analysis reflects real-world targeting patterns relevant to your business. - Filters global threat intelligence by industry
Nyra analyzes global threat intelligence data to identify adversaries, malware families, and campaigns actively targeting your specific industry vertical, isolating signal from noise. - Maps adversary behavior to your environment
Nyra correlates industry-relevant threat actors with vulnerabilities and misconfigurations present in your infrastructure, creating a direct link between your exposures and attacker tactics. - Enriches exposure with attacker tactics
Every finding aligns with MITRE ATT&CK techniques, Real-Time Indicators (RTIs), and known attack behaviors, revealing not only what is vulnerable but also how attackers intend to exploit it. - Produces threat-informed outputs for action
The agent generates threat-aligned exposure summaries, prioritization plans, and draft patch jobs, all prepared for human review and decision-making.
What You Get
This release equips your teams with threat-aligned insights and actionable outputs that connect exposure data with real-world adversary activity. The result is clearer visibility into risk, smarter prioritization of remediation efforts, and improved communication with stakeholders.
-
Threat-informed exposure summaries
Clear identification of industry-targeting adversaries, affected findings, and MITRE ATT&CK techniques present in your environment. Automatically emailed to stakeholders. -
Attacker-aligned prioritization plans
Remediation strategies ordered by threat actor relevance, exploitation likelihood, and business impact, transcending CVSS-based rankings. -
Draft patch jobs
Pre-prepared patch recommendations are scoped exclusively to adversary-linked vulnerabilities and require human approval before execution. -
Email notifications
Automatic updates with threat-aligned findings, industry-relevant actors, and remediation priorities delivered to leadership for visibility.
When to Use Agent Nyra
You can use Nyra to:
- Validate risk against actual attacker behavior during threat-driven prioritization cycles
- Conduct monthly or quarterly reviews, ensuring remediation aligns with evolving threat landscapes
- Evaluate ransomware readiness by identifying vulnerabilities exploited by ransomware actors targeting your industry
- Demonstrate to leadership why threat-informed prioritization outperforms generic vulnerability scoring
Best Suited For
Agent Nyra is best suited for the following teams:
- Security Operations teams seeking threat context
- Threat Intelligence teams correlating intelligence with exposure
- CISOs and security leaders presenting risk to executives
- Incident Response teams' understanding of attacker tactics
Core Strengths of Agent Nyra
Nyra's core strengths are:
- Threat Actor Mapping
- Industry Risk Correlation
- Adversary-Based Prioritization
- Threat-Informed Decision Making
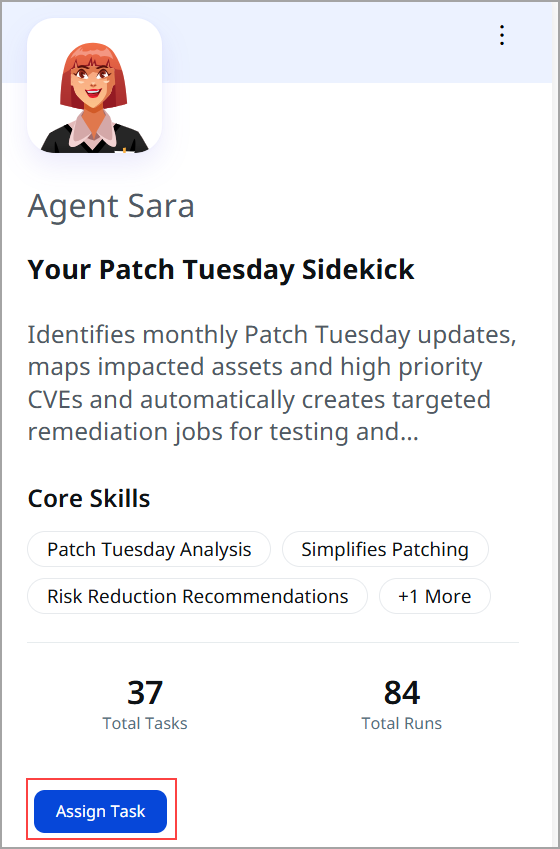
Agent Sara: Your Patch Tuesday Sidekick
Agent Sara automates the labor-intensive process of responding to Patch Tuesday releases. Every month, vendors release security updates in a coordinated event that impacts thousands of organizations. Agent Sara tracks these vulnerabilities, assesses their impact on your environment, and delivers ready-to-execute remediation plans all within minutes of release.
The Problem Sara Solves
Patch Tuesday management is a monthly operational burden. Security teams must review vendor advisories, extract CVEs, map vulnerabilities to assets, assess business impact, and create remediation plans. This process typically consumes hours of manual effort and delays remediation during the critical window when patch availability is highest.
Agent Sara eliminates this manual work, moving from reactive triage to proactive action within minutes.
Key Capabilities of Agent Sara
Sara has the following key capabilities:
- Identifies the current Patch Tuesday cycle
Sara detects the active Patch Tuesday release month and automatically gathers associated vendor advisories and CVEs from major vendors. - Tracks Patch Tuesday CVEs
The agent continuously monitors and maintains the authoritative list of Patch Tuesday CVEs for the current month, filtering out older vulnerabilities to keep analysis focused. - Maps Patch Tuesday CVEs to your environment
Sara correlates Patch Tuesday vulnerabilities with your specific assets and findings across hosts, applications, cloud workloads, and container images. - Analyzes Patch Tuesday exposure
The agent identifies impacted assets, total findings, unique CVEs, and critical issues, and provides percentage-impact metrics for your overall environment. - Aligns Exposure with business context
Highlights Patch Tuesday impact on crown jewels (Asset Criticality Score ≥ 4/5), critical business entities, and essential assets configured in your system. - Generates Patch Tuesday actions
Produces Patch Tuesday-specific exposure summaries, prioritization plans, and draft patch jobs prepared for human review and execution. - Enables controlled Patch Tuesday remediation
Facilitates faster, safer Patch Tuesday remediation through a structured, human-in-the-loop workflow aligned with enterprise change control.
What You Get
With the help of agent Sara, you can refined your outputs in the form of
-
Exposure summaries
Narrative summaries detailing the impact of Patch Tuesday will include information on the top affected asset groups, the distribution of critical findings, and actionable next steps. These summaries are available in-product or via email. -
Prioritization plans
The analysis is scoped specifically to the current month's Patch Tuesday vulnerabilities, taking into account their criticality, the nature of business entities, and the protection of essential assets, while remaining fully editable by team members. -
Draft patch jobs
Prepared patch jobs including all affected assets, mapped patches, scope filters, and justification summaries. Human approval is always required before execution. -
Email notifications
Automatic updates with exposure summaries, prioritization plans, and patch job notifications, following standard templates for consistency and audit compliance.
When to Use Agent Sara
You can use Sara to:
- Run immediately after Patch Tuesday releases to understand scope, urgency, and environmental impact within hours.
- Use exposure summaries and prioritization plans during monthly patch planning and change management reviews.
- Create concise leadership summaries for Change Advisory Board reviews and executive briefings outlining impact and business justification.
- Track weekly remediation progress throughout the month, monitoring what has been patched and what requires attention.
Best Suited For
Agent Sara is best suited for the following teams:
- Vulnerability Management teams managing monthly patch cycles
- IT Operations and Patch Management teams overseeing deployments
- Security Operations teams coordinating remediation
- Security leaders and CISOs reporting to executives
Core Strengths
Sara's core strengths are:
- Patch Tuesday Coverage and Tracking
- Rapid Exposure Analysis
- Risk-Based Prioritization
- Automated Patch Job Drafting
Agent Sid: Hacker's Eye View of Your Perimeter
Agent Sid provides an external attack surface perspective by discovering and analyzing all internet-facing assets across your organization. The agent continuously scans for web applications, open ports, exposed databases, weak certificates, and security misconfigurations, exactly what hackers see when probing your perimeter. Sid transforms external asset management from a manual, incomplete process into continuous, comprehensive visibility.

The Problem Sid Solves
Many organizations have only partial visibility into their internet-facing infrastructure. Shadow IT, unmanaged subsidiaries, legacy systems, and cloud resources often exist outside formal asset management systems, creating blind spots that attackers actively exploit. Without a complete inventory of the external perimeter, security teams cannot accurately assess external risk.
Agent Sid eliminates these blind spots by automatically discovering and cataloging your entire external attack surface.
Key Capabilities of Agent Sid
Sid has the following key capabilities:
- Starts from trusted seed inputs
Sid begins discovery with known inputs such as organization name, domain names, or IP netblocks, anchoring and focusing the discovery process for accuracy. - Discovers your external attack surface
The agent continuously identifies internet-facing assets across domains, subsidiaries, cloud providers, and IP space, performing both horizontal and vertical domain enumeration. - Attributes assets to your organization
Sid correlates DNS records, WHOIS data, and infrastructure signals to accurately map discovered assets and subsidiaries to your organization, eliminating false positives. - Tags and adds assets to your inventory.
Automatically tags discovered assets as EASM (External Attack Surface Management) and adds them to your Unified Asset Inventory for tracking and analysis. - Analyzes external exposures
The agent evaluates risky open ports, exposed services, databases, weak SSL/TLS configurations, expired certificates, and typosquatted domains. - Detects high-risk and toxic combinations
Sid flags priority exposures such as internet-facing assets with critical vulnerabilities, high-risk ports with available exploits, and publicly reachable databases. - Generates EASM summary reports
Creates comprehensive, actionable External Attack Surface Management reports that capture your external exposure in a shareable, leadership-ready format.
What You Get
With the help of agent Sid, you can refined your outputs in the form of
-
Exposure Summaries – Point-in-time snapshots of your internet-facing exposure displayed on Agent Sid's details page, showing assets, risky ports, exposed databases, certificates, and domains.
-
EASM Summary Reports – Downloadable PDF reports capturing external exposure in a structured, shareable format suitable for leadership, audits, and red teams.
-
Continuous Monitoring – Automatic updates with exposure snapshots, ensuring you maintain a current understanding of your perimeter over time.
-
Email Notifications – Automatic updates with exposure snapshots and EASM report notifications in a compact, readable format for stakeholder understanding without platform login.
When to Use Agent Sid
You can use Sid to:
- Maintain continuous external attack surface visibility with regular automated discovery runs
- Prepare comprehensive EASM reports before audits and compliance assessments to demonstrate external security posture
- Provide red teams and penetration testing teams with a comprehensive asset inventory and exposure analysis
- Discover unmanaged assets, shadow IT, and unaccounted-for subsidiaries contributing to external risk
Best Suited For
Agent Sid is best suited for the following teams:
- Security Operations teams managing perimeter defense
- Attack Surface Management teams overseeing external infrastructure
- CISOs and risk owners assessing organizational exposure
- Incident Response teams understanding of attack vectors
Core Strengths of Agent Sid
Sid's core strengths are:
- External Attack Surface Management (EASM)
- External Exposure Analysis
- Continuous Perimeter Discovery
- Risk Surface Management and Attribution
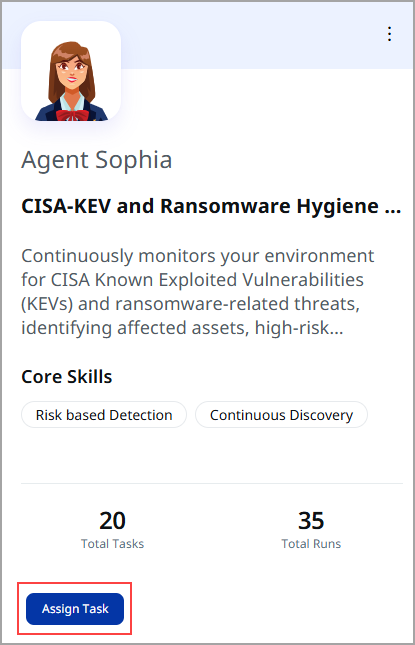
Agent Sophia: CISA-KEV and Ransomware Hygiene Assistant
Agent Sophia prioritizes real-world exploitation risk by focusing on CISA Known Exploited Vulnerabilities (KEVs) and ransomware-related threats. Rather than managing thousands of theoretical vulnerabilities, Sophia concentrates remediation efforts on the specific vulnerabilities attackers are actively exploiting today and the techniques used in ransomware campaigns targeting your industry.
The Problem Sophia Solves
Vulnerability management teams face overwhelming lists of potential issues, many of which represent theoretical risk rather than active threats. Meanwhile, CISA-confirmed actively exploited vulnerabilities demand immediate attention due to federal requirements and real compromise risk. Ransomware campaigns targeting your industry require focused defense.
Agent Sophia filters this noise by isolating the vulnerabilities attackers are exploiting right now.
Key Capabilities of Agent Sophia
Sophia has the following key capabilities:
- Identifies ransomware-related vulnerabilities
Sophia detects vulnerabilities linked to ransomware campaigns, techniques, and exploitation patterns, highlighting threats associated with disruptive attacks. - Maps risks to your environment
The agent correlates CISA KEVs and ransomware vulnerabilities with your specific assets, applications, and services, showing exactly what is exposed and where. - Evaluates internet-facing exposure
Sophia highlights KEV and ransomware risks on externally reachable systems, identifying immediate entry points for attackers and highest-priority targets. - Aligns risk with business criticality
The agent surfaces KEV and ransomware exposure across crown jewels and critical business entities, showing where compromise would have the most significant impact. - Generates urgent remediation actions
Produces exposure summaries, threat-focused prioritization plans, and draft patch jobs focused on the fastest risk reduction. - Enables controlled remediation workflow
Facilitates rapid elimination of KEV and ransomware vulnerabilities through a human-in-the-loop process aligned with enterprise change control.
What You Get
With the help of agent Sophia, you can refined your outputs in the form of:
-
Exposure summaries
Concise snapshots of KEV and ransomware exposure, viewable in-product or sent via email for leadership visibility. -
Prioritization plans
Focused remediation strategies targeting the fastest reduction of real-world exploitation risk. -
Environment Mapping
Correlates KEVs and ransomware-linked vulnerabilities with your assets across hosts, applications, and services. -
Draft Patch Jobs
Prepared patch recommendations scoped to KEV and ransomware findings, always requiring human approval before execution. -
Email Notifications
Automatic updates share exposure summaries and urgency markers, keeping leadership informed.
When to Use Agent Sophia
You can use Sophia to:
- Track and remediate CISA KEVs within mandated remediation timelines to meet federal and compliance requirements
- Evaluate and strengthen organizational ransomware readiness during heightened threat periods or readiness assessments
- Prepare vulnerability assessments for compliance reviews and federal or regulatory audits
- Create executive briefings on active exploitation risk and real-world threats for leadership updates
Best Suited for
Agent Sophia is best suited for the following teams:
- Vulnerability Management teams managing CISA KEV compliance
- Security Operations teams coordinating urgent remediation
- Incident Response teams addressing active threats
- CISOs and risk owners reporting on real-world risk
- Federal organizations meeting federal mandate requirements
- Regulated organizations meeting compliance obligations
Core Strengths of Agent Sophia
Sophia's core strengths are:
- CISA Known Exploited Vulnerability (KEV) Coverage
- Ransomware Risk Hygiene Assessment
- Threat-Informed Prioritization
- Exploit-Driven Risk Reduction
Key Design Principles
All agents share fundamental design principles:
- Human-in-the-Loop Workflow
All agents analyze, prioritize, and prepare recommendations, but they never execute remediation automatically. Every patch job, configuration change, or significant action requires human review and approval, ensuring you maintain complete control and compliance with your change control processes. - Context-Aware Analysis
Each agent understands your business context, industry classification, critical assets, business entities, and asset criticality scores, ensuring recommendations reflect what matters most to your organization. - Integration with Enterprise Processes
The agents are designed to fit within existing security operations workflows, change advisory boards, and compliance processes rather than requiring new operational paradigms. - Actionable Intelligence
Rather than generating overwhelming data, each agent produces focused, actionable intelligence exposure summaries, prioritization plans, draft jobs, and notifications designed for immediate decision making. - Continuous Monitoring and Reporting
Each agent provides automated email notifications and in-product dashboards, enabling continuous visibility without requiring manual checking.
Implementation and Getting Started
Prerequisites
To use agents effectively, ensure the following prerequisites are met:
- Active connectivity to your asset inventory and vulnerability data sources
- Configuration of industry classification, critical assets, and business entities
- Email distribution lists for stakeholder notifications
- Standard change control approval workflows
Activation Steps
Follow these steps to activate and configure your Agentic AI for optimal performance:
- Enable Agentic AI.
Activate through your admin settings - Configure Agent tasks.
Set industry classification and business context for your organization - Schedule Agent Runs.
Establish timing for continuous or periodic agent execution - Review Initial Outputs.
Examine initial agent outputs and adjust configurations as needed - Integrate with Change Control.
Connect agent outputs to your change advisory board and remediation workflows
To know more about Agentic AI, refer to Explore our AI Agents from ETM Online Help.
Introduced Cyber Risk AI Assistant ROCky
With this release, ETM now has ROCky – the Cyber Risk AI Assistant, an intelligent, conversational chatbot designed to help you quickly access insights, explore risks, and make informed security decisions. ROCky provides a guided, intuitive interface that enables users to interact with ETM using natural language, reducing the effort required to analyze risk data and improving day-to-day operational efficiency.
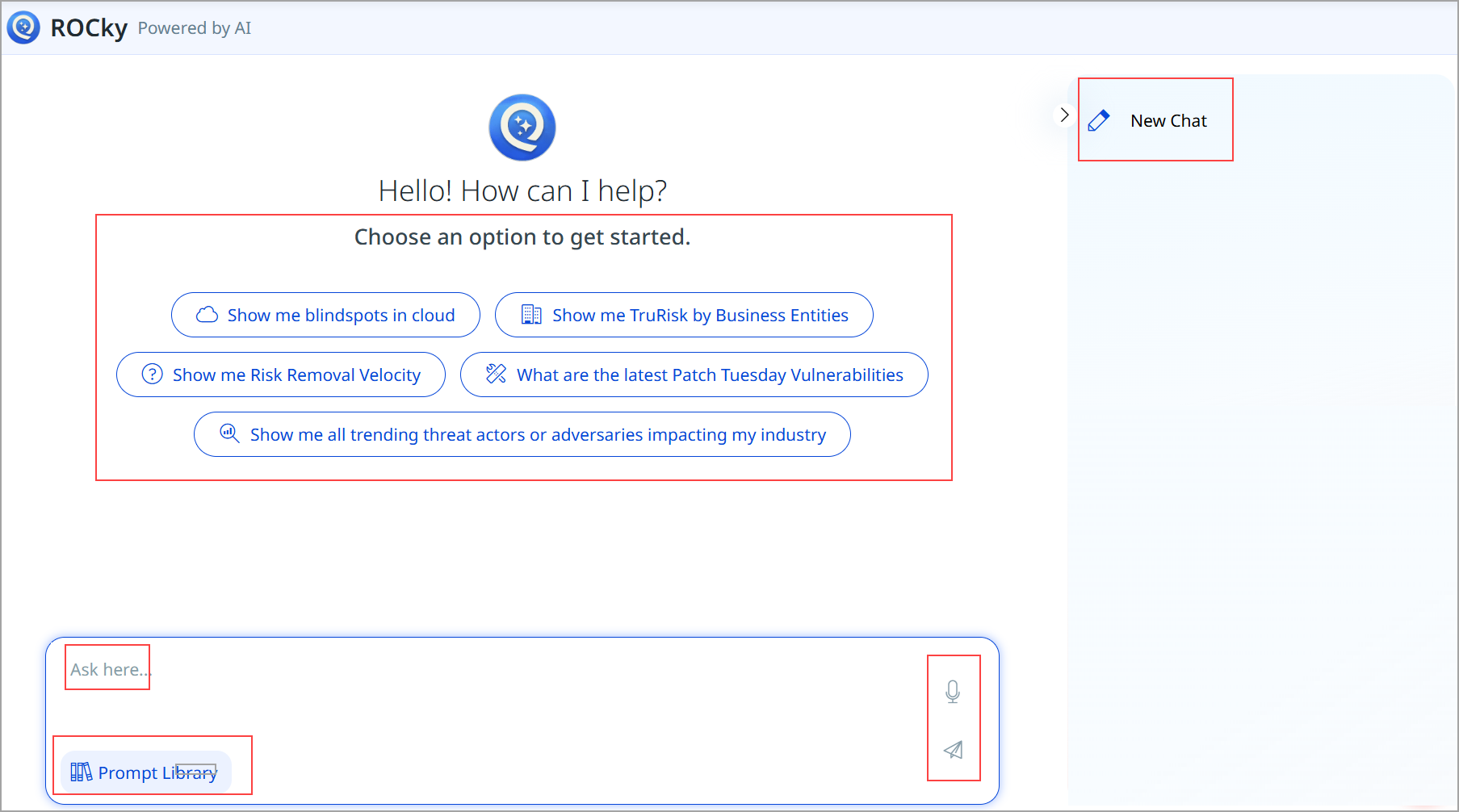
Availability
The AI Chatbot, ROCky, is accessible through the ETM platform. You can interact with your security and risk data using conversational queries in the ETM user interface via ROCky. To enable this feature, connect with Qualys Support or your Technical Account Manager (TAM).
Key Capabilities of ROCky
ROCky has the following key capabilities:
-
Intuitive Chat Interface
ROCky features a user-friendly chat interface that allows you to ask questions, explore insights, and continue conversations from a single screen. The interface is designed for both first-time users and advanced practitioners, enabling quick access to critical ETM information. -
Quick-Start Options
Preconfigured quick-start prompts are available to help you get immediate answers with a single click. These options represent commonly requested queries and are ideal for first-time users or for accessing frequently used insights without typing custom questions. -
Prompt Library for Guided Workflows
The Prompt Library provides categorized, ready-to-use prompts that support standard security and risk management workflows. These guided prompts help you explore ETM capabilities without needing to craft complex queries manually.
Common Workflows Supported
Here is an overview of the common workflows ROCky supports:
- Daily Security Reviews:
Get a high-level summary of findings to assess your security posture. - Risk Remediation Planning:
Identify patchable findings and prioritize remediation efforts. - Business Context Analysis:
Compare risky and best-performing business entities. - Threat Response Preparation:
Explore trending threat actors and adversary techniques mapped to MITRE TTPs. - Asset Inventory Audits:
Review internet-facing assets and cloud blind spots.
Benefits of using ROCky
ROCky plays a vital role by simplifying how users interact with ETM data. By combining conversational AI with guided workflows, the AI chatbot helps teams access insights faster, work more efficiently, and make better-informed security decisions—while lowering the learning curve for new users.
- Faster Insights
Quickly access ETM data and risk insights without navigating complex reports. - Improved Productivity
Reduce time spent crafting queries with guided prompts and natural language interaction. - Better Decision-Making
Gain actionable intelligence across risk, threats, compliance, and assets. - Lower Learning Curve
Enable new users to become productive faster with built-in guidance.
Ask Questions to ROCky in Natural Language
In addition to guided prompts, ROCky allows you to ask custom questions using natural language. You can query vulnerabilities, risks, threats, and trends relevant to your environment and receive contextual responses based on ETM data.
To enter a custom query, you can navigate to the text input field located at the bottom of the ROCky chat window. By typing their question or request in natural language and then pressing Enter or clicking the Send icon, ROCky will process the request and display relevant results.
The New Chat option allows you to start a fresh conversation at any time. This clears the previous context and is useful when switching topics or initiating a new line of analysis.
Sample Queries
- What vulnerabilities affect our database systems?
- Show me risks in our network infrastructure.
- Which threat actors target our industry?
- What is the current threat level?
- Explain the latest security trends.
Issues Addressed
There are no notable customer issues in this release.