Viewing Assets
In the Assets tab, you can view assets for which FIM is both activated and not activated in Cloud Agent.
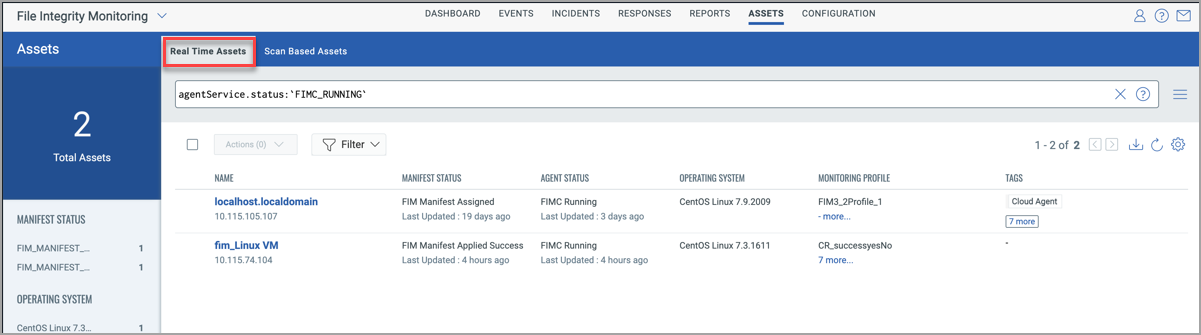
Real-Time Assets
You can assign a monitoring profile to the real-time asset by clicking on the Actions menu.
Filter Assets
You can find assets based on the Operating System, Manifest Status, and Agent Status using the filters in the left pane. The Manifest Status, and Agent Status columns also display the time the status is updated.
The QQL agentService.status is not supported for FIM assets on AIX. Hence, no data is fetched for AIX assets if you use this QQL, and the Agent Status column does not display any data.
Manifest Status
As part of agent-status-core, the user gets to know if the agent has downloaded the manifest.
Only after the Agent further applies the downloaded manifest, it come into effect.
After downloading the manifest, two additional manifest statuses are displayed for Windows Agent:
- FIM_MANIFEST_APPLIED_SUCCESS
- FIM_MANIFEST_APPLICATION_FAILED
Important: The following manifest statuses are not supported for AIX assets:
- FIM_MANIFEST_APPLICATION_FAILED :
- FIM_MANIFEST_APPLIED_SUCCESS
- FIM_MANIFEST_ASSIGNED :
- FIM_MANIFEST_ASSIGNMENT_FAILED
Following are the meanings of manifest statuses:
- FIM_MANIFEST_APPLIED_SUCCESS: Depicts that the manifest is applied successfully at the agent.
- FIM_MANIFEST_APPLICATION_FAILED: Depicts that there was some failure at agent while applying the manifest.
- FIM_MANIFEST_ASSIGNED: Depicts that the manifest is downloaded at the agent.
- FIM_MANIFEST_ASSIGNMENT_FAILED: Depicts some failure at the agent during manifest download.
- NO_FIM_MONITORING_PROFLIE_FOUND: After agent activation, this status depicts that the asset doesn't have any active FIM monitoring profiles assigned to it.
- FIM_ACTIVATION_REQUEST_REQUIRED: After activating the agent for FIM on CAUI, this status depicts that FIM server has received the request for activation.
- FIM_MANIFEST_PUBLISHED: Depicts that FIM manifest has been sent from FIM server.
- FIM_MANIFEST_Decommissioned: Depicts that Manifest gets decommissioned/removed from the agent in case the last profile for the asset is deactivated or removed.
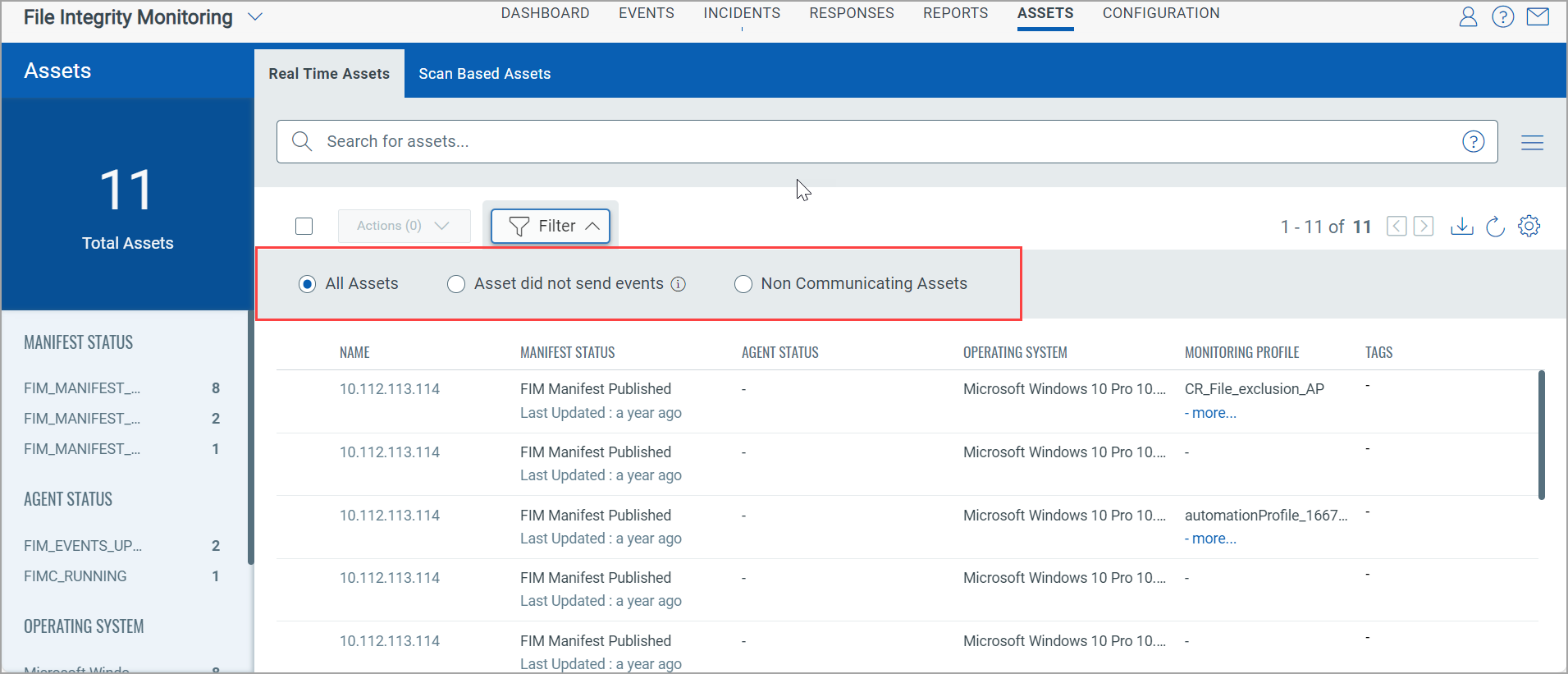
Filter
With Filter, you can find assets in three different categories. Following are the three filters.
|
Filter |
Description |
|---|---|
|
All Assets
|
All Assets shows the list of all assets. |
|
Assets that did not send Events
|
Select the Assets that did not send Events option and select the required duration in hours or days. You can enter theduration upto seven days or 168 hours. You can also filter the assets using tokens. For more information on tokens, see Asset Tokens. |
|
Non-communicating Assets
|
The non-communicating assets enable you to view the list of assets that are non-responsive. These are the assets that have not communicated with the Qualys platform in seven days or more. These assets are highlighted with a tool-tip message and a warning icon. Note: We have an out-of-the-box dashboard widget template for non-communicating assets. You can customize the widget for non-communicating assets based on your requirements. You can add the widgets to the dashboard to get a unified look of the non-communicating assets. |
See also: Search Tutorial | Downloading Asset Details
Related Topics