Release 3.4
March 06, 2025
What's New?
New Application - TruRisk Eliminate
With this release, we introduced a new application, TruRisk Eliminate, which includes Patch Management, Mitigation, and Isolation support.
Not all vulnerabilities can be remediated with a patch, as configuration changes are needed in addition to patching many times. With Qualys TruRisk Eliminate, these requirements are taken care of. Also, you can mitigate zero-day vulnerabilities. Another significant benefit is you are no longer required to be concerned about downtime or outages.
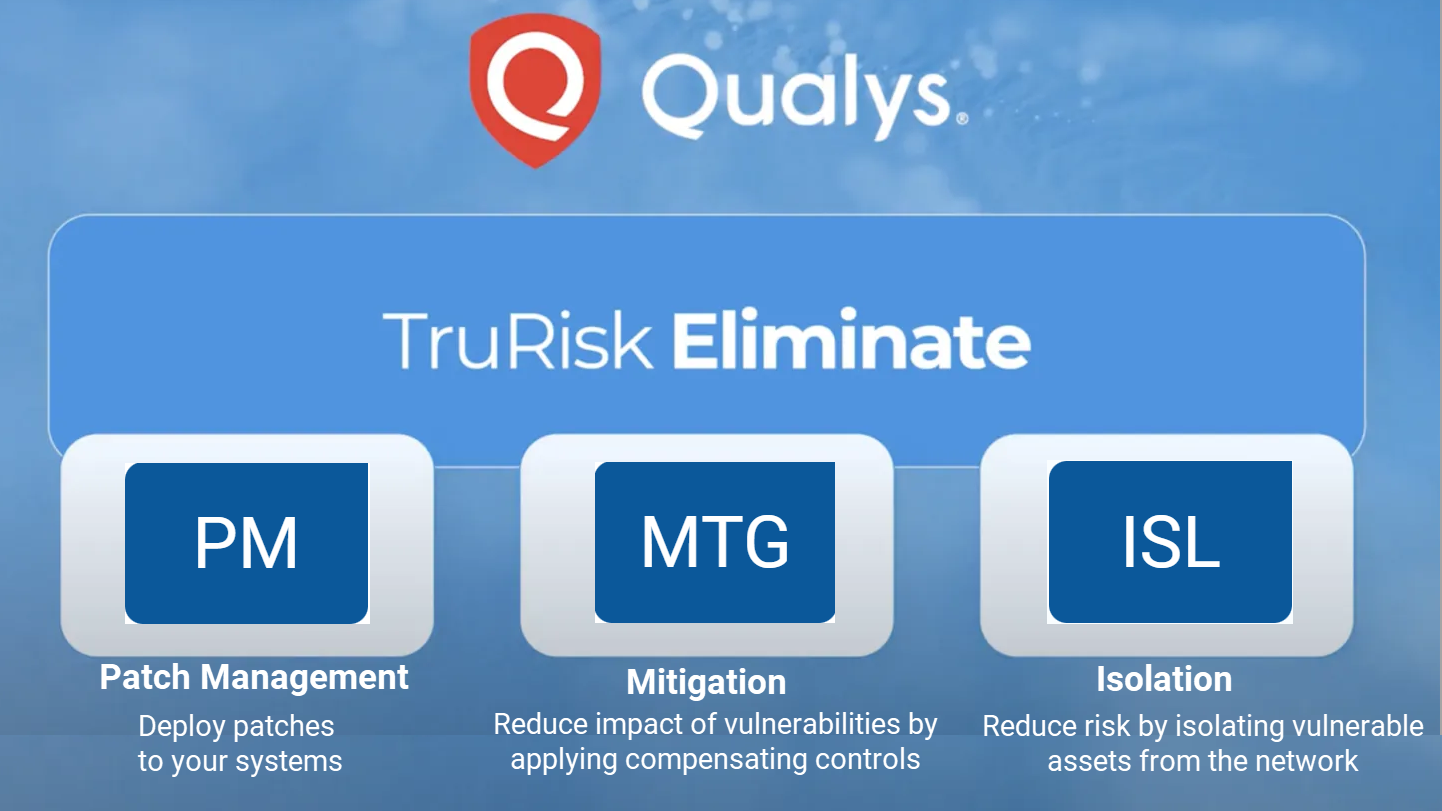
- Qualys TruRisk Eliminate expands the Patch Management solution to enable you to use the same Qualys Cloud Agent (CA), Platform, and Workflows to deploy patches and address vulnerabilities.
- You can mitigate or remediate the vulnerabilities until the patch is available and fix the vulnerabilities when the patch is available by deploying the patch jobs.
- You can use the same CA to isolate or quarantine your potentially dangerous Windows and Linux assets from causing any damage to other assets in the network. You can isolate such assets by creating and running the Isolation jobs. For more information, refer to the Online Help.
TruRisk Eliminate Capabilities
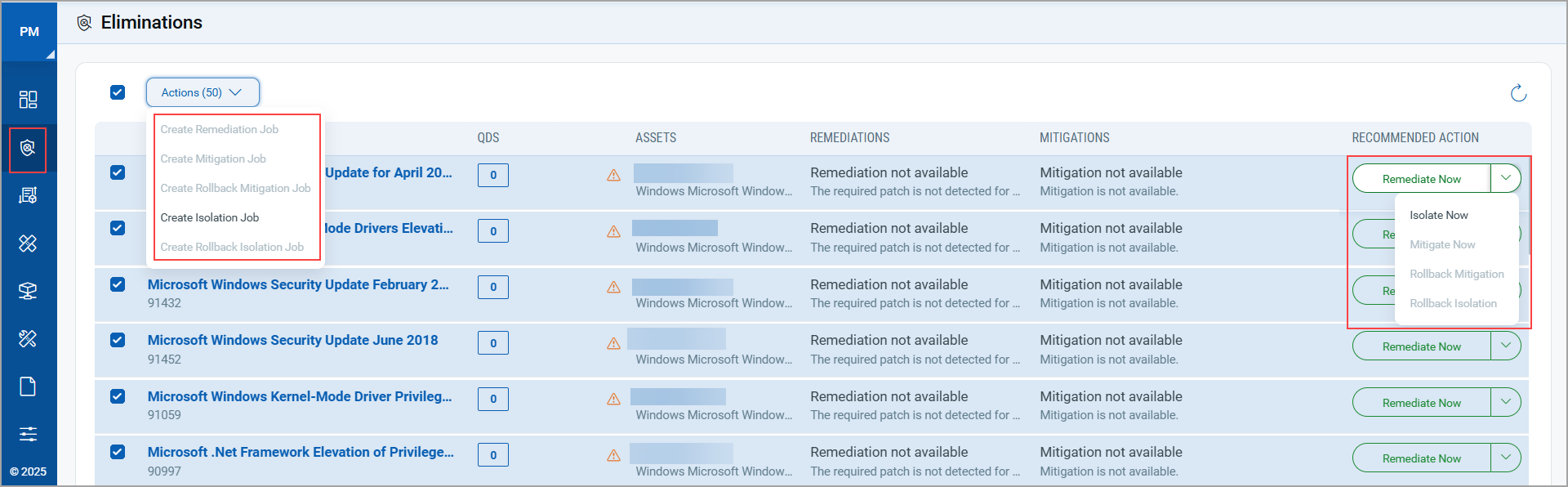
You can create the following types of jobs to meet your needs:
- Create Remediation Job: You can remediate vulnerabilities found on Windows assets by deploying a job that includes missing patches and configuration scripts.
- Create Mitigation Job: You can apply the script-based mitigation to your Windows or Linux assets as a temporary fix to address the vulnerabilities.
- Create Rollback Mitigation Job: You can roll back the script-based mitigation applied to your Windows or Linux assets as a temporary fix to address the vulnerabilities.
- Create Isolation Job: You can isolate or quarantine your potentially dangerous Windows and Linux assets from causing any damage to other assets in the network.
- Create Rollback Isolation Job: You can bring the isolated or quarantined asset back to your network after the vulnerabilities are addressed.
Prerequisites
- Windows Cloud Agent version 6.1.1 or later
- Linux Cloud Agent version 7.1.1 or later
Although TruRisk Eliminate includes Patch Management, Mitigation, and Isolation, availing of the license (Trial or Full) and activating assets for each is also a prerequisite. For more information, Contact your Technical Account Manager (TAM).
New and Updated QQL Tokens
Refer to the following table to learn more about the new and updated tokens in this release.
| Tab | Token | Usage |
|
Windows > Assets Linux > Assets |
isIsolated (New) |
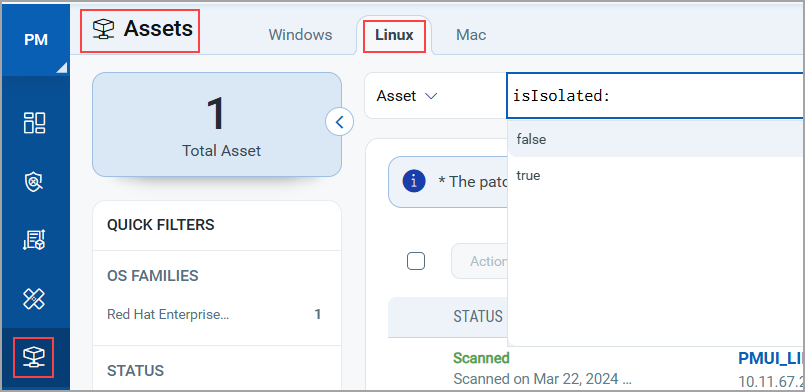
To find assets that are isolated from your network. The supported values are true and false QQL Token Screenshot: Assets > Linux tab
|
|
Assets
|
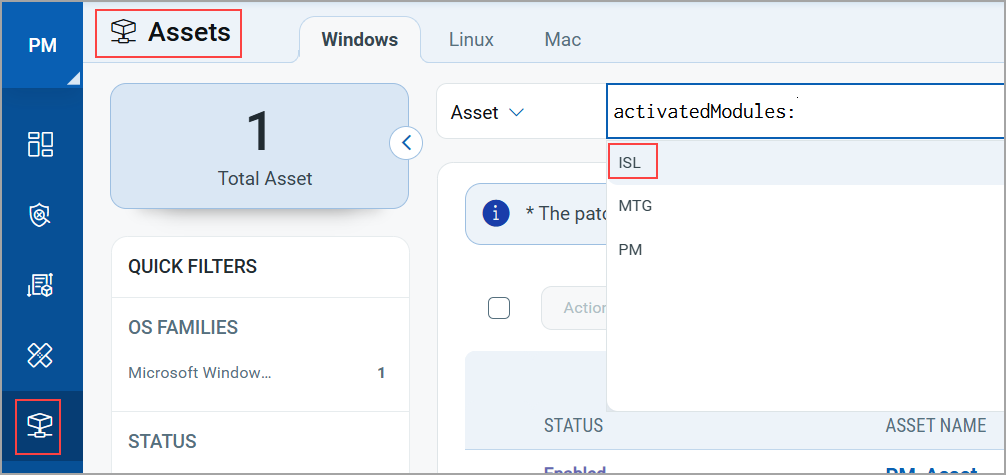
activatedModules (Updated) |
To find assets that are activated for Patch Management, Mitigation, or Isolation application.
QQL Token screenshot: Assets > Windows tab
|
Issues Addressed
The following reported and notable customer issues have been fixed in this release.
| Component/Category | Description |
|
PM - Licensing |
We fixed the issue observed for a customer, wherein the customer could see irrelevant or excess logs under the Activity Logs in the Administration utility. |
|
PM - Job Windows |
An incorrect message about the pre-action execution being successful without a system reboot was shown, though the system reboot took place. This issue is fixed now, and the correct message indicates that the pre-action execution is successful with a system reboot. |
|
PM - Job Windows |
We fixed the issue with the QQL-based scheduled patch job, in which the patches and asset count were visible in the preview but not in the job details. |
|
PM - Job Linux |
We fixed the issue where the Linux Patch Job was not sent to the targeted assets. |