Release 3.17.1
April 16, 2024 (Updated on May 24, 2024)
What's New?
Administration |
Permission Enhancements in Cloud Security Platform Applications
We have enhanced the Cloud Security Platform Applications permissions as follows:
- Only a Manager user role in the VM/VMDR application can be the super-user for all the Cloud Security Platform applications such as AV, WAS, WAF, MDS, CA, SAQ, and CM.
- To convert a non-manager user to a super user in the Cloud Security Platform applications, you must modify the permissions to Manager from the VM/VMDR application. This change will automatically modify the Cloud Security Platform application's permissions.
- If Cloud Security Platform application users do not have consistent permissions or roles, it must be modified from the VM/VMDR application.
For more information about Assigned User Roles in the Administration application, refer to Administration Online Help.
Cloud Agent |
Updated Maximum Scan Delay and Scan Randomize Interval
With this release, you can delay the first Cloud Agent scan or interval scan up to 24 hours. The maximum value of the Scan Delay and Scan Randomize is updated to 1440 minutes from 720 minutes. The change is also applicable to the VM and PC interval scans.
Currently, the Cloud Agent performs the first scan between 0 to 720 minutes after the Cloud Agent is installed. An increase in the Scan Delay value helps eliminate temporary and short-lived cloud instances created and deployed throughout the day from the scan.
This feature will be available only when the Windows and Linux Agent binaries with delay interval scan support are available. For supported agent versions, refer to the Features by Agent Version section in the Cloud Agent Platform Availability Matrix.
To define or update the Scan Delay and Scan Randomize values, navigate to the VM Scan Interval and PC Scan Interval tabs in the Configuration Profile.
For example, updating VM Scan interval:
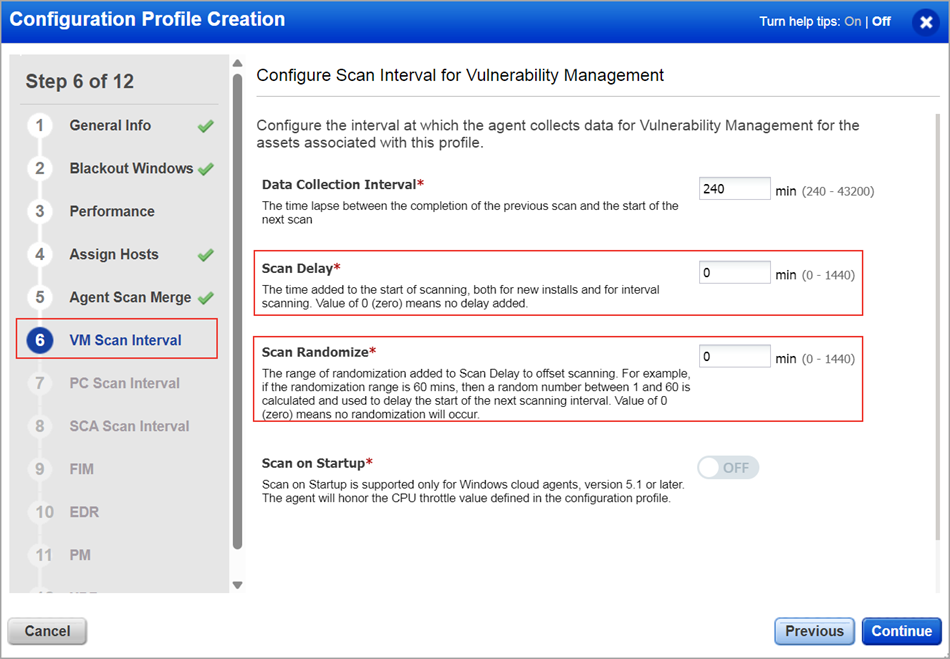
You can configure the new Scan Delay and Scan Randomize values for the existing profiles or a new profile with the require Cloud Agent versions.
Vulnerability Detection and Response |
Introduced EPSS Score in QDS
The Exploit Prediction Scoring System (EPSS) is the newly added attribute in the QDS Technical Attributes factors. EPSS is one of the supporting factors that enhances the prioritization of the vulnerability and its remediation efforts. It provides the probability of a vulnerability that can be exploited over the next 30 days.
The EPSS score will only be available for the QIDs with a CVE.
The following screenshot of the Vulnerability Details displays EPSS Score in the QDS Details section:

For more information about other fields and sections in the Vulnerability Details, refer to VMDR Online Help.
Display Result as Tags for Table Widget
We have added Tags as the new option to display results for the Table Widget. This option helps generate your query results based on Tags. You can use this option to generate collated data for Asset Count, TruRisk Score, and Vuln Count. To access this option, you must have Add Tag or Remove Tag permissions enabled from the Administration application.
The following screenshot is an example of the Display results as Tags option that displays the Asset Count and TruRisk Score data for the Tags attached to the Windows asset:
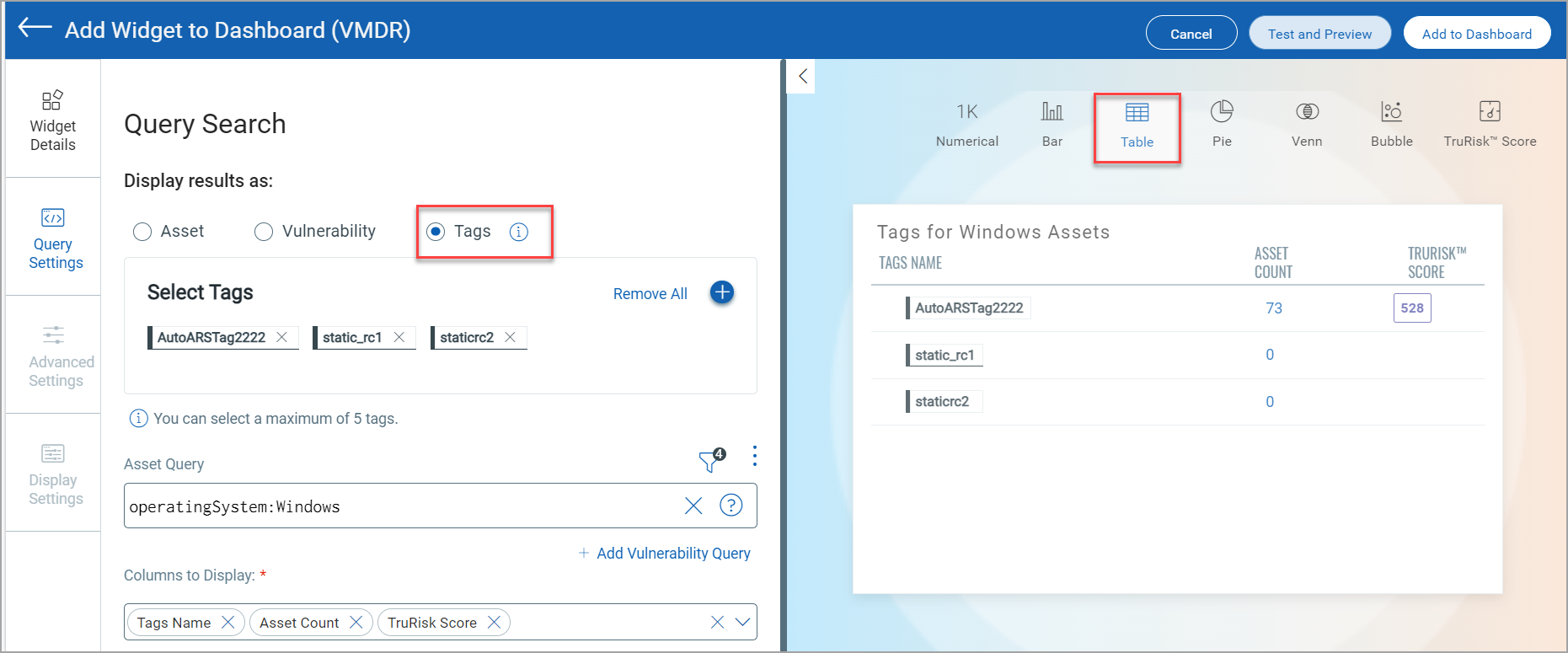
For more information about Tags in Table widget, refer to Unified Dashboard Online Help.
Introduced Vulnerability Detection Searches and Dynamic Tags
Vulnerabilities tagging provides a flexible and scalable way to manage various workflows. You can create tags based on the scope, available remediation, actionable activity, or pending remediation. Dynamic Tag allows you to define Tag Rules. You can now apply dynamic tags using the Add Tags option in the Actions drop-down menu of the Vulnerabilities tab. The following screenshot displays the Add Tag option:
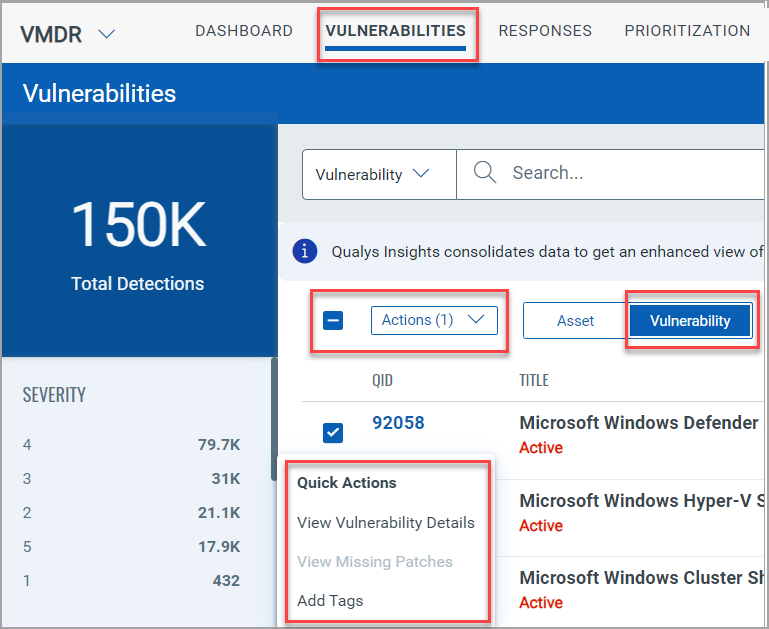
To apply any asset tag rules, you need to have a VMDR (Trial/Purchase) + GAV/CSAM (Trial/Full) and Non-VMDR/VM + CSAM (Trial/Full) subscription. This requirement does not apply to the Vulnerability Detection Searches type of Tag Rule.
For information about steps to add tags, refer to VMDR Online Help.
New Tokens
| Token Name | Description |
| vulnerabilities.riskFactor.cisaKnownExploits | This token lists the QIDs that are impacted by CISA Known Exploits. |
| vulnerabilities.riskFactor.threatActorName | Use this token to identify the QIDsLabyrinth Chollima. |
| vulnerabilities.riskFactor.malwareName | This token lists the QIDs that are impacted by the malware. |
| vulnerabilities.riskFactor.exploitCodeMaturity | This token lists the QIDs that can be exploited based on the existing state of exploit techniques and code availability. |
| vulnerabilities.riskFactor.trending | Use this token to get the list of QIDs trending within a specific date range. You can select the date range from the drop-down menu. |
| vulnerabilities.tags.name | Use this token to help you find the vulnerabilities tag. |
For more information about the Vulnerabilities token, refer to VMDR Online Help.
Issues Addressed
The following reported and notable issues have been fixed with this release.
| Category/Component | Application | Description |
| CA-UI | Cloud Agent UI | Fixed an issue where customers could not download a complete list of Cloud Agents from Cloud Agent UI. |
| CA-UI | Cloud Agent UI | Fixed an issue where performance setting values for a configuration profile failed to match the standard performance level settings. |
| Portal-Administration UI | Administration | We fixed an issue where an Admin Role Management user could not get the list of all users assigned to a scanner role. |
| Portal API | GAV/CSAM | With this release, the issue of degraded API performance is fixed by clearing the Indexing Flow. |
| VM-Assets | Vulnerability Detection and Response | This release fixed an issue where the customer got an error while launching a scan for tagged assets, as the Asset Group tags were not applied to the scanners added to the asset group. |
| AM&T API | Vulnerability Detection and Response | This release fixed an issue where the Administration UI and search API response had discrepancies in user details as deleted user details were displayed by API when the user tried to search with the user name. |
| Shared-Portal | Administration | We have updated the Activity Logs error messages to remove occurrences of unwanted characters. |
| VM - Scan Schedule | GAV/CSAM | We fixed an issue where the customer saw 'null' in the OS field of the Asset Summary after running a scheduled scan. |
| ATS, Shared Portal | GAV/CSAM | We fixed an issue where changes to the tag tree structure resulted in the tag rule of a tagset not getting updated. This led to missing asset data. The complete list of assets was not identified unless the customer performed a manual reevaluation after changing the tag structure. |
| CSAM+GAV-UI, Shared - Portal | GAV/CSAM | We fixed an issue where applying tags to many assets had a long response time or resulted in errors. |
| CSAM +GAV-UI | GAV/CSAM | With this release, we fixed an issue where users with Scanner Roles could not create asset tags by enhancing the "Modify Dynamic Rule" permissions. |