TotalAppSec Release 2.4 | Web Application Scanning Release 1.24
November 14, 2025
 TotalAppSec
TotalAppSec
Enhanced Discovery of Web Applications and APIs through Scans
We have enhanced TotalAppSec capabilities to discover potential web applications and APIs within existing web assets through the discovery and vulnerability scans.
This enhancement broadens your security coverage by discovering potential web applications and APIs, adding them to your subscription, and scanning them for vulnerabilities.
Potential APIs Discovery
The discovery and vulnerability scan discovers potential APIs based on the links crawled and XHR requests from the existing web assets in your subscription.
The discovered potential APIs are displayed in the Discovery > Discovered APIs page.
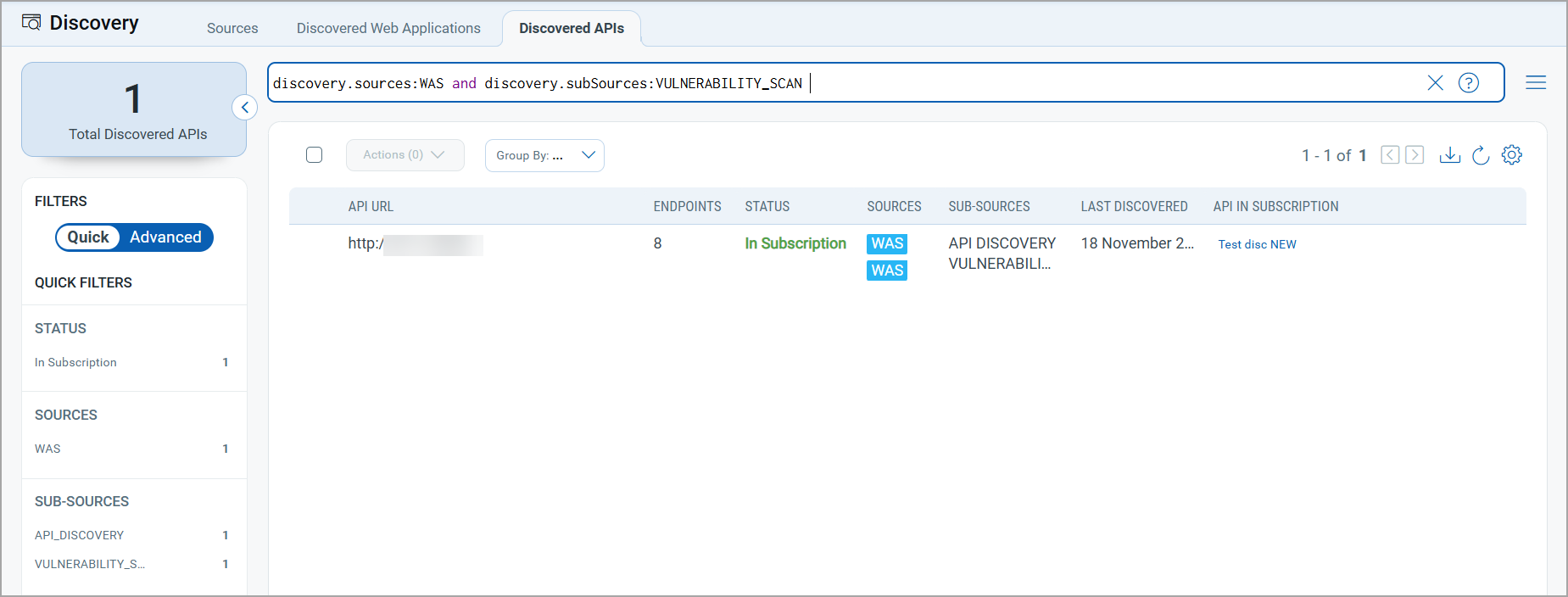
You can add these discovered APIs to subscriptions from the Quick Actions menu and launch vulnerability, compliance, or discovery scans.
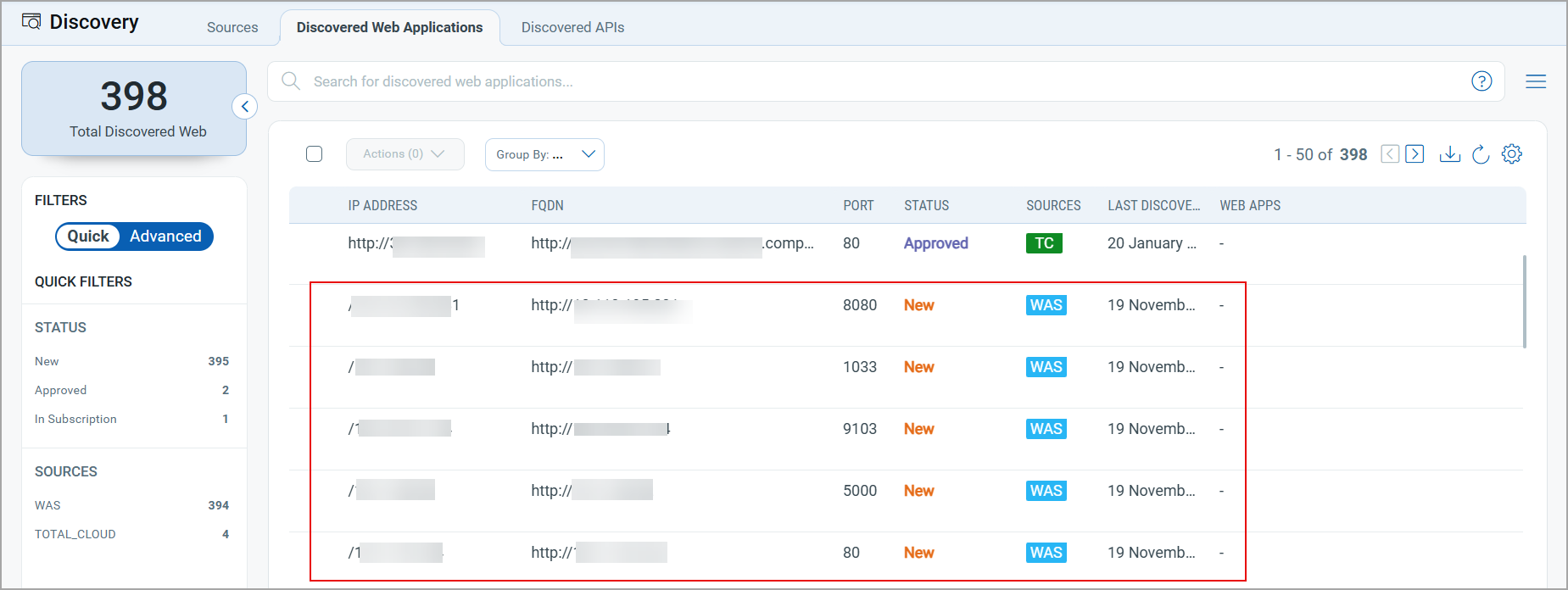
Potential Web Applications Discovery
When a vulnerability scan runs on a web asset in your subscription, it will now discover the potential web applications available in the web asset.
The potential web applications are displayed in the Discovery > Discovered Web Applications page.
The Discovered Web Applications tab displays the number of web applications with the Source as WAS and the Sub-Source as API DISCOVERY WAS SCAN.
End-to-End Logging for Connector Activities
With this release, we have introduced end-to-end logging for connector activities. You can now view these comprehensive logs directly on the Connector screen in the Logs tab.
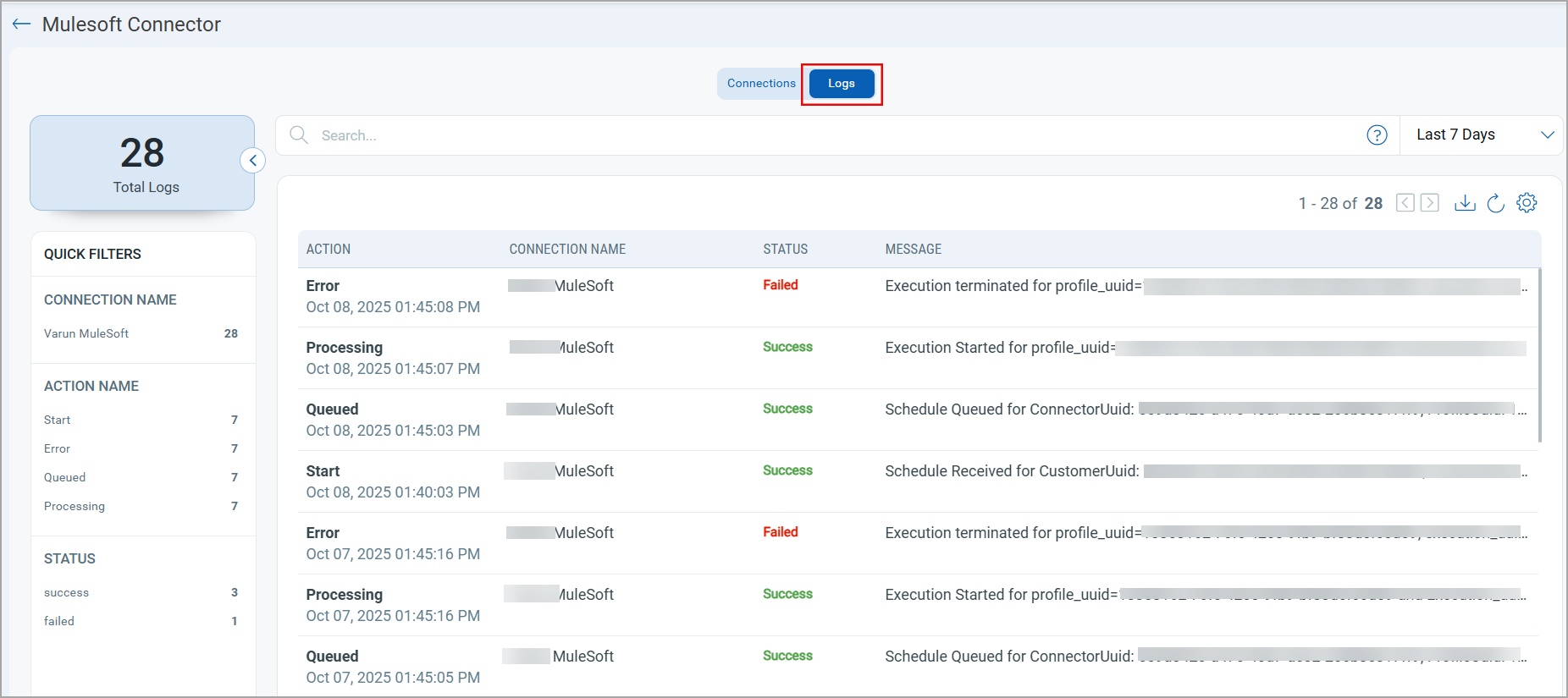
These enhanced logs offer greater insight into connector operations, enabling more advanced analysis and effective troubleshooting.

 TotalAppSec and Web Application Scanning
TotalAppSec and Web Application Scanning
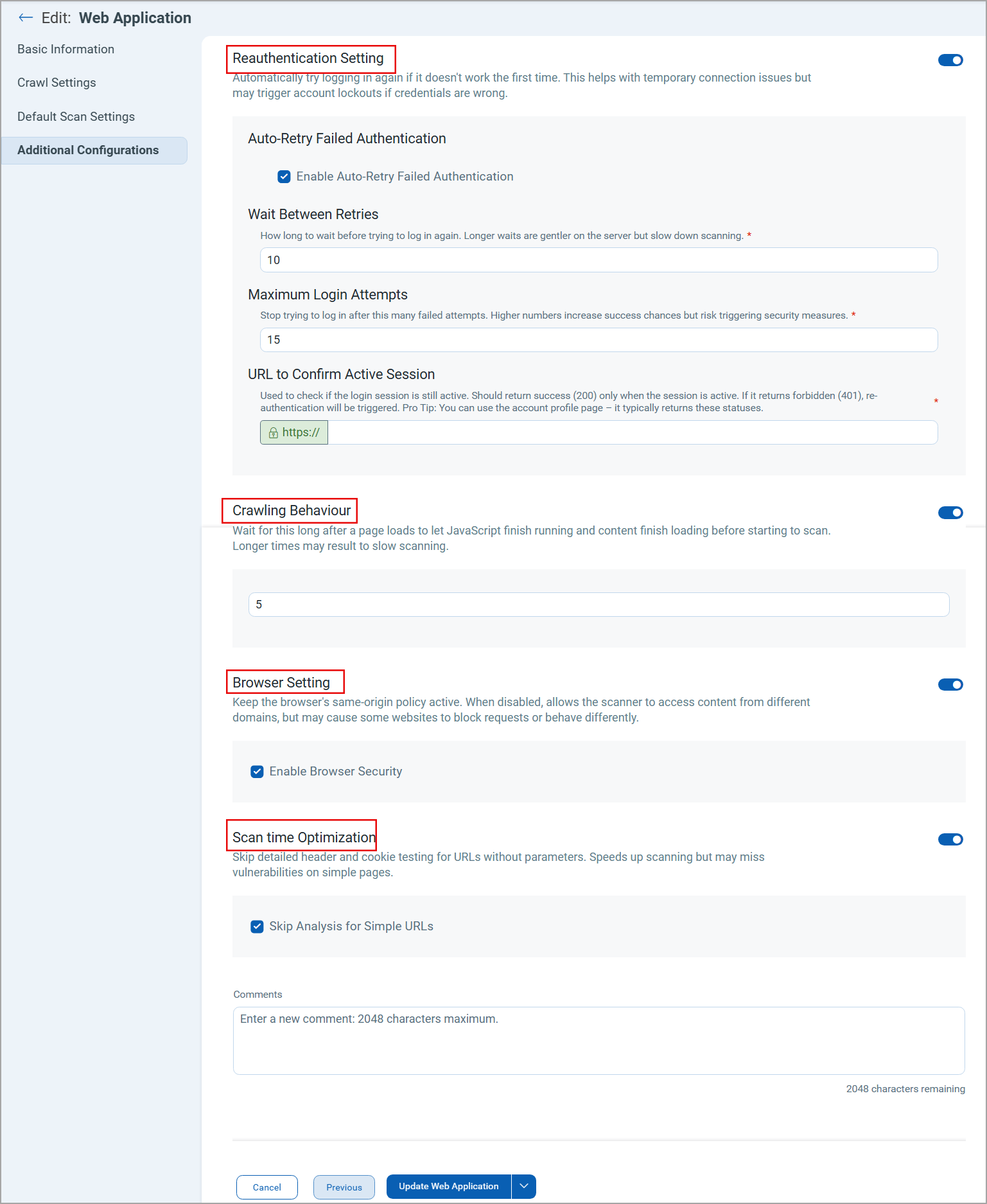
New Scan Settings in the Additional Configurations for Web Application
You can now define key scan parameters directly from the user interface using the new options available in the Additional Configurations section of the create and edit Web Application workflow.
Earlier, these settings were managed through backend settings. This enhancement provides greater flexibility and control while ensuring that default values and safeguards are maintained for optimal scanning performance.
The following settings are now available under Additional Configurations:
- Reauthentication Setting: Defines automatic login attempts in case of authentication failure. This helps with temporary connection issues but may trigger account lockouts if credentials are wrong.
- Auto-Retry Failed Authentication: Enables automatic retry after the failed authentication attempts during scanning.
- Wait Between Retries: Specifies the duration for which the system should wait before retrying the authentication.
- Maximum Login Attempts: Specifies maximum number of times the system attempts to connect to the authentication server.
- URL to Confirm Active Session: Specifies the URL to verify whether the login session with the authentication server is active.
- Crawling Behavior: Specifies the duration for which the system waits before start of scanning after the page loads.
- Browser Setting: Enables or disables the same-origin policy to control content access across domains.
- Scan Time Optimization: Enables scan time optimization by skipping detailed header and cookie testing for URLs without parameters.
Addition of Debug Scan Option
We have introduced the Debug Scan checkbox under the Scan Settings page in the create and edit vulnerability scan workflow. To troubleshoot scan issues, you can now select the Debug Scan option to collect detailed scan logs.
To enable the Debug Scan mode, navigate to Launch New Scan > Vulnerability > Scan Settings.
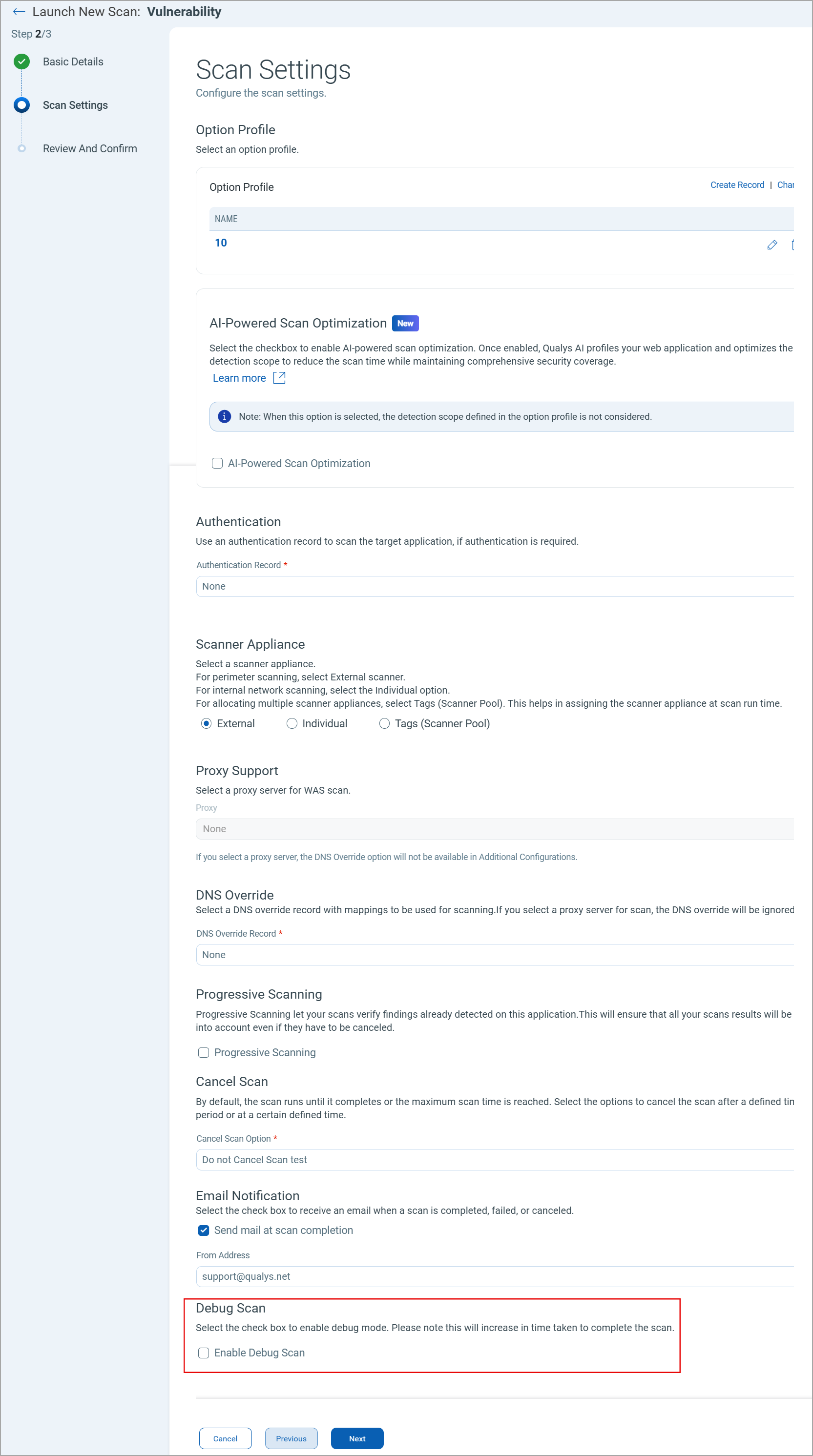
The Debug Scan option is only available when launching a vulnerability scan.
Issues Addressed
| Application | Category/Component | Description |
|---|---|---|
|
TAS |
API Discovery Scan |
We fixed an issue where the user encountered an error while launching an API discovery scan on any web application. |
|
TAS |
Azure API Connector Configuration |
We fixed multiple issues with the Azure API Connector configuration. The following changes are made:
|
|
TAS and WAS |
Scans, user roles, and permissions |
An issue was observed where a sub-user could see the scan results for the assets that were out of scope. It was identified that this case was observed for the user with the Auditor role. The issue is fixed. |
|
TAS and WAS |
Authentication Configuration |
We fixed an issue where authenticated scans were performed on the assets in WAS, even when the authentication was disabled in the Web Malware Detection (MDS). |
|
TAS and WAS |
Proxy Configuration |
We fixed an issue where users were entering invalid FQDNs or IP addresses in the Proxy Exception field on the Proxies tab. |
|
TAS and WAS |
Certificate authentication |
We fixed an issue where users encountered an error while uploading a certificate for authentication under Authentication Record > Server Record > Upload Certificate. |
|
TAS and WAS |
Web Application Configuration |
An issue was observed where the user disabled the Set up Exclusion Lists option in the Web Application > Additional Configurations. When an allow list is available in the Global Settings, the change is not saved. The Set up Exclusion Lists option is enabled automatically. The issue is fixed. |
|
TAS and WAS |
Scheduled scan |
We fixed an issue where scan schedules in daylight saving time zones were shifted by one hour. The time zone offset now automatically adjusts to account for daylight saving time. |
|
TAS and WAS |
Scan schedules with tags |
We fixed an issue where schedule scans created with tags in the Web Applications and APIs tabs were not displayed in the Application Details > Schedules section. |
|
TAS and WAS |
Scheduled Scans |
We fixed an issue where scheduled scans were being canceled automatically without displaying any error message. |
|
TAS and WAS |
Scheduled and On-demand scans |
We fixed an issue where there was a discrepancy in the vulnerabilities and links crawled during the on-demand scans and scheduled scans. |
|
TAS and WAS |
Detections |
We fixed an issue where users could not view scan findings and observed a mismatch in scan dates. |