Release 2.12
October 21, 2024
What’s New?
TotalCloud 2.12.0 brings updates to the cloud inventory.
Amazon Web Service
Added New Resources to the Cloud Inventory
With this release, we have included support for new resources on the AWS Inventory. The cloud inventory ensures these new resources are assessed against the best global compliance standards supported by Qualys, such as NIST, PCI DSS, HIPAA, GDPR, etc.
New Resources Introduced
The following are the newly introduced resources in the TotalCloud app.
-
Route53 Hosted Zones
-
Route53 Domains
-
Redshift
Microsoft Azure
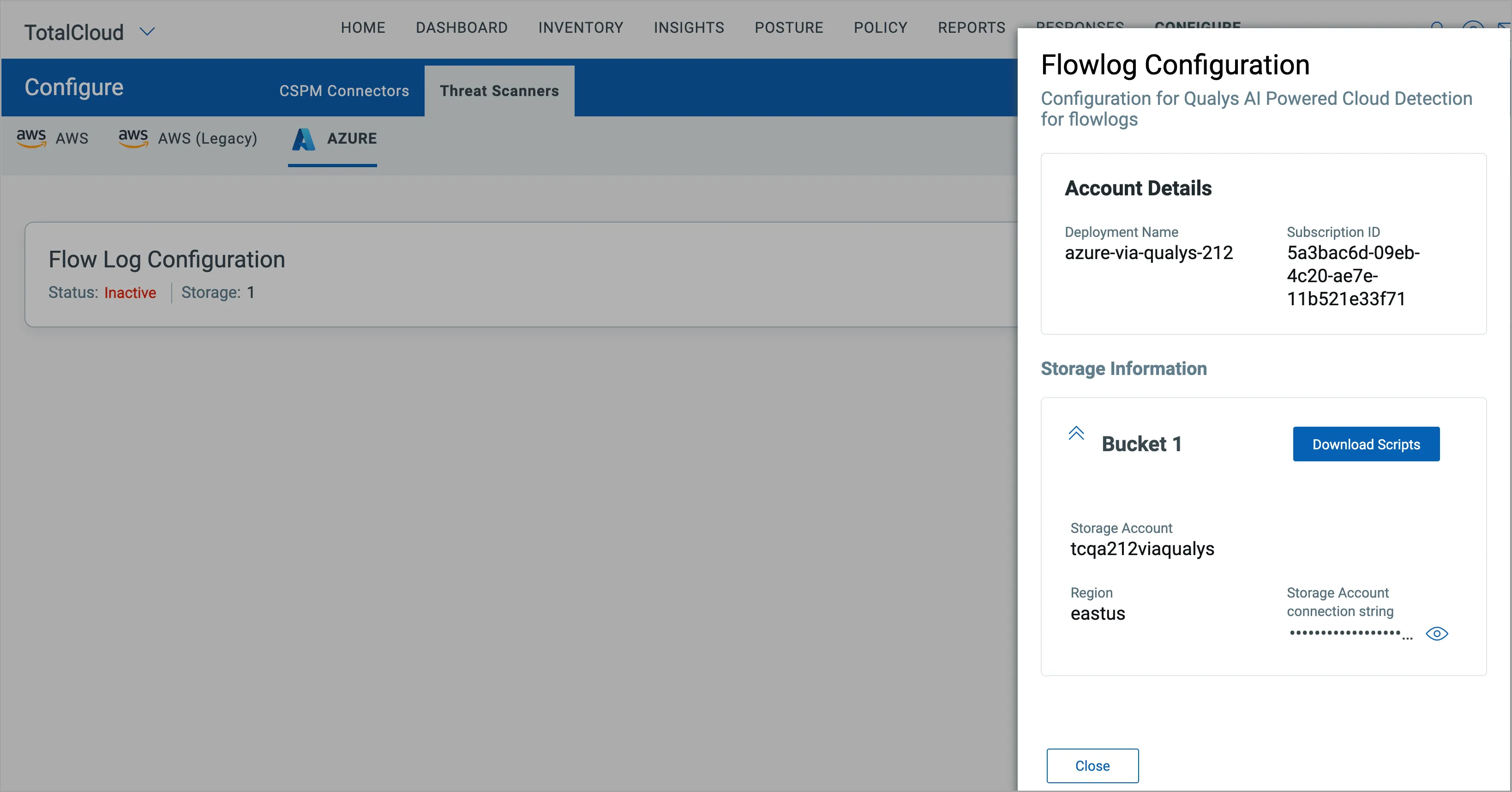
Enhanced Deployment Script for Azure Cloud Findings
With this release, we have enhanced the behavior of CDR findings for Azure flow logs. You can now configure Azure NSG flow log findings with the new deployment scripts on the Azure tab on the Threat Scanner page. The tab helps create configurations with information about the storage where you have decided to collect the NSG flow logs.
To configure the Azure NSG Flow Logs,
- Navigate to Threat Scanners > Azure.
- Create a Deployment.
- View your deployment and Download the Script.
For FedRAMP customers, the updated scripts deploy functions in customer subscriptions to connect to Qualys FedRAMP Cloud.
Google Cloud Platform
Added New Resources to the Cloud Inventory
With this release, we have included support for new resources on the GCP Inventory. The cloud inventory ensures these new resources are assessed against the best global compliance standards supported by Qualys, such as NIST, PCI DSS, HIPAA, GDPR, etc.
New Resources Introduced
The following are the newly introduced resources in the TotalCloud app.
- Cloud Load Balancing
- Cloud CDN
Oracle Cloud Infrastructure
Added New Resources to the Cloud Inventory
With this release, we have included support for a new resource on the OCI Inventory. The cloud inventory ensures these new resources are assessed against the best global compliance standards supported by Qualys, such as NIST, PCI DSS, HIPAA, GDPR, etc.
New Resource Introduced
The following is the newly introduced resource in the TotalCloud app.
Load Balancer
Common Features
Added Support for QQL Search Bar in CDR Tab
With this release, we have added support for a QQL search bar under the CDR tab of your AWS Instances and Azure VMs. You can search for specific findings using the available Qualys Query Language token and narrow down the list of threats you want to view. You can apply the filter to look at the findings that occurred in the last 24 hours to 30 days.
To find the search bar, navigate to TotalCloud > Inventory > Amazon Web Services/Microsoft Azure
Select Instances/Virtual Machines as the resource type and click any asset.
Navigate to the Cloud Detection and Response tab to view the QQL search bar.
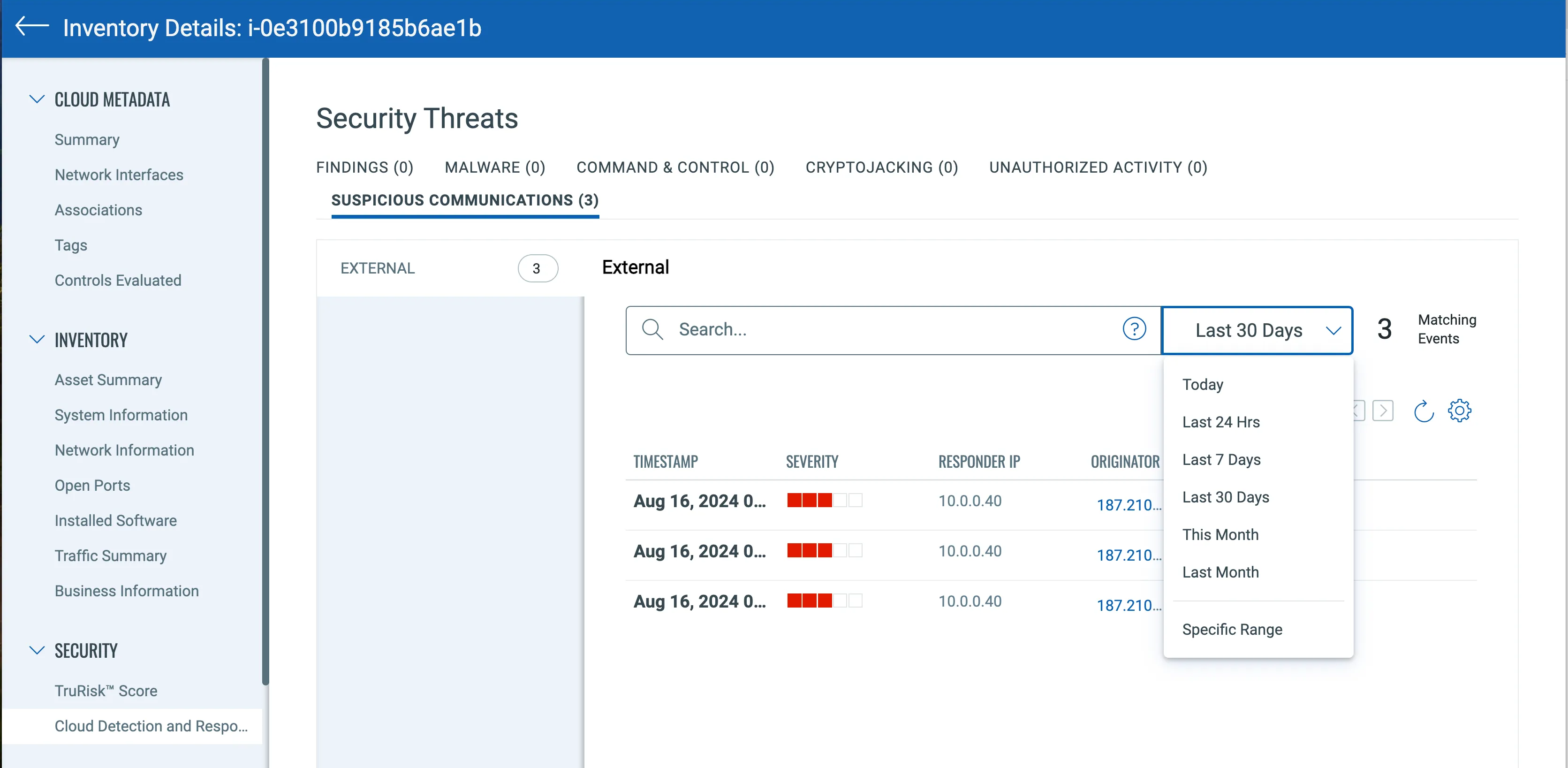
New Tokens
With this release, we have introduced support for new tokens.
AWS Resource Tokens
Route53 Hosted Zones
Tokens introduced in the Route53 Hosted Zones resource.
|
Name |
Description |
Example |
|---|---|---|
|
name |
Find Route 53 resources with the specified hosted zone name. | name: example.com |
|
route53.hostedZone.recordname |
Find Route 53 hosted zones with the specified record name. | route53.hostedZone.recordname: www.example.com |
|
route53.hostedZone.isPrivateZone |
Find Route 53 hosted zones based on whether they are private or public | route53.hostedZone.isPrivateZone: true |
| route53.hostedZone.arn | Find Route 53 hosted zones with the specified Amazon Resource Name (ARN) | route53.hostedZone.arn: arn:aws:route53:::hostedzone/Z1PA6795UKMFR9 |
Route53 Domains
Tokens introduced in the Route53 Domains resource.
|
Name |
Description |
Example |
|---|---|---|
|
name |
Find Route 53 resources with the specified Route 53 Domain name. | name: example.com |
| route53.domain.autorenew | Find Route 53 domains based on their auto-renewal status. | route53.domain.autorenew: true |
Redshift
Tokens introduced in the Redshift resource.
|
Name |
Description |
Example |
|---|---|---|
| redshift.clusteridentifier | Find Redshift clusters with the specified cluster identifier. | redshift.clusteridentifier: my-redshift-cluster |
| redshift.clusterstatus | Find Redshift clusters with the specified status (e.g., available, creating, deleting, final-snapshot, modifying, rebooting, renaming, resizing). | redshift.clusterstatus: available |
| redshift.clusternamespacearn | Find Redshift clusters with the specified namespace ARN. | redshift.clusternamespacearn: arn:aws:redshift:us-west-2:123456789012:namespace:my-namespace |
| redshift.kmskeyid | Find Redshift clusters using the specified KMS (Key Management Service) key ID for encryption. | redshift.kmskeyid: 1234abcd-12ab-34cd-56ef-1234567890ab |
GCP Resource Tokens
Cloud Load Balancing
Tokens introduced in the Cloud Load Balancing resource.
|
Name |
Description |
Example |
|---|---|---|
|
name |
Find load balancers with the specified name. | name: web-lb |
| region | Find load balancers in the specified region. | region: us-west-2 |
| loadBalancing.IpAddress | Find load balancers associated with the specified IP address. | loadBalancing.IpAddress: 203.0.113.1 |
| loadBalancing.scheme | Find load balancers with the specified scheme (INTERNAL, EXTERNAL, INTERNAL_MANAGED,INTERNAL_SELF_MANAGED, EXTERNAL_MANAGED). | loadBalancing.scheme: INTERNAL |
| loadBalancing.forwardingRuleTarget | Find load balancers with the specified forwarding rule target. This could be an instance group, IP address, or another resource. | loadBalancing.forwardingRuleTarget: projects/my-project/regions/us-central1/instanceGroups/my-instance-group |
Cloud CDN
Tokens introduced in the Cloud CDN resource.
|
Name |
Description |
Example |
|---|---|---|
| cdn.name | Find CDNs with the specified name. | cdn.name: example |
OCI Resource Tokens
Load Balancer
Tokens introduced in the Load Balancer resource.
|
Name |
Description |
Example |
|---|---|---|
|
name |
Find load balancers with the specified name. | name: web-lb |
|
id |
Find load balancers with the specified id. | id: 12345 |
| compartmentId | Find load balancers with the specified compartment id. | compartmentId: ocid1.compartment.oc1..aaaaaaaax3oie |
| loadbalancer.isPrivate | Find load balancers that are set to private. | loadbalancer.isPrivate: true |
| loadbalancer.isIpPublic | Find load balancers that are set to public. | loadbalancer.isIpPublic: true |
| loadbalancer.shapeName | Find load balancers with the specified shape name. | loadbalancer.shapeName: flexible |
| loadbalancer.lifecycleState | Find load balancers with the specified lifecycle state. |
loadbalancer.lifecycleState: ACTIVE |
Common Tokens
CDR Tokens
Tokens introduced to the Cloud Detection and Response tab in resource details.
|
Name |
Description |
Example |
|---|---|---|
|
severity |
Find threats with the specified severity (2,3,4) | severity:2 |
Control Changes
Changes introduced to controls in this release.
AWS
New Controls in "CIS Amazon Web Services Foundations Benchmark"
|
CID |
Title |
Service |
Resource |
|---|---|---|---|
|
537 |
Ensure security contact information is registered |
ACCOUNT |
ACCOUNT |
|
538 |
Ensure that Images (AMIs) are not older than 90 days |
EC2 |
EC2_IMAGES |
New Controls in "AWS Best Practices Policy"
|
CID |
Title |
Service |
Resource |
|---|---|---|---|
|
539 |
Ensure that Images (AMIs) are not unused more than 90 days |
EC2 |
EC2_IMAGES |
Migrated controls from "Amazon Web Services Best Practices Policy" to "AWS Identity Access Management Best Practices Policy"
|
CID |
Title |
|---|---|
|
3 |
Ensure access keys unused for 90 days or greater are disabled |
|
6 |
Ensure that custom IAM Password Policy is Defined |
|
7 |
Ensure that custom IAM password policy requires at least one uppercase letter |
|
8 |
Ensure that custom IAM password policy requires at least one lowercase letter |
|
9 |
Ensure that custom IAM password policy requires at least one symbol |
|
10 |
Ensure that custom IAM password policy requires at least one number |
|
13 |
Ensure that custom IAM password policy expires passwords within 90 days or less |
|
17 |
Ensure IAM policies are attached only to groups or roles |
|
399 |
Ensure that all IAM users are members of at least one IAM group |
|
400 |
Ensure an IAM User does not have access to the console |
|
448 |
Ensure that all your SSL/TLS IAM certificates are using 2048 or higher bit RSA keys |
Azure
New control in "CIS Microsoft Azure Foundations Benchmark"
|
CID |
Title |
Service |
Resource |
|---|---|---|---|
|
50233 |
PHP version' is the Latest, If Used to Run the Web App |
APP_SERVICE |
WEB_APP |
|
50235 |
Java version' is the latest, if used to run the Web App |
APP_SERVICE |
WEB_APP |
|
50470 |
Ensure that Private Endpoints are Used for Azure Key Vault |
KEY_VAULT |
KEY_VAULT |
|
50471 |
Ensure Private Endpoints are used to access Storage Accounts |
STORAGE_ACCOUNT |
STORAGE_ACCOUNT |
|
50234 |
Python version' is the Latest Stable Version, if Used to Run the Web App |
APP_SERVICE |
WEB_APP |
OCI
New Controls in "OCI Best Practices Policy"
|
CID |
Title |
Service |
Resource |
|---|---|---|---|
|
40055 |
Ensure Delete Protection is enabled for Loadbalancers |
LOAD_BALANCER |
LOADBALANCER |
Issues Addressed
- We updated the detection logic of the following controls to resolve false positive cases- CID 388, 433, 50036, 52008.
- We have updated the control logic of CID 19 to support AWS Advanced Event Selectors and prevent scenarios of evaluations failures.
- We have updated the control logic of CID 253 to ensure that 'Region' column in the CSV report shows accurate data.