Release 2.15
March 1, 2025
What’s New?
TotalCloud 2.15.0 brings updates to the resource inventory, Insights, controls and more.
Amazon Web Service
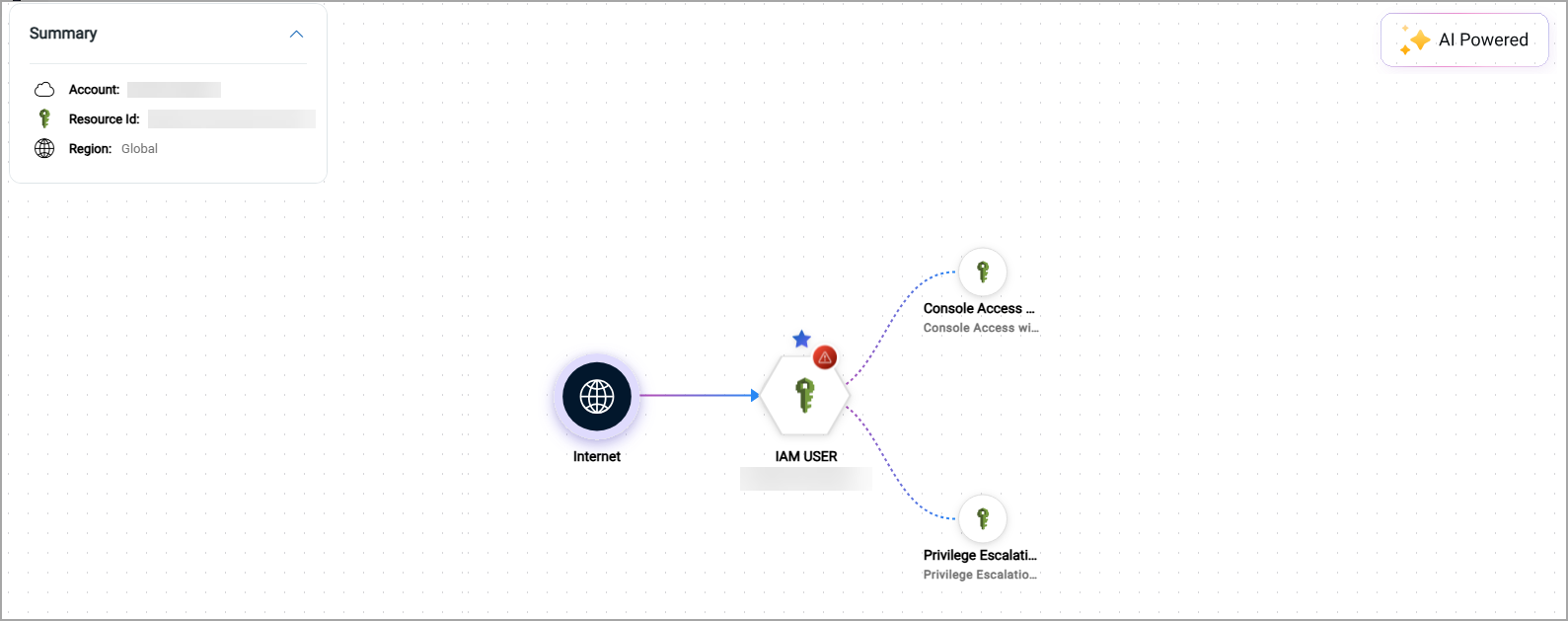
Introduced Attack Path Visualization to AWS TruRisk Insights
With this release, Qualys TotalCloud has enhanced AWS TruRisk Insights enabling a visual representation of resource relationships and potential security impact paths across your AWS environments. The new Attack Path column in AWS TruRisk Insights reveals security relationships between vulnerable cloud resources. Now, security teams can visualize how detected vulnerabilities and misconfigurations might cascade through interconnected cloud components, including compute instances, storage services, Kubernetes clusters, and databases.
This enhancement allows security teams to:
- Visualize the complete attack chains across AWS cloud environments
- Break down exposure chains for comprehensive risk assessment
- Understand the potential "blast radius" of vulnerabilities
- Trace security impacts across connected resources
To leverage this powerful new feature, simply navigate to the Insights tab of your TotalCloud app.
Select an insight with an icon under the Attack Path column to view their attack path.
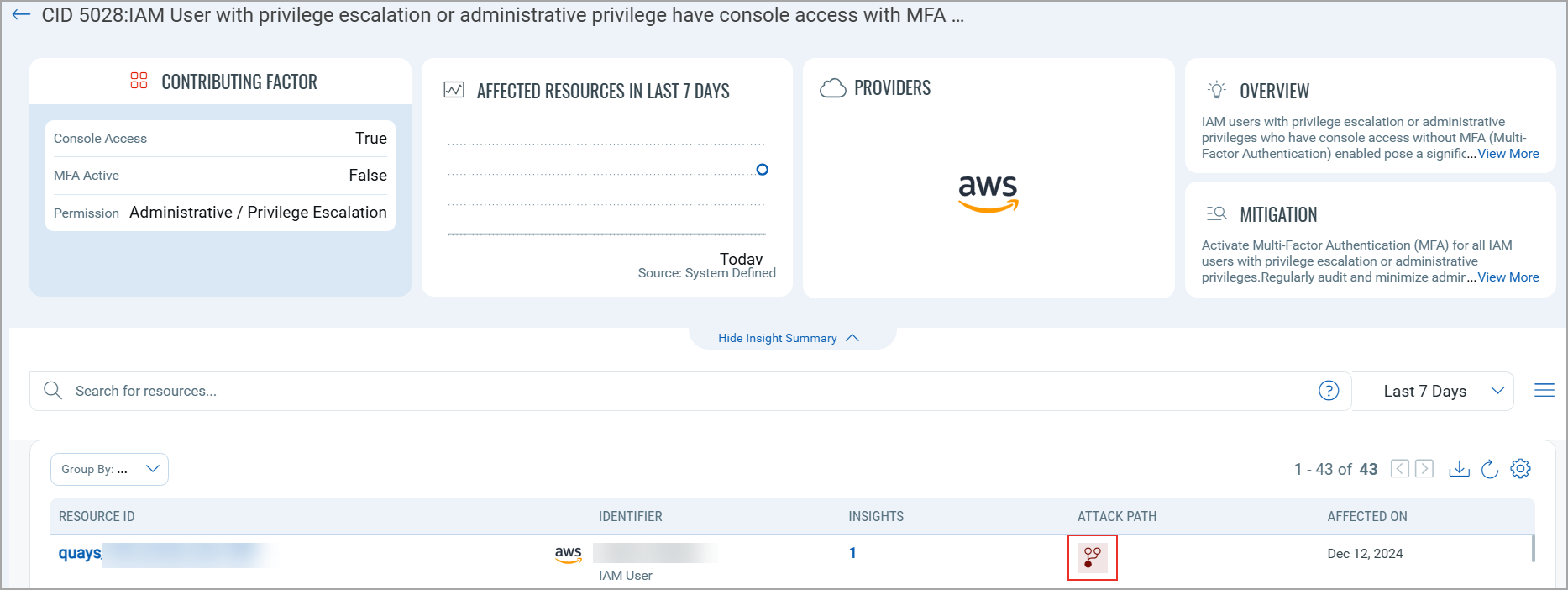
You can further click the individual affected resource to learn more about its vulnerabilities and misconfigurations, along with its control evaluations.
Added New Resource to the Cloud Inventory
With this release, we have included support for a new resource on the AWS Inventory. The cloud inventory ensures these new resources are assessed against the best global compliance standards supported by Qualys, such as NIST, PCI DSS, HIPAA, GDPR, etc.
New Resources Introduced
The following is the newly introduced resources in the TotalCloud app.
AWS AMIs
Microsoft Azure
Extended Cloud Detection and Response Support to Azure Resources
With this releases, we have extended the support of TotalCloud's CDR to Azure resources. Now, CDR can detect malware, ransomware, crypto-miner, and malicious network activity in your Azure environment using VTap.
To create an Azure CDR Deployment,
- Navigate to the Threat Scanners tab in the TotalCloud application.
- Select Azure from the available cloud provider tabs.
- Download the customizable Terraform scripts and click Create Deployments.
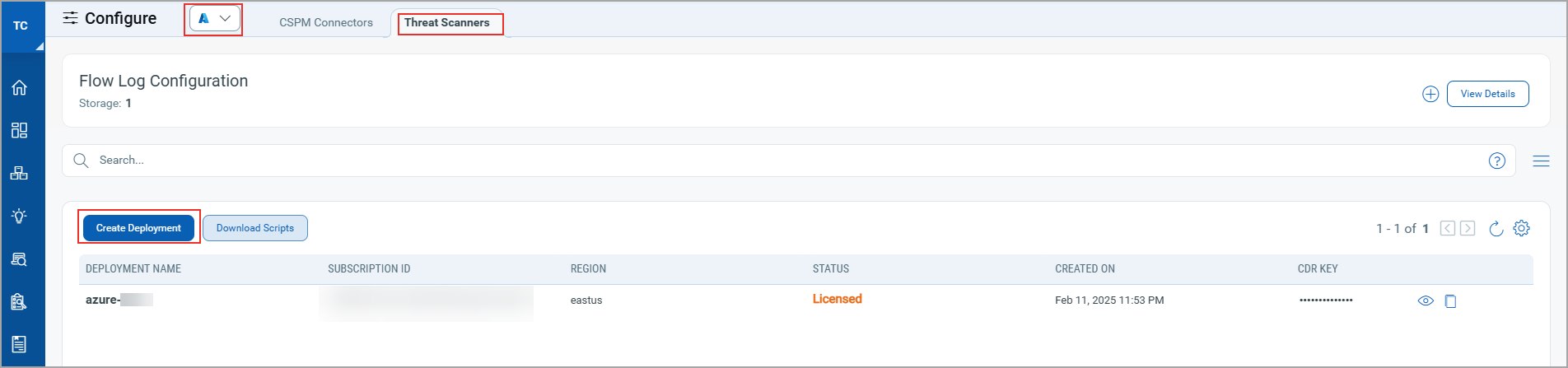
For more information on deploying CDR for Azure, you can refer to the Cloud Detection and Response documentation.
Oracle Cloud Infrastructure
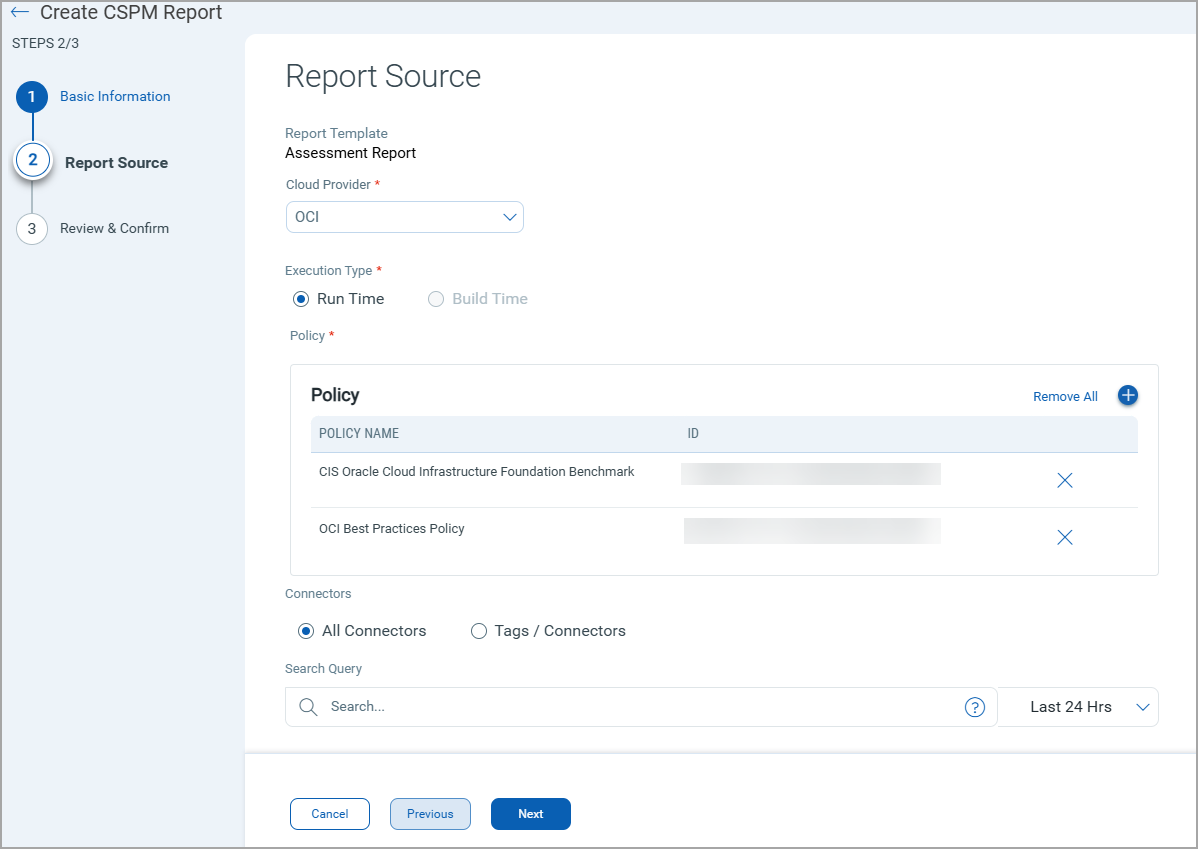
Introduced Reports for Oracle Cloud Infrastructure
With this release, we are extending the assessment repor features of TotalCloud to our OCI Cloud as well, assisting in the full maturity of OCI's CSPM features. Generate detailed reports identifying evaluated controls and the vulnerable/misconfigured resouces in your OCI environment. You can export the reports in PDF or CSV. Evaluate your OCI resources against region and sector-wise mandates by generating Mandate Reports.
To avail the new OCI Reports, simply navigate to the Reports tab in TotalCloud app.
Click the Create dropdown and select CSPM Report.
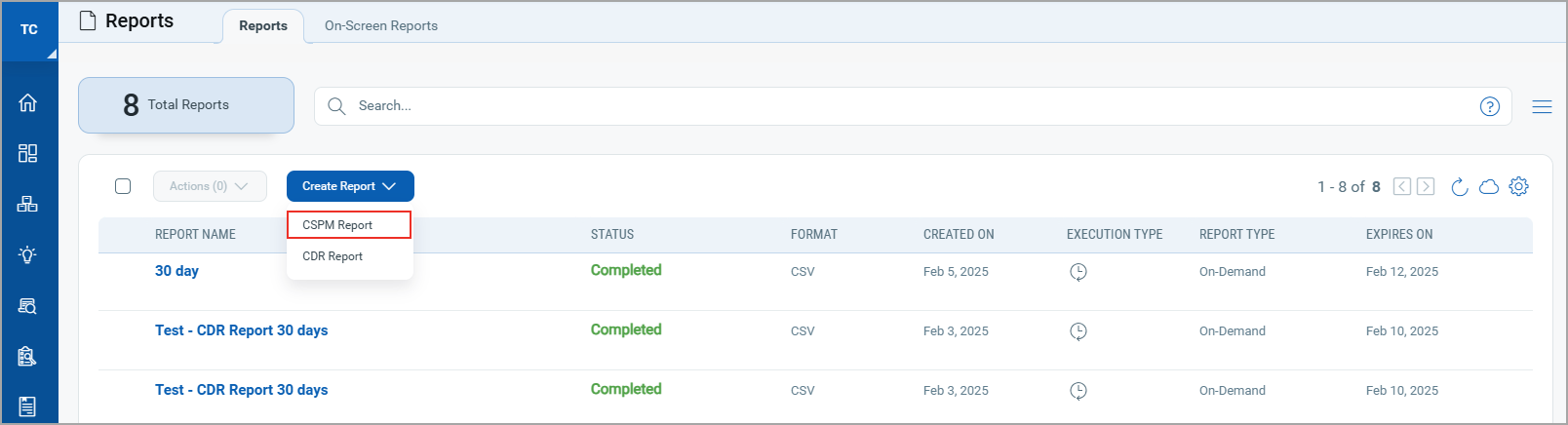
Configure the report parameters and you can view or export your report instantly.
Common Updates
Introduced Reports for Cloud Detection and Response
TotalCloud's Reporting feature is also extended to the CDR events. Generate CSV reports on CDR findings of any cloud provider. You can narrow down your findings with our advanced QQL search bar. Now, you can improve your threat posture with documented findings and take informed decisions.
To generate a CDR Report, navigate to the Reports tab of your TotalCloud app.
Click Create dropdown and select CDR Report.
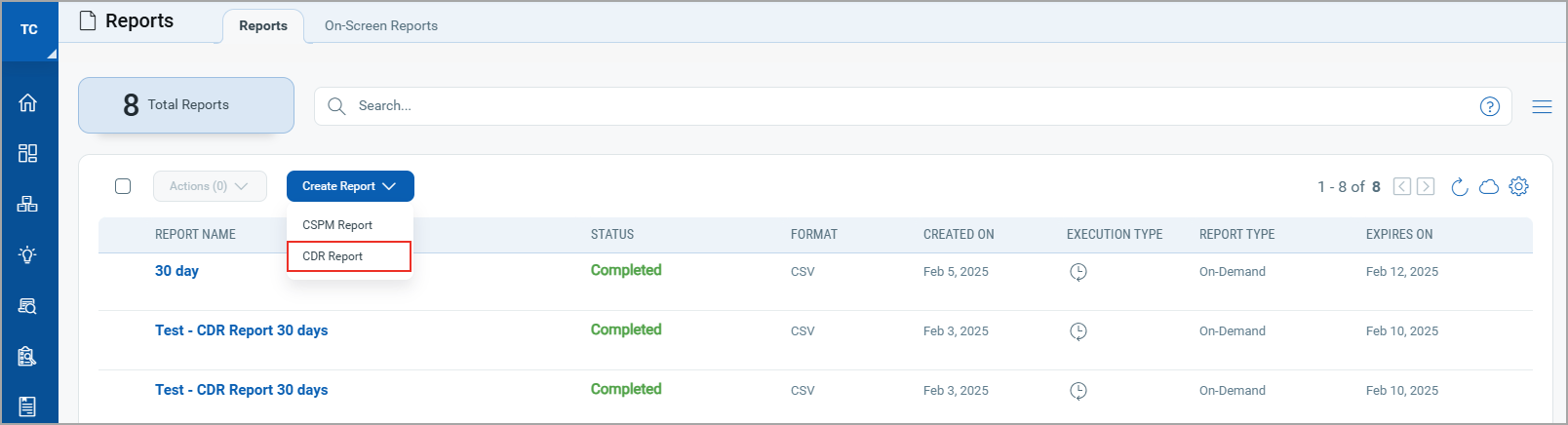
Configure the report parameters and you can view or export your report instantly.
Control Changes
Changes introduced to controls in this release.
Amazon Web Services
Deprecated AWS Controls
|
CID |
Title |
|---|---|
|
470 |
Ensure to enable network isolation for processing jobs(if configured) |
|
471 |
Ensure ML storage volume attached to training jobs are encrypted |
|
474 |
Ensure to enable inter-container traffic encryption for training jobs |
|
475 |
Ensure to enable network isolation for training jobs |
|
476 |
Ensure ML storage volume attached to Hyperparameter Tuning jobs are encrypted |
|
478 |
Ensure to encrypt the output of Hyperparameter tuning jobs in s3 |
|
480 |
Ensure to enable inter-container traffic encryption for Hyperparameter tuning jobs(if configured) |
|
482 |
Ensure to enable network isolation for Hyperparameter tuning jobs(if configured) |
|
521 |
Ensure ML storage volume attached to processing jobs are encrypted
|
AWS Policy Migration
|
CID |
Title |
Old Policy |
New Policy |
|---|---|---|---|
|
538 |
Ensure that Images (AMIs) are not older than 90 days |
CIS Amazon Web Services Foundations Benchmark Policy |
AWS Best Practices Policy |
Microsoft Azure
New Controls introduced in Microsoft Azure
|
CID |
Title |
Service |
Resource |
|---|---|---|---|
|
50481 |
Ensure network access is restricted to Logic Apps |
LOGIC_APP |
LOGIC_APP |
Azure Policy Migration
|
CID |
Title |
Old Policy |
New Policy |
|---|---|---|---|
|
50049 |
Ensure Web app has Client Certificates (Incoming client certificates) set to On |
Azure Best Practices Policy |
CIS Microsoft Azure Compute Services Benchmark |
|
50155 |
Ensure that only secure connections to Redis Cache is enabled |
Azure Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50171 |
Ensure that Azure Redis Cache servers are using the latest version of the TLS protocol |
Azure Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50153 |
Ensure that public network access is disabled in Redis Cache |
Azure Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50039 |
Ensure Enforce SSL connection is set to ENABLED for MySQL Database Server |
Azure Database Service Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50040 |
Ensure Enforce SSL connection is set to ENABLED for PostgreSQL Database Server |
Azure Database Service Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50041 |
Ensure server parameter log_checkpoints is set to ON for PostgreSQL Database Server |
Azure Database Service Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50074 |
Ensure server parameter connection_throttling is set to ON for PostgreSQL Database Server |
Azure Database Service Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50045 |
Ensure server parameter log_retention_days is greater than 3 days for PostgreSQL Database Server |
Azure Database Service Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50117 |
Ensure Allow access to Azure services for PostgreSQL Database Server is disabled |
Azure Database Service Best Practices Policy |
CIS Microsoft Azure Database Services Benchmark |
|
50173 |
Ensure that Geo-redundant storage is enabled for Storage Accounts |
Azure Best Practices Policy |
CIS Microsoft Azure Storage Services Benchmark |
|
50471 |
Ensure Private Endpoints are used to access Storage Accounts |
Azure Best Practices Policy |
CIS Microsoft Azure Storage Services Benchmark |
Deprecated Azure Controls
|
CID |
Title |
|---|---|
|
50462 |
Ensure that Allow Blob Anonymous Access is set to Disabled |
New Tokens
New Tokens introduced in TotalCloud 2.15.0
Amazon Web Services
Tokens introduced in AWS Resources
Amazon Machine Images (AMI)
With this release, we have added support for AMIs in the Resource Inventory. Use the following tokens to find AMIs from the AWS Inventory.
|
Name |
Description |
Example |
|---|---|---|
| ami.state | Find AMIs based on their current state (pending, available, invalid, deregistered, transient, failed, error, disabled) |
`ami.state: available` |
| ami.architecture | Find AMIs based on processor architecture (i386, x86_64, arm64, x86_64_mac, arm64_mac) |
`ami.architecture: arm64` |
| ami.bootmode | Find AMIs based on boot mode (uefi, uefi-preferred, legacy-bios) |
`ami.bootmode: uefi` |
| ami.hypervisor | Find AMIs based on hypervisor type (ovm, xen) |
`ami.hypervisor: xen` |
| ami.imagetype | Find AMIs based on image type (machine, kernel, ramdisk) |
`ami.imagetype: machine` |
| ami.platform | Find AMIs based on platform type (Linux/UNIX, Red Hat BYOL, Windows, Ubuntu Pro, etc.) |
`ami.platform: Ubuntu Pro` |
Issues Fixed
- We updated the detection logic of the following controls to resolve false positive cases- CID 367, 426, 452, 50051, 50062, 50169, 50303, 50304, .
- We updated the detection logic of CID 50075 to ensure remediated resources pass the Evaluation.
- We fixed an issue where the combination of
tags.nameandpolicy.nametokens resulted in inaccurate data. - We fixed an issue where the Policy Compliance widget showed inaccurate count of resources that Passed with Exception.
- We fixed an issue where the "Network Interface" detail in the Resource Inventory failed to display "Public IPv4 Address" for some resources.
- We fixed an issue where CID:403 failed for multiple resources despite remediation.
- We fixed an issue where AWS resource inventory displayed an inaccurate count Lambda resources.