The host detection API is often used in conjunction with other information that can be downloaded using other Qualys APIs.
Technical reports need additional information for each vulnerability such as the description, solution, threat or impact. The detection API provides the QID for each vulnerability found for an asset. The QID is a unique ID that references a vulnerability within the Qualys KnowledgeBase. Use the following workflow to create custom technical reports:
Step 1 - Use the host list detection API to return “host based” vulnerability data for hosts in your account.
Step 2 - Use the KnowlegeBase API (/api/2.0/fo/knowledge_base/vuln/?action=list) to obtain vulnerability data, such as the vulnerability description, threat and impact. It’s possible to make a request for all vulnerabilities (QIDs) in the KnowledgeBase or just a specific vulnerability.
For example, to make a request for QID 90082 use the following URL: https://qualysapi.qualys.com/api/2.0/fo/knowledge_base/vuln/?actio n=list&ids=90082
where “qualysapi.qualys.com” is the name of the API server where your account is located (in this case US Platform 1).
Step 3 - Correlate the vulnerability information in the third party application using the QID number provided in the XML output which is returned by the host detection API (Step 1) and the KnowledgeBase API (Step 2).
A typical integration would be to create tables in a database for the XML output from both Qualys API functions and use QID as a key for a join. This way it would be possible to create queries that will provide all the vulnerabilities for a given set of hosts (according to custom search criteria) and their descriptions.
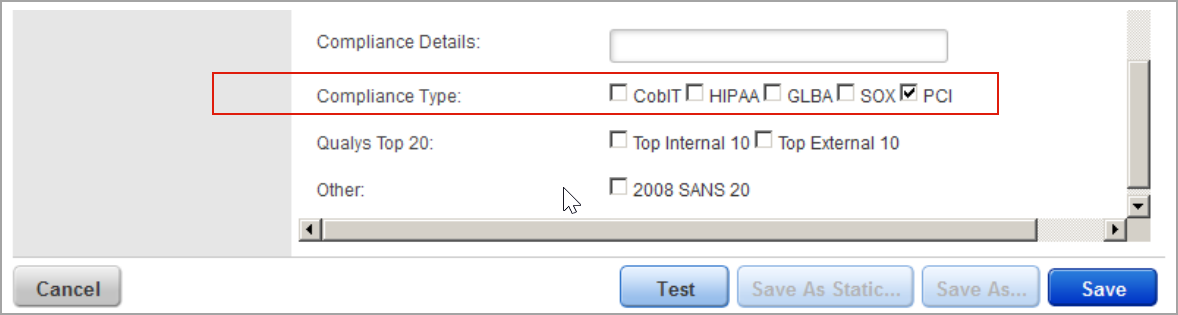
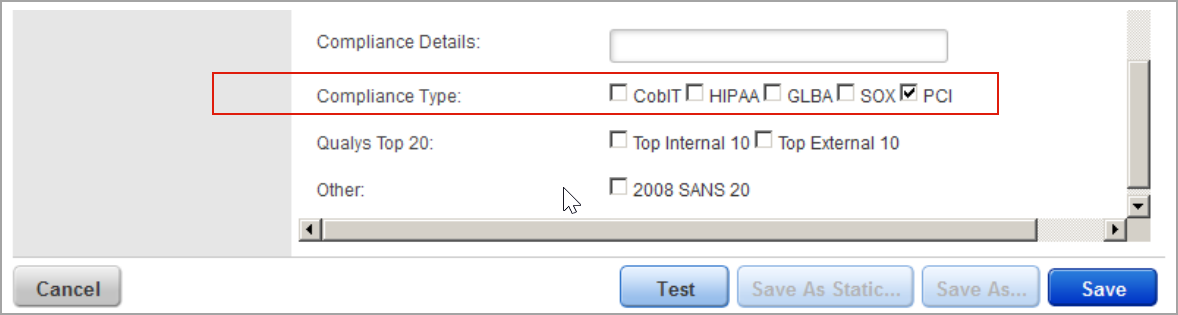
Step 1 - First you need to create a dynamic search list titled “PCI Vulns” using the Qualys user interface. When creating the dynamic search list, select the PCI option next to Compliance Type as shown below.
Step 2 - Create an asset group titled “PCI Hosts” containing the hosts which are in scope for PCI compliance.
Step 3 - Make the following host list detection API request using the asset group title “PCI Hosts” and the search list title “PCI Vulns”: https://qualysapi.qualys.com/api/2.0/fo/asset/host/vm/detection/?action=list&ag_titles=PCI+Hosts&include_search_list_titles=PCI+Vuln s'
where “qualysapi.qualys.com” is the name of the API server where your account is located (in this case US Platform 1).