View Vulnerability Information
You can learn everything you need to know about a vulnerability by going to VM/VMDR > KnowledgeBase and selecting Info from the Quick Actions menu. You can view basic details for the vulnerability like the title, severity and type. You can also see whether you'll need to use authentication to detect the vulnerability.
See a term you don't know?
Check out our Glossary
How can I tell if authentication is needed?
Check out the discovery method for the vulnerability which will indicate whether authentication is required. You'll also see a key  next to Authentication when authenticated scanning can be used. Not sure how to get started with authentication? Go here to find out.
next to Authentication when authenticated scanning can be used. Not sure how to get started with authentication? Go here to find out.
How can I tell if the vulnerability was changed by a user?
If the vulnerability was modified by a user then you'll see Edited: Yes. This means that a Manager user changed the severity level and/or added comments to the Threat, Impact or Solution.
Why is the technology field not visible for certain QIDs on the vulnerability Information page?
The technology field is visible only if the QID has some technology associated with it, else the field is not visible on the window.
Note: The technology type is visible only if the QIDs are associated with SCA QIDs
Why is the code modified date for certain QIDs blank on the vulnerability Information page?
If the QID does not have a code modified date, it is shown blank on the vulnerability information page.
Do I have the option to filter the QIDs based on code modified date?
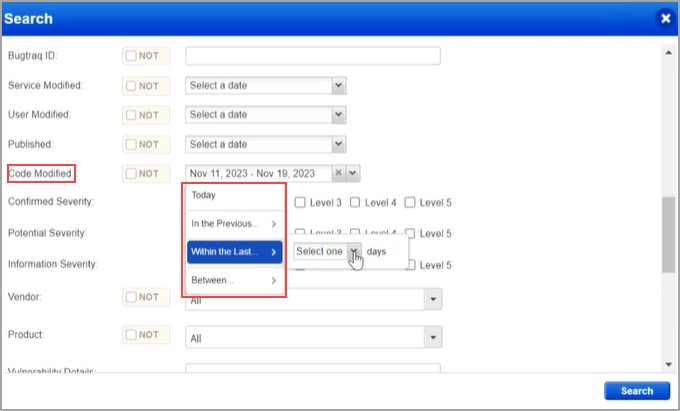
Yes. You have the option to filter the QIDs based on code modified date: You can select any of the options shown below.
- Between specific dates
- Within the last few days
- In the previous week, month, quarter, or year
- Today
Tell me about published and modified dates
Published date - When the vulnerability was first added to the KnowledgeBase.
Service modified date - When vulnerability attributes were changed like the title, severity level, patch availability, CVSS scores, PCI relevance, etc.
This date is not updated based on changes to exploitability information since these changes don't affect the signature code, scoring or the QID description.
User modified date - When a user edited the vulnerability to change the severity level or to add comments.
Tell me about the Change Log section
The Change Log section includes log entries when there are changes to the QID detection logic and changes to key values. Change log entries will be automatically created whenever risk-relevant fields are modified, including:
- Authentication Type
- Category
- CVE
- CVSS
- Linked Exploits
- PCI Flags
- Impact
- Patch
- Patch Available
- Vendor Reference
- Remote Flags
- RTIs Changes
- Severity
- Solution
- Threat
- Title
- Workaround
Changes to other components such as detection logic can also be recorded by the Vulnerability Signatures team. For each change, you will see the date of the change and comments provided by the team. The modified date for a QID would change if there is a change in one of the fields for a QID in the KnowledgeBase. For example, if the severity of a QID was updated.
For more details, see KnowledgeBase QID Updates | Change Log and Modified Date
When is the QID Modified date updated?
QID Modified date is updated if there are changes made to the following description fields:
- Category: Information Gathered, Confirmed Vulnerability, Potential Vulnerability
- Severity: Severity levels [1,2,3,4,5]
- Vendor Reference: URL to vendor's page
- Patch Available: [Yes, No]
- Title: Title of QID
- Threat: If Threat tab is updated
- Solution: If Solution tab is updated
- Authentication Type: Windows, Unix, Oracle, SNMP, VMware, WebLogic, MS SQL, etc.
- PCI Explanation: QID falls into any of these categories for PCI : SQL Injection, Cross-site scripting (XSS) flaw, Directory traversal, HTTP response splitting/header injection, Unsupported software, Databases access, Default account/password, Unrestricted DNS zone transfer, Backdoor, SSL Specific
- PCI Exception: Reason why QID is marked as PCI exception
Tell me about the list of vendors/products in the Software section
The list of vendors and products associated with the vulnerability is provided by NIST. Please note that this feature covers all QIDs that are associated with a CVE.
What are the supported modules?
These are the Qualys modules that can be used to detect the vulnerability. We'll indicate whether the QID can be detected by a VM scan, Windows Cloud Agent, Linux Cloud Agent, etc.
Use the KnowledgeBase Search to quickly identify vulnerabilities by supported module.
Tell me about the detection of supported module QIDs
When you run a scan on any QID supported module, only the QIDs supported by a specific module is detected. For example, when you run a VM scan, only the QID supported by the VM module is detected and processed.
To verify if a QID is supported for a specific module, navigate to KnowledgeBase > Search tab > Enter the QID > Search. Click the displayed QID to view the Supported Modules in the preview.
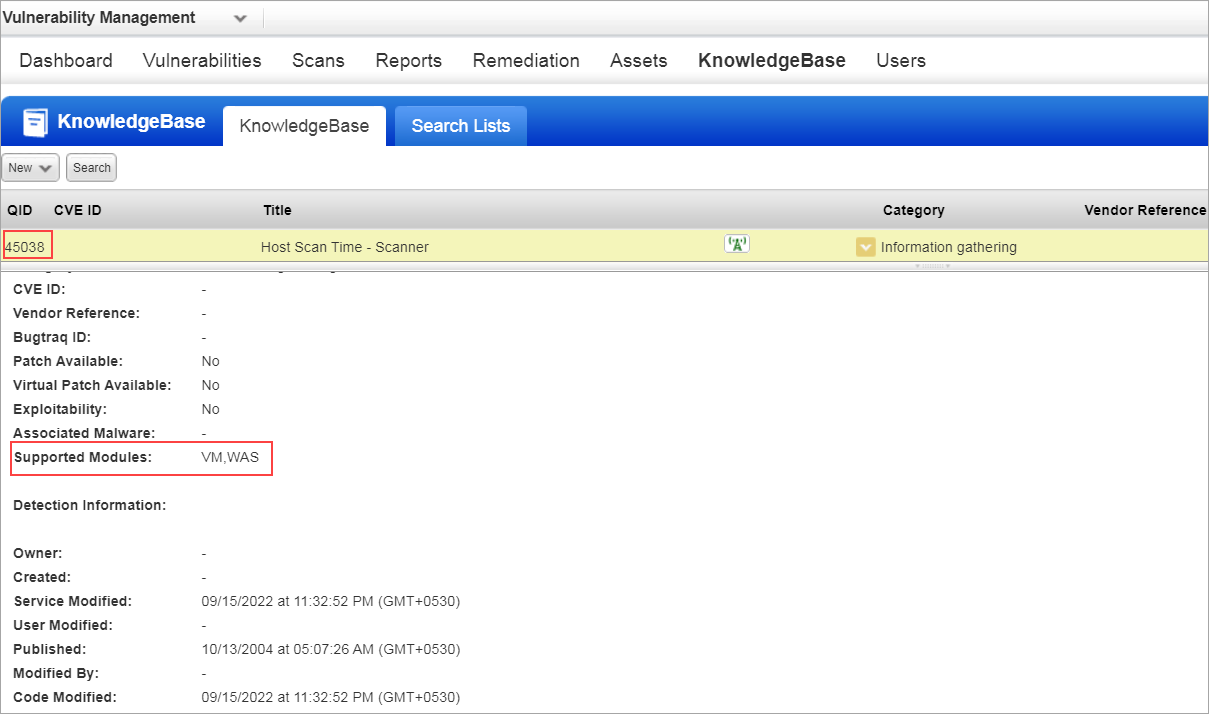
For example, QID 45038 is supported only by VM and WAS. When you perform VM and WAS scans, only this QID is detected and processed. If you select the supported module as Windows-Agent in the Search tab for the same QID, the information is not displayed. It displays the message No data found matching your filter.