Understand Your Risk Context
Traditional vulnerability scoring falls short of providing actionable risk intelligence. This section introduces QVS and QDS scores, which are the foundational elements that enable TruRisk™ to deliver contextual and business-relevant risk assessment.
Qualys Vulnerability Score (QVS)
QVS operates at the CVE level, incorporating external threat intelligence and exploit factors to assess vulnerability risk. QVS is computed for all vulnerabilities in the National Vulnerability Database (NVD), including those without Qualys detection signatures (QIDs), ensuring comprehensive coverage.
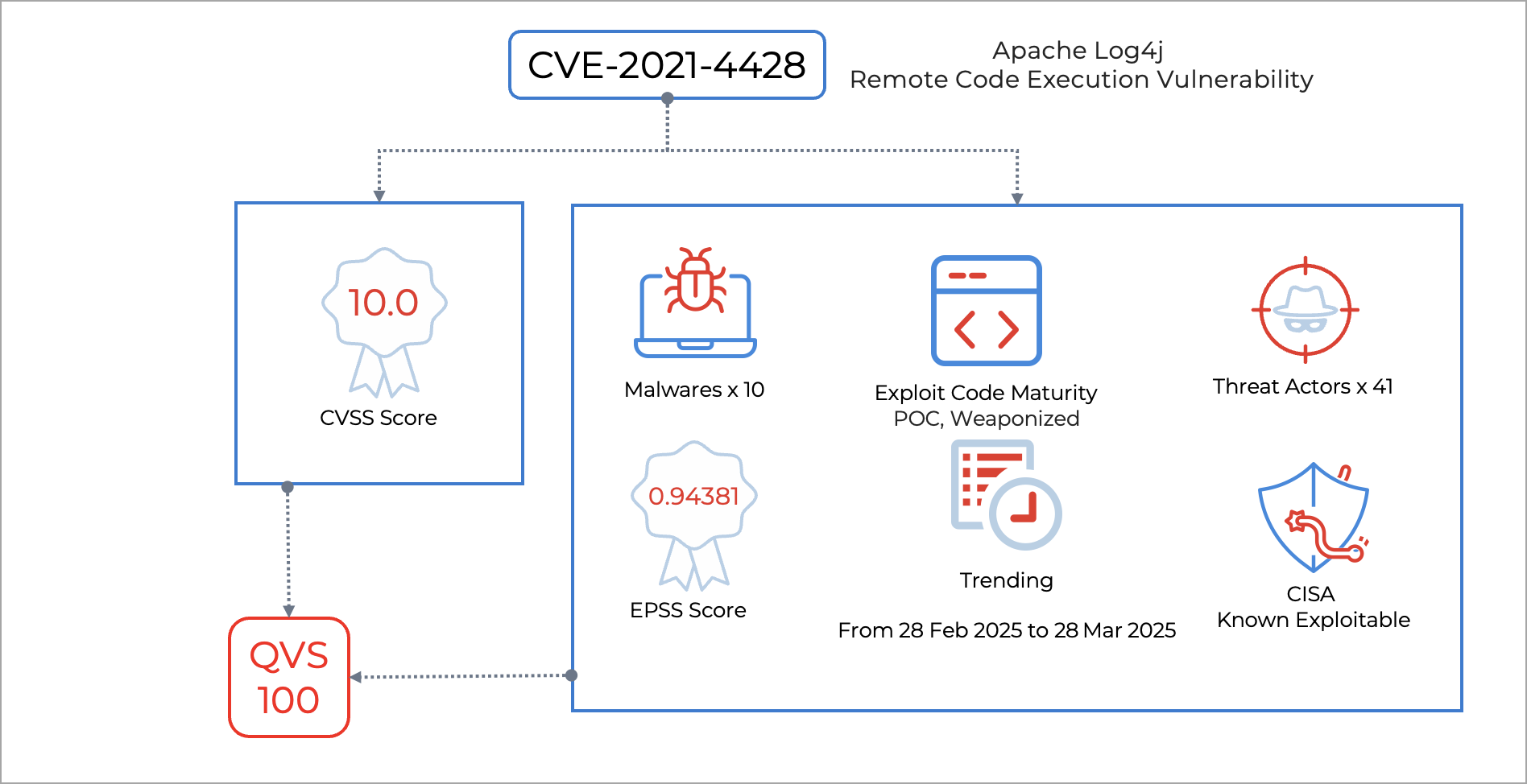
In the following example, QVS provides a comprehensive risk assessment by combining traditional vulnerability metrics with real-world threat intelligence data. The scoring framework first evaluates the Threat attributes of a CVE. If the CVE is listed in the CISA KEV catalog and/or is associated with malware or a known threat actor, it receives a higher weight (greater than 90%). The remaining 10% is assigned to exploit maturity, EPSS, and trending factors. If Threat attributes are not present, 65% of the score is based on the CVSS base score. This score reflects technical severity, exploitability, and impact on confidentiality, integrity, and availability. The remaining 35% is distributed across exploit maturity, EPSS, and trending feeds.
The QVS score of 100 reflects not only a high CVSS base score but also confirms active exploitation in the wild, widespread interest from threat actors, availability of exploit code, and significant potential for real-world impact. This makes it a top priority for security remediation efforts, as it combines both high technical severity and active real-world threat activity.
QVS Risk Factors
The following table lists the QVS risk factors in a sequential order:
| Sequence | Key Factor | Description |
| 1 | CVSS Base Score, EPSS, CISA KEV |
The QDS algorithm starts with the CVSS score as the foundation input to assess vulnerability technical severity. |
| 2 | Threat Actors | Validates exploitation by threat actors or ransomware groups. Vulnerabilities actively used by these groups receive the highest threat level ratings. |
| 3 | Malware | Verifies active exploitation by malware families. Vulnerabilities currently exploited by malware receive elevated risk ratings. |
| 4 | Exploit Code Maturity | Evaluates the sophistication of available exploit code. Weaponized exploits (mature, easily usable for system compromise) receive higher ratings than Proof-of-Concept (PoC) exploits (theoretical or limited functionality). |
| 5 | Exploit Type and Real-Time Threat Indicators (RTIs) | Analyzes vulnerability type classification. Remote exploitation vulnerabilities and web application vulnerabilities receive higher risk ratings than Denial-of-Service (DoS) vulnerabilities. |
| 6 | Trending in the Wild | Monitors recent exploitation activity within the last 30 days across the Dark Web, social media, GitHub, and other intelligence sources. Trending vulnerabilities receive additional risk elevation. |
The above-listed factors are assessed by analyzing more than 300,000 + CVEs tracked from 25+ different exploit and threat intelligence sources.
Building an accurate risk profile for any CVE requires combining multiple factors to assess its risk. Qualys Detection Score leverages these factors to compute the true risk of the vulnerability.
QVS Beyond NVD Dependencies
Sometimes, CVEs may not appear in the NVD database for several days to years. This delay could be due to the vulnerability not having been made public or to insufficient resources being available for research on the entry. In such scenarios, the Qualys Security Research Team assigns the CVSS Score based on the NVD standards.
How it works
When NVD has not yet processed a CVE, Qualys creates QIDs based on vendor advisories and our threat research. QVS is calculated using Real-Time Threat Indicators (RTIs) rather than waiting for official NVD scoring.
The scoring uses a weighted approach, with 20% derived from available CVSS data and 80% from RTI analysis.
Example: QID 6017591
This QID exists without associated CVEs because the CVE hasn't been "received" or added to NVD's dataset yet. Despite this:
- RTIs indicate "Exploit Code Available" and "Denial of Service" potential
- Both factors are classified as Severe by Qualys Threat Research
- Easy exploitation combined with availability impact results in a Critical QVS score
- CVE-2025-21655 exemplifies this scenario
This proactive approach means you may encounter QDS scores that appear high, even when QID severity is shown as medium, because Qualys utilizes multiple intelligence sources beyond NVD data. This enables immediate risk assessment and threat response, rather than waiting weeks or months for official NVD processing.
Understanding the Qualys Vulnerability Score for CVEs
The Qualys Vulnerability Score (QVS) is a Qualys-assigned score for a vulnerability based on multiple factors associated with the CVE, including CVSS and external threat indicators such as active exploitation, exploit code maturity, CISA-known exploitable vulnerabilities, and others. It is also computed for vulnerabilities that don’t have Qualys vulnerability detection signatures (QIDs). For QIDs with no published CVEs or low QDS, QVS will be calculated based on Real-time Threat Indicators (RTIs), such as Zero-day Exploits, Active Attacks, Ransomware, and Wormable.
There are two approaches to querying and displaying vulnerabilities. One is aligned with Qualys Identifier (QID) and the other with industry standards (CVE). This allows you to utilize QID and CVE-based data for more effective risk analysis and decision-making. Learn more here: Understanding Old and New Vulnerability Queries.
These QVS scores can be individually queried for insights from our dedicated API endpoint.
Qualys Detection Score (QDS)
QDS operates at the QID level and represents the primary score for vulnerability prioritization. QDS incorporates multi-CVE consolidation. If multiple CVEs contribute to a QID, the CVE with the highest score is considered for the QDS calculation.
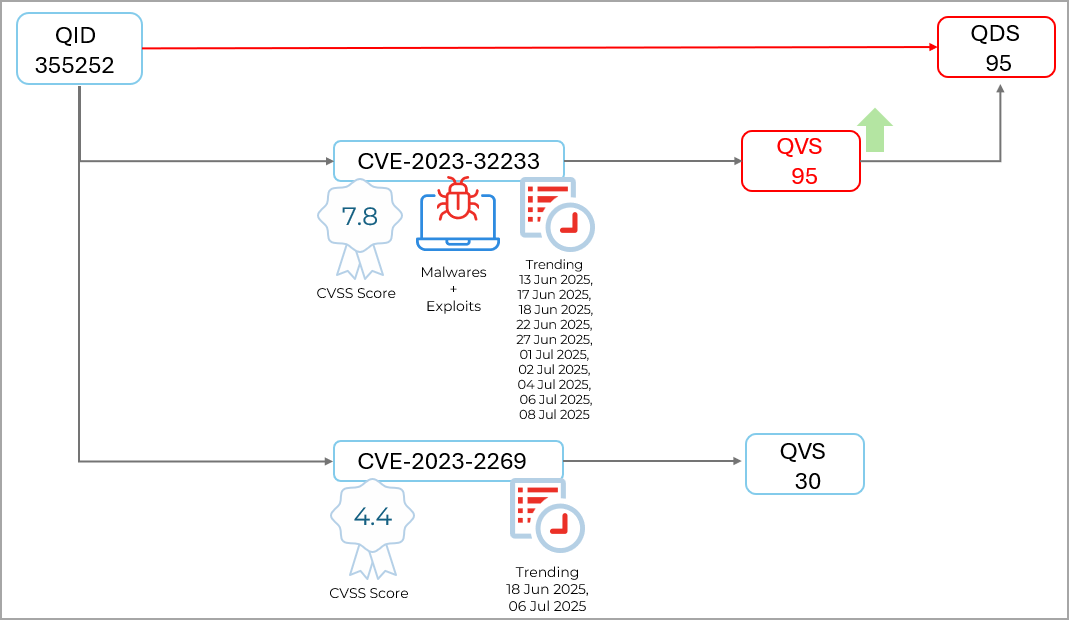
For example, QID 355352 is associated with two CVEs: CVE-2023-32233 and CVE-2023-2269. Each CVE receives its individual QVS score, where CVE-2023-32233 scores 75 while CVE-2023-2269 scores 30.
When calculating the QDS for this QID, Qualys selects the highest QVS among all associated CVEs. For each CVE, a QVS is calculated by considering the Technical, Temporal, and Trending factors related to the likelihood of an exploit. Since CVE-2023-32233 has the highest QVS of 75, the resulting QDS for QID 355352 becomes 75, ensuring that the most critical vulnerability drives the overall detection score.
You can prioritize your vulnerabilities based on the QDS. QDS has a range from 1 to 100 and with four severity levels:
- Critical: 90-100
- High: 70-89
- Medium: 40-69
- Low: 1-39
QDS is derived from the following factors:
- Vulnerability technical details (CVSS score): The highest Qualys Vulnerability Score (QVS) for CVEs is associated with the QID. QDS selects the highest QVS of all the CVEs related to that QID.
- Vulnerability temporal details: QDS monitors external threat intelligence details for a vulnerability and collects data like Exploit Code Maturity (ECM), malware, active threat actors, and whether a threat is trending. It accounts for any compensating/mitigation controls applied to an asset to reduce the risk score for a given vulnerability. For example, QDS will reduce the risk of a Remote Desktop Protocol (RDP) vulnerability if RDP is disabled.
We recommend prioritizing vulnerabilities with a TruRisk™-QDS score of 70 or higher.
QDS Calculation Process
The QDS calculation involves the following steps:
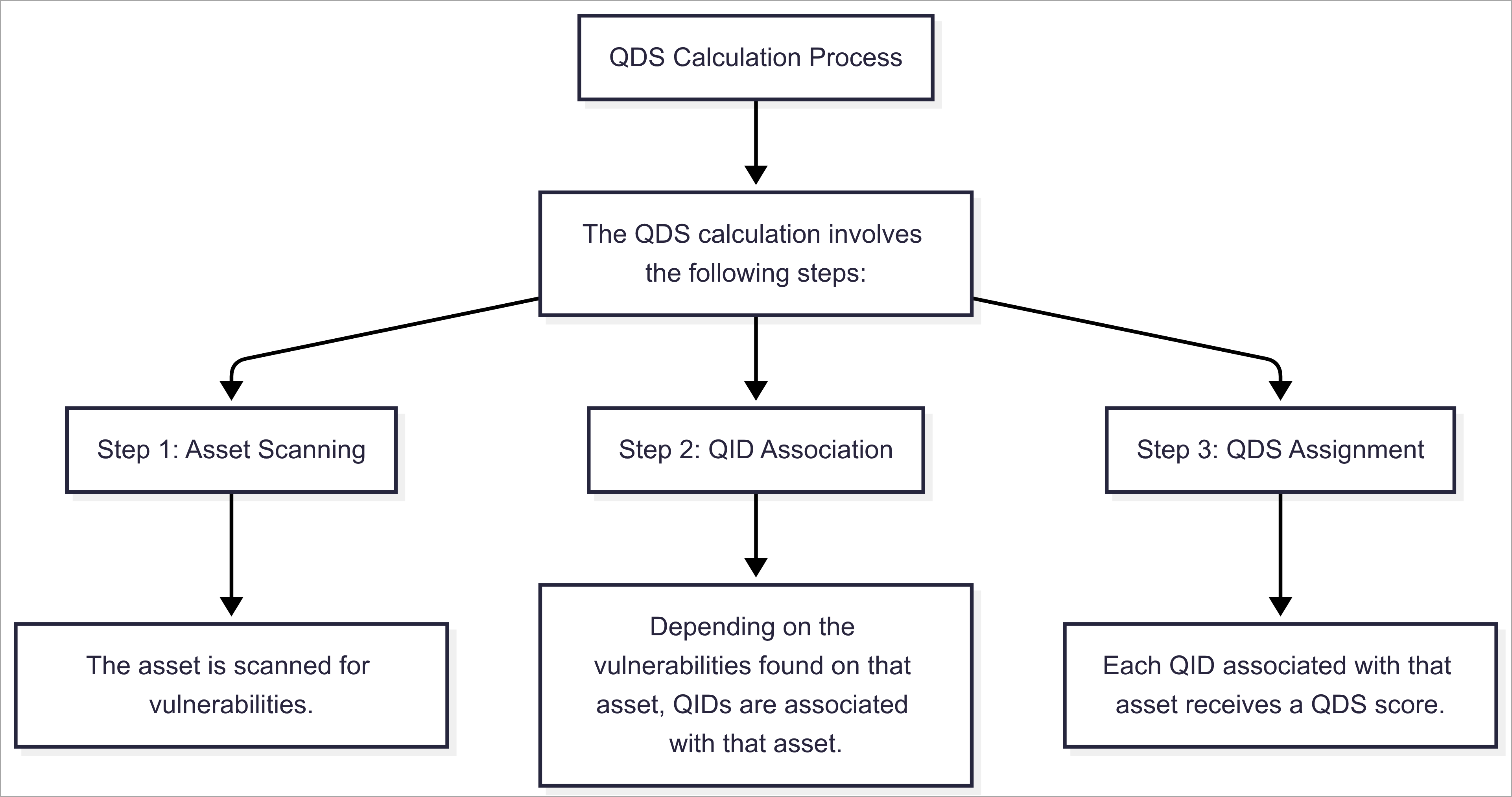
QIDs are not only associated with vulnerabilities. They are also associated with information gathered from that asset. These information-gathering QIDs do not have a QDS associated with them and do not affect the TruRisk™ Score of that asset.
QDS vs CVSS
A vulnerability with a low CVSS score can still have a high QDS because attackers often exploit overlooked vulnerabilities to evade detection. Organizations relying solely on CVSS may miss these risks.
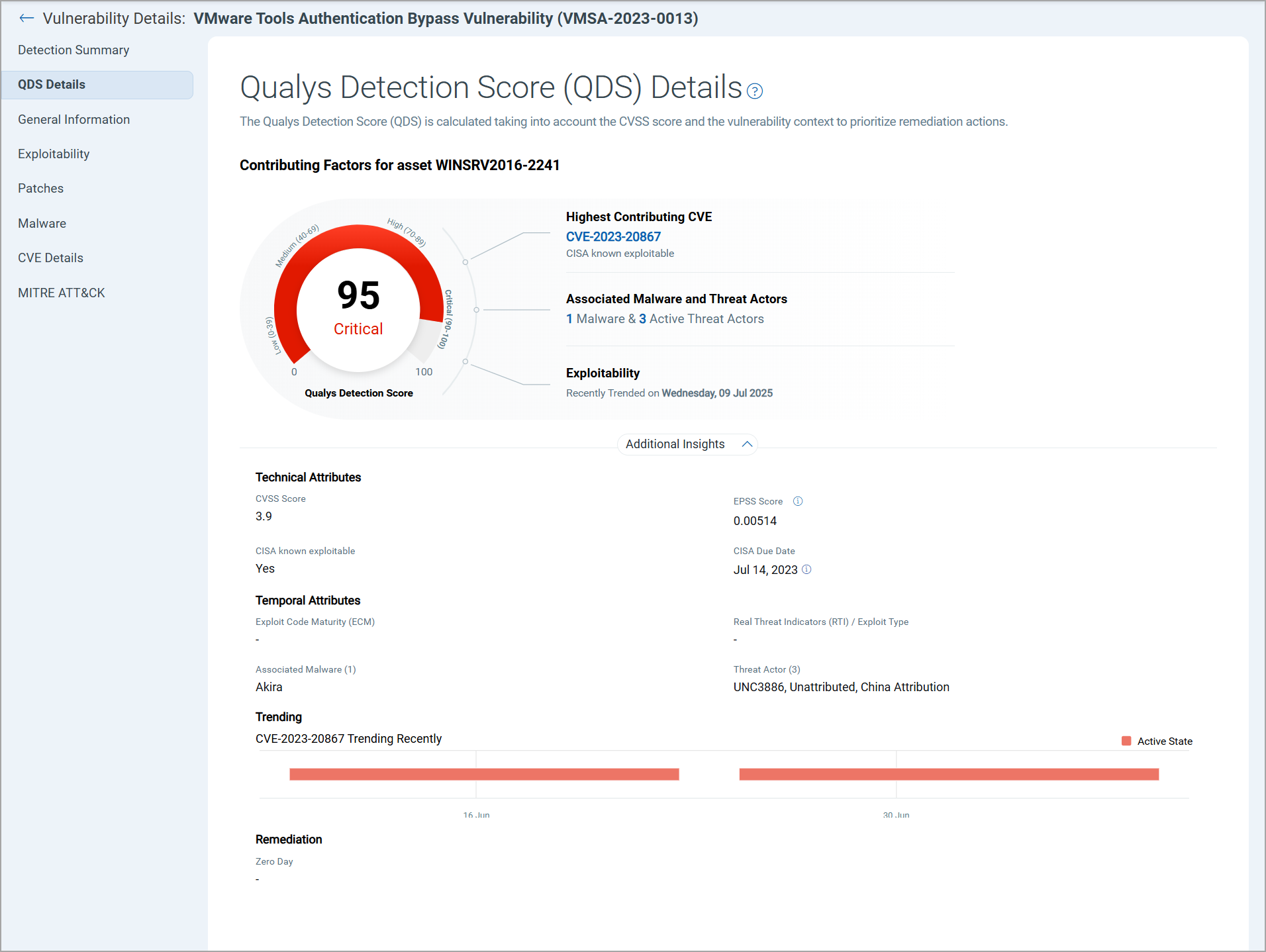
Example 1 - Low CVSS, High QDS
To identify vulnerabilities with a QDS of 90 or higher and Low CVSS criticality, use the following QQL query:
vulnerabilities.vulnerability.cvss2Info.baseScoree<4.0 and vulnerabilities.vulnerability.cvss3Info.baseScore<4.0 and vulnerabilities.detectionScore>79
In the example result below, CVE-2023-20867 has a CVSS score of 3.9. Yet, it appears on the CISA KEV list, is linked to an active malware campaign, and is being exploited by multiple threat actors, demonstrating why QDS provides critical insights beyond CVSS alone.
Example 2 - High CVSS, Low QDS
Some vulnerabilities may have a high CVSS score but a low QDS score if they lack active exploitation or associated threats. To identify vulnerabilities with a QDS of 70 or lower and Critical CVSS classification, use the following QQL query:
vulnerabilities.vulnerability.cvss2Info.baseScore>=7.0 and vulnerabilities.vulnerability.cvss3Info.baseScore:7.0 and vulnerabilities.detectionScore:<=40
For example, CVE-2021-43905 has a critical CVSS score of 9.6, yet its QDS remains low due to the absence of known exploits or malware activity so the likelihood of exploitation is low.
![]()
Interpret Qualys TruRisk™ Scores
The following table lists the scores that can be individually queried for insights through our dedicated API endpoint.
| QDS/QVS Range | Description |
| >95 |
Vulnerability Detected by Qualys with a CVSS rating of Critical, High, or Medium AND has functional exploit code available AND exploit code is actively leveraged by threat actors, malware, and ransomware groups to compromise systems AND trending in the wild, dark web. OR High likelihood of exploitation in the next 30 days (EPSS) OR Evidence of exploitation in the wild |
| 90-95 |
Vulnerability Detected by Qualys with a CVSS rating of Critical, High, or Medium AND has functional exploit code available AND exploit code is actively leveraged by threat actors, malware, and ransomware groups to compromise systems. OR Evidence of exploitation in the wild OR High likelihood of exploitation in the next 30 days (EPSS) |
| 70-89 |
Vulnerability Detected by Qualys with a CVSS rating of Critical, High, or Medium AND has functional exploit code available, with no evidence of exploitation. OR CVSS rating of Critical, High, or Medium with evidence of exploitation, and mitigation in place. |
| 60-69 | Vulnerability Detected by Qualys with a CVSS Critical, AND Proof of Concept1 (PoC) exploit is available. |
| 50-59 | Vulnerability Detected by Qualys with a CVSS High, AND a (PoC) exploit is available. |
| 40-49 | Vulnerability Detected by Qualys with a CVSS Critical, High, AND no exploit available. |
| 30-39 | Vulnerability Detected by Qualys with a CVSS Medium, AND a PoC exploit is available. |
| 1-29 | Vulnerability Detected by Qualys with a CVSS Low vulnerabilities, low risk of exploitation. |