Enterprise TruRisk™ Platform Release 10.37.2
February 23, 2026
Qualys Vulnerability Management (VM)
KnowledgeBase Enhancement - Support for Search List for Deep Scan QIDs
With this feature, we have provided the ability to search Deep Scan QIDs in Knowledge Base and Search List, which helps to filter all the Deep Scan QIDs and list them on the Knowledge Base listing page. To support this, we have added a new option, Deep Scan - Windows, under the Cloud Agent Scan Type field to the search window (KnowledgeBase > Search). When you create a static search list, you can view the Deep Scan - Windows checkbox in the Search window.
Deep Scan improves detection accuracy by inspecting deeper file system locations, increasing coverage for non-standard application paths, and enhancing visibility into modern and custom-built workloads. As a result, security teams can close blind spots that traditional scans often miss, without impacting agent performance.
This capability enables more comprehensive discovery of software and vulnerabilities in complex environments.
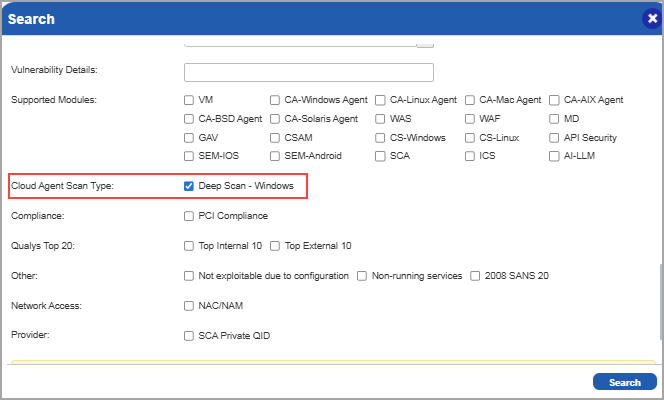
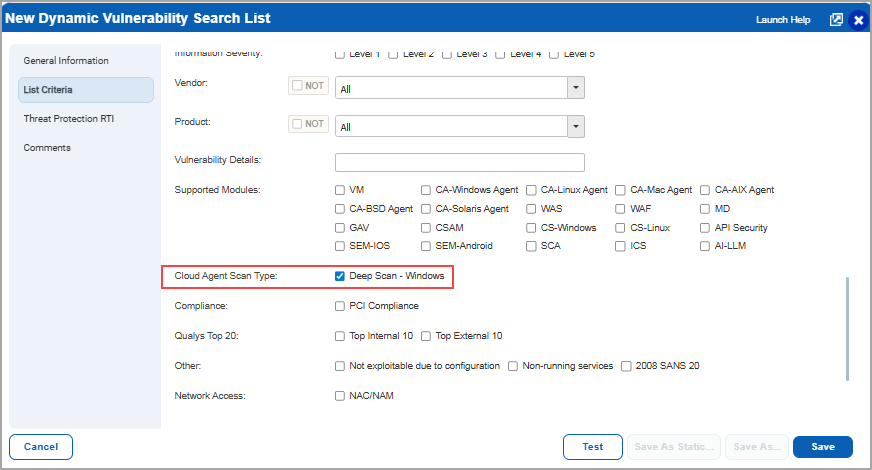
This option is visible when you create a dynamic search list: (KnowledgeBase > Search Lists > New > Dynamic List > New Dynamic Vulnerability Search List).
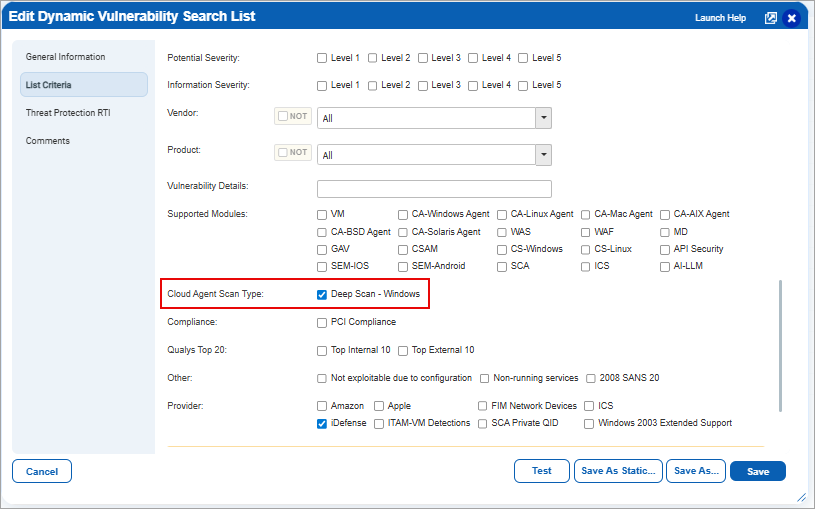
Also, this option is visible when you edit a dynamic search list (KnowledgeBase > Search Lists > Dynamic search list > Quick Action > Edit > Edit Dynamic Vulnerability Search List).
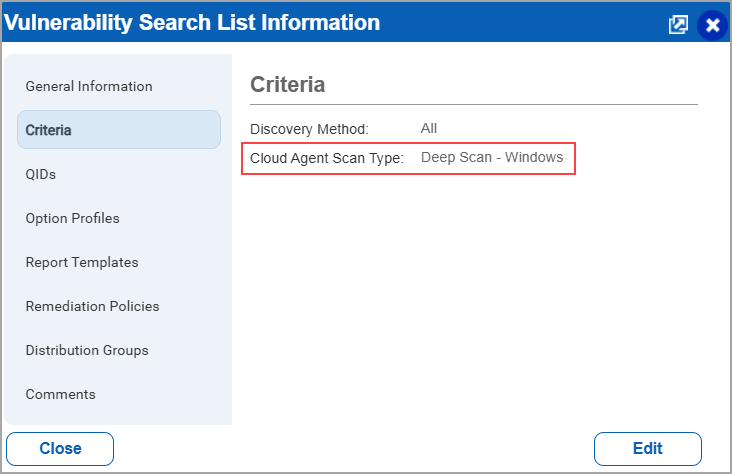
Once you have created a dynamic search list, on the KnowledgeBase > Search Lists > Quick Menu > Info > Vulnerability Search List Information page, you can view the Cloud Agent Scan Type as Deep Scan - Windows under Criteria and its respective QIDs in the left pane.
This feature is being reevaluated and will be reintroduced in a future release.
Issues Addressed
The following reported and notable customer issues are fixed in this release:
| Component/Category | Application |
Description |
| VM - Host List Detection API | Vulnerability Management |
When the users executed the host list detection API endpoint /api/{version}/fo/asset/host/vm/detection/ across different versions (for example, v2.0 and v5.0), inconsistencies were observed in the responses when the detection_updated_since parameter was used. Relevant code changes have been implemented to resolve the issue. |