MITRE ATT&CK® Matrix
MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK®) framework enhances your organization's network security using a defensive and standardized matrix. Using the robust ATT&CK knowledge base, you can evaluate your organization's adherence to the MITRE ATT&CK® framework.
Using Qualys provisioned Enterprise MITRE ATT&CK Matrix, you can identify the gaps in the security architecture, instantly contain the threat, and protect your organization from new attacks.
In this section, we have listed some of the Frequently Asked Questions that will be helpful for you while working on implementing the Enterprise MITRE ATT&CK Matrix:
- What are the Prerequisites for MITRE ATT&CK Matrix?
- Before I proceed, which MITRE ATT&CK terms should I be aware_of?
- Where can I get the list of MITRE ATT&CK Tactics and Techniques?
- How does Qualys VMDR uses the MITRE ATT&CK Matrix?
What are the Prerequisites for MITRE ATT&CK Matrix?
Following are the prerequisties for Enterprise MITRE ATT&CK Matrix in the Prioritization tab of VMDR:
- Application: VMDR full subscription
- Operating Systems: Windows, Linux, or Mac
- User Role: VMDR Manager User
Additionally, with the Qualys Policy Compliance (PC) subscription, you can reduce internal and external threats by scanning the compliance check of your systems against your policies. Qualys Endpoint Detection and Response (EDR) subscription leverages you to get the list of compromised events.
Before I proceed, which MITRE ATT&CK terms should I be aware of?
| Terms | Description |
| Adversarial | Adversarial represents threat actors |
| Tactics | Tactics represents the threat actors' goal for an attack. |
| Techniques | Techniques represents how threat actors' can achieve their Tactic or goal. |
| Common Knowledge | Common Knowledge documents the use of tactics and techniques by adversaries. |
| Sub-Techniques | Sub-Techniques are specific description of the adversarial behavior to achieve a goal. |
| Risk Findings | Risk Findings is displayed in the MITRE ATT&CK Matrix in the Prioritization tab of the VMDR application. The Risk Findings score is the sum of vulnerabilities, and misconfigurations. |
Where can I get the list of MITRE ATT&CK Tactics and Techniques?
Currently, there are 14 Tactics and more than 150 Techniques. To know more about each Tactics and Techniques, refer to the MITRE ATT&CK webpage.
How does Qualys VMDR use the MITRE ATT&CK Matrix?
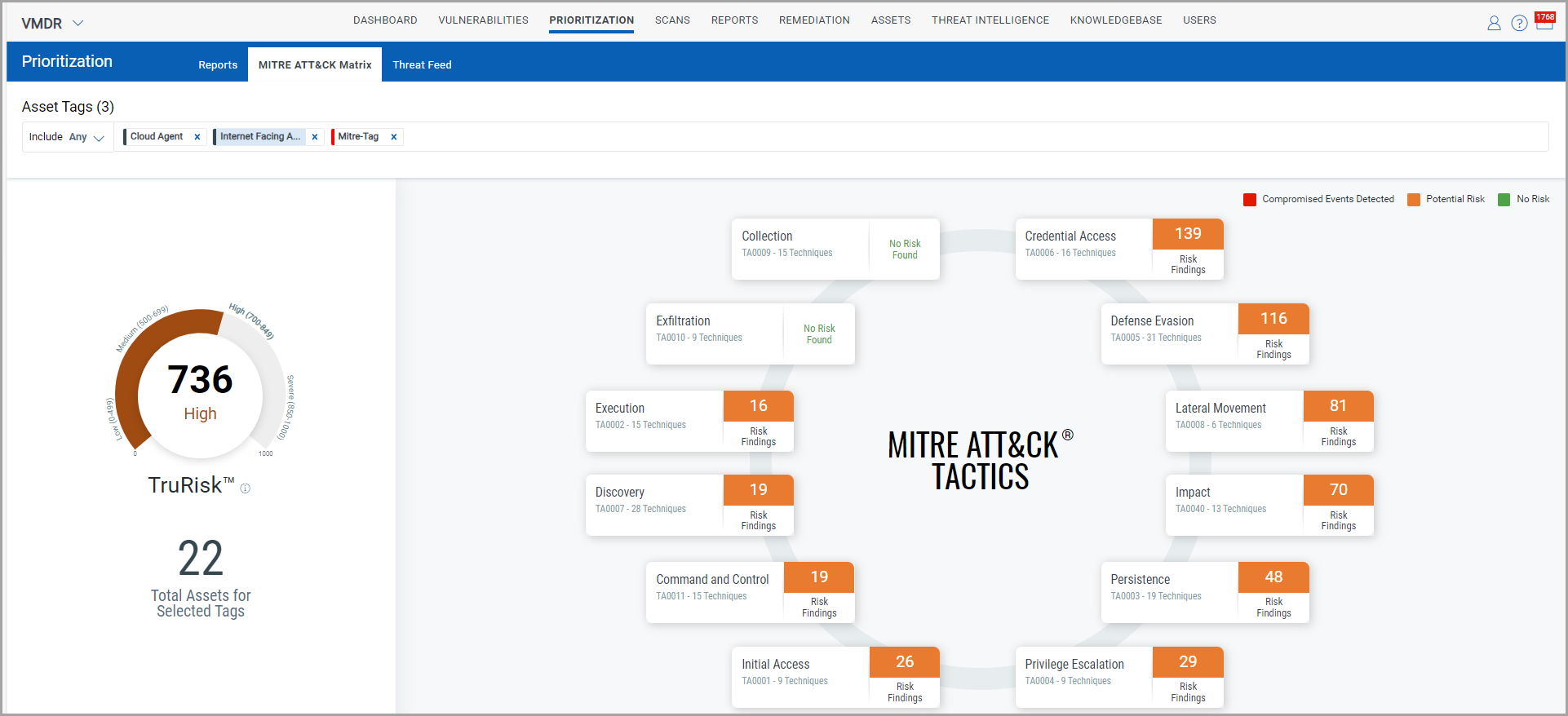
The VMDR application leverages the MITRE ATT&CK® framework in the matrix form based on the vulnerabilities (QID), misconfigurations (CID), and Endpoint Detection and Response (EDR) events. The MITRE ATT&CK Matrix in the Prioritization tab of the VMDR application shows a detailed view of Tactics, Techniques, and Sub-Techniques. To know more, see MITRE ATT&CK Matrix in VMDR Prioritization
The following pictorial representation of the matrix depicts the Tactics and Techniques based on the vulnerabilities (QID), misconfigurations (CID), and Endpoint Detection and Response (EDR) events:
With Qualys provisioning MITRE ATT&CK Matrix, you can not only detect, but also remediate the vulnerabilities and events. Thus, with the subscription of Qualys Policy Compliance and Qualys Endpoint Detection and Response applications, you can foster a secure and strong network security in your organization.
Additional Resources
MITRE ATT&CK webpage