MITRE ATT&CK Matrix in VMDR Prioritization
Consider a scenario where a threat actor wants to install malware to infect workstations on the network. The threat actor can initially use the Initial Access Tactic to gain network access. The Initial Access Tactic consists of 10 Techniques. The attacker can use any of these techniques to get network access maliciously. Once the attacker gains access, they can further use the Lateral Movement Tactic to infect the systems in the network. The Lateral Movement Tactic consists of 9 Techniques. To evaluate, determine, and remediate such attacks, the MITRE ATT&CK Matrix in the Prioritization tab helps you enhance the robustness of your organization's products and services.
Perform the following steps in the VMDR Prioritization tab to get in-depth information about MITRE ATT&CK Matrix for your Qualys Enterprise TruRisk™ Platform:
- Click MITRE ATT&CK Matrix.
- Select critical asset tags to prioritize your MITRE ATT&CK Matrix scope.
- Based on the asset tags selected, the MITRE ATT&CK Matrix page gives an interactive representation of the ATT&CK Tactics and Techniques. The following screenshot is an example of the Matrix page:
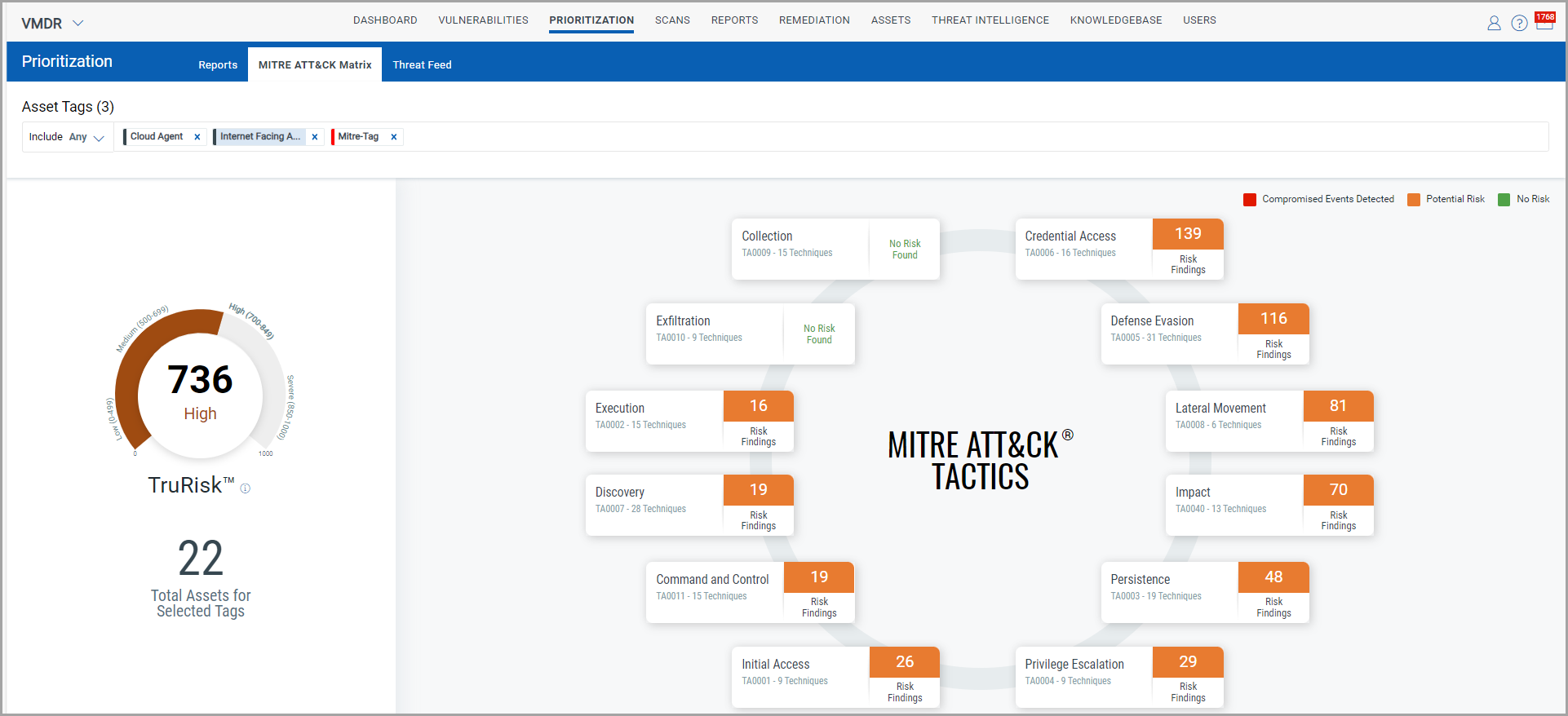
- Hover on any Tactic Names to get the list of vulnerabilities and misconfigurations on assets. The Technique name is listed along with the Risk Findings.
To explain the MITRE ATT&CK Matrix in detail, we have used the Initial Access Tactic and its Techniques as an example in screenshots.
- Click any of the Tactic Name. This Tactic Name lists its Techniques and its Risk Findings. The following screenshot is an example when the Initial Access Tactic is selected:
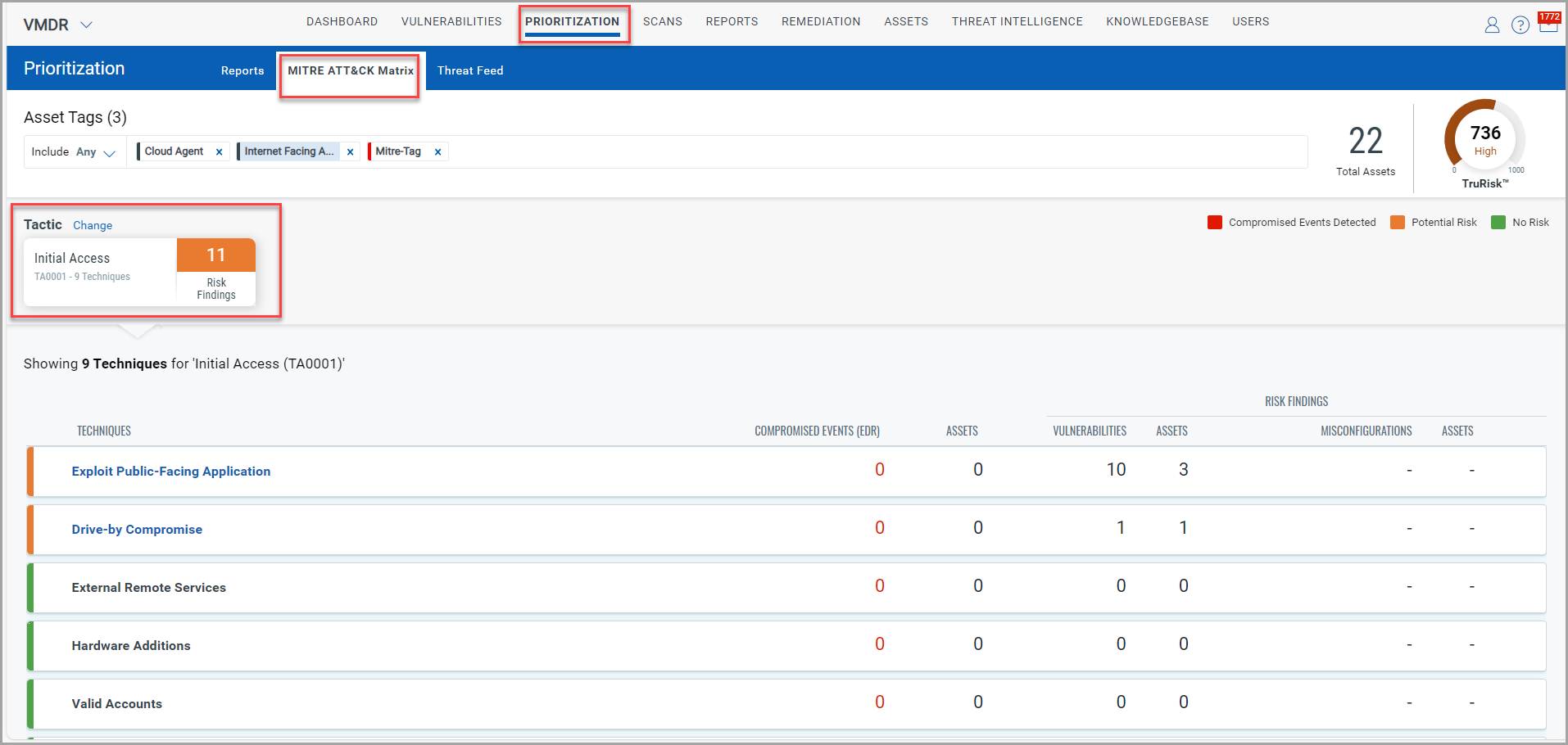
-
If you want more details about the technique with the highest Risk Finding, click the Technique Name. In this example, the Exploit Public-Facing Applications Technique has the highest number of Vulnerabilities and Assets. Thus, when you click a Technique Name, complete information about the technique name is displayed.
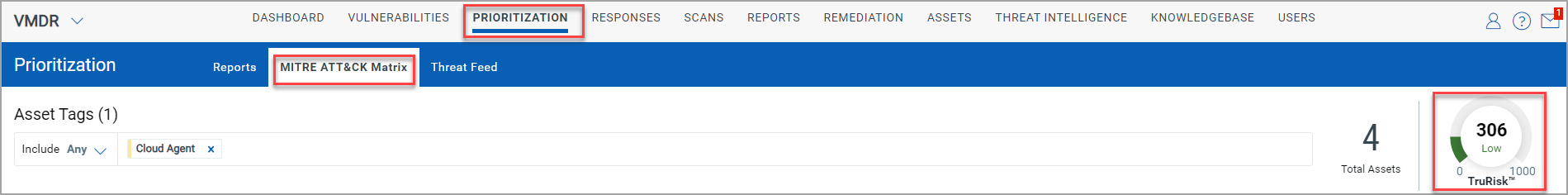
The following screenshot highlights the average Trurisk score for the selected assets:
The following screenshot highlights the information about each Technique widget:
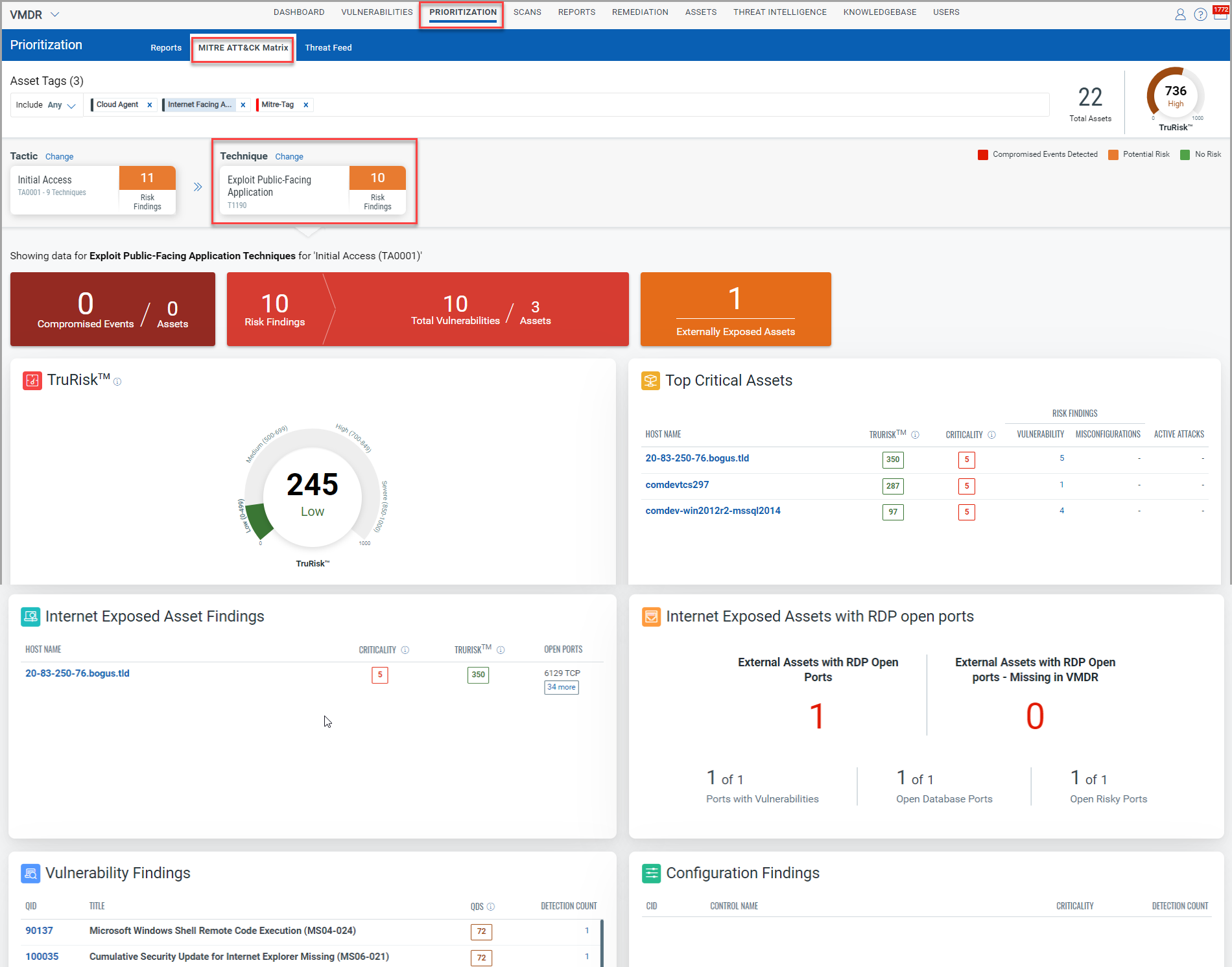
- TruRisk- The TruRisk widget shows the average assets score for the selected tags and the Technique. In the Technique widget screenshot, the average score is 245.
- Top Critical Assets- The Top Critical Assets list the hostnames under the selected tags, their TruRisk Score, and assets with QIDs, tactics, and techniques.
- Internet Exposed Asset Findings- Internet-Facing assets are the most vulnerable assets. Using the system-defined Internet Facing Assets, the Internet Exposed Asset Findings widget lists the vulnerable hostnames, which, in turn, expedites the process of addressing vulnerabilities and securing your internal sensitive information.
- Internet Exposed Assets with RDP open ports- Threat Actors can use Open Ports for backdoor entries or system identification. The widget gives you the asset count by categorizing the data as-
- External Assets with RDP open ports: Gives the count of External Assets with RDP open ports for VMDR Application. If a value exists, click on the count, and you will be redirected to the Vulnerabilities page of VMDR.
- External Assets with RDP open ports - Missing in VMDR: Gives the count of External Assets with RDP open ports for non-VMDR applications. If a value exists, click on the count, and you will be redirected to the Inventory page of the CSAM application.
This widget also displays details of the ports with vulnerabilities, open database ports, and open risky ports.
- Vulnerability Findings- Click any of the QIDs listed in the Vulnerability Findings widget to get General Information about the Vulnerability, such as its Identification, CVSS Summary, Vulnerability Analysis, Exploitability, Patches, and Malware.
- Configuration Findings- The Configuration Findings widget lists the incorrectly configured controls.
Thus, the various widgets in the MITRE ATT&CK Matrix in the Prioritization tab help you continuously reevaluate your security configurations and secure your network.