Release 10.0
April 19, 2024
What's New?
New QIDs in the Release
The following new QIDs are introduced in the release:
| Vuln ID | Category | Title | Description |
|---|---|---|---|
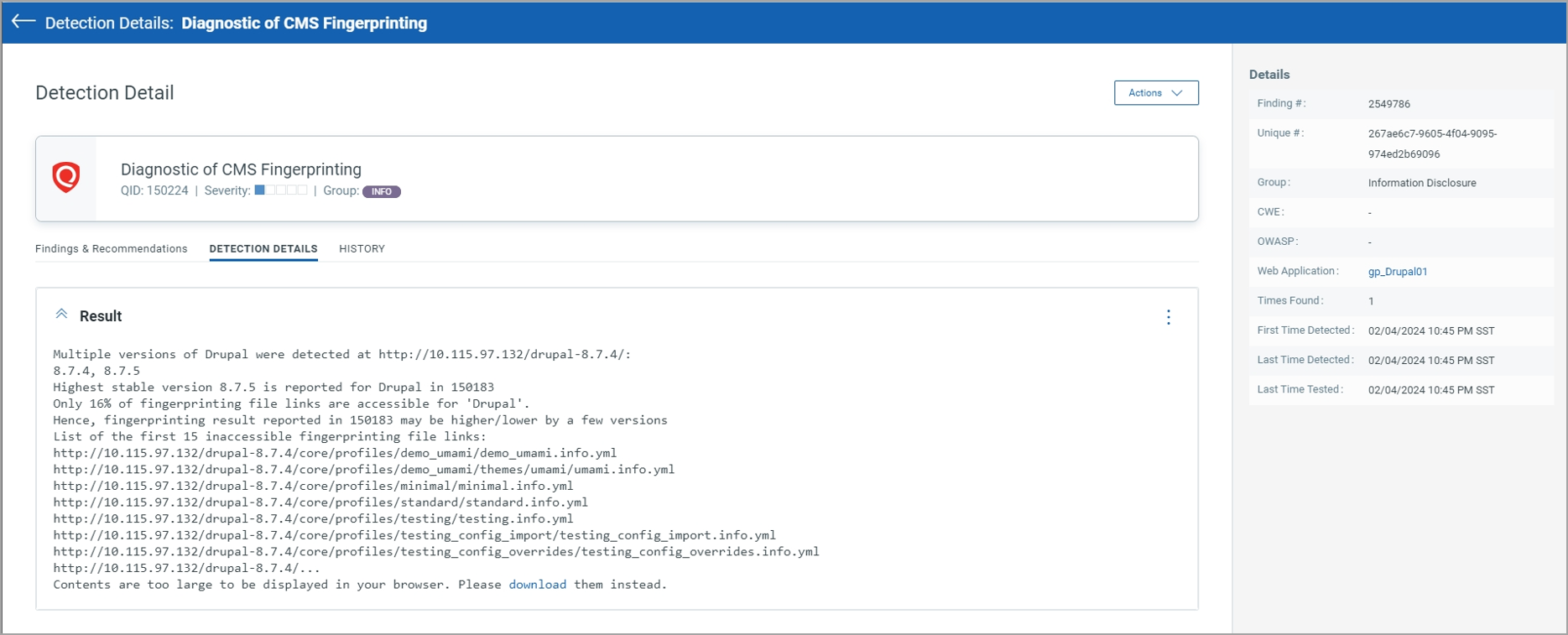
| 150224 | Information Gathered | Diagnostic of CMS Fingerprinting | This QID is reported when CMS fingerprinting finds at least one of the following scenarios: - Several possible versions of CMS are identified, in which case all the detected versions are listed. - If plugin files are not accessible, then list of top 15 inaccessible links will be reported. - Too many fingerprinting file links are not accessible, in which case the percentage of accessible links is given and the first 15 inaccessible links (at most) are listed. |
|
Example of report QID 150224
|
|||
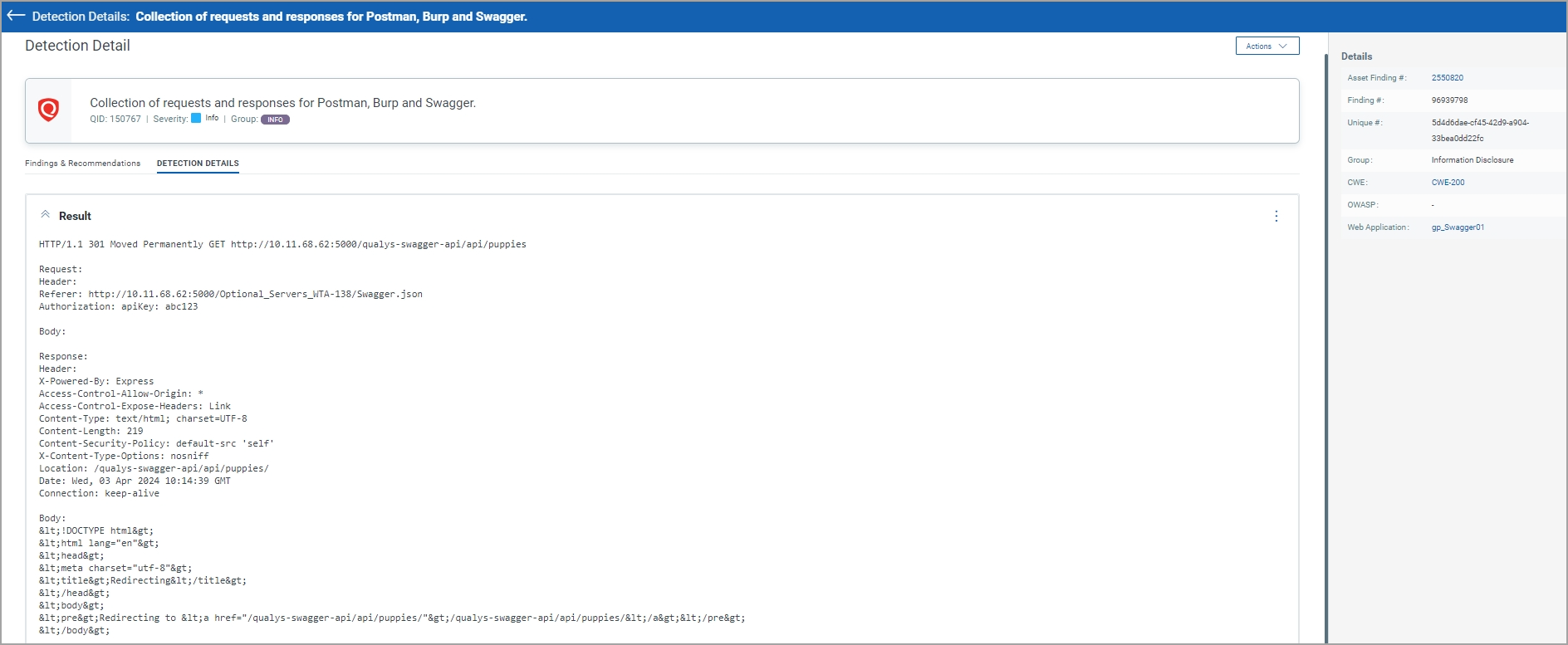
| 150767 | Information Gathered | Collection of requests and responses for Postman, Burp and Swagger | List of all the HTTP requests and responses collected as part of Postman, Burp and Swagger crawling. This includes URL, header and body for requests and responses. Note: If the response is not printed, please make sure to check the collection (Swagger/Postman/Burp) end points are not out of scope and there are no corrupted links. If WAS determines a Logout link in the collection the link will not be clicked/submitted and will not have a response recorded in this QID. First, 500 end points will be reported under this QID. |
|
Example of report QID 150767
|
|||
Improvements to Authentication via Microsoft SSO
With this release, we have added a browser option flag to enable web security. The flag can be enabled where authentication is failing to ensure compatibility with Microsoft Single Sign-On (SSO).
This flag can be enabled both at the web application level and the subscription setting. However, we recommend setting it at the web app level and adding it to the subscription if all applications within the subscription require the same Single Sign-On (SSO) configuration.
The browser option flag is not enabled by default. To enable the flag, contact your Qualys representative.
Enhanced Reporting Payment Page Form
With this release, we have added the detection of payment page forms. The form that WAS discovers during the scan containing CCNumber, CVV Code, and CCExpiryMonth fields is considered a payment form.
Details related to the form containing payment card information in a web application are reported in the information gathered QID—QID 153008.
HTTP Response Codes in Headers
With this release, the HTTP Response code is added to the QID response headers. HTTP response codes indicate whether the response received is valid. In case, the response code is unexpected
This change is applicable to all WAS QIDs for which the response headers are included in QID output.
The change is not applicable for the following QIDs:
- 150162
- 150398
- 150112
- 150180
- 150124
- 150181
- 151015
- 150150
Support for DNS Override
With this release, the NextGen WAS Engine supports DNS override functionality.
With the DNS override functionality, you can override DNS for the FQDN included in the web application target specification. This allows you to scan web applications that do not have a DNS entry or may have a different IP address in a non-production environment (development or QA) than in production.
Issues Addressed
The following reported and notable customer issues have been fixed in this release.
| Category/Component | Issue |
|---|---|
|
QIDs updated
|
QID 150010 reports external links and QID 150020 reports links rejected due to crawl scope or exclusion. In these QIDs, the reporting of URLs was incorrect. The URLs were getting reported without http:// or https:// . We have fixed this issue, and now the complete URL is getting reported, for example, http://www.example.com/ |
|
WAS Scan
|
We have fixed an issue where the WAS scan crashed during the discovery of links. The issue is caused when a response larger than the buffer length is received. Now, the buffer length is increased. If the response length exceeds the buffer size, the URL is truncated. |