Creating Custom QID Scripts
The CAR application is now closely integrated with the VM/VMDR application. The integration between CAR and VMDR allows you to create custom QIDs for vulnerabilities unique to your environment. You can identify potential risks in first-party and open-source software using VM/VMDR and CAR integration. You can create custom vulnerability definitions using detection scripts in CAR application, providing a comprehensive overview of all vulnerabilities in your environment.
There are three ways to create a Custom QID script. You can either enter a script manually. You can upload a script from your local machine, or you can also import it from GitHub.
You can create up to 5000 Custom QIDs per subscription.
You can execute the Custom QID scripts only on the assets enabled for the VM/VMDR application.
Let us take an example of creating a Custom QID by providing the script manually and choosing Linux as a platform.
Creating Custom QID Scripts
Follow these steps to create a Custom QID:
1. Navigate to Scripts > Scripts > Create > New Script.
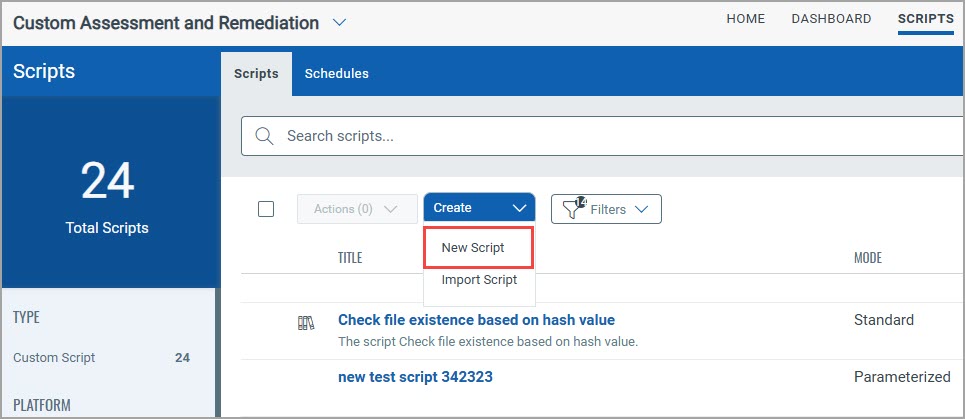
A Create New Script page is displayed.
2. In the Create New Script, provide Name, and Description.
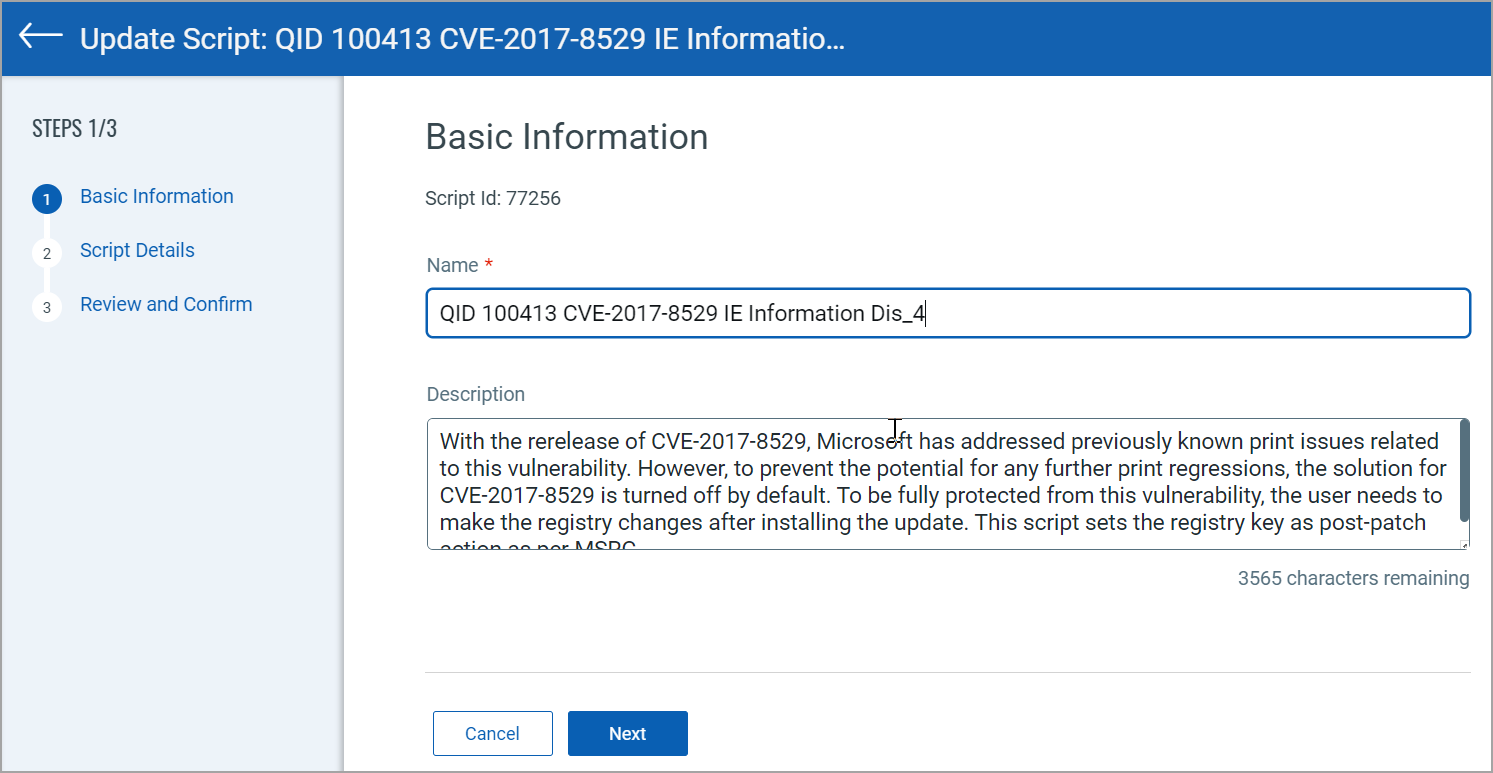
The Name of the script serves as the QID title by default. However, it can be customized.
The Description is a script description that serves as a vulnerability description. It is a part of 'Detection Summary' under 'Vulnerability Details'.
3. Click Next to navigate to Script Details.
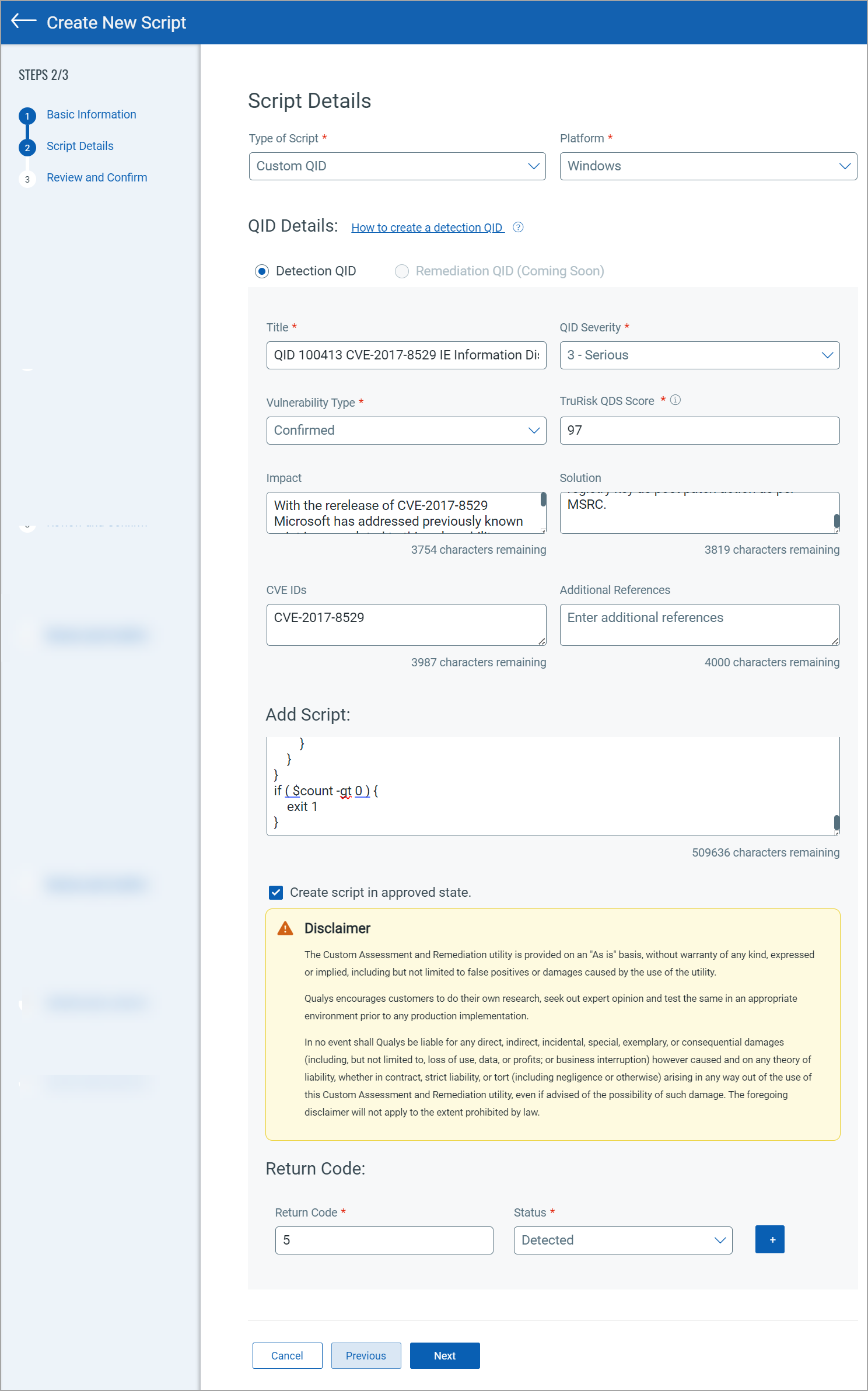
4. On the Script Details page, select Custom QID from the Type of Script.
The Detection QID is automatically selected.
5. Select Platform (Unix, Windows, Linux, MAC).
6. Provide the inputs for QID Details,
-
Title: Provide a title to your QID.
-
QID Severity: It is a QID Severity. You can select from values 1 to 5.
-
Vulnerability Type: Select the Vulnerability Type as Confirmed, Potential, or Information Gathered.
For Vulnerability Type Potential and Confirmed, you can provide the TruRisk QDS Score. However, for Vulnerability Type Information Gathered, you can not provide the TruRisk QDS Score.
-
TruRisk Qualys Detection Score (QDS): Provide TruRisk QDS score.
-
Impact: Provide the details of the possible outcome if the vulnerability is exploited.
-
Solution: Provide a verified solution for the impact.
-
CVE IDs: Provide a CVE ID that is associated with a specific QID.
-
Additional References: Provide a URL or an ID as an additional reference.
7. From Add Script, select the Scripting Language and Category from the respective drop-down lists.
8. Select the Scripting language in which you want to write the script.
For Windows, Unix, and Linux, the list of Scripting Languages is different.
On selecting Linux or Unix as a Platform, you get the scripting languages such as Lua, Perl, Python, and Shell in the drop-down list.
Similarly, for Windows, we support scripting languages such as PowerShell-Command, PowerShell-Script, Python, and VBScript.
9. Select a Category to label the script based on the use case.
10. Specify the Timeout Limit in seconds, minutes, or hours. The Timeout Limit lets you define how long a script must be in execution.
The Timeout Limit for all Windows assets, Linux assets, and Unix assets range from one second to 48 hours. The default value is 300 seconds.
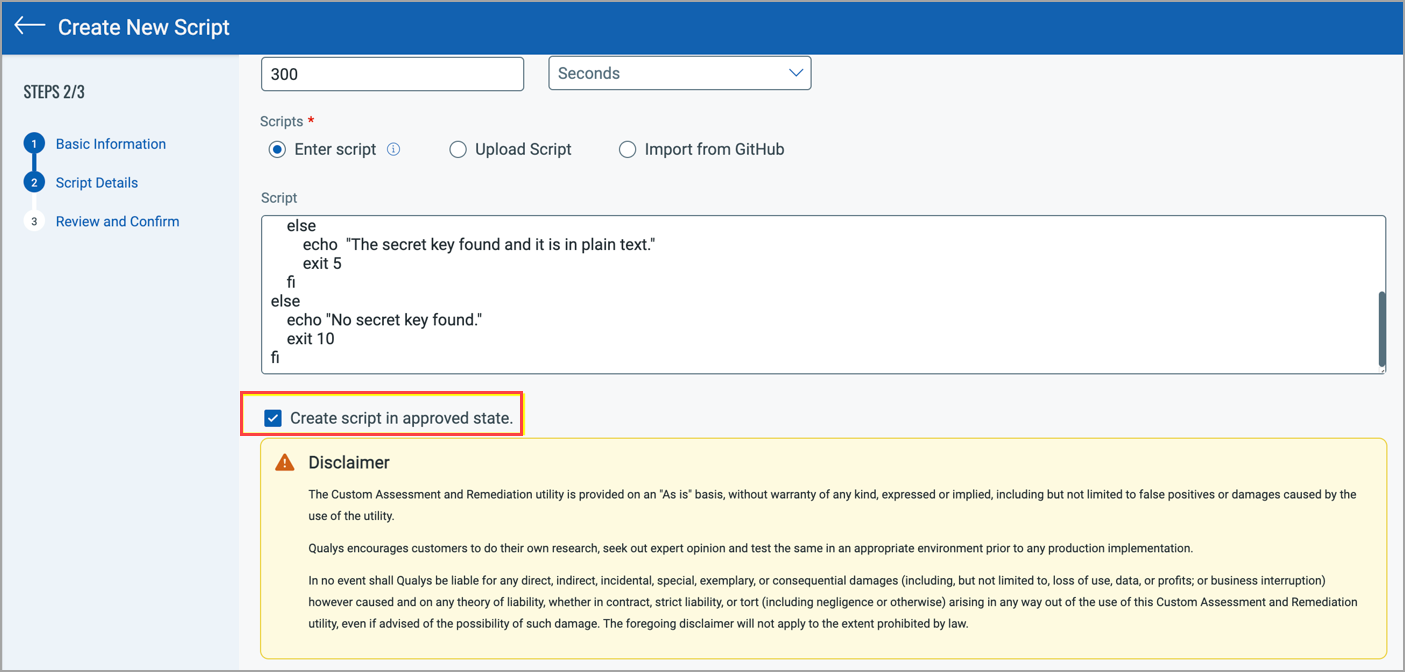
11. In Scripts, manually provide the script by typing or copying and pasting it from another resource.
You can also upload the script from a local machine.
Or you can import the script from GitHub by directly connecting to your public or private repository.
12. Select Create Script in the Approved state.
This option is available only for the manager role.
The user with any other user role must get the script approved by the authorized user. You can view the details on Qualys CAR RBAC.
13. Enter the Return code and the Status based on the script you provide.
You can provide multiple return codes for multiple scenarios.
QID is marked detected or not detected based on the exit code returned by the script you provide. We recommend you customize the script to return different exit codes based on your requirements.
You may want to use multiple exit codes in a custom QID script for detection. Therefore we added the capability to add multiple return code mappings while creating a custom QID.
#!/bin/bash
SECONDS=0
lib_openssl_ver(){
lib_list=$(find / -name $1 -xdev ! -fstype nfs ! -fstype nfs4 ! -fstype cifs ! -fstype smbfs ! -fstype gfs ! -fstype gfs2 ! -fstype safenetfs ! -fstype secfs ! -fstype gpfs ! -fstype smb2 ! -fstype vxfs ! -fstype vxodmfs ! -fstype afs ! -fstype acfs 2>/dev/null)
for i in $lib_list
do
if ! command -v strings &> /dev/null
then
ver=$(grep --text -o 'OpenSSL [[:digit:]][^ ]*' $i 2>/dev/null |sort|uniq|tail -n 1|awk '{print $2}' 2>/dev/null)
if [[ -n $ver ]]
then
echo "Path: $i" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
echo "Version(s): $ver" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
echo "----------------------------------------" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
ver_chk=$(echo "$ver"|grep -E "3\.0\.[0-6]" 2>/dev/null)
if [[ -n $ver_chk ]]
then
flag=$((flag+1))
fi
fi
else
ver=$(strings $i 2>/dev/null| grep -i -E "^openssl[[:blank:]]+[[:digit:]][^ ]*" 2>/dev/null|sort|uniq|tail -n 1|awk '{print $2}' 2>/dev/null)
if [[ -n $ver ]]
then
echo "Path: $i" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
echo "Version(s): $ver" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
echo "----------------------------------------" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
ver_chk=$(echo "$ver"|grep -E "3\.0\.[0-6]" 2>/dev/null)
if [[ -n $ver_chk ]]
then
flag=$((flag+1))
fi
fi
fi
done
}
echo "Detecting OpenSSL version in libssl.so* and libcrypto.so*" | tee /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
echo "----------------------------------------" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
flag=0
#Finding OpenSSL version in libssl.so*
lib_openssl_ver libssl.so*
#Finding OpenSSL version in libcrypto.so*
lib_openssl_ver libcrypto.so*
echo "vulnerabilitiesFound: $flag" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
duration=$SECONDS
echo -e "\n$(($duration / 60)) minutes and $(($duration % 60)) seconds elapsed in script execution" | tee -a /usr/local/qualys/cloud-agent/openssl_findings.stdout 2>/dev/null
(ls /usr/local/qualys/cloud-agent/openssl_findings.stdout >> /dev/null 2>&1 && echo -e "\nScan Result File: /usr/local/qualys/cloud-agent/openssl_findings.stdout") || echo -e "\nCan not create output file: /usr/local/qualys/cloud-agent/openssl_findings.stdout"
if [ $flag -gt 0 ]
then
exit 99
else
exit 100
fi
Return Code:
99:Detected
100: Not Detected
We recommend to avoid using the reserved operating system return codes.
14. Click Next to navigate to Review and Confirm.
15. From Review and Confirm, click Save to save the details. Or you can click Save and Create Schedule to create a QID scan schedule. After clicking Save and Create Schedule you are navigated to the Create Schedule page. For more information refer to Working with Scripts Schedules.
A QID number is generated.
Your Custom QID Script is created and you can view it on the Scripts Details.
To detect this custom QID on your Assets you can click Save and Create Schedule.
Once you select Save and Create Schedule you are navigated to Create Schedule. Provide the basic information like Schedule Name and Description and click Next.
The Custom QID is already selected. You can add the assets and click Next.
You can specify the date and time for script execution. You can also select a recurring type of schedule.
Once created, you can edit the script. However, you can not edit the Vulnerability Type while editing the script.
Next Step,
Execute the script. A job is created when you execute a script. For more information, refer to Executing Scripts.
Modify the Approved Script Content
The manager role can edit the content of the approved script.
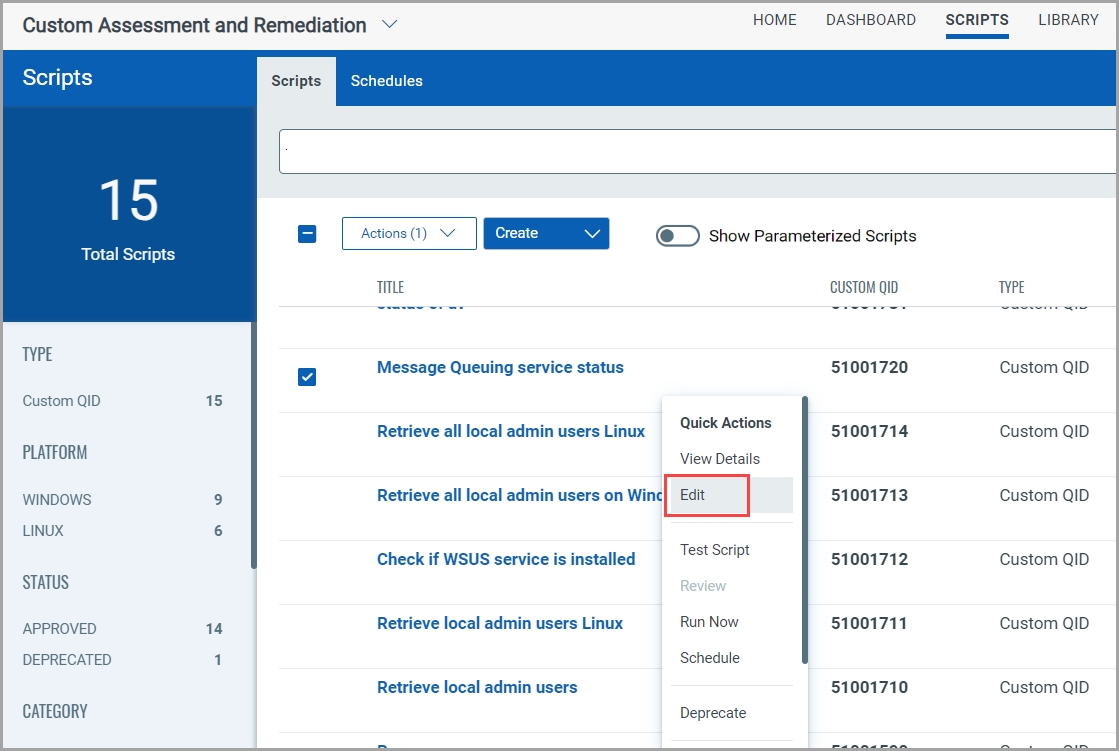
To modify the Approved script navigate to Scripts,
1. Select Quick Actions of the approved script.
2. Click Edit.
3. Click Next from the Basic Information page.
4. The Script Details page is displayed. To modify the script content start typing in the new content field.
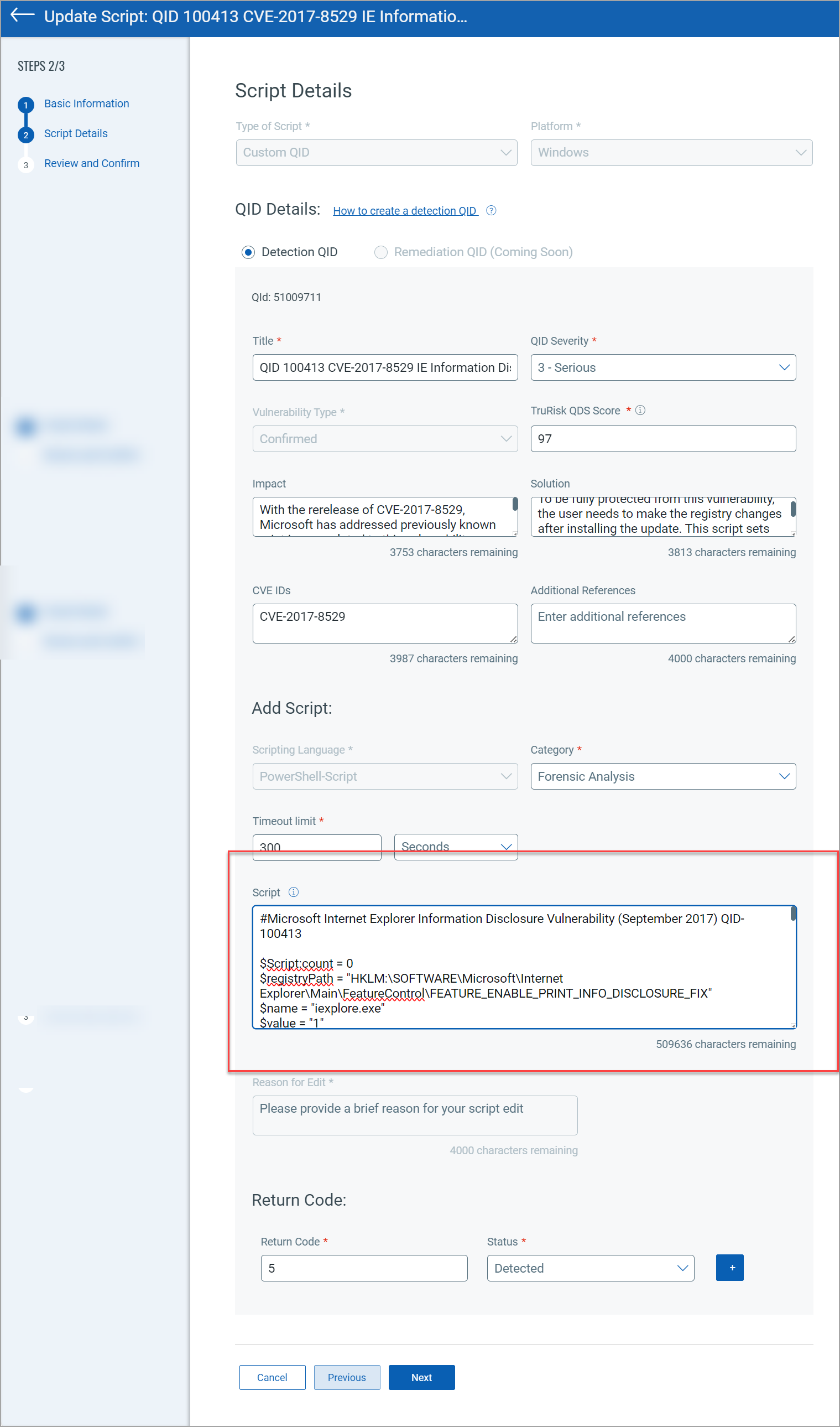
5. Edit the script and provide the reason for the modification.
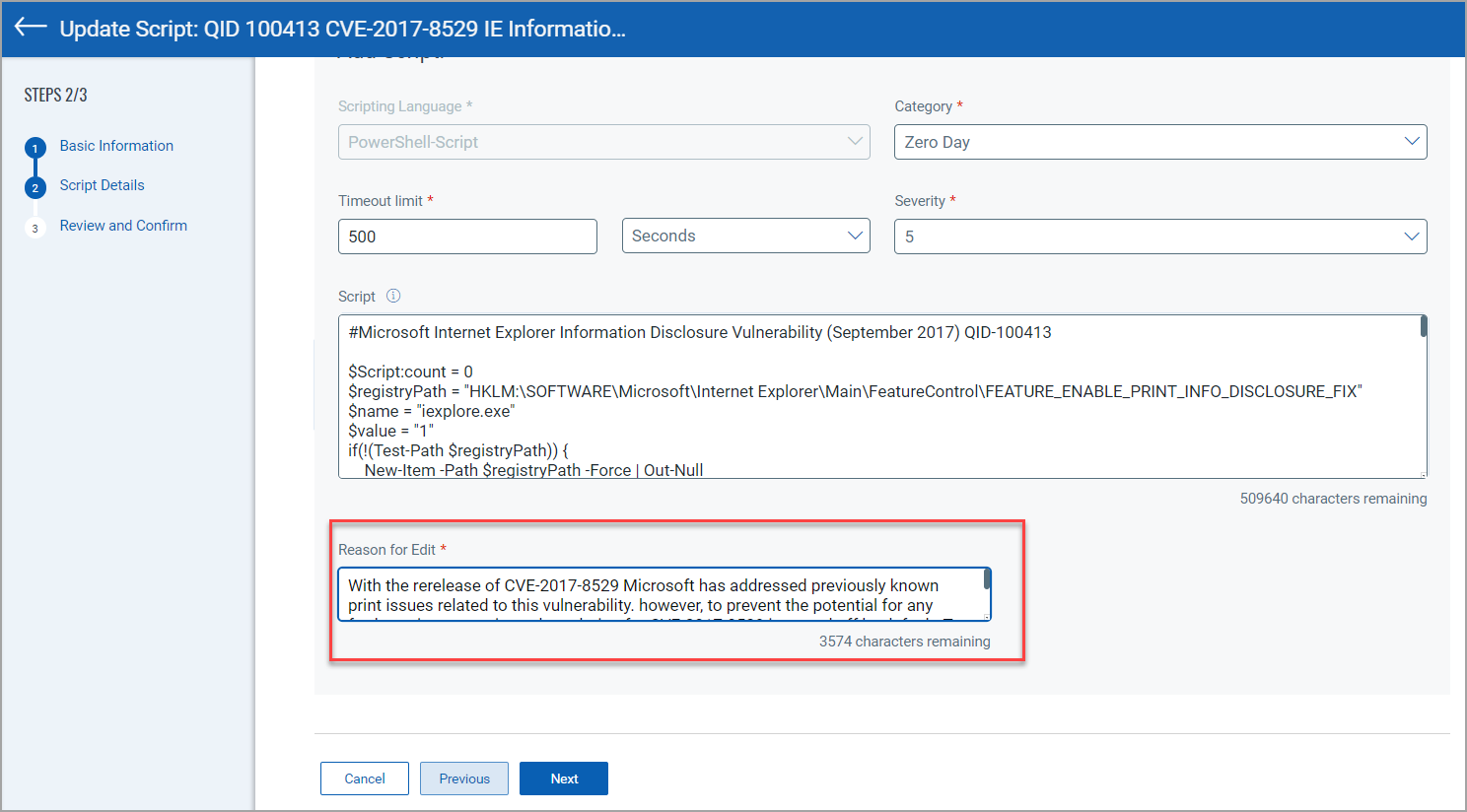
6. Click Next.
7. Review and Confirm page is displayed. Click Update to update the script modification.