Event Details
The Incident Details window displays the information about the following:
Summary
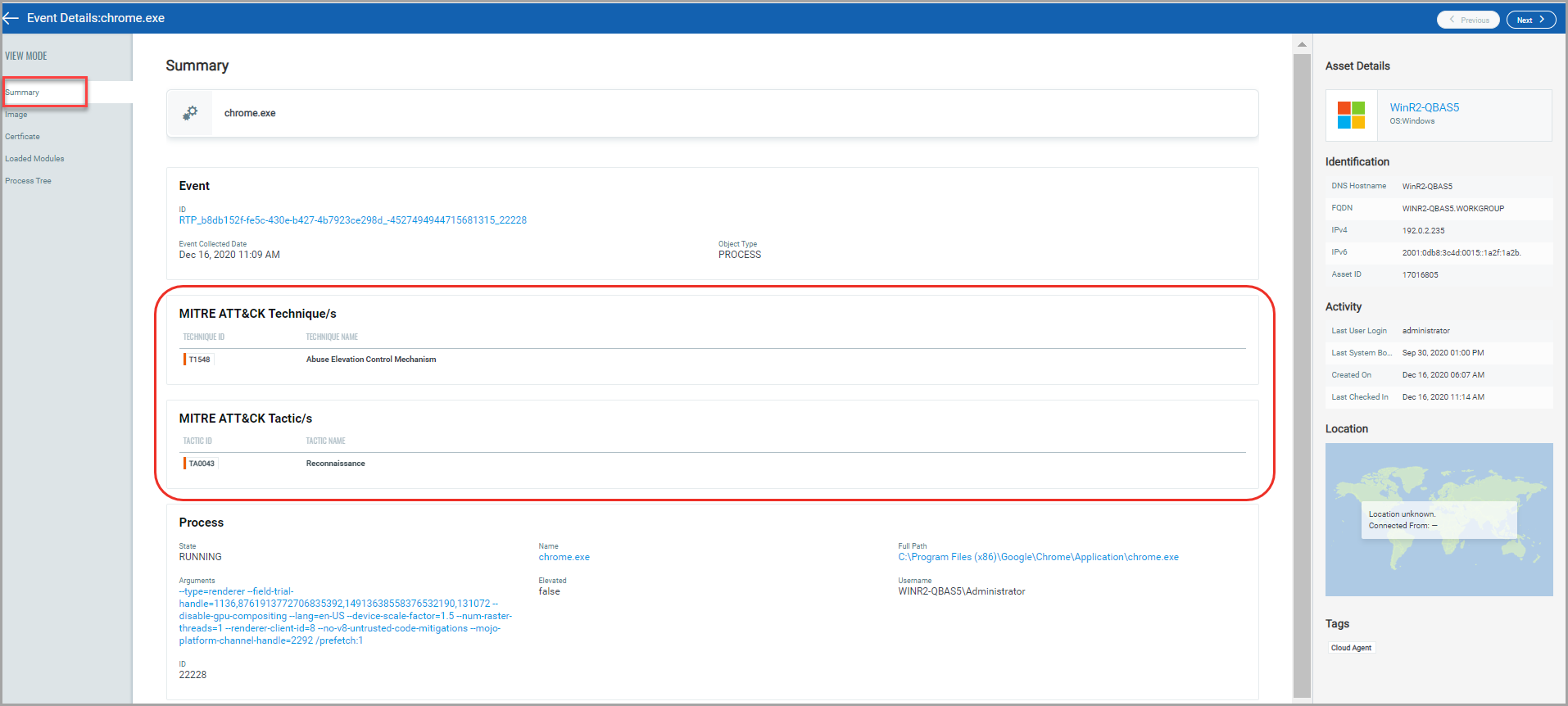
You can perform Remediation actions such as Quarantine File, Delete File, and Kill Process from the Summary section. For more information, see Remediation. The MITRE ATT&CK in the Summary section defines the tactics, techniques, and procedures that adversaries and malware leverage. EDR helps detect malicious behavior on the endpoint by evaluating the events in context with MITRE ATT&CK. Events registered on the agents are analyzed, and appropriate ATT&CK tactics and techniques are applied on the Event Details page.
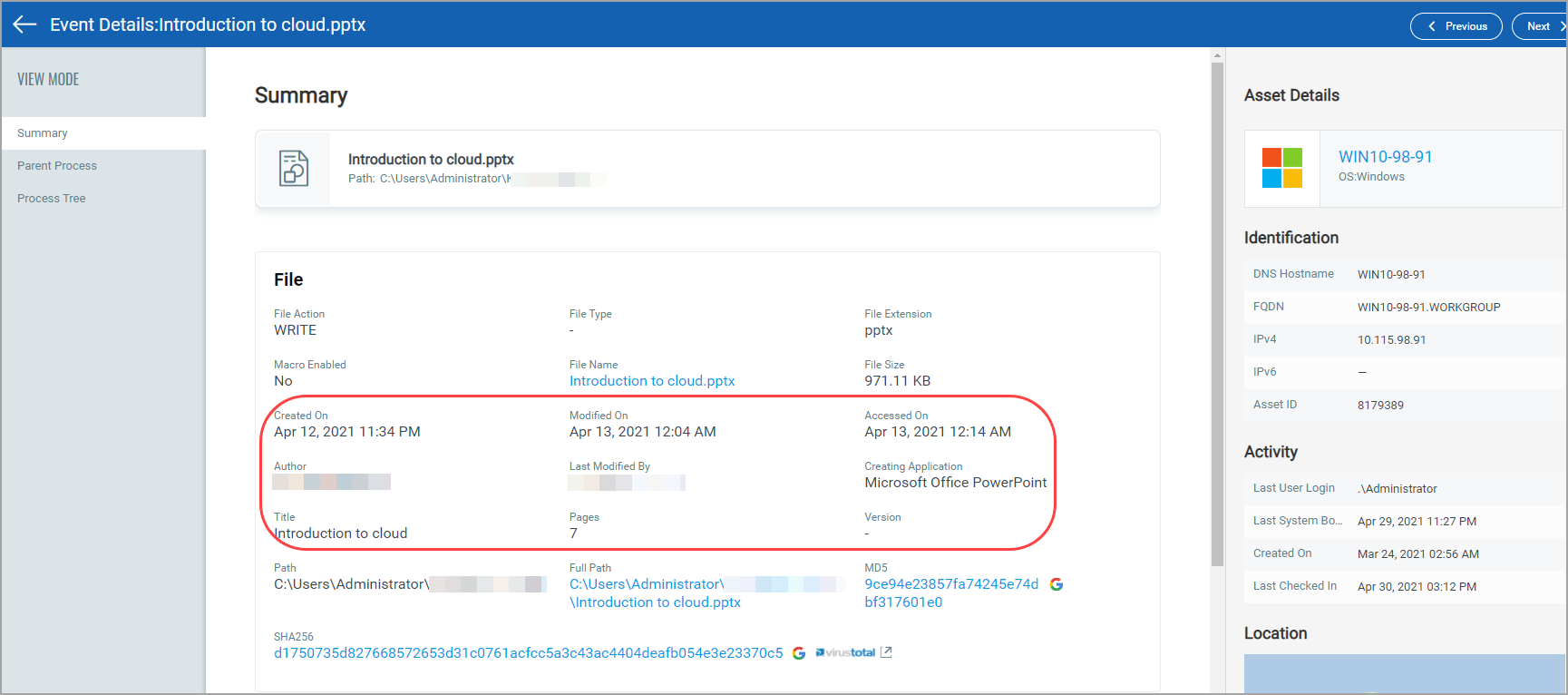
All the detected non-Portable Executable (non-PE) files are listed in the Events of the Hunting tab. Navigate to a non-PE file, and in the event details section, you can view the file's details and Parent Process and Process Tree details. For example, if it is a .pptx file, you will view the following details in your event details Summary:
Related Events
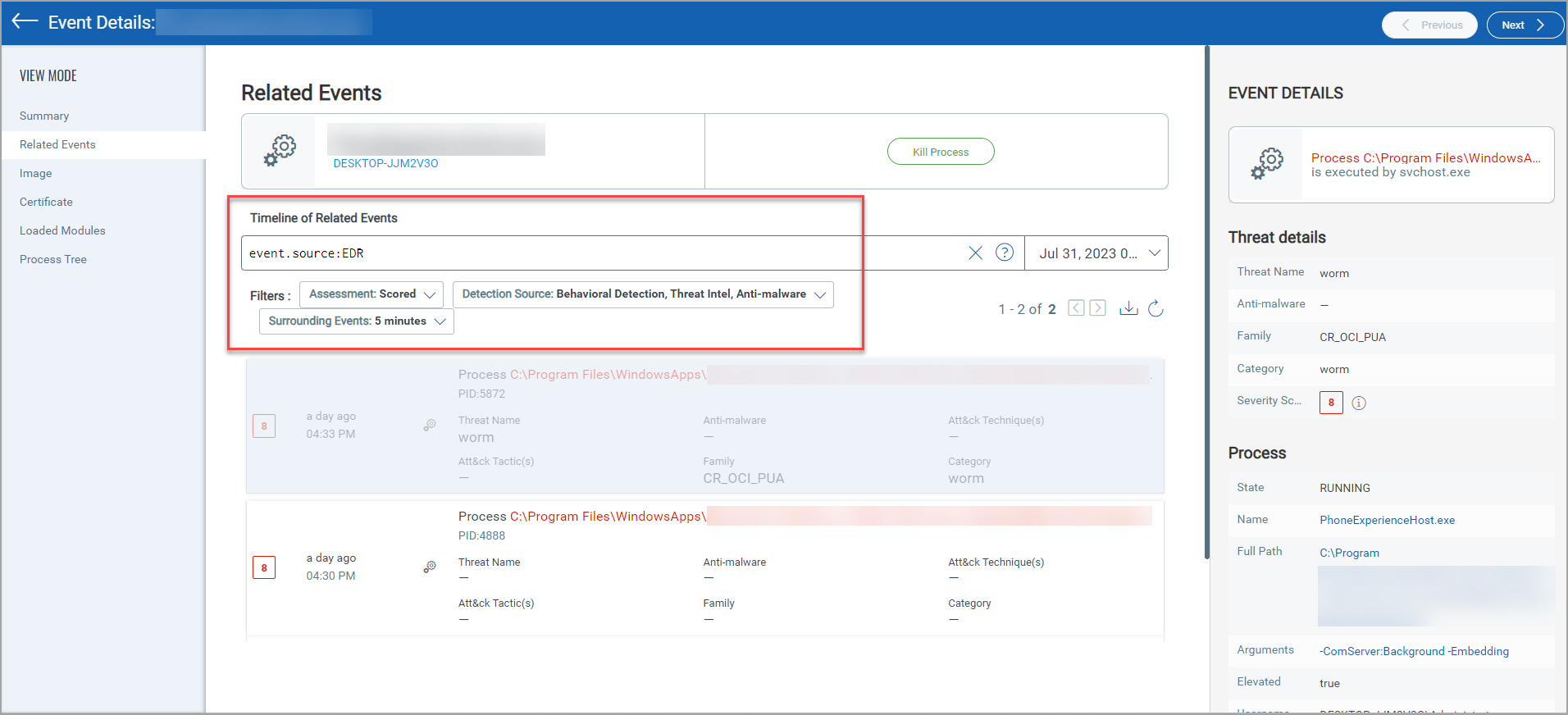
In the Related Events section you can filter the events based on the Assessment, Detection Source, and Surrounding Events. You can select all the three filters at a time. Alternatively, you can search for the detected events from the Search for events search bar using the Events Search Token. You can enhance the search results by selecting the timeframe from Last Month to Today. Select the drop-downLast 30 days to view the list of timeframe options.
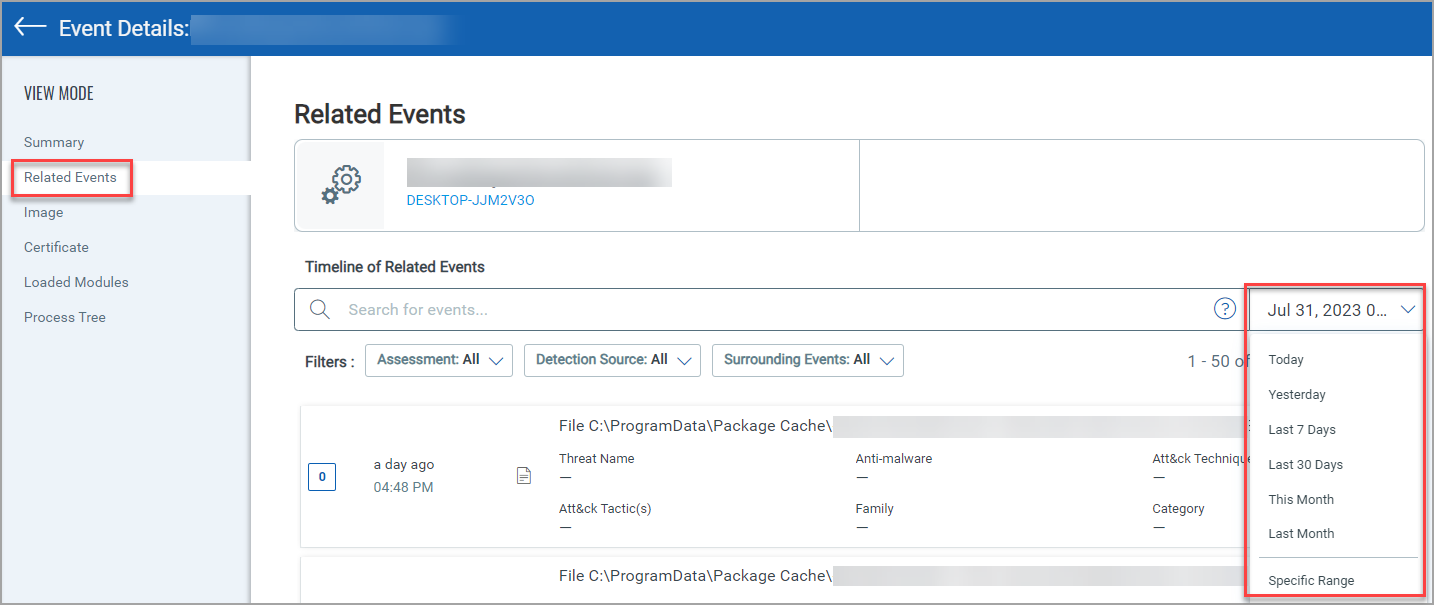
Assessment, Detection Source, and Surrounding Events filters in the Related Events section displays the list of event based on the selected options.
- Assessment: The Scored and Not Scored fields in the Assessment filter lists the events based on the severity score.
- Scored: Scored lists the events with the Severity Score from 1 to 10.
- Not Scored: Not Scored lists the events with the Severity Score 0.
- Detection Source: From the Detection Source filter you can select the threat source as, Anti-malware, Behavioral Detection, and Threat Intel.
- Surrounding Events: The 1 minute and 5 minutes timeframe lists the events that occured during this duration. The time calculation can be (+) or (-) the time selection. By default, the timeframe for an event is (+) or (-) 15 minutes.
You can select multiple threat source while using the Detection Source filter.
Loaded Modules
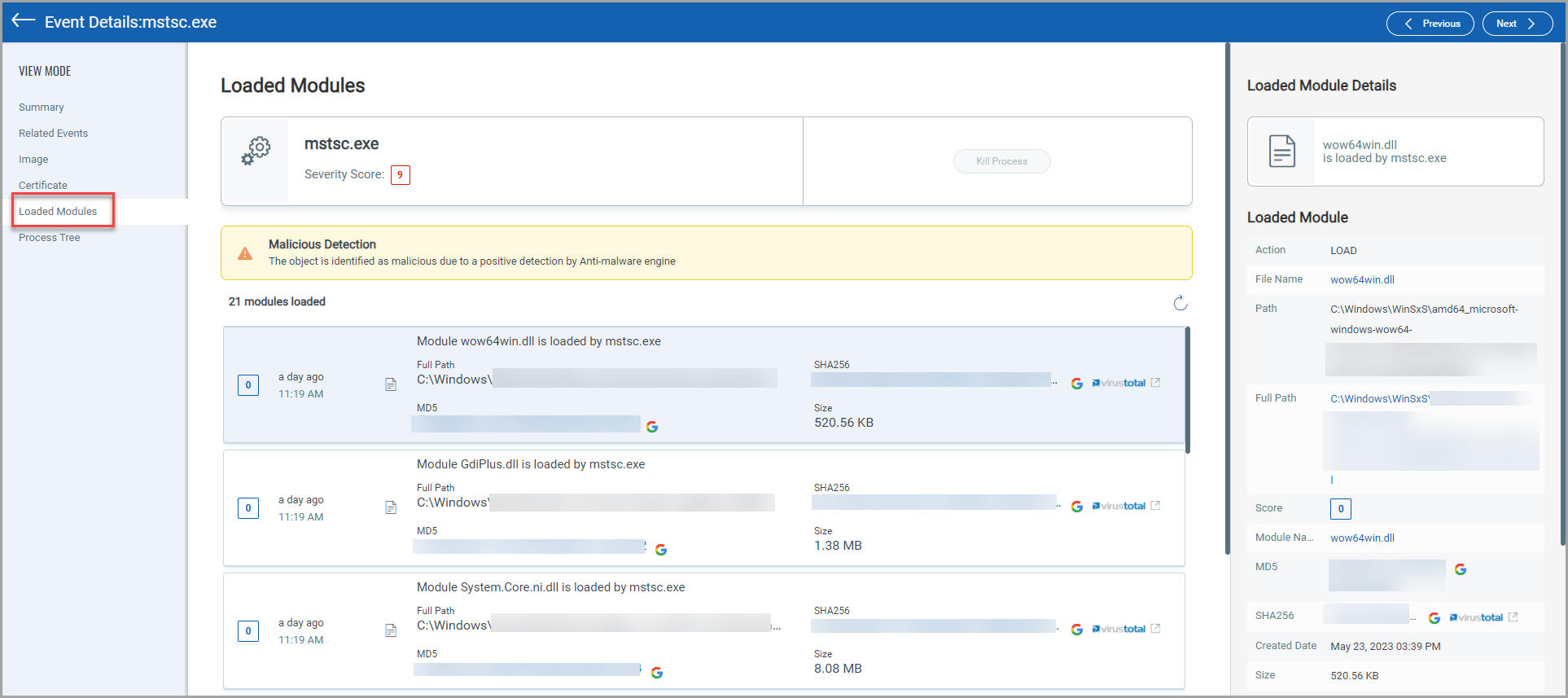
The Loaded Modules section displays the information of the loaded modules of each event. The section also displays if any malicious detection has been detected. Click the module name(s) listed in the table, the right-pane in the Loaded Modules section provides the complete module details. The following screenshot is an example of Loaded Module section:
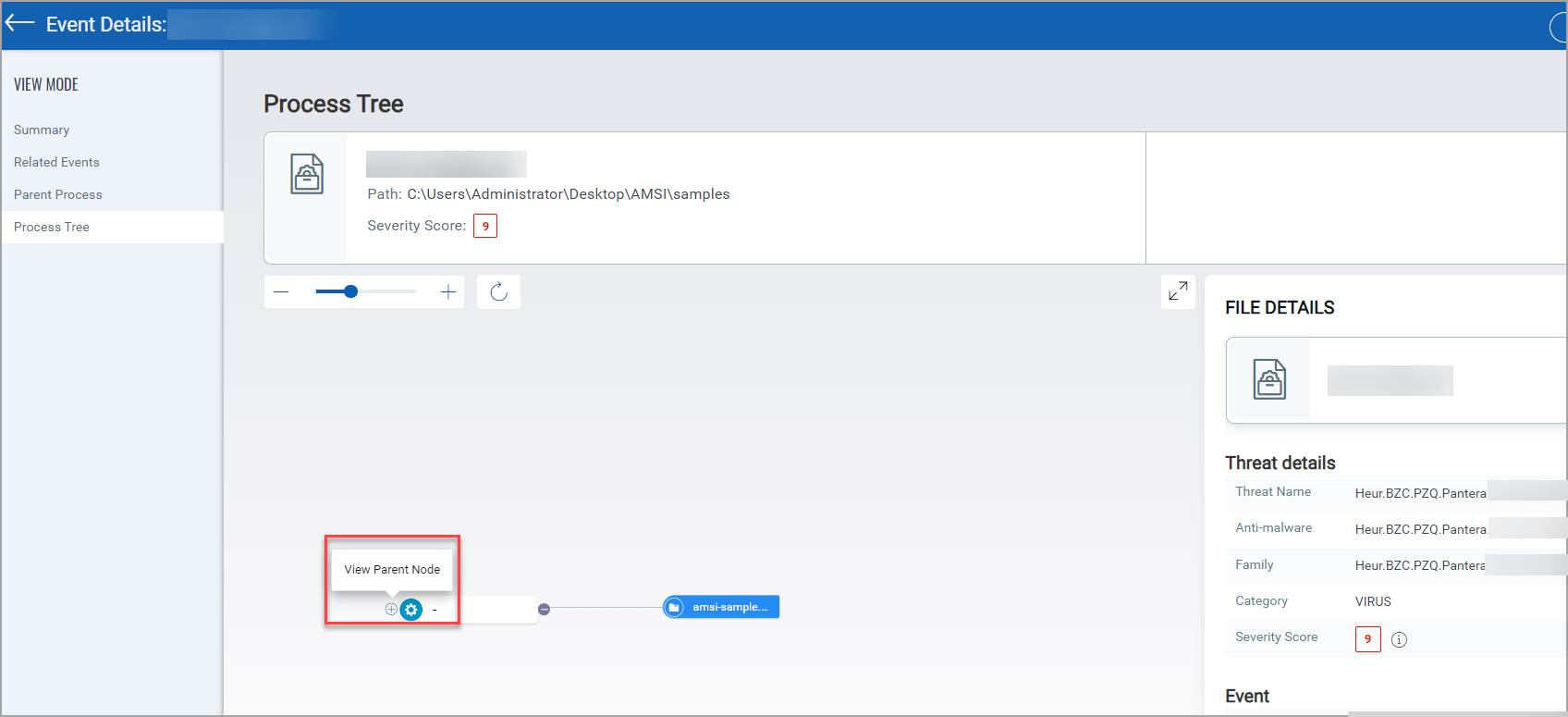
Process Tree
The Process Tree section displays the process tree for File and Process events in the Event Details section. The process tree displays all the related events of the selected event. In the process tree view, the selected event node is highlighted. You can traverse between the nodes by clicking a node in the hierarchy. You can click on the (+) and (-) to expand and collapse the tree nodes and display the related events. You can view the Parent Node, if a root has a parent node.