Network Attack Defense
Assume a scenario where an attacker performs a brute force attack on your systems, leading to the spread of malware across the network and causing damage to your organization. To prevent such attacks, we recommend implementing Network Attack Defense (NAD). NAD protects your Linux systems from attack types such as brute force, network exploits, password stealers, drive-by-download infection vectors, bots and Trojans.
The Network Attack Defense (NAD) detects and responds to host-based attacks by analyzing network traffic. It improves visibility and control of host-based network threats. As NAD is part of network monitoring, as an Administrator you can monitor the network attacks through EDR UI.
Linux Versions not Supported
- CentOS Linux 6 and 9
- Oracle Enterprise Linux (OEL) 6
- Red Hat Enterprise Linux (RHEL) 6 and 9
Prerequisites
- Qualys EPP is enabled
- Linux Agent 6.2.0 and above
- 64-bit Linux machines that use systemctl to manage services
- iptables package
Things to Consider before you Proceed
If the prerequisites are met, consider the following points before you start working on NAD:
- NAD uses port number 8887. If you have Firewall running on the same port, NAD will be unable to recieve network traffic. Thus, to avoid conflict NAD will not start if either firewalld or ufw is running
-
Incoming traffic routed through NAD will appear to be coming from a local IP address, even though it might come from an external IP.
-
When NAD is initiated or terminated, all connections on the protocols FTP/SSH will be terminated.
Using NAD with EDR
To implement NAD you need to perform the following steps on EDR UI and your Linux system:
Steps to perform on an existing Anti-malware Profile on EDR UI
- Select the Attack Techniques. This action ensures a security layer is added against the selected attack. The following screenshot is an example that displays the selected Attack Techniques:
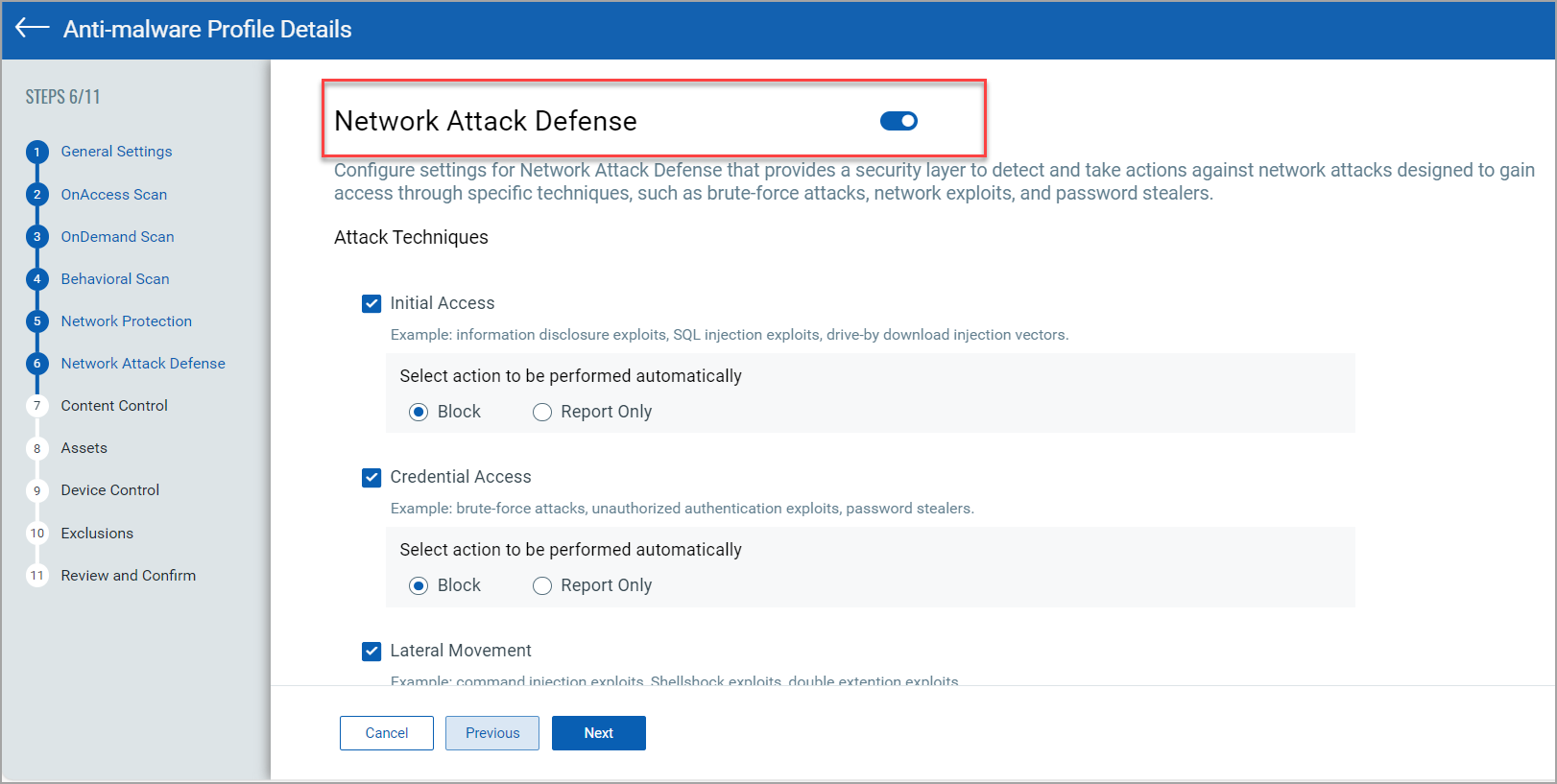
- Click Next until Step 11 and click Update Anti-malware Profile.
Step to perform on your Linux System
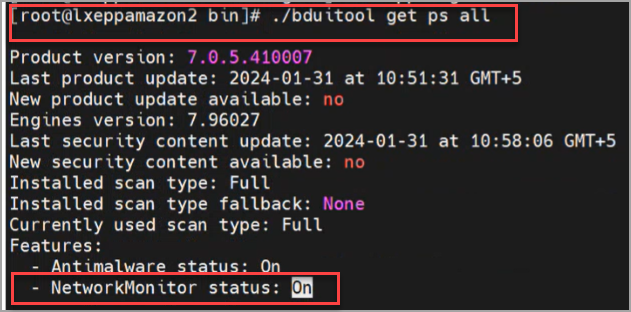
Run the following command to verify the network monitor is on
# .bduitool get ps all
The following screenshot displays the network monitor status:
Network Attack Defense Workflow
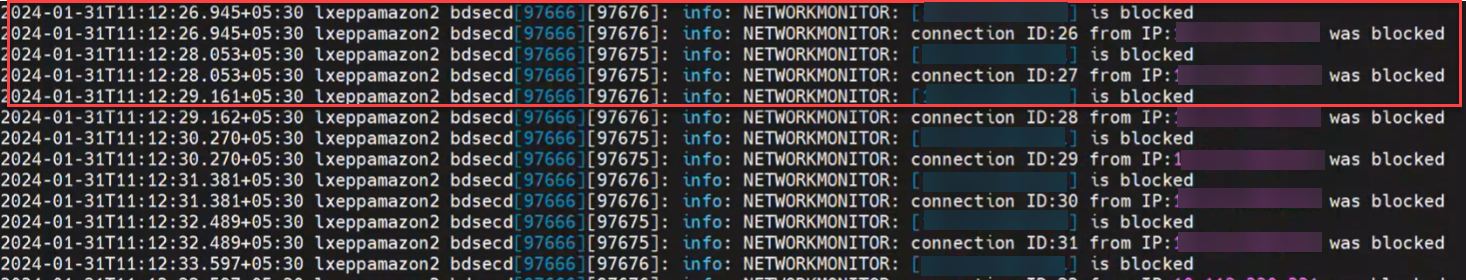
If a network attack is performed the network monitor will block and report the attacks that you selected from the Attack Techniques in EDR UI. The following screenshot displays NAD blocking an attack:
Generate Network Monitor Logs
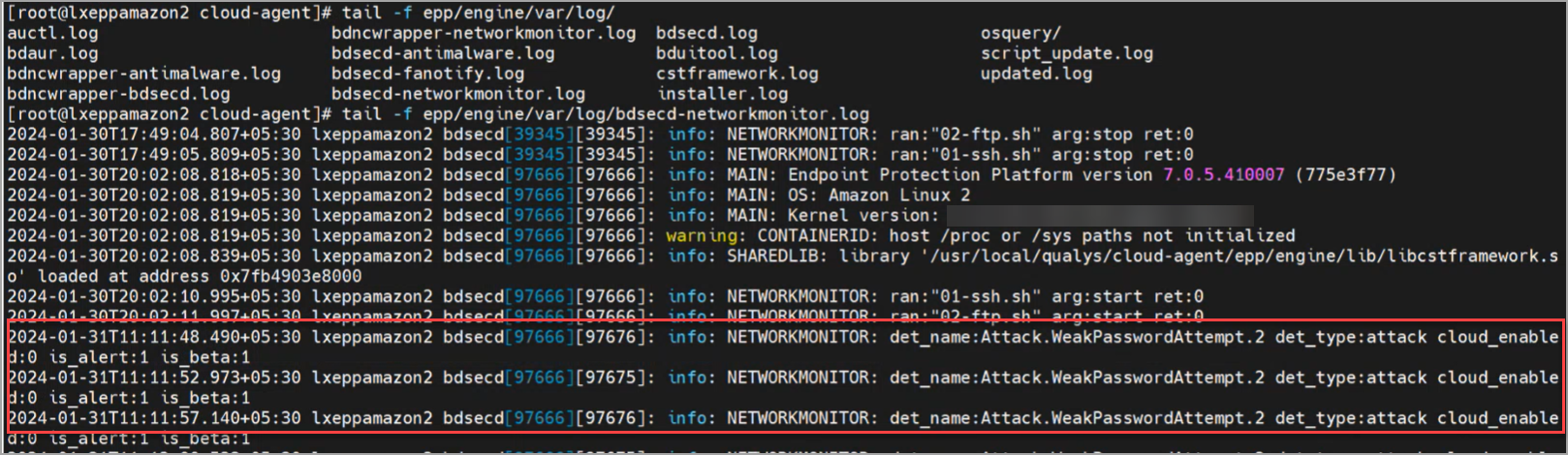
After the attack is blocked, execute the following command to generate network monitor logs:
# epp/engine/var/log/bdsecd-networkmonitor.log
The following screenshot displays the logs generated and the attack that occurred:
After you provide information in the Network Attack Defense, click Next to proceed to the next step - Content Control.