Getting Started with TruConfirm
TruConfirm is an automated exposure-validation layer integrated within the Qualys Enterprise TruRisk Management (ETM) platform that safely confirms whether prioritized exposures are actually exploitable in production. TruConfirm:
- Validates real-world exploitability on live production assets using safety-first, benign techniques
- Converts scanner findings into decision-grade evidence: exploitable now vs not exploitable/ blocked.
- Operationalizes the result as a native experience inside Qualys ETM.
TruConfirm is available as a separate tab within the ETM user interface. To access it, connect with your Technical Account Manager (TAM) or Qualys support.
Prerequisites
Before deploying TruConfirm, confirm the following prerequisites are in place:
- An active Qualys ETM subscription with VMDR enabled.
- For third-party scanner findings, configured connectors for Tenable (io/sc), Rapid7 InsightVM, or Microsoft Defender for Endpoint within ETM.
- TruConfirm requires network reachability from the ETM validation engine to the target assets on the relevant service ports.
- Out-of-Band validation: Target assets must be able to initiate outbound DNS queries and HTTP requests to the Qualys-hosted listener infrastructure. If egress filtering is in place, work with your network team to permit callbacks to the designated Qualys listener endpoints.
- TruConfirm operates in an agentless mode for network-reachable services.
- An Option Profile is created in VM.
TruConfirm maintains a continuously updated payload library. Not every CVE in the VMDR catalog has a corresponding validation payload. The ETM interface indicates per-finding validation support. CVEs without a payload remain at their original TruRisk™ score and are unaffected by TruConfirm processing.
Understand TruConfirm Validation
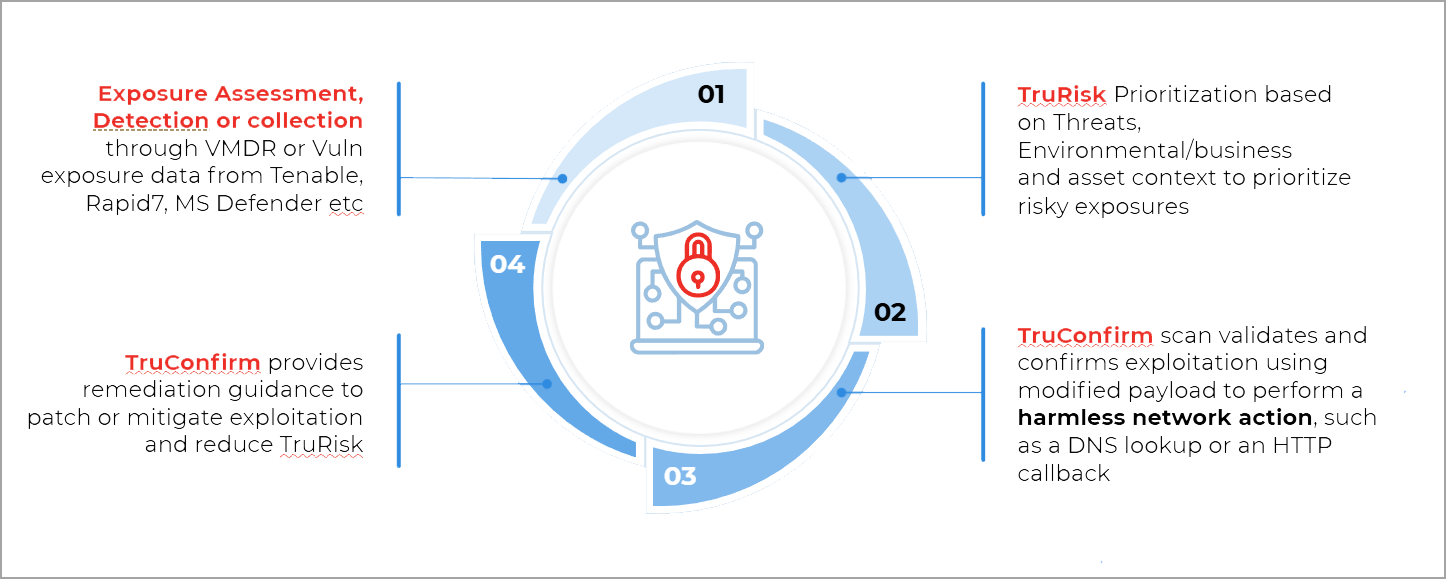
Understanding the four-stage loop before you run your first validation will help you interpret the result correctly.
TruConfirm selects the appropriate validation method: Direct Response, Cryptographic Verification, or Out-of-Band, based on the CVE's characteristics and how the target is expected to respond. You do not need to select a method manually.
For more information, refer to the TruConfirm Validation Workflow section.
Where Can You Launch TruConfirm Scans From
- From the left-navigation panel, go to TruConfirm tab > Scan tab:
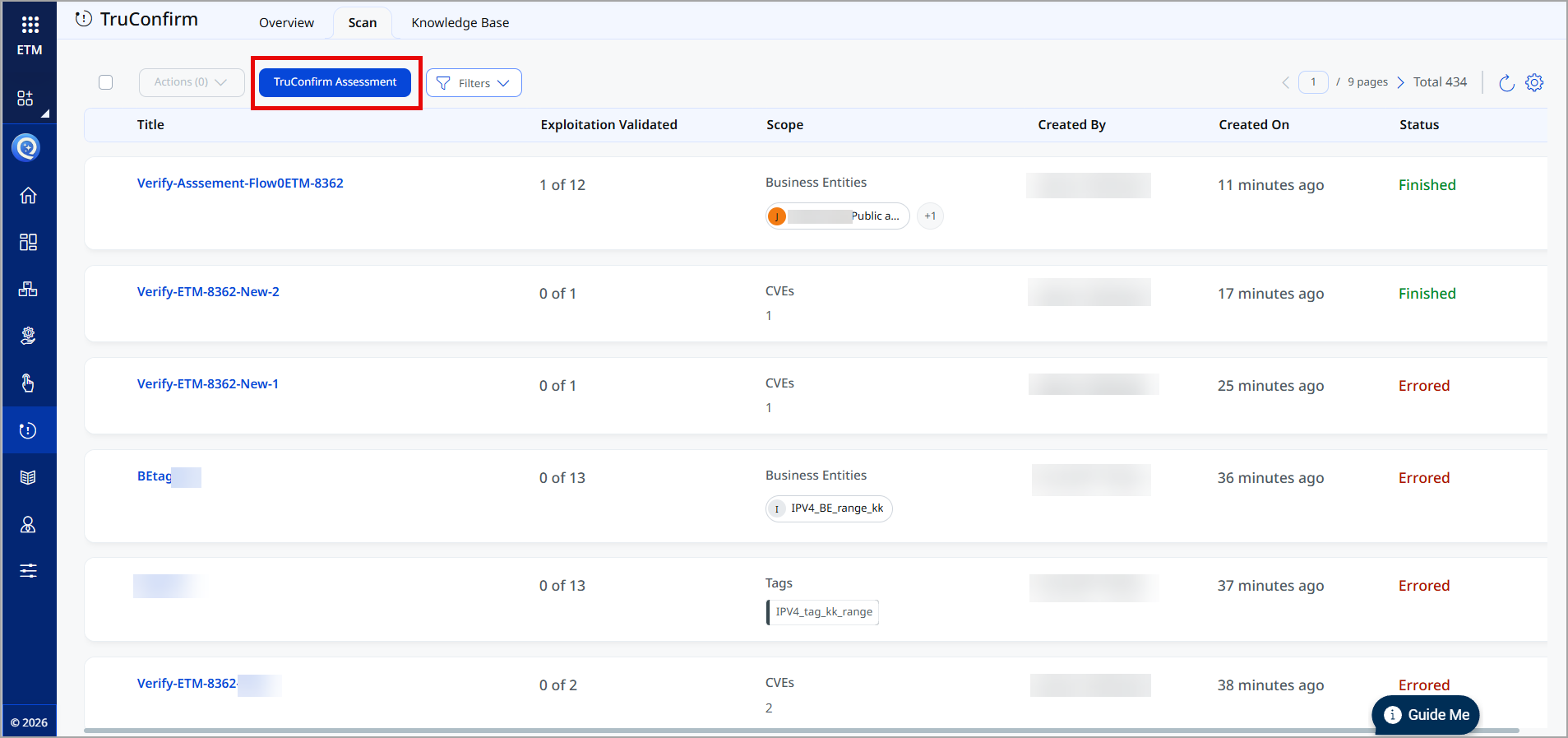
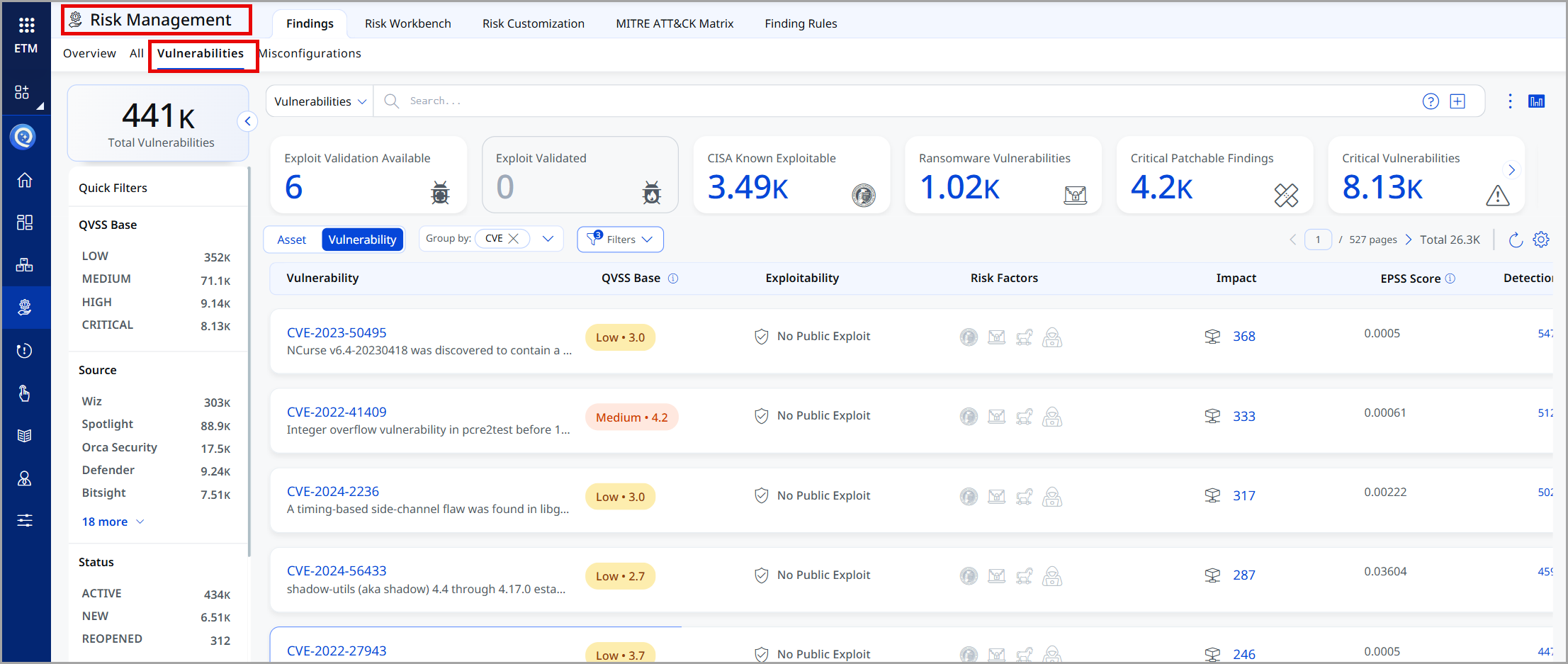
- From the left-navigation panel, go to the Risk Management tab > Findings > Vulnerabilities tab.
How TruConfirm Validation Works
TruConfirm selects the most appropriate validation method based on the specific CVE characteristics and the environment's expected response behavior. Following are the three methods, each designed for a distinct class of vulnerability:
What are Modified Benign Payloads?
The term Modified Benign Payload refers to a purpose-built interaction, not a traditional exploit. Traditional exploit code is engineered to gain unauthorized access, elevate privileges, or exfiltrate data. A Modified Benign Payload is engineered exclusively to elicit a vulnerability-specific, observable response that confirms or denies a reachable execution path.
TruConfirm End-to-End Validation Workflow
TruConfirm is positioned after initial detection and before active remediation, acting as the final verification filter that determines actual exploitability. The workflow proceeds in four stages:
Stage 1. Multi-Source Ingestion
TruConfirm is vendor-agnostic within the ETM ecosystem. It ingests exposure data and validates vulnerabilities discovered by Qualys VMDR, Tenable.io / Tenable.sc, Rapid7 InsightVM, and Microsoft Defender for Endpoint.
Stage 2. Exploitability validation
TruConfirm runs modified benign payloads against each unvalidated detection using the appropriate validation method (Direct Response, Cryptographic Verification, or OOB/Silent). Payloads are selected based on the CVE characteristics and the target's expected response behavior. This stage produces a definitive validation status: Confirmed Exploitable, Blocked by Control, or Inconclusive.
Stage 3. QVSS Score Update
The QVSS score is adjusted based on the exploit validation outcome.
- If a vulnerability is validated, the QVSS score is elevated, indicating a higher risk and the need for prioritized remediation.
- If the vulnerability is ruled out, the QVSS score remains unchanged at its original level.
Stage 4. ETM Remediation Guidance
ETM provides remediation guidance to patch or mitigation exploitation.
Related Topics