Understanding Trulens Home Page
The landing page provides a comprehensive, industry-tailored snapshot of the threat landscape most relevant to the you. It combines summarized intelligence, trending activity, and peer comparisons into a single, easy-to-navigate view. The page is divided into four major sections namely 20 Threat Actors, Trending CVEs Impacting You, Assets impacted by trending CVEs, Peer & Performance Benchmarking, and Top 5 Threat Categories in your industry each designed to answer a key question about the customer’s risk and threat environment.
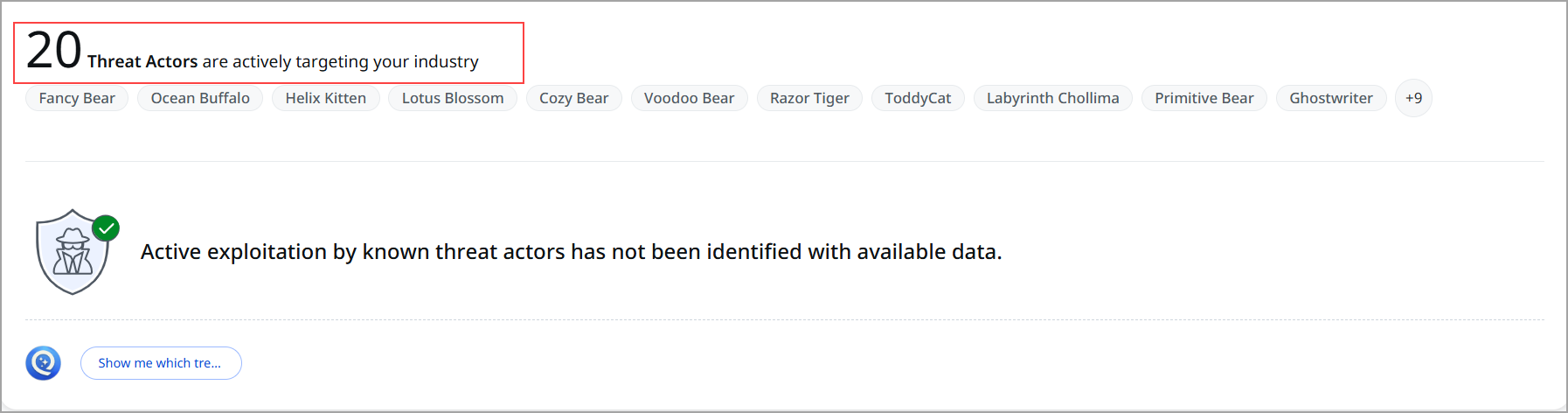
20 Threat Actors
This section provides a high-level summary of threat actor activity relevant to your industry. It highlights the number of known adversary groups that have historically targeted organizations in similar sectors and indicates whether there is evidence of active exploitation against your environment.
You can view 20 known threat actors are associated with attacks against organizations in your industry. Examples listed include Fancy Bear, Ocean Buffalo, Helix Kitten, Lotus Blossom, Cozy Bear, and Ghostwriter. These names represent tracked adversary groups commonly referenced in threat intelligence databases.
You can explore further details by selecting Show me which threat actors, which expands the view to provide deeper intelligence and navigates to CyberRisk Agent ROCky.
Overall, this section helps users quickly understand who might target their industry and whether those actors are actively exploiting vulnerabilities, enabling informed prioritization of security monitoring and risk mitigation.
Trending CVEs Impacting You
This section highlights recent and relevant security vulnerabilities (CVEs) that may affect your environment. Its purpose is to help you identify vulnerabilities that are currently gaining attention in the cybersecurity landscape and determine whether they require immediate action.
The search bar helps to look up a specific CVE identifier. This makes it easy to investigate known vulnerabilities and check whether they are relevant to the organization’s assets or technology stack.
You can use the three filtering options that organize vulnerabilities by their level of urgency and relevance:
- Trending
Displays vulnerabilities that are currently receiving significant attention across the security community, often due to increased discussion, exploitation attempts, or rapid adoption in attack campaigns. - Actively Exploited
Lists vulnerabilities that are confirmed to be exploited in real-world attacks. These typically require immediate prioritization for patching or mitigation. - Newly Added
Shows vulnerabilities that have been recently published or added to the platform’s vulnerability intelligence database.
The View All link opens the complete vulnerability list, allowing deeper analysis and investigation.
Overall, this section provides a quick, intelligence-driven overview of high-visibility vulnerabilities, helping security teams prioritize remediation efforts and maintain awareness of emerging threats.
Assets impacted by trending CVEs
This dashboard helps you quickly understand which of your organization's assets are exposed to the most dangerous and actively trending vulnerabilities right now.
Trending CVEs: The latest high-risk vulnerabilities that are gaining rapid attention in the cybersecurity community. These are selected based on factors such as:
- New exploit code being released
- Active exploitation in the wild
- High EPSS (Exploit Prediction Scoring System) scores
Assets Impacted: The total number of your devices, servers, cloud instances, containers, applications, or other assets that are vulnerable to these trending CVEs.

Trending Threats
This section highlights active and high-urgency threats that Qualys identifies as currently trending across the global threat landscape. It provides information about what is currently being actively exploited and assesses the severity of the situation.
What you see here:
Card-based display of Actively Exploited CVEs. Each CVE card includes labels such as:
- Ransomware association: Indicates whether the CVE is linked to known ransomware campaigns.
- Malware activity: Shows if active malware families are exploiting this vulnerability.
- Threat actor involvement: Highlights whether specific threat groups are known to target the CVE.
- CISA KEV exposure: Flags if the vulnerability is listed in the CISA Known Exploited Vulnerabilities catalog.
- Patch availability: Specifies whether a vendor-issued fix is available for remediation.
Clicking any CVE card takes you to a detailed CVE page, showing deeper intelligence and any associated impact.

Peer & Performance Benchmarking
This section demonstrates how to compare against peers within your industry. This section provides an overview of your performance in comparison to others in the industry.
For each metric, the visualization includes three benchmark points:
- Your organization’s performance
- Industry average performance
- Top performers in the industry
Key metrics shown:
- MTTR for Critical Threats: Average time taken to remediate vulnerabilities classified as critical threats.
- Ransomware-Related Vulnerabilities: Count of vulnerabilities associated with known ransomware activities.
- EOL/EOS Critical Vulnerabilities: Number of critical vulnerabilities found on end-of-life or end-of-support assets.
- MTTR for CISA KEV items: Average remediation time for vulnerabilities listed in the CISA Known Exploited Vulnerabilities catalog.

Top 5 Threat Categories in Your Industry
This section highlights the top threat themes driving risk in your industry. This section addresses the various types of threats that are influencing the risk landscape for organizations similar to your organization.
Categories include:
- Ransomware-as-a-Service (RaaS): Threat actors leveraging subscription-based ransomware kits to launch scalable attacks.
- Supply Chain Compromise: Attacks executed by exploiting vulnerabilities in third-party vendors or software dependencies.
- Data Exfiltration Malware: Malware designed to stealthily extract sensitive data from compromised systems.
- Business Email Compromise (BEC): Social engineering attacks that manipulate email channels to fraudulently access funds or information
- Targeted Espionage Actors: Advanced threat groups conducting focused, long-term campaigns to steal strategic or confidential data.
