Windows Registry Integrity Monitoring
Windows registry provides information about the installed application and a store to persist the data.
The compromised integrity of the Windows Registry is a valuable indicator of the presence of malware or that the system is compromised.
As Security Analysts, we must be able to monitor the changes to the registry and determine if its integrity is compromised. Compliance standards such as PCI DSS, NERC CIP (CIP 010), FISMA, SOX, NIST (SI7), HIPAA, CIS controls, and GDPR mandate that integrity monitoring solutions be deployed on critical systems to be compliant.
Once an asset is installed from the cloud agent, activate the asset. You can view it under the Asset tab after activation.
From the Configurations tab, you can create a monitoring profile. For more information, refer to the Creating a FIM Profile section.
Create rule(s) for the profile. While creating the rule, select Rule Type as Registry Key or Registry Value. For more information, refer to the Creating a FIM Profile section.
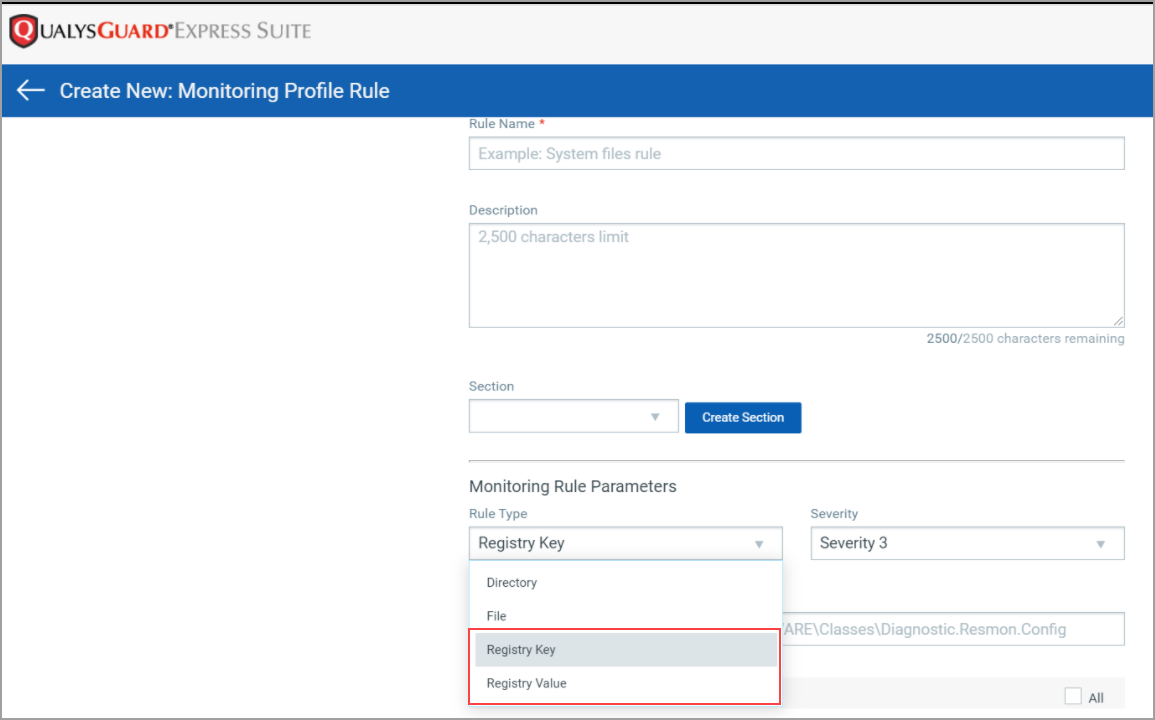
- Selecting Registry Key as the Rule type:
- Mention the Key path that you want to monitor. For example:
HKEY_LOCAL_MACHINE\SOFTWARE\<username> - Select the other attributes you want to monitor and Save the rule.
- Selecting Registry Value as the Rule type:
- Mention the value you want to monitor.
- Mention the Key path that you want to monitor. For example:
Two attributes are available for the user to select: Value Removal (Deletion) and Value Write Changes (Content Change).
- Add data for Key Path and Value Path. In Key Path, enter the registry base path to be monitored, and in Value Path, enter the value to be monitored.
- For Registry Key Full Path -
HKEY_LOCAL_MACHINE and HKEY_USERS, only these two hives are supported for Registry monitoring.
Do not use these special characters / " < > | * ? in registry key paths. Special characters allowed are [ ] {} ( ) . - At least one Inclusion filter is required if you specify only an HKEY_LOCAL_MACHINE key without any subkey or value.
- For Registry Value Name -Do not use these special characters / " < > | * ? in registry value name. Special characters allowed are [ ] {} ( ).
- For Registry Key Full Path -
- Advanced Filters for Key -
- Do not use these special characters / " < > | in key paths.
- Although it can contain characters and numbers including spaces, slashes, commas(,) and [ ] {} ( ).
- Registry Keypath should not start or end with a slash (/).
- Advanced Filters for Value
-
Instead of manually creating the rules, you can also import the rules from the library available.
-
Select the option Monitor Registry from the Rules tab, and all the registry rules available in the library will be imported into your profile.
-
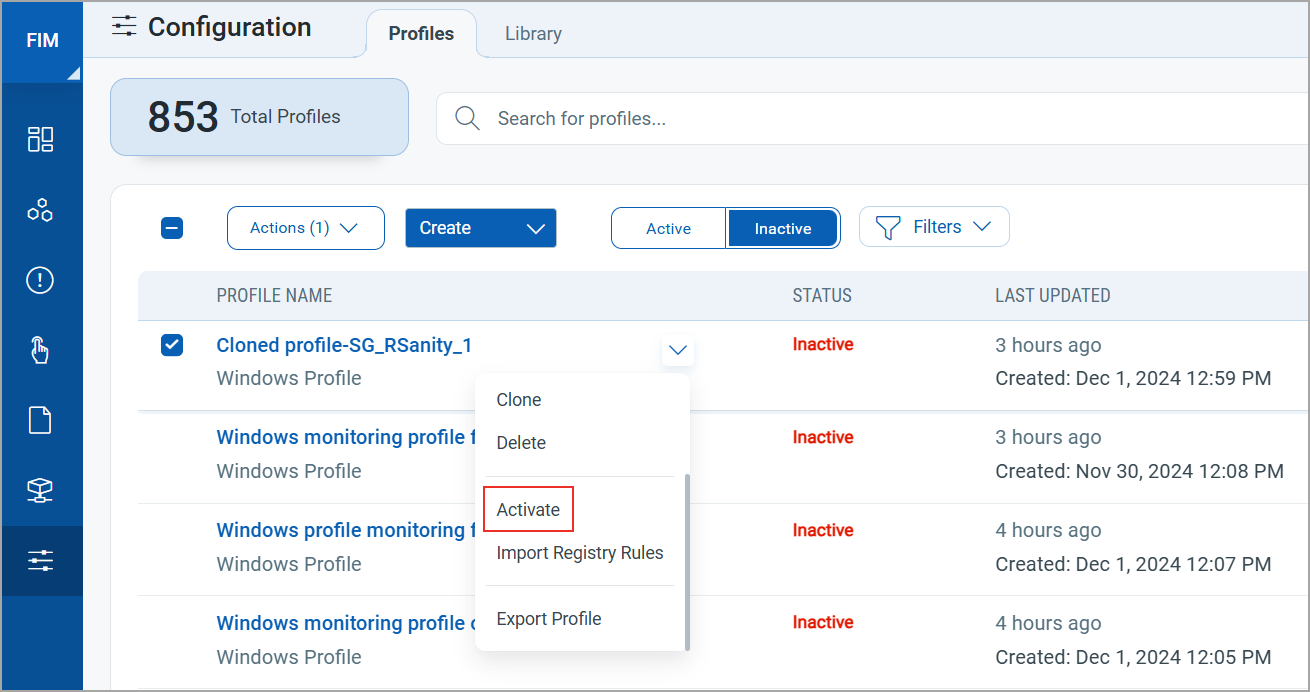
To activate a profile, the user must have at least one rule defined.
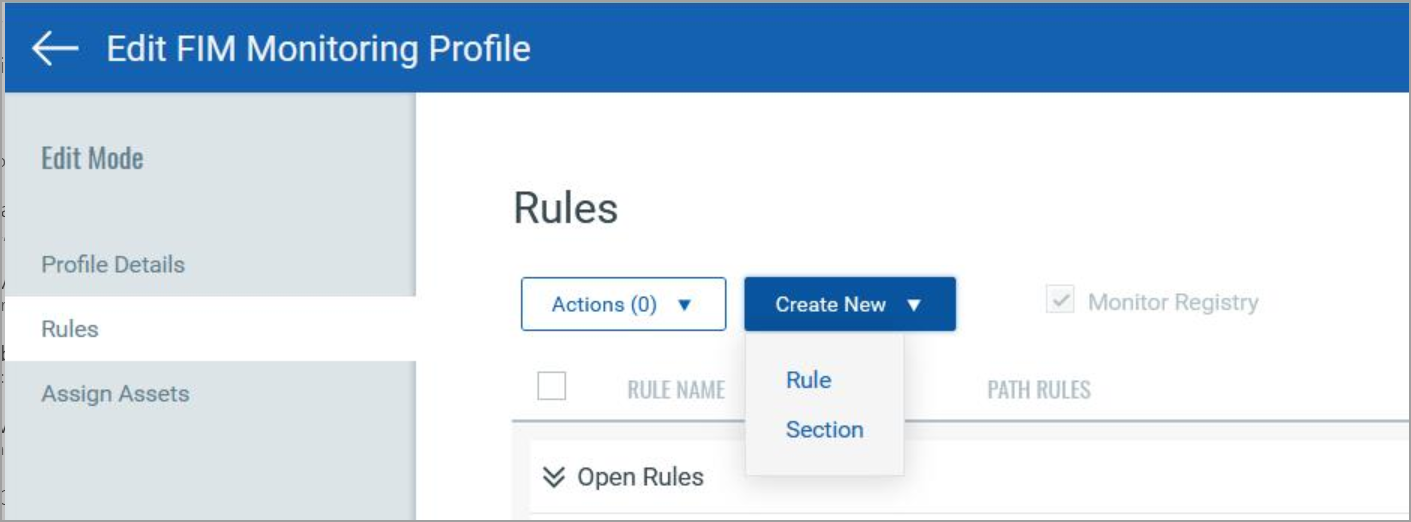
Remember to save the profile after selecting an option to reflect the changes.
- You can also select Import Registry Rules from the drop-down menu in the Profiles tab.
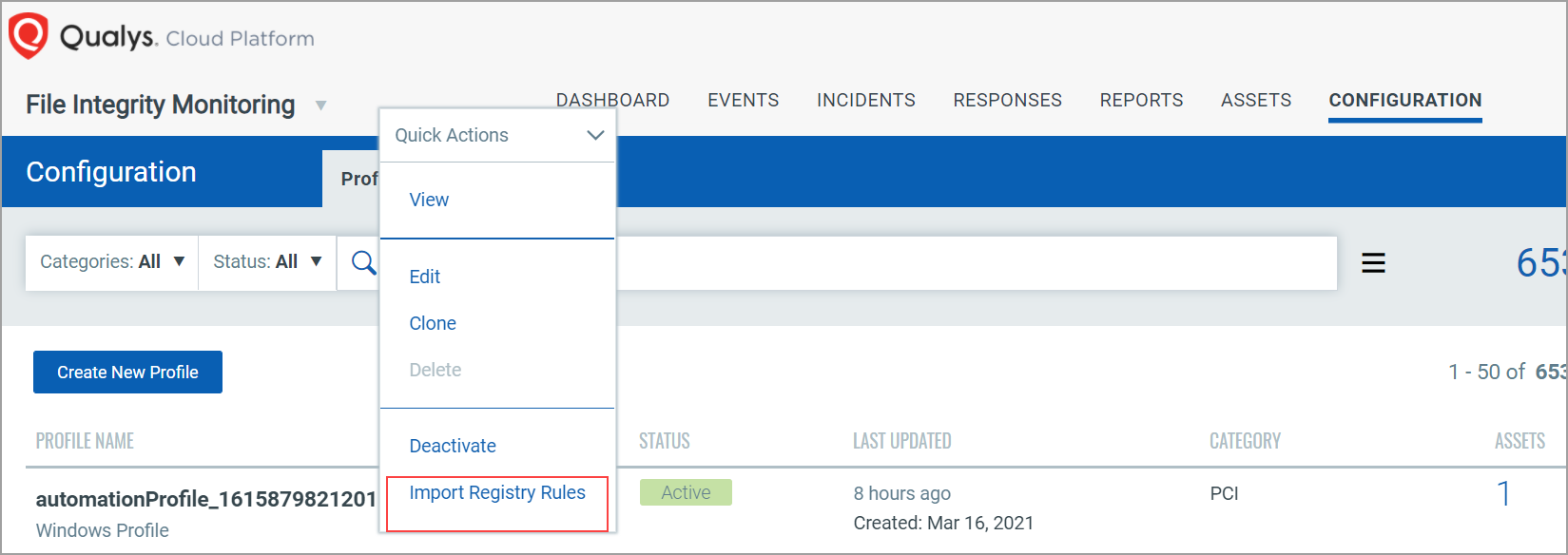
The Import Registry Rules option will be disabled for profiles with the Import Registry Rules checkbox already selected.
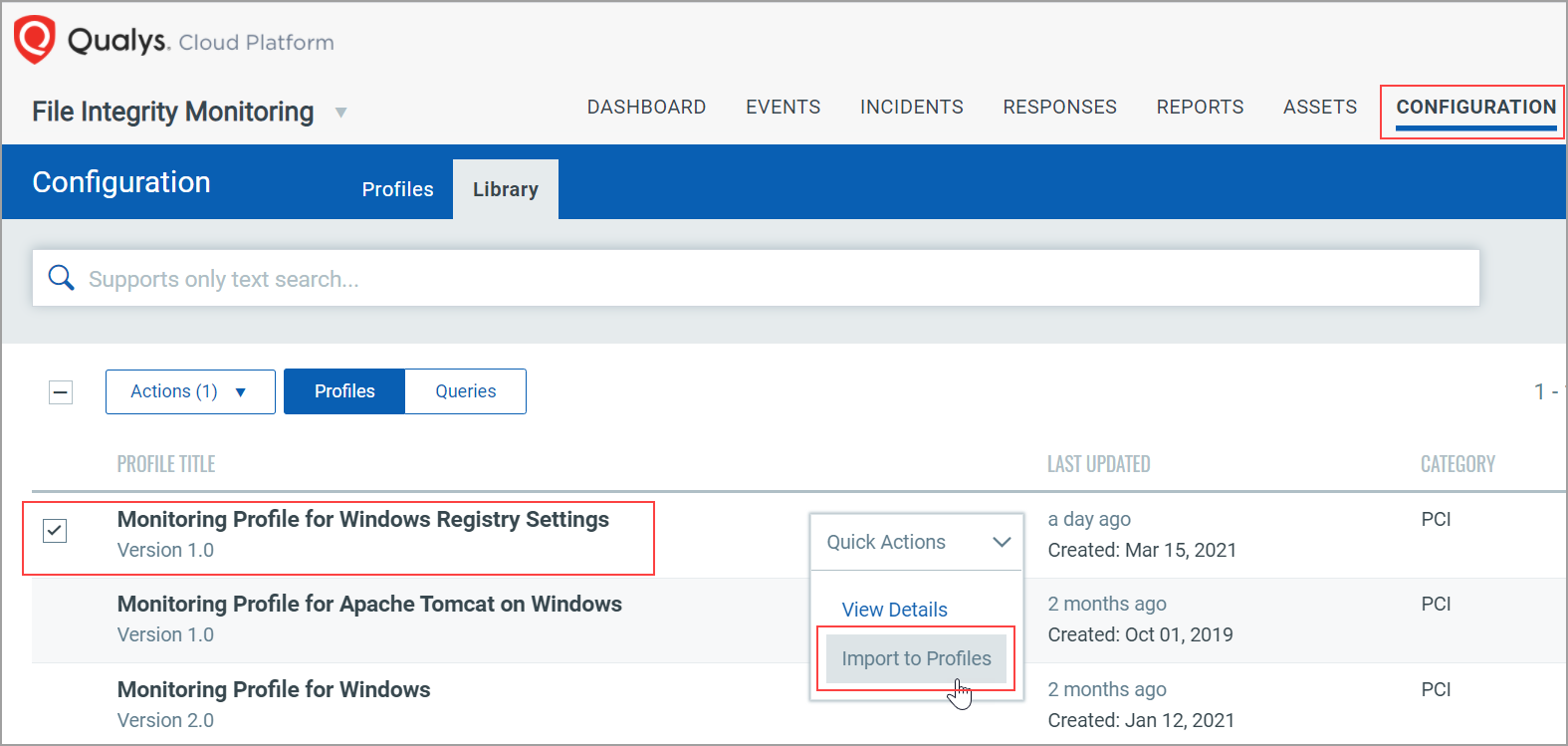
- You can also import the Monitoring Profile for Windows Registry Settings from the Library tab.
Once the manifest is generated, it will start reporting the changes.
To learn more, refer to Importing a FIM Profile from the Qualys Library section.
Any activity marked to be monitored will be reported. You can view the events on the UI.