TotalCloud Release 2.22
March 09, 2026
TotalCloud Release 2.22 adds CDR enhancements, GCP attack path visualization, CNAPP dashboards, snapshot scan improvements, and multi-cloud security control updates.
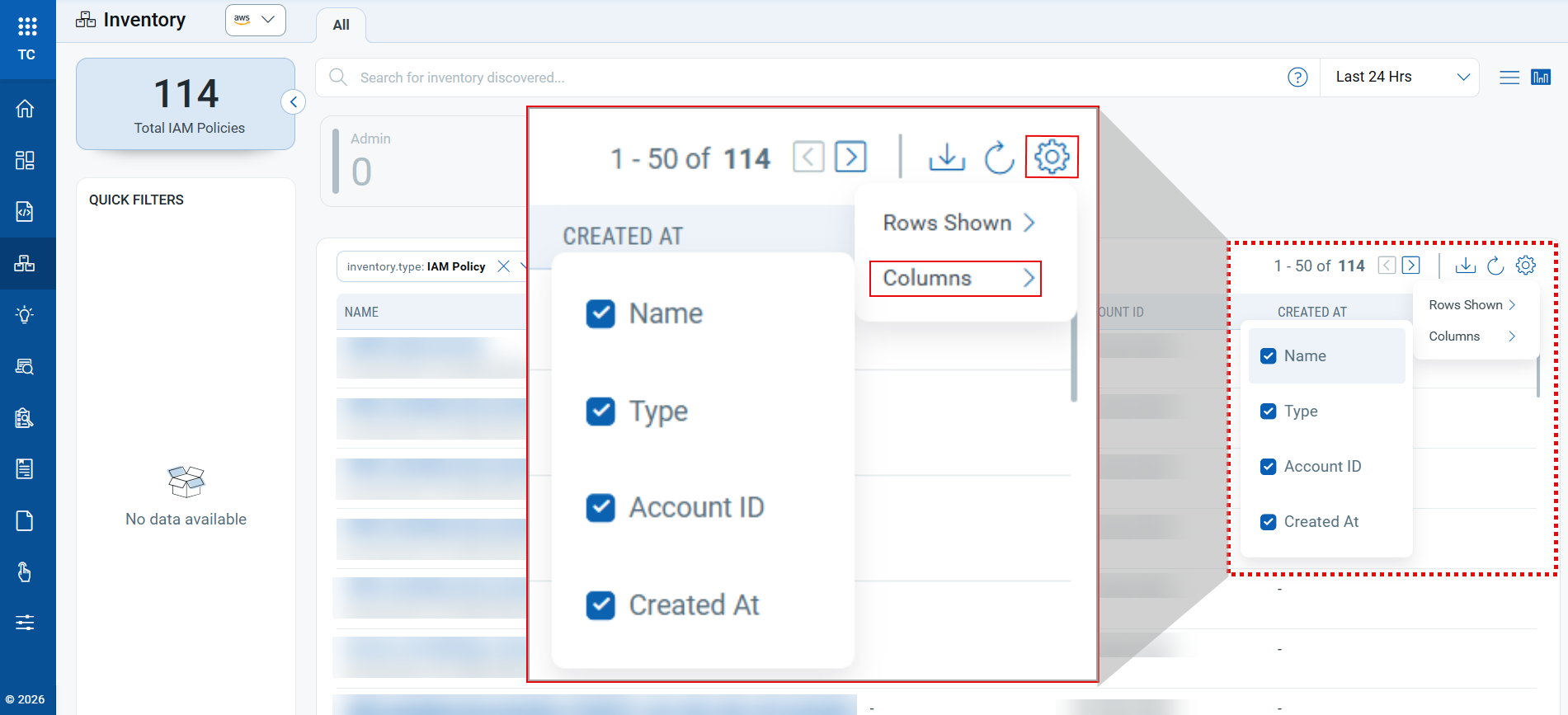
Customizable Inventory Column View in TotalCloud
Applicable for:
With this release, you can customize the columns displayed on the inventory listing page. You can choose which columns are displayed by default, improving visibility and usability.
Previously, the inventory page showed a fixed set of columns. Now you can personalize the view to what matters most to you.
To update the column view, go to Settings → Columns, then select or deselect the required columns.
Attack Path Visualization Extended to GCP in TruRisk™ Insights
Applicable for:
With this release, we are extending the Attack Path Visualization to Google Cloud Platform (GCP) within TruRisk™ Insights. This enhancement enables you to view attack paths for GCP environments alongside existing AWS and Azure environments, providing a unified multi-cloud experience.
Attack Path Visualization support is available for the following insights:
| Insight CID | Title |
|---|---|
| 5000 | Public VM with TruRisk score > 800 |
| 5002 | Public VM with confirmed vulnerability type |
| 5015 | Public VM with vulnerability detected in last 7 days |
| 5017 | Public VM with a critical exploitable vulnerability |
| 5079 | Public Load Balancer |
| 5081 | Privilege escalation and lateral movement risk detected on public VM due to Arbitrary Code Execution via Windows Themes vulnerability |
| 5082 | OpenSSH Remote Code Execution (RCE) exploitation attempt on public VM with critical exploitable vulnerability |
| 5083 | Atlassian confluence data center and server remote code execution (RCE) vulnerability detected on public VM |
| 5084 | Microsoft HTTP/2 Protocol Distributed Denial of Service (DoS) Vulnerability detected on public VM |
| 5085 | Public VM running with Chrome Browser 120.0.6099.234(Mac) and 120.0.6099.224(Windows and Linux) which are actively attacked vulnerabilities and have public exploit. |
| 5157 | Public VM using default service account with access to most Google Cloud infrastructure and critical exploitable vulnerabilities |
| 5158 | Publicly accessible cloud run services |
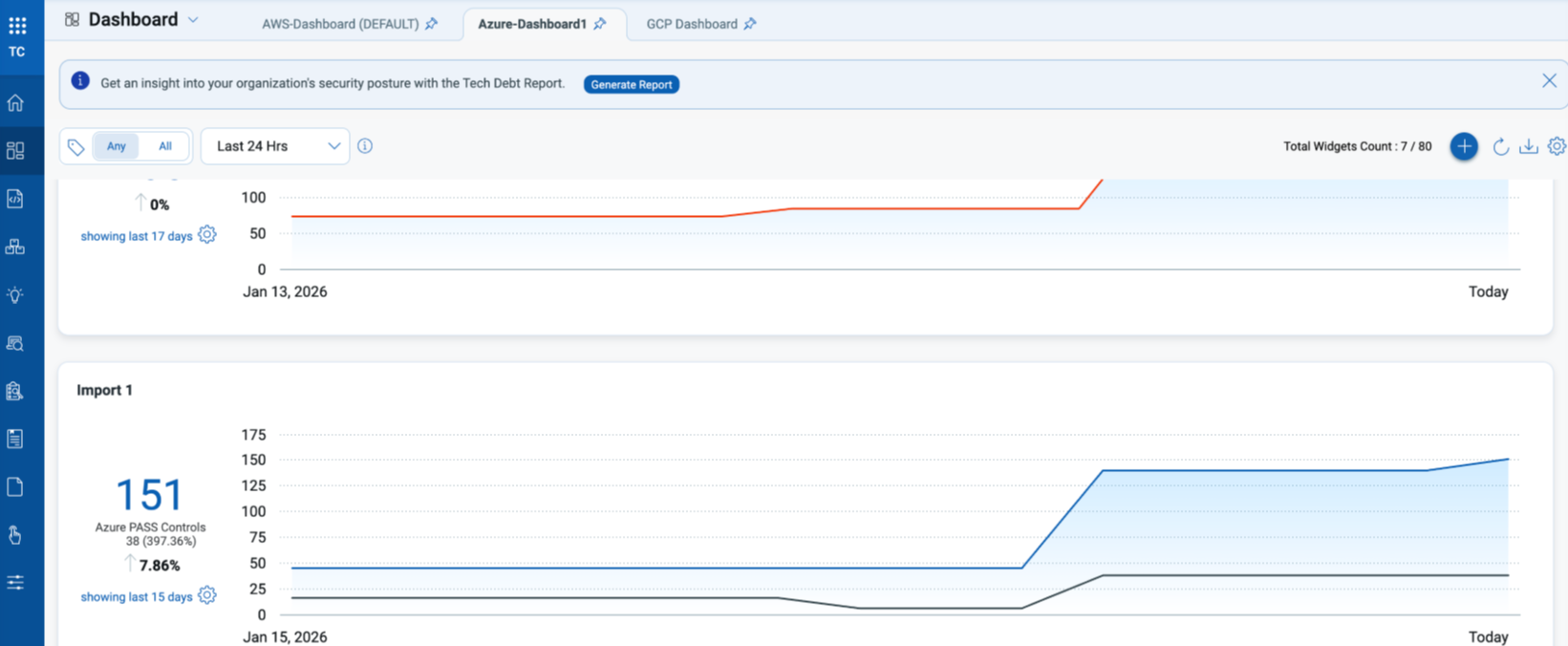
Enhanced Cloud Posture Trend Graph Dashboard Widget
Applicable for:
With this release, we are enabling Trend Graphs in TotalCloud to help you visualize cloud posture changes over time directly from dashboard widgets.
Key Features:
- Trend graphs are generated from posture evaluation data using QQL queries.
- Trend graphs display posture data for the most recent 90 days, with older data automatically removed as new data is added.
- Trend processing pauses if a trend-enabled widget is not viewed for 90 consecutive days.
- When the widget is viewed again after 90 days of inactivity, the trend graph resumes and rebuilds a fresh rolling 90-day view from current data.
- Trend data is derived and displayed based on the Manager’s scope.
- All users with Manager scope will see consistent trend data across widgets.
- At the subscription level, a maximum of 10 trending widgets is allowed for TotalCloud.
- Trend graphs are supported only when the widget query uses supported tokens. See the list of unsupported tokens here.
- Please contact our support team to enable this feature on your subscription.
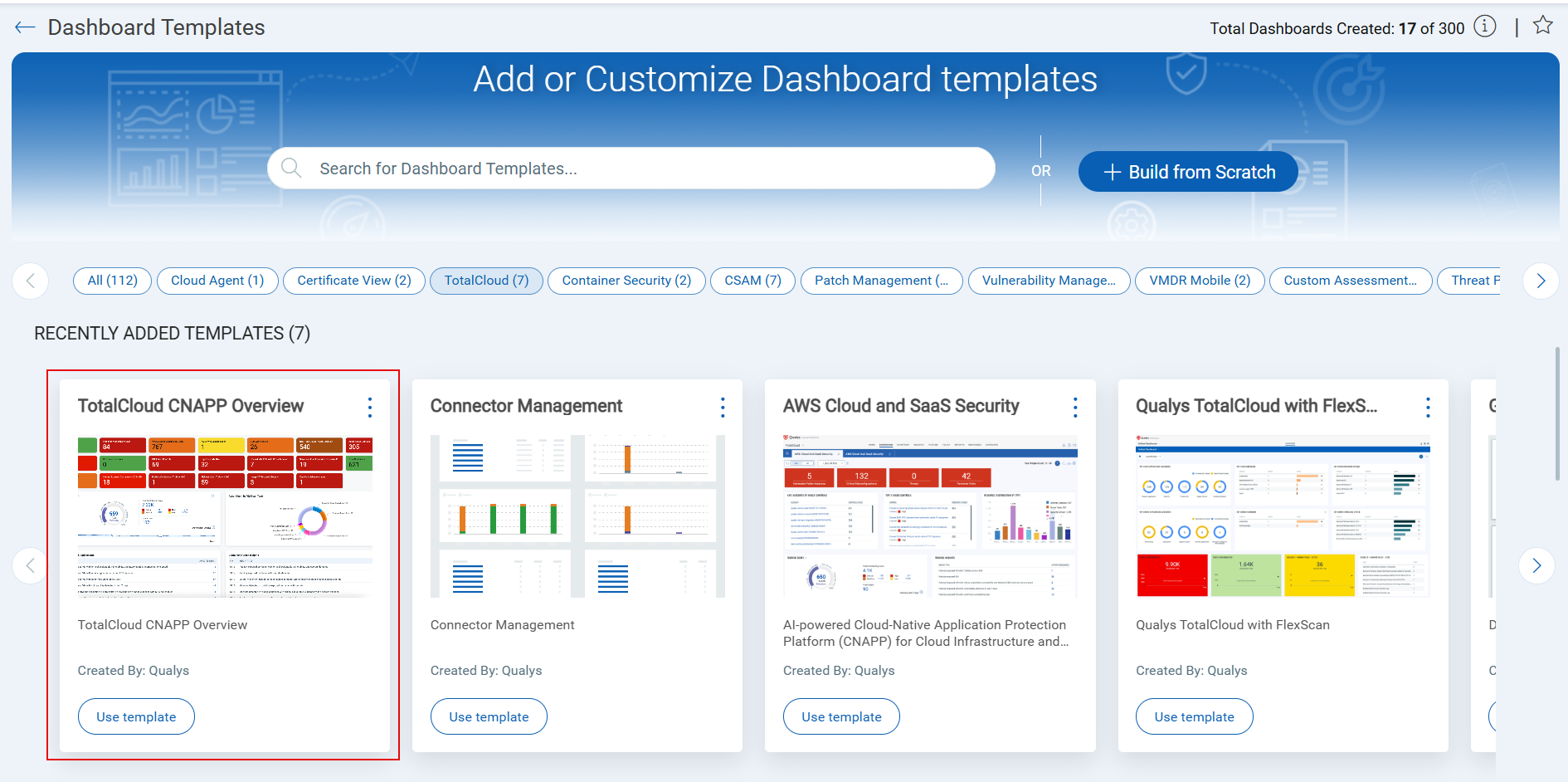
Enhanced TotalCloud CNAPP Dashboard Template (Prebuilt Dashboard)
Applicable for:
With this release, we are introducing the TotalCloud CNAPP Dashboard as a pre-built Dashboard Template within the Unified Dashboard experience.
Previously, this dashboard was shared manually as a JSON file that required users to import it individually. By making this dashboard available as a template under the TotalCloud product, you can now quickly create the dashboard directly from Unified Dashboard without any manual JSON sharing.
Key Features
- Access the TotalCloud CNAPP dashboard directly from the Unified Dashboard templates library under the TotalCloud product.
- Create a fully configured dashboard from the template without importing or managing JSON files.
- View detection and insights across TotalCloud product capabilities in a single, consolidated dashboard.
Benefits
- Eliminate manual steps and reduce setup time when onboarding users to TotalCloud.
- No need to manually share or validate dashboard JSON files with each user.
- Ensure consistent visibility and insights across all users.
Azure On-Demand Snapshot Scan Enhancements
Applicable for:
With this release, TotalCloud now supports On-Demand Snapshot Scan for Azure Virtual Machines, extending snapshot scan capabilities beyond connectors to individual VM assets. These updates are integrated into the existing TotalCloud UI to provide a unified experience for snapshot scanning.
Key features
- Snapshot Scan Eligibility Filtering: You can use the new token
scanType.isSnapshotScanEnabledto automatically filter and display only VMs that support on-demand snapshot scanning. - VM-Level On-Demand Snapshot Scan: You can trigger an on-demand snapshot scan for an individual Azure VM by selecting the VM and then selecting snapshot scan from the actions button.
- Multi-VM Snapshot Scanning: You can select and scan multiple Azure VMs in a single request. Supports selection of up to 50 VMs at a time.
Benefits
- Faster Post-Remediation Validation: By enabling on-demand snapshot scans, you can validate security fixes on specific Azure VMs immediately after remediation instead of waiting for the next scheduled scan.
- Consistent UI Experience: Snapshot scan actions and eligibility behavior align with connector-level workflows.
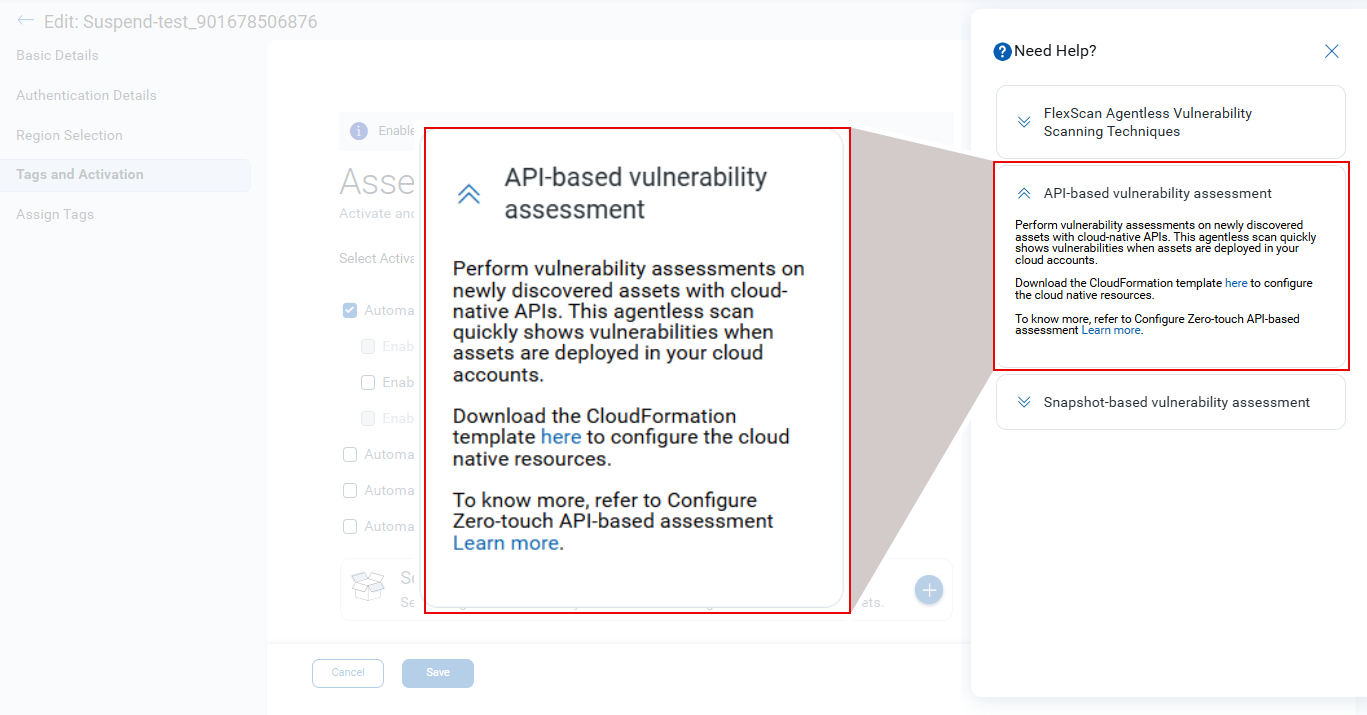
Direct Download of CloudFormation Template (CFT)
Applicable for:
Previously, you were redirected to GitHub to download the CloudFormation Template (CFT) for API-based assessment, with this release, you can now directly download the latest CFT from the Connector Edit option → Tags and Activation → Need Help section.
CDR Enhancements and Updates
The following sections describe the enhancements made to the CDR environment in the upcoming CDR release.
Exception Support for CRS‑Related Events
Applicable for:
With this release, exception handling has been extended to cover all container-related CRS events. You can now create exceptions for CRS events originating from container activities, giving you greater flexibility and control over how you manage alerts.
This enhancement simplifies workflows when dealing with known, trusted, or accepted risks by allowing you to:
- Filter out repetitive or expected behaviors from trusted container processes
- Reduce unnecessary investigations and alert fatigue
- Maintain a cleaner, more focused, and actionable set of risk signals
For steps to create and manage exceptions, see Risk Acceptance Rules.
GovCloud Support for AWS and Azure Flow Logs
Applicable for:
With this release, we are expanding CDR support to AWS and Azure GovCloud across key workflows, Flow Logs, Azure Flow Logs (including Azure Gov), and AWS appliance creation.
Key Features:
- AWS and Azure appliance: GovCloud entries now supported
You can create appliance entries for GovCloud in the same way as Commercial, enabling license provisioning and preparatory steps for regulated environments.
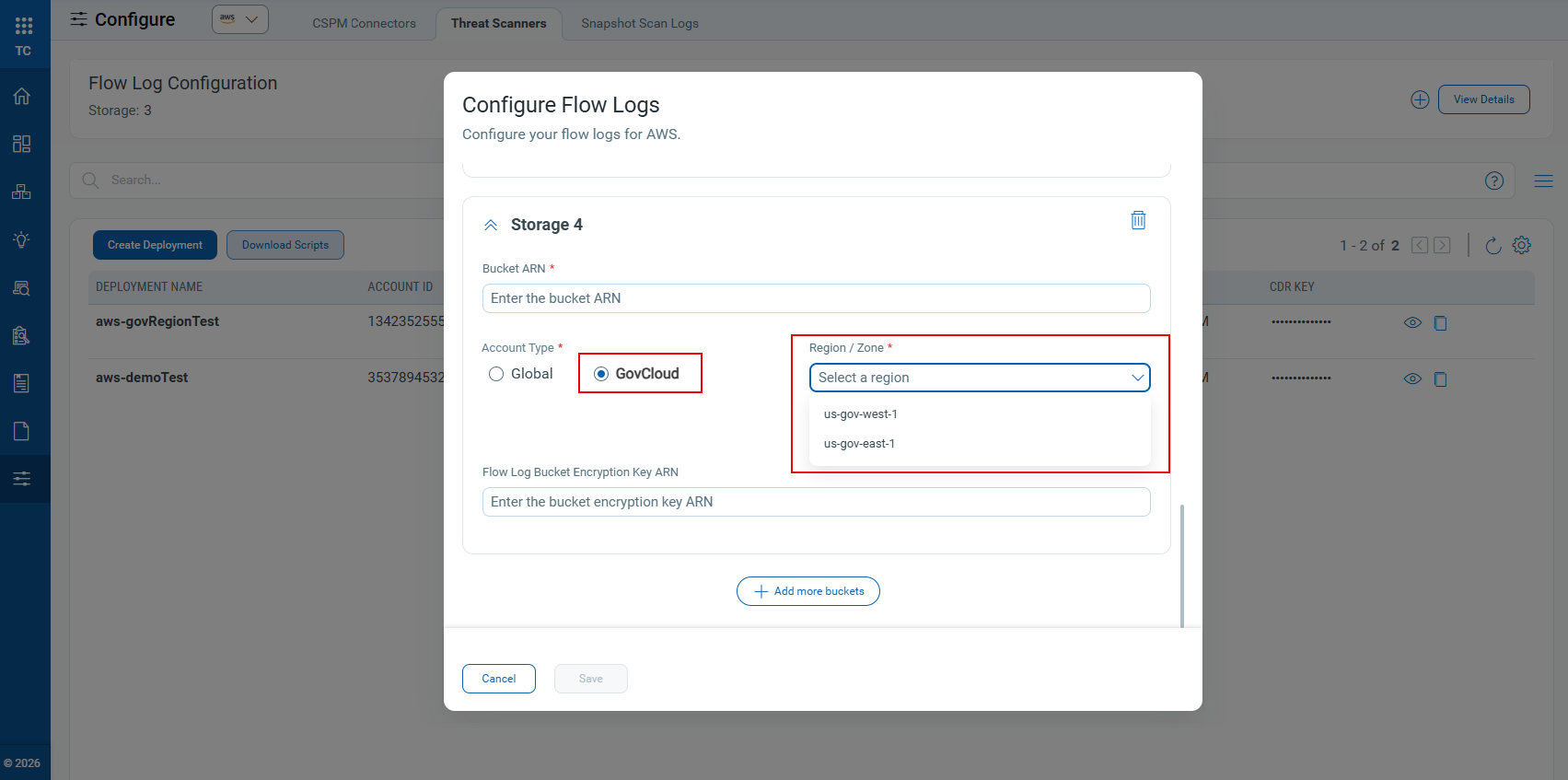
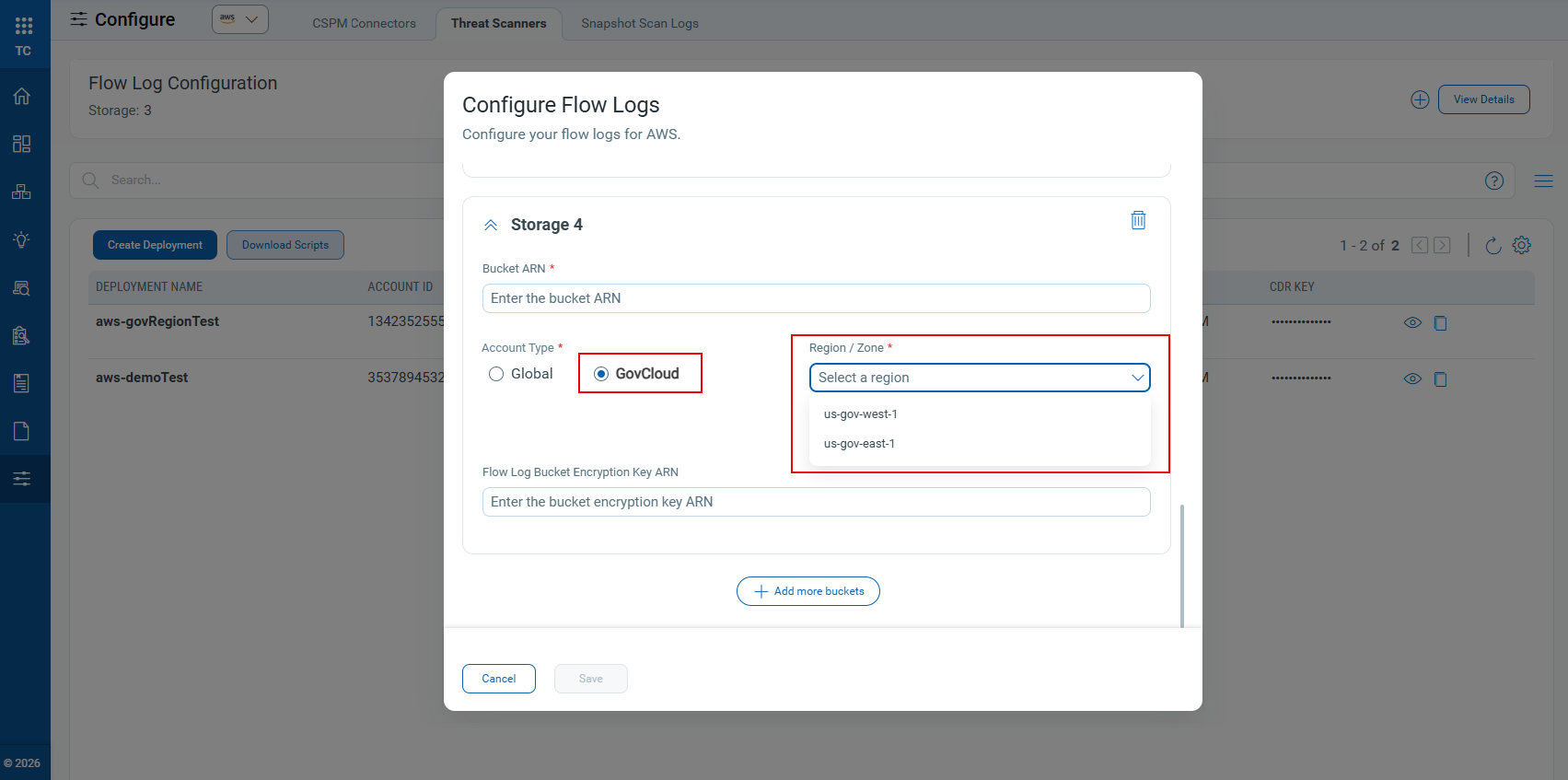
To create a new appliance with Gov Cloud Support, navigate to Configure → Threat Scanners → Add Storage → Add more storage. Provide the required details, select Account Type as GovCloud, and then select the applicable region from the drop-down.
→ Add more storage. Provide the required details, select Account Type as GovCloud, and then select the applicable region from the drop-down.
- Azure Terraform package split (Commercial vs. Gov)
Terraform downloads for Azure now include two configuration files, auto‑filled with cloud type, region, and gateway values to ensure correct parameters for Azure Commercial and Azure Gov deployments.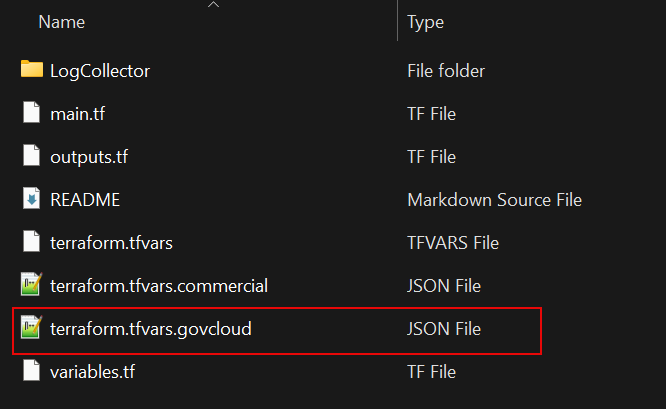
Ensure you are logged into the correct AWS account type, Commercial or GovCloud, before clicking Launch Stack. If you are logged into the wrong account type, the Launch Stack page may not prefill the required values and may display an error.
AWS GovCloud CFTs are provided separately for this release. Please contact Qualys Support for a secure S3 download link. The in‑product download script option currently supports download of AWS Commercial Cloud templates only.
CRS Runtime Events Integration with CDR
Applicable for:
This release enhances the integration between Container Runtime Security (CRS) and CDR, you can now configure runtime event collection through updated Helm parameters. This allows network‑event‑based threats detected by CRS sensors to appear correctly in the CDR Investigate tab.
Customers deploying the CRS runtime sensor must now manually add the new configuration parameters (shown below) to the Helm installation command.
runtimeSensor.processAllowList.enabled=true --set runtimeSensor.processAllowList.value='/*/(curl|wget|clang|bcc|gcc|docker|unshare|mount|kubectl|crictl|modprobe|pnscan|masscan|wpscan|nmap|zgrab|nslookup|netstat|ifconfig|ping|traceroute|route|tcpdump|python|crontab|service|sysctl|rm|nc|ip|arp|debugfs|grep|egrep|fgrep|find|locate|mlocate|gdb|bash|sh|rsync|scp|sftp|dcp|pkexec|find|zip|tar|gzip|hdiutil|7z|sudoedit|sudo|Steghide|Foremost|Stegsolve|Exiftool|Exiv2|Binwalk|Zsteg|Wavsteg|StegCracker|Fcrackzip|ssh|chmod|chown|insmod|dd|devmem|gcore|strace|crash|memdump|fmem|procdump|pmdump|pcredz|mimipenguin|creddump|gsecdump|hashdump|laZagne|volatility|secretsdump|memfetch|avml|ln)$'
Previously, these values were bundled within the Helm chart. They are now provided explicitly during installation, allowing CRS network events to be correctly transmitted to and processed by CDR.
Refer to the Container Security online help for Installation/Uninstallation of the Container Runtime Sensor, and the required CLI commands.
New Tokens
The following section describes the new tokens introduced as part of TotalCloud 2.22.0
| Name | Description | Example |
|---|---|---|
| scanType.isSnapshotScanEnabled | Use this to filter instances discovered by Connectors with Snapshot Scan enabled. | scanType.isSnapshotScanEnabled TRUE |
Control Updates
Updated CIS Policy Versions
Applicable for:
We have updated the following policies to their latest CIS versions.
| Policy | CIS Version |
|---|---|
| CIS Amazon Web Services Foundation Benchmark | Version 6.0.0 |
| CIS Azure Foundation Benchmark | Version 5.0.0 |
New Run Time Controls in AWS without Policy Attachment
Applicable for:
| Platform | CID | Title | Service | Resource |
|---|---|---|---|---|
| AWS | 583 | Ensure that SageMaker notebook instances should be launched in a custom VPC | SageMaker | SageMaker notebook |
| AWS | 584 | Ensure that DMS Endpoints should use SSL | DMS | DMC Endpoint |
| AWS | 585 | Ensure that DMS replication tasks for the source database should have logging enabled | DMS | DMC Endpoint |
| AWS | 586 | Ensure that DMS endpoints for Redis OSS should have TLS enabled | DMS | DMC Endpoint |
| AWS | 587 | Ensure that DMS endpoints for MongoDB should have an authentication mechanism enabled | DMS | DMC Endpoint |
| AWS | 588 | Ensure that DMS endpoints for Neptune databases should have IAM authorization enabled | DMS | DMC Endpoint |
| AWS | 590 | Ensure that API Gateway routes should specify an authorization type | API Gateway | API Gateway |
| AWS | 592 | Ensure that Amazon EC2 Auto Scaling groups should use Amazon EC2 launch templates | EC2 | Auto Scaling Group |
| AWS | 594 | Ensure that the Amazon EC2 Client VPN endpoints should have client connection logging enabled | EC2 | CLIENT_VPN_ENDPOINT |
| AWS | 595 | Ensure that VPCs should be configured with an interface endpoint for ECR API | VPC | VPC_ENDPOINT |
| AWS | 596 | Ensure that VPCs should be configured with an interface endpoint for Docker Registry | VPC | VPC_ENDPOINT |
| AWS | 597 | Ensure that VPCs should be configured with an interface endpoint for Systems Manager | VPC | VPC_ENDPOINT |
| AWS | 598 | Ensure that VPCs should be configured with an interface endpoint for Systems Manager Incident Manager Contacts | VPC | VPC_ENDPOINT |
| AWS | 599 | Ensure that VPCs should be configured with an interface endpoint for Systems Manager Incident Manager | VPC | VPC_ENDPOINT |
| AWS | 600 | Ensure that AWS ES OpenSearch domain error logging to CloudWatch Logs should be enabled | ELASTICSEARCH_SERVICE | ES_DOMAIN |
| AWS | 601 | Ensure that AWS ES OpenSearch domain audit logging to CloudWatch Logs should be enabled | ELASTICSEARCH_SERVICE | ES_DOMAIN |
| AWS | 602 | Ensure that AWS ES OpenSearch domains should have fine-grained access control enabled | ELASTICSEARCH_SERVICE | ES_DOMAIN |
| AWS | 603 | Ensure that AWS Connections to OpenSearch domains should be encrypted using the latest TLS security policy | ELASTICSEARCH_SERVICE | ES_DOMAIN |
| AWS | 606 | Ensure that ECS services should not have public IP addresses assigned to them automatically | ECS | ECS_SERVICE |
New Controls in CIS Microsoft Azure Foundation Benchmark Policy
Applicable for:
| Platform | CID | Title | Service | Resource |
|---|---|---|---|---|
| Azure | 50536 | Ensure 'HTTP2' is set to 'Enabled' on Azure Application Gateway | APPLICATION_GATEWAYS | APPLICATION_GATEWAYS |
| Azure | 50537 | Ensure request body inspection is enabled in Azure Web Application Firewall policy on Azure Application Gateway | APPLICATION_GATEWAYS | APPLICATION_GATEWAYS |
| Azure | 50538 | Ensure bot protection is enabled in Azure Web Application Firewall policy on Azure Application Gateway | APPLICATION_GATEWAYS | APPLICATION_GATEWAYS |
| Azure | 50539 | Ensure Azure DDoS Network Protection is enabled on virtual networks | VIRTUAL_NETWORK | VIRTUAL_NETWORK |
| Azure | 50540 | Ensure Microsoft Defender CSPM is set to 'On' | SECURITY_CENTER | SECURITY_POLICY |
| Azure | 50541 | Ensure Microsoft Defender for APIs is set to 'On' | SECURITY_CENTER | SECURITY_POLICY |
| Azure | 50542 | Ensure Allow Public Network Access is set to Disabled for Azure Databricks | AZURE_DATABRICKS | AZURE_DATABRICKS |
| Azure | 50543 | Ensure No Public IP is set to Enabled in Azure Databricks | AZURE_DATABRICKS | AZURE_DATABRICKS |
| Azure | 50544 | Ensure private endpoints are used to access Azure Databricks | AZURE_DATABRICKS | AZURE_DATABRICKS |
| Azure | 50545 | Ensure that diagnostic settings are configured for Azure Databricks | AZURE_DATABRICKS | AZURE_DATABRICKS |
| Azure | 50546 | Ensure Public Network Access is Disabled for Key Vaults | KEY_VAULT | KEY_VAULT |
| Azure | 50547 | Ensure automatic key rotation is enabled within Azure Key Vault | KEY_VAULT | KEY |
| Azure | 50548 | Ensure certificate Validity Period (in months) is less than or equal to 12 | KEY_VAULT | CERTIFICATES |
| Azure | 50549 | Ensure Azure Resource Manager Delete locks are applied to Azure Storage Accounts | STORAGE_ACCOUNT | STORAGE_ACCOUNT |
| Azure | 50550 | Ensure critical data in Azure Databricks is encrypted with customer-managed keys | AZURE_DATABRICKS | AZURE_DATABRICKS |
| Azure | 50551 | Ensure Azure Resource Manager ReadOnly locks are applied to Azure Storage Accounts | STORAGE_ACCOUNT | STORAGE_ACCOUNT |
New Controls for Azure Without Policy Attachment
Applicable for:
| Platform | CID | Title | Service | Resource |
|---|---|---|---|---|
| Azure | 50552 | Ensure Basic Authentication Publishing Credentials are Disabled for Web apps | APP_SERVICE | WEB_APP |
| Azure | 50553 | Ensure Basic Authentication Publishing Credentials are Disabled for Function apps | APP_SERVICE | FUNCTION_APP |
| Azure | 50554 | Ensure Basic Authentication Publishing Credentials are Disabled for API apps | APP_SERVICE | API_APP |
| Azure | 50555 | Ensure Basic Authentication Publishing Credentials are Disabled for Standard Logic apps | LOGIC_APP | LOGIC_APP |
| Azure | 50223 | Ensure that Only Approved Extensions Are Installed for Virtual Machines | VIRTUAL_MACHINE | VIRTUAL_MACHINE |
New Controls in GCP Kubernetes Engine Best Practices Policy
Applicable for:
| Platform | CID | Title | Service | Resource |
|---|---|---|---|---|
| GCP | 52189 | Ensure GKE clusters are not running using the Compute Engine default service account | Kubernetes Engine | Kubernetes clusters |
| GCP | 52190 | Ensure Kubernetes Secrets are encrypted using keys managed in Cloud KMS | Kubernetes Engine | Kubernetes clusters |
| GCP | 52192 | Ensure Control Plane Authorized Networks is Enabled | Kubernetes Engine | Kubernetes clusters |
| GCP | 52194 | Ensure clusters are created with Private Nodes | Kubernetes Engine | Kubernetes clusters |
| GCP | 52195 | Enable Customer-Managed Encryption Keys (CMEK) for Boot Disks | Kubernetes Engine | Kubernetes Nodes |
| GCP | 52196 | Ensure Logging and Cloud Monitoring is Enabled | Kubernetes Engine | Kubernetes clusters |
New Controls in OCI Best Practices Policy
Applicable for:
| Platform | CID | Title | Service | Resource |
|---|---|---|---|---|
| OCI | 40096 | Ensure Kubernetes Secrets are encrypted at rest in Etcd | KUBERNETES | KUBERNETES_CLUSTER |
Controls Policy-To-Policy Migration
Applicable for:
| Platform | CID | Title | Old Policy | New Policy |
|---|---|---|---|---|
| AWS | 88 | Ensure database instance replication is set to the another zone for High Availability | AWS Database Service Best Practices | CIS Amazon Web Services Foundations Benchmark |
| AWS | 339 | Ensure EBS default encryption is enabled with customer managed key | AWS Best Practices Policy | CIS Amazon Web Services Foundations Benchmark |
| Azure | 50060 | Ensure that Azure Virtual Network subnet is configured with a Network Security Group | Azure Best Practices Policy | CIS Microsoft Azure Foundations Benchmark |
Controls added to CIS Microsoft Azure Foundations Benchmark Policy :
Applicable for:
| Platform | CID | Title | New Policy |
|---|---|---|---|
| Azure | 50173 | Ensure that Geo-redundant storage is enabled for Storage Accounts | CIS Microsoft Azure Foundations Benchmark |
Control Title Changes
Applicable for:
| Platform | CID | Old Title | New Title |
|---|---|---|---|
| AWS | 41 | Ensure no security groups allow ingress from 0.0.0.0/0 to port 22 | Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to port 22 |
| AWS | 42 | Ensure no security groups allow ingress from 0.0.0.0/0 to port 3389 | Ensure no security groups allow ingress from 0.0.0.0/0 or ::/0 to port 3389 |
| AWS | 88 | Ensure database instance replication is set to the another zone for High Availability | Ensure Multi-AZ deployments are used for enhanced availability in Amazon RDS |
| AWS | 402 | Ensure that PostgreSQL RDS instances have Query Logging enabled | Ensure that PostgreSQL instances have Query Logging enabled |
| AWS | 579 | Ensure that AWS ElastiCache Redis Standalone clusters are not associated with default VPC | Ensure that AWS ElastiCache Redis standalone clusters are not associated with default VPC |
| AWS | 580 | Ensure that AWS ElastiCache Redis Standalone Clusters are not using their default endpoint ports | Ensure that AWS ElastiCache Redis standalone clusters are not using default endpoint ports |
| Azure | 50026 | Ensure keyvault is recoverable | Ensure Purge protection is set to Enabled on Azure Key Vault |
| Azure | 50165 | Ensure that Resource Logs are enabled in Service Bus Namespaces | Ensure that diagnostic settings are enabled in Service Bus Namespaces |
| Azure | 50276 | Ensure that Diagnostic logs are enabled in Search Services | Ensure that diagnostic settings are enabled in AI Search Services |
Control Enhancements
Applicable for:
| Platform | CID and Title | Enhancement |
|---|---|---|
| AWS | CID 77: Ensure VPC security group attached to Relational Database Service (RDS) Database Instance does not allows Inbound traffic from ANY source IP CID 106: Ensure Lambda Function is Configured with Private VPC Access |
The control logic is enhanced to properly handle an edge case and improved the clarity of evidence presented in the results. |
| AWS | CID 107: Ensure Lambda excess permissions are removed | The control has been enhanced to correctly manage cases where a Lambda‑associated IAM role has been deleted, and the evidence output has been updated for greater transparency and clarity. |
| AWS | CID 250: Ensure RDS instances should not have be open to a large scope | The control logic is enhanced using the AWS SDK to address several edge cases and improved the clarity of the evidence generated. |
| AWS | CID 148: Ensure that AWS ElastiCache Redis clusters are not associated with default VPC | Fixed workflow issues for CID 148 where the replication-group-id (entityId) mismatch between parent and child streams impacted evaluation. |
| AWS | CID 257: Ensure status of the "log_destination" parameter for PostgreSQL instance is set to "csvlog" CID 258 - Ensure status of the "log_rotation_age" parameter for PostgreSQL instance is set to 60(minutes) CID 259 - Ensure status of the "log_connections" parameter for PostgreSQL instance is set to ON(1) CID 260 - Ensure status of the "log_disconnections" parameter for PostgreSQL instance is set to ON(1) CID 261 - Ensure status of the "log_hostname" parameter for PostgreSQL instance is set to OFF(0) CID 262 - Ensure status of the "log_statement" parameter for PostgreSQL instance is set to "ddl" or stricter CID 263 - Ensure status of the "pgaudit.log" parameter for PostgreSQL instance is set to appropriate value CID 265 - Ensure status of the "log_destination" parameter for Aurora PostgreSQL cluster is set to "csvlog" CID 266 - Ensure status of the "log_rotation_age" parameter for Aurora PostgreSQL cluster is set to 60(minutes) CID 267 - Ensure status of the "log_connections" parameter for Aurora PostgreSQL cluster is set to ON(1) CID 268 - Ensure status of the "log_disconnections" parameter for Aurora PostgreSQL cluster is set to ON(1) CID 269 - Ensure status of the "log_hostname" parameter for Aurora PostgreSQL cluster is set to OFF(0) CID 270 - Ensure status of the "log_statement" parameter for Aurora PostgreSQL cluster is set to "ddl" or stricter CID 271 - Ensure status of the "pgaudit.log" parameter for Aurora PostgreSQL cluster is set to appropriate value CID 402 - Ensure that PostgreSQL instances have Query Logging enabled CID 409 - Ensure that "ssl_max_protocol_version" parameter for Aurora PostgreSQL cluster is set to latest version CID 410 - Ensure that "ssl_min_protocol_version" parameter for Aurora PostgreSQL cluster is set to latest version |
Added evidence to get the Engine type of Instance/cluster. |
| AWS | CID 409 - Ensure that "ssl_max_protocol_version" parameter for Aurora PostgreSQL cluster is set to latest version CID 410 - Ensure that "ssl_min_protocol_version" parameter for Aurora PostgreSQL cluster is set to latest version |
Predicate logic is updated and unnecessary condition ("AllowedValues") removed |
| Azure | CID 50026: Ensure 'Purge protection' is set to 'Enabled' | The control logic is updated to align with Microsoft’s February 2025 change that enforces soft delete on all Key Vaults. The predicate now checks only for purge protection, and the control title has been updated accordingly. |
| Azure | CID 50165: Ensure that diagnostic settings are enabled in Service Bus Namespaces | The control logic is enhanced to validate for specific log types and detailed evidence for destination information. |
| Azure | CID 50231: Ensure that Microsoft Defender for SQL Servers on Machines is set to On | The control logic is updated to validate both tier and name for Terraform templates, and resource_type and tier for ARM templates. |
| Azure | CID 50276: Ensure that diagnostic settings are enabled in AI Search Services | The control logic is enhanced to validate specific log types and added detailed evidence for destination information. |
Controls Deprecated
Applicable for:
| Platform | CID | Title | Policy |
|---|---|---|---|
| AWS | 199 | Ensure not to setup access keys during initial user setup for all IAM users that have a console password | CIS Amazon Web Services Foundations Benchmark AWS Infrastructure as Code Security Best Practices Policy |
| AWS | 201 | Ensure RDS Instance should not have an Interface open to a public scope | AWS Database Service Best Practices AWS Infrastructure as Code Security Best Practices Policy |
| AWS | 457 | Ensure Aurora Serverless AutoPause is enabled for RDS cluster | AWS Database Service Best Practices AWS Infrastructure as Code Security Best Practices Policy |
| AZURE | 50093 | Ensure that Azure Application Gateway have the Web application firewall (WAF) enabled | Azure Infrastructure as Code Security Best Practices Policy Azure Best Practices Policy |
| AZURE | 50094 | Ensure that Azure Application Gateway allows TLSv1.2 or above | Azure Infrastructure as Code Security Best Practices Policy Azure Best Practices Policy |
| AZURE | 50225 | Ensure that Storage accounts disallow Blob public access | Azure Infrastructure as Code Security Best Practices Policy |
| AZURE | 50264 | Ensure Virtual Machines are utilizing Managed Disks | Azure Infrastructure as Code Security Best Practices Policy |
| AZURE | 50247 | Ensure that Azure Event Grid Domain public network access is disabled | Azure Infrastructure as Code Security Best Practices Policy |
| AZURE | 50269 | Ensure that PostgreSQL server enables customer-managed key for encryption | Azure Infrastructure as Code Security Best Practices Policy |
| AZURE | 50311 | Ensure no PostgreSQL Databases allow ingress from (ANY IP) | Azure Infrastructure as Code Security Best Practices Policy |
Build-Time Control Remediation Updates
Applicable for:
| Platform | CID | Title | Framework | Remediation | Old Remediation |
|---|---|---|---|---|---|
| AWS | 91 | Ensure Enhance monitoring is enabled for Relational Database Service (RDS) Database Instance | CloudFormation | Ensure AWS::RDS::DBInstance resource has property Properties/MonitoringInterval set to "1" or more | |
| AWS | 106 | Ensure Lambda Function is Configured with Private VPC Access | CloudFormation | Ensure AWS::Lambda::Function or AWS::Serverless::Function resource has property Properties/VpcConfig configured | |
| AWS | 277 | Ensure Sagemaker domain is encrypted by KMS using a customer managed Key (CMK) | CloudFormation | Ensure AWS::SageMaker::NotebookInstance,AWS::SageMaker::Domain resource has property KmsKeyId configured | |
| AWS | 323 | Ensure MSK Cluster logging is enabled | CloudFormation | Ensure AWS::MSK::Cluster resource has property Properties/LoggingInfo/BrokerLogs configured with at least one of CloudWatchLogs, Firehose, or S3 having Enabled set to true | |
| AWS | 324 | Ensure MSK Cluster encryption at rest and in transit is enabled | CloudFormation | Ensure AWS::MSK::Cluster resource has property Properties/EncryptionInfo/EncryptionInTransit configured with ClientBroker set to TLS and InCluster set to true | |
| AWS | 343 | Ensure that AWS Lambda function is configured for function-level concurrent execution limit | CloudFormation | Ensure AWS::Lambda::Function and AWS::Serverless::Function resource has property Properties/ReservedConcurrentExecutions set to 0 |
|
| AWS | 345 | Ensure AppSync is protected by WAF | CloudFormation | Ensure AWS::AppSync::GraphQLApi resource has AWS::WAFv2::WebACLAssociation configured | |
| AZURE | 50081 | Ensure that Microsoft Defender for Storage is set to On | ARM | Ensure Microsoft.Security/pricings resource has property properties/pricingTier set to Standard | |
| AZURE | 50084 | Ensure App Service Authentication is set on Function Apps | ARM | Ensure Microsoft.web/sites/config resource has name set to authsettingsV2 and has property platform/enabled set to True | |
| AZURE | 50085 | Ensure Function App redirects all HTTP traffic to HTTPS in Azure App Services | ARM | Ensure Microsoft.Web/sites, Microsoft.Web/sites/slots resource has property httpsOnly set to true or Microsoft.Web/sites/config resource has property httpSettings/requireHttps set to true | |
| AZURE | 50089 | Ensure HTTP 2.0 is enabled on Function App | ARM | Ensure Microsoft.Web/sites, Microsoft.Web/sites/slots resource has property http20Enabled set to true | |
| AZURE | 50098 | Ensure that ssl_minimal_tls_version_enforced is set to 1.2 for SQL server | ARM | Ensure Microsoft.Sql/servers resource has property properties/minimalTlsVersion set to 1.2 or 1.3 | |
| AZURE | 50124 | Ensure that Azure CosmosDB does not allow access from all networks | Terraform | Ensure azurerm_cosmosdb_account resource has property is_virtual_network_filter_enabled set to true and either virtual_network_rule or ip_range_filter configured when public_network_access_enabled is true or not explicitly disabled | Ensure azurerm_cosmosdb_account resource has argument public_network_access_enabled set to False |
| AZURE | 50124 | Ensure that Azure CosmosDB does not allow access from all networks | ARM | Ensure Microsoft.DocumentDB/databaseAccounts resource has property isVirtualNetworkFilterEnabled set to true and either virtualNetworkRules or ipRules configured when enableMultipleWriteLocations is enabled | |
| AZURE | 50136 | Ensure Web App enforces FtpsOnly access to FTP traffic | ARM | Ensure Microsoft.Web/sites resource has property siteConfig/ftpsState set to FtpsOnly or Disabled | |
| AZURE | 50141 | Ensure that Microsoft Defender for Key Vault is set to On | ARM | Ensure Microsoft.Security/pricings resource has name set to KeyVaults and property pricingTier set to Standard | |
| AZURE | 50143 | Ensure that CORS does not allow every resource to access the Function Apps | ARM | Ensure Microsoft.web/sites has property properties/siteConfig/cors/allowedOrigins configured | |
| AZURE | 50144 | Ensure that CORS does not allow every resource to access the Web apps | ARM | Ensure Microsoft.web/sites resource does not have property siteConfig/cors/allowedOrigins set to '*' | |
| AZURE | 50148 | Ensure that Managed identity is used in Web apps | ARM | Ensure Microsoft.Web/sites resource has property identity/type configured | |
| AZURE | 50150 | Ensure that Remote debugging is turned off for Web apps | ARM | Ensure Microsoft.Web/sites resource has property siteConfig/remoteDebuggingEnabled set to false | |
| AZURE | 50153 | Ensure that public network access is disabled in Redis Cache | ARM | Ensure Microsoft.Cache/redis resource has property publicNetworkAccess set to Disabled | |
| AZURE | 50174 | Ensure that Public network access is disabled for Azure File Sync | ARM | Ensure Microsoft.StorageSync/storageSyncServices resource has property incomingTrafficPolicy set to AllowVirtualNetworksOnly | |
| AZURE | 50181 | Ensure Storage Accounts are using the latest version of TLS encryption | ARM | Ensure Microsoft.Storage/storageAccounts resource has property minimalTlsVersion set to TLS1_2 | |
| AZURE | 50218 | Ensure that the expiry date is set on all keys from RBAC key Vault | ARM | Ensure Microsoft.KeyVault/vaults/keys resource has property rotationPolicy/attributes/expiryTime configured | |
| AZURE | 50219 | Ensure the Storage Account naming rules | Terraform | Ensure azurerm_storage_account resource has argument name configured as per azure storage account naming convention i.e the account name should be unique within azure and should be between 3 and 24 characters and may contain numbers and lowercase letters only | Ensure azurerm_storage_account resource has argument name configured as per amazon storage account naming convention i.e the account name should be unique within azure and should be between 3 and 24 characters and may contain numbers and lowercase letters only |
| AZURE | 50219 | Ensure the Storage Account naming rules | ARM | Ensure Microsoft.Storage/storageAccounts resource has argument name configured as per azure storage account naming convention i.e. the account name should be unique within azure and should be between 3 and 24 characters and may contain numbers and lowercase letters only | |
| AZURE | 50220 | Ensure that no sensitive credentials are exposed in VM custom_data | ARM | Ensure Microsoft.Compute/virtualMachines resource does not have property properties/osProfile/customData configured with secrets | |
| AZURE | 50224 | Ensure that managed virtual network is enabled in Azure Synapse workspaces | ARM | Ensure Microsoft.Synapse/workspaces resource does not have property managedVirtualNetwork set to default | |
| AZURE | 50227 | Ensure that Automation account variables are encrypted | ARM | Ensure Microsoft.Automation/automationAccounts/variables resource has property isEncrypted set to true | |
| AZURE | 50228 | Ensure that Azure Data Explorer uses disk encryption | ARM | Ensure Microsoft.Kusto/clusters resource has property enableDiskEncryption set to true | |
| AZURE | 50229 | Ensure that Azure Data Explorer uses double encryption | ARM | Ensure Microsoft.Kusto/clusters resource has property enableDoubleEncryption set to true | |
| AZURE | 50230 | Ensure that Azure Batch account uses key vault to encrypt data | ARM | Ensure Microsoft.Batch/batchAccounts resource has property keyVaultReference configured | |
| AZURE | 50231 | Ensure that Microsoft Defender for SQL Servers on Machines is set to On | ARM | Ensure Microsoft.Security/pricings resource has property name set to SqlServerVirtualMachines and pricingTier set to Standard | |
| AZURE | 50232 | Ensure that Net Framework version is the latest, if used as a part of the web app | Terraform | Ensure azurerm_app_service resource has argument dotnet_framework_version set to v6.0 for the site_config block or azurerm_windows_web_app resource has argument dotnet_version set to v8.0 for the application_stack block | Ensure azurerm_app_service resource has argument dotnet_framework_version set to v5.0 for the site_config block |
| AZURE | 50232 | Ensure that Net Framework version is the latest, if used as a part of the web app | ARM | Ensure Microsoft.Web/sites/config resource has property netFrameworkVersion set to v8.0 | |
| AZURE | 50233 | Ensure PHP version is the latest, if used to run the Linux Web App | ARM | Ensure Microsoft.Web/sites resource has property siteConfig/phpVersion set to 8.1 or 8.2 | |
| AZURE | 50234 | Ensure Python version is the latest, if used to run the Linux Web App | ARM | Ensure Microsoft.Web/sites resource has property siteConfig/pythonVersion set to 3.9 or 3.10 or 3.11 or 3.12 | |
| AZURE | 50235 | Ensure Java version is the latest, if used to run the Linux Web App | ARM | Ensure Microsoft.Web/sites resource has property siteConfig/javaVersion set to 17 | |
| AZURE | 50236 | Ensure that Web Apps use Azure Files | ARM | Ensure Microsoft.Web/sites/config resource has property azureStorageAccounts set to AzureFiles | |
| AZURE | 50238 | Ensure that managed disks use a specific set of disk encryption sets for the customer-managed key encryption | ARM | Ensure Microsoft.Compute/disks resource has property properties/encryption/diskEncryptionSetId configured | |
| AZURE | 50239 | Ensure that automatic OS image patching is enabled for Virtual Machine Scale Sets | ARM | Ensure Microsoft.Compute/virtualMachineScaleSets resource does not have property orchestrationMode set to Flexible and has at least one extension in properties/virtualMachineProfile/extensionProfile/extensions with properties/enableAutomaticUpgrade set to true | |
| AZURE | 50241 | Ensure that Virtual Machine Scale Sets have encryption at host enabled | ARM | Ensure Microsoft.Compute/virtualMachines has property properties/securityProfile/encryptionAtHost set to True and Microsoft.Compute/virtualMachineScaleSets resource has property properties/virtualMachineProfile/securityProfile/encryptionAtHost set to True | |
| AZURE | 50243 | Ensure that Cosmos DB accounts have customer-managed keys to encrypt data at rest | ARM | Ensure Microsoft.DocumentDB/databaseAccounts resource has property keyVaultKeyUri configured | |
| AZURE | 50244 | Ensure that Azure Data Factory uses Git repository for source control | ARM | Ensure Microsoft.DataFactory/factories resource has property repoConfiguration/type configured | |
| AZURE | 50245 | Ensure that public network access is disabled in Azure Data Factory | ARM | Ensure Microsoft.DataFactory/factories resource has property publicNetworkAccess set to Disabled | |
| AZURE | 50248 | Ensure that API Management services use virtual networks | ARM | Ensure Microsoft.ApiManagement/service resource has property virtualNetworkConfiguration configured | |
| AZURE | 50250 | Ensure that Firewall is enabled on Key Vaults | ARM | Ensure Microsoft.KeyVault/vaults resource has property properties/networkAcls/defaultAction set to Deny | |
| AZURE | 50251 | Ensure that Key Vault keys are backed by HSM | ARM | Ensure Microsoft.KeyVault/vaults/keys resource has property kty set to RSA-HSM or EC-HSM | |
| AZURE | 50253 | Ensure that Key Vault Secrets have Content-Type set | ARM | Ensure Microsoft.KeyVault/vaults/secrets resource has property properties/contentType configured | |
| AZURE | 50257 | Ensure that Web Application Firewall (WAF) is enabled in Azure Front Door Services | ARM | Ensure Microsoft.Network/frontDoors resource has at least one frontend endpoint with properties/webApplicationFirewallPolicyLink/id configured | |
| AZURE | 50259 | Ensure that Azure Front Door uses WAF in Detection or Prevention modes | ARM | Ensure Microsoft.Network/FrontDoorWebApplicationFirewallPolicies resource has property policySettings/enabledState set to Enabled | |
| AZURE | 50261 | Ensure that Service Fabric cluster has the ClusterProtectionLevel property set to EncryptAndSign | ARM | Ensure Microsoft.ServiceFabric/clusters resource has property fabricSettings with at least one entry where name is set to Security and parameters contains an entry with name set to ClusterProtectionLevel and value set to EncryptAndSign | |
| AZURE | 50270 | Ensure that Azure Synapse workspaces have no IP firewall rules attached | ARM | Ensure Microsoft.Synapse/workspaces resource does not have dependsOn property configured with Microsoft.Synapse/workspaces/firewallRules dependencies | |
| AZURE | 50316 | Ensure that key vault enables purge protection | ARM | Ensure Microsoft.KeyVault/vaults resource has property properties/enablePurgeProtection set to True | |
| AZURE | 50317 | Ensure that key vault enables soft delete | ARM | Ensure Microsoft.KeyVault/vaults resource has property properties/enableSoftDelete configured | |
| AZURE | 50318 | Ensure that App service enables HTTP logging | ARM | Ensure Microsoft.web/sites/config has property properties/httpLoggingEnabled set to True | |
| AZURE | 50319 | Ensure that App service enables detailed error messages | ARM | Ensure Microsoft.Web/sites/config resource has property detailedErrorLoggingEnabled set to true | |
| AZURE | 50320 | Ensure that App service enables failed request tracing | ARM | Ensure Microsoft.Web/sites/config resource has property requestTracingEnabled set to true | |
| AZURE | 50322 | Ensure that Azure Cosmos DB disables public network access | ARM | Ensure Microsoft.DocumentDB/databaseAccounts resource has property properties/publicNetworkAccess set to Disabled | |
| AZURE | 50324 | Ensure that Front Door WAF prevents message lookup in Log4j2 | Terraform | Ensure azurerm_frontdoor_firewall_policy resource has managed_rule block configured with type set to DefaultRuleSet or Microsoft_DefaultRuleSet. If override blocks are configured for the JAVA rule group, ensure rule ID 944240 has enabled set to true and action set to Block or Redirect to prevent Log4j2 message lookup vulnerability | Ensure azurerm_frontdoor_firewall_policy has managed_rule configured with type set to Microsoft_DefaultRuleSet |
| AZURE | 50324 | Ensure that Front Door WAF prevents message lookup in Log4j2 | ARM | Ensure Microsoft.Network/frontdoorWebApplicationFirewallPolicies resource has property managedRules/managedRuleSets configured with ruleSetType set to DefaultRuleSet or Microsoft_DefaultRuleSet, and if ruleGroupOverrides is configured for the JAVA rule group, ensure rule ID 944240 has enabledState set and action set to Block or Redirect to prevent Log4j2 message lookup vulnerability | |
| AZURE | 50325 | Ensure that Application Gateway WAF prevents message lookup in Log4j2 | Terraform | Ensure azurerm_web_application_firewall_policy resource has managed_rules block configured with managed_rule_set having type set to OWASP and version set to 3.1 or 3.2. If rule_group_override is configured for the REQUEST-944-APPLICATION-ATTACK-JAVA rule group, ensure rule ID 944240 is NOT included in disabled_rules to prevent Log4j2 message lookup vulnerability | Ensure azurerm_web_application_firewall_policy resource has block managed_rules.managed_rules_set configured with attributes type set to OWASP and version set to 3.1 |
| AZURE | 50325 | Ensure that Application Gateway WAF prevents message lookup in Log4j2 | ARM | Ensure Microsoft.Network/ApplicationGatewayWebApplicationFirewallPolicies resource has property managedRules/managedRuleSets configured with ruleSetType set to OWASP and ruleSetVersion set to 3.1 or 3.2. If ruleGroupOverrides is configured for the REQUEST-944-APPLICATION-ATTACK-JAVA rule group, ensure rule ID 944240 is NOT disabled to prevent Log4j2 message lookup vulnerability | |
| AZURE | 50338 | Ensure public accessibility is not enabled for Azure MSSQL Server | ARM | Ensure Microsoft.Sql/servers resource has property publicNetworkAccess set to Disabled |