API Security in Web Application Scanning
Limited Customer Release
May 22, 2024
Introduction
Web Application Scanning (WAS) can scan REST APIs, allowing users to upload Swagger/Postman collections or Burp proxy captures to the web application. However, as APIs are represented as web applications in WAS, the API scanning capacity was not clearly communicated.
With this release, we are introducing a dedicated API scanning feature. The new API scanning feature enhances WAS with new QIDs, coverage of the OWASP API Top 10, and compliance verification tools for OpenAPI or Swagger.
Prerequisites
The following application versions are required for the API Security feature:
- Web Application Scanning 1.14.0.0
- NextGen WAS Engine 10.1.1
- Qualys Cloud Platform 3.18.0.0
Changes in User Interface
New Tab – APIs
The APIs tab is added under Applications to display the list of APIs in your subscription. The APIs tab displays the API name, last scanned date, updated date, and tags. The tab displays the vulnerability level of the application with the number of open vulnerabilities and the TruRisk™ score calculated for the APIs, which indicates the API application's vulnerability level.
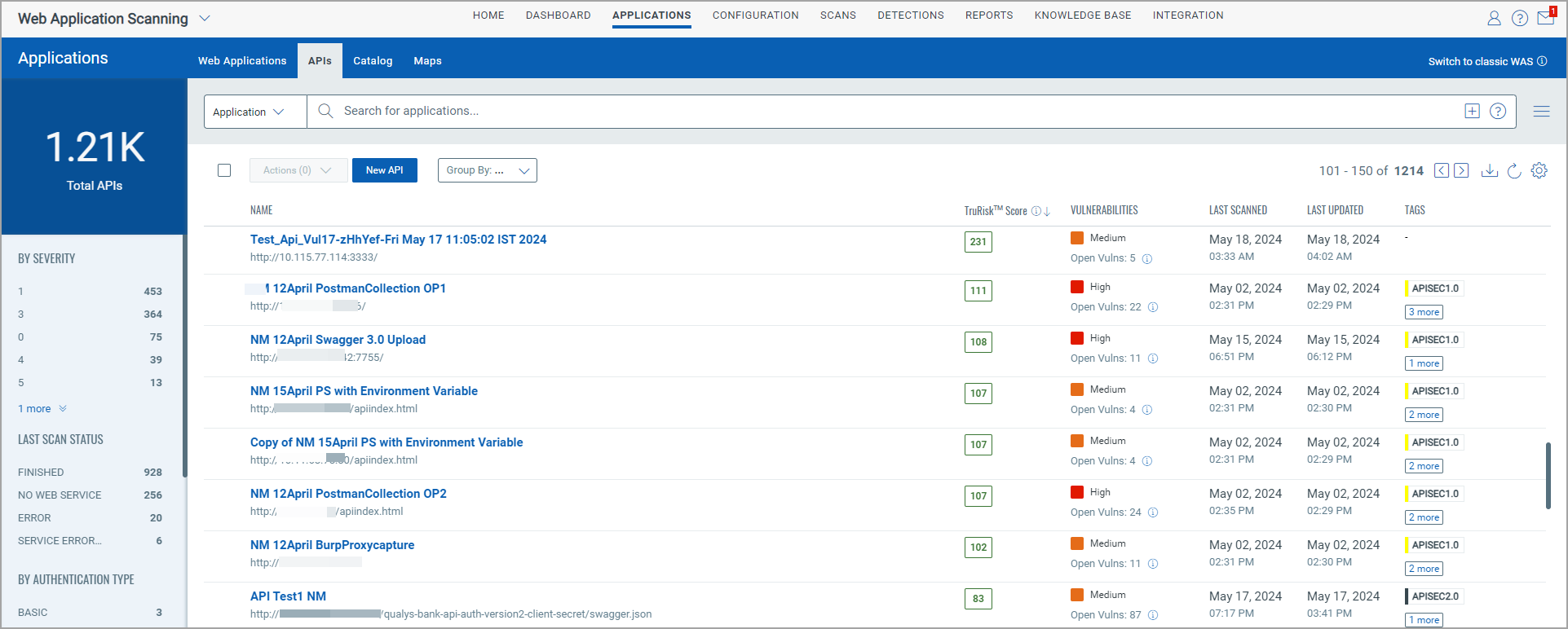
You can perform the following actions on the APIs in the list using the Quick Actions menu:
- View and edit API records
- View vulnerability report
- Launch vulnerability and compliance scan
- Add and remove tags
- Add comment
- Purge or remove API asset
- Clone existing API records using the Save As option
For more information on APIs tab, see View your APIs.
Scans
You can launch a vulnerability and compliance scan for APIs from the Scans tab. The compliance scan is available only for API with Swagger API.
For the compliance scan, you must create a new option profile named Api Compliance Option Profile.
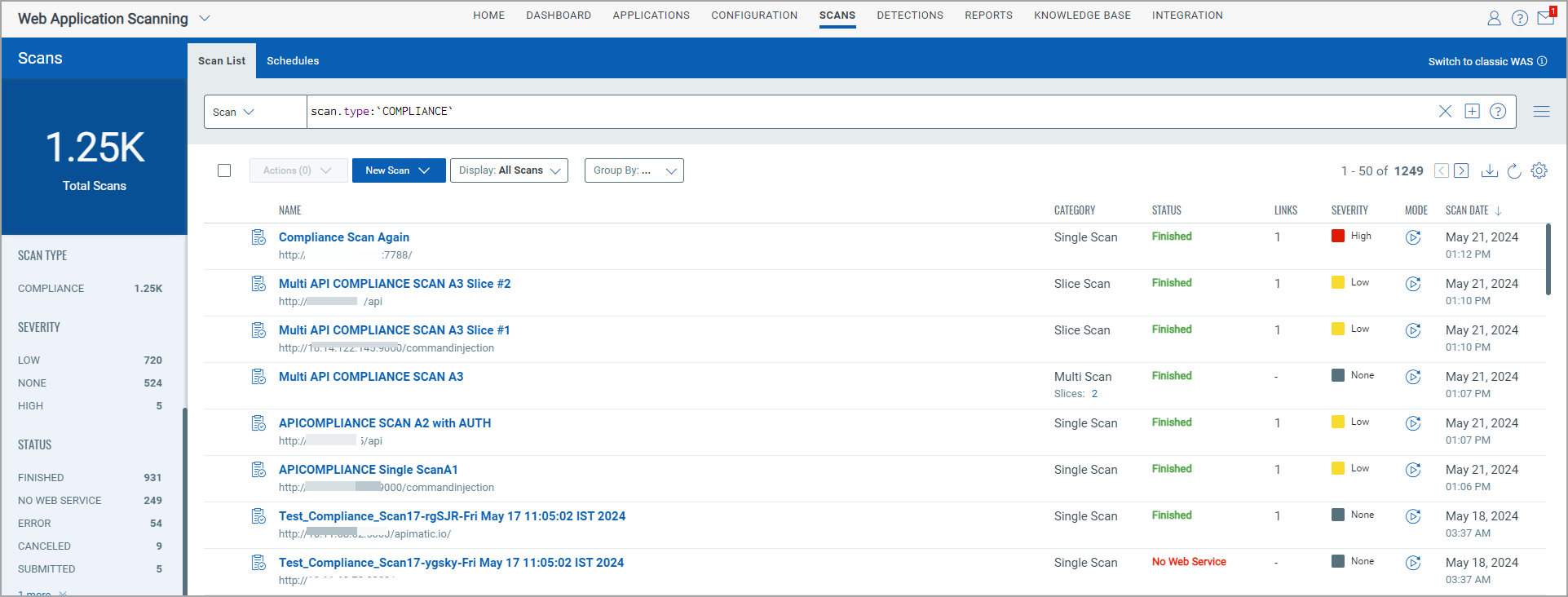
For details on how to launch a compliance scan, refer to Launch Compliance Scan.
Currently, scheduling of API scans is not supported.
Detections
The Detections tab displays API detections with web application detections.
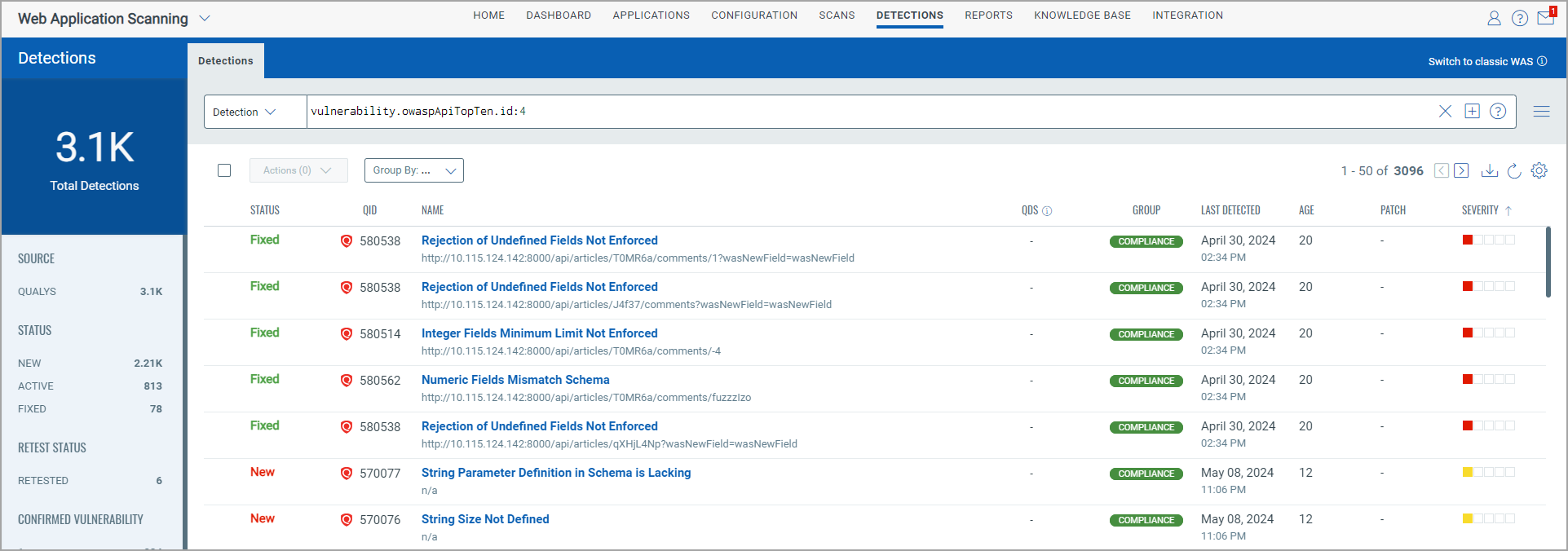
All the actions available in the Quick Actions menu for web application detections are also available for the API detections.
Retesting for API vulnerabilities is available for the vulnerabilities identified through a vulnerability scan and not for vulnerabilities found during a compliance scan.
Online Reports
You can generate application reports and scan reports for API, which are displayed in the Online Reports tab.
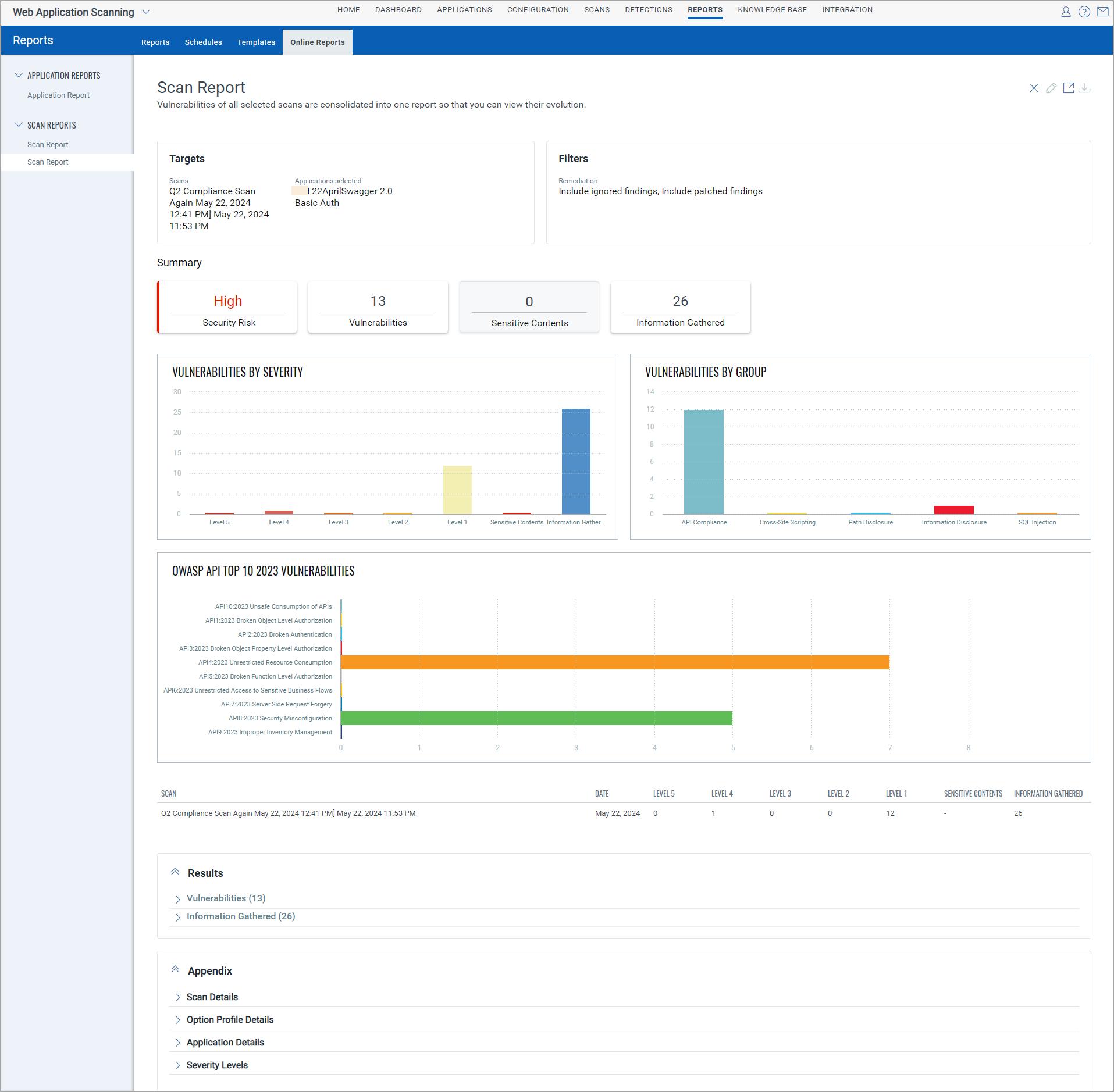
Currently, the Download button is unavailable for application or scan reports for APIs.
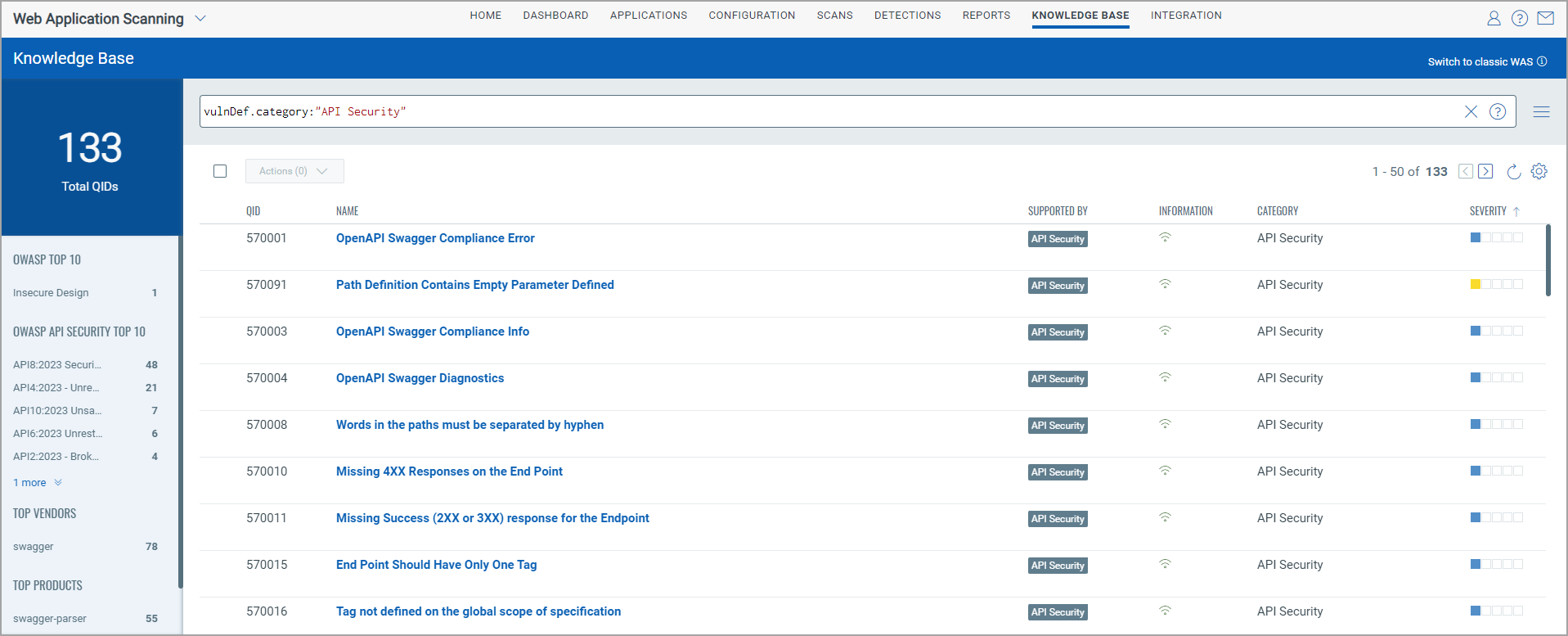
KnowledgeBase
New API QIDs are added and visible on the KnowledgeBase data list. OWASP API Top Ten 2023 categories are added, and API QIDs are mapped against these categories.
A new category – API Security is added to the WAS KnowledgeBase with the list of API compliance-related QIDs.
Token Changes
New Tokens
The following new tokens are added for the APIs
| Tab | Token Name | Description |
|---|---|---|
| Detections | vulnerability.owaspApiTopTen.id | Use an integer value to find detections with the given OWASP API Top Ten 2023 category ID. |
| vulnerability.owaspApiTopTen.name | Use a text value to find scans with detections with the given OWASP API top ten 2023 category name. | |
| Scans | scan.findings.owaspApiTopTen.id | Use an integer to find scans with detections with the given OWASP API top ten 2023 category ID. |
| scan.findings.owaspApiTopTen.name | Use a text value to find scans with detections with the given OWASP API top ten 2023 category name. | |
| KnowledgeBase | vulnDef.owaspApiTopTen.id | Use an integer value to search QIDs the given OWASP API top ten 2023 category ID. |
| vulnDef.owaspApiTopTen.name | Use values within quotes or backticks to search QIDs with the given OWASP API top ten 2023 category name. |
Updated Tokens
The following token is modified.
| Tab | Token Name | Description |
|---|---|---|
| Scans | scan.type | A new value—COMPLIANCE is added to find the compliance scan from the list of scans. |