TotalCloud Release 2.18
July 25, 2025
TotalCloud 2.18 brings updates to supported integrations, insights, inventory, and controls.
Important Announcement: Migration of Qualys Services from ADAL to MSAL
We would like to inform you that the Azure Active Directory Authentication Library (ADAL) has been officially deprecated by Microsoft. Although existing applications using ADAL may continue to function, Microsoft has ended all support and development for ADAL, including security updates, as of June 30, 2023.
What You Should Know:
- Microsoft ended support and development for ADAL on June 30, 2023.
- No new features or security updates will be provided for ADAL.
- Continued use of ADAL is not recommended due to potential security risks.
Actions Taken:
We have proactively completed the migration from ADAL to the Microsoft Authentication Library (MSAL) across all impacted systems and services. This ensures continued security, supportability, and compliance with Microsoft’s recommended best practices.
This update is for your awareness only. No changes or actions are required from your side.
IPv6 Support Enhancements for Cloud Security Posture Management (CSPM)
With this release, we have added comprehensive IPv6 support across the Cloud Security Posture Management (CSPM) platform to provide enhanced visibility, evaluation, and control of cloud assets with IPv6 addressing.
Benefits:
- IPv6 metadata is now collected for all supported resource types and is displayed on the Inventory alongside IPv4, offering complete network visibility.
- Inventory and Evaluation APIs now include IPv6 metadata in the response payloads.
Supported Inventory Types for Cloud Providers:
- AWS: Instance, VPC Endpoint Service, Network Interfaces
- Azure: Virtual Machine
- GCP: Kubernetes clusters, Instances, Subnetworks
- OCI: Compute Instance, Loadbalancer, Kubernetes Clusters
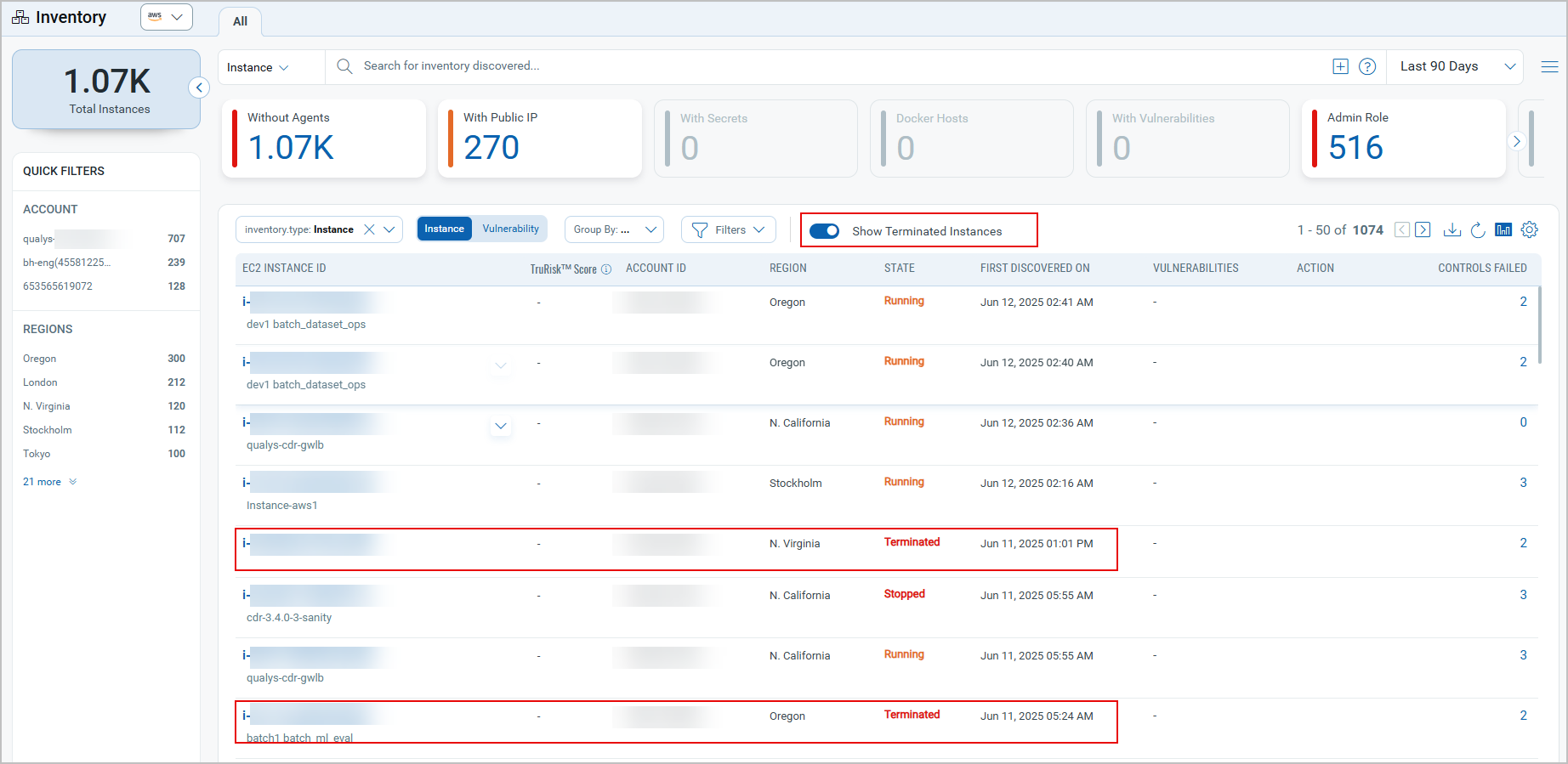
Enhanced Resource Filtering in TotalCloud Inventory
Previously, the TotalCloud Inventory displayed all resources based on the selected date range, regardless of their status. This included terminated Instances (AWS and OCI), deleted VMs (Azure), and terminated VM instances (GCP). With this release, the inventory types now default to showing only non-terminated resources across all supported cloud providers.
AWS and OCI instances show two distinct states for terminated resources:
- AWS: 'terminated' (lowercase) and 'TERMINATED' (uppercase).
- OCI: 'Terminated' (Camelcase) and 'TERMINATED' (uppercase).
This feature is available for the following Inventory types:
- Instances for AWS.
- Virtual Machines for Microsoft Azure.
- VM Instances for GCP.
- Compute Instances for OCI.
To facilitate this enhancement, a new toggle switch has been added next to the filter selection at the top of the section. The toggle switches are labelled as:
- Show terminated instances for AWS and OCI.
- Show Deleted Virtual Machines for Microsoft Azure.
- Show Terminated VM Instances for GCP.
The switch is turned off by default, ensuring that only non-terminated resources are shown initially. When turned on, terminated resources are also included in the list.
Benefits:
- Provides a focused and relevant default view of active resources.
- Reduces manual filtering steps to show current inventory.
Toggle Switch off: Only non-terminated resources are shown.
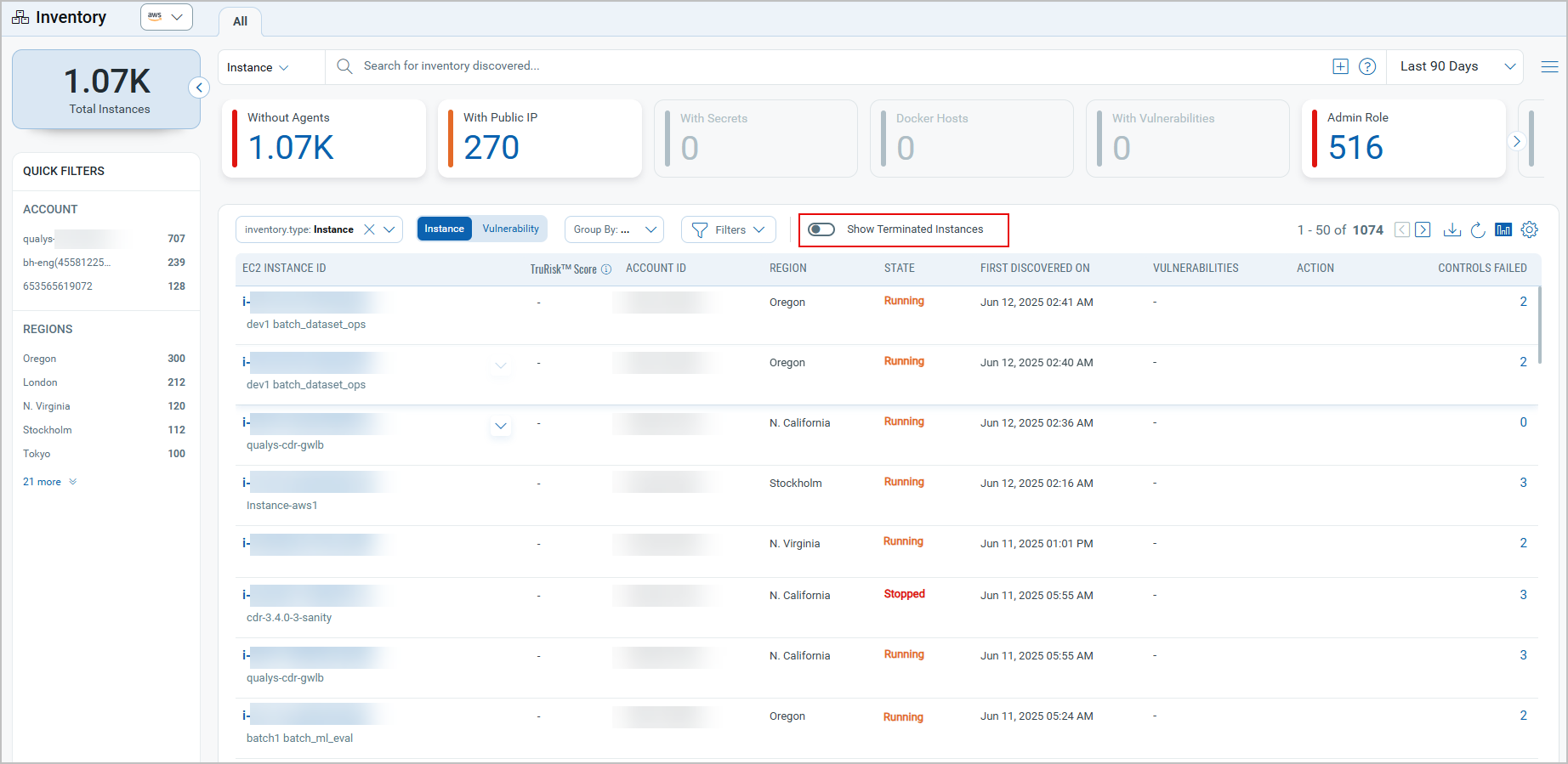
Toggle Switch on: Terminated resources are also included in the list.
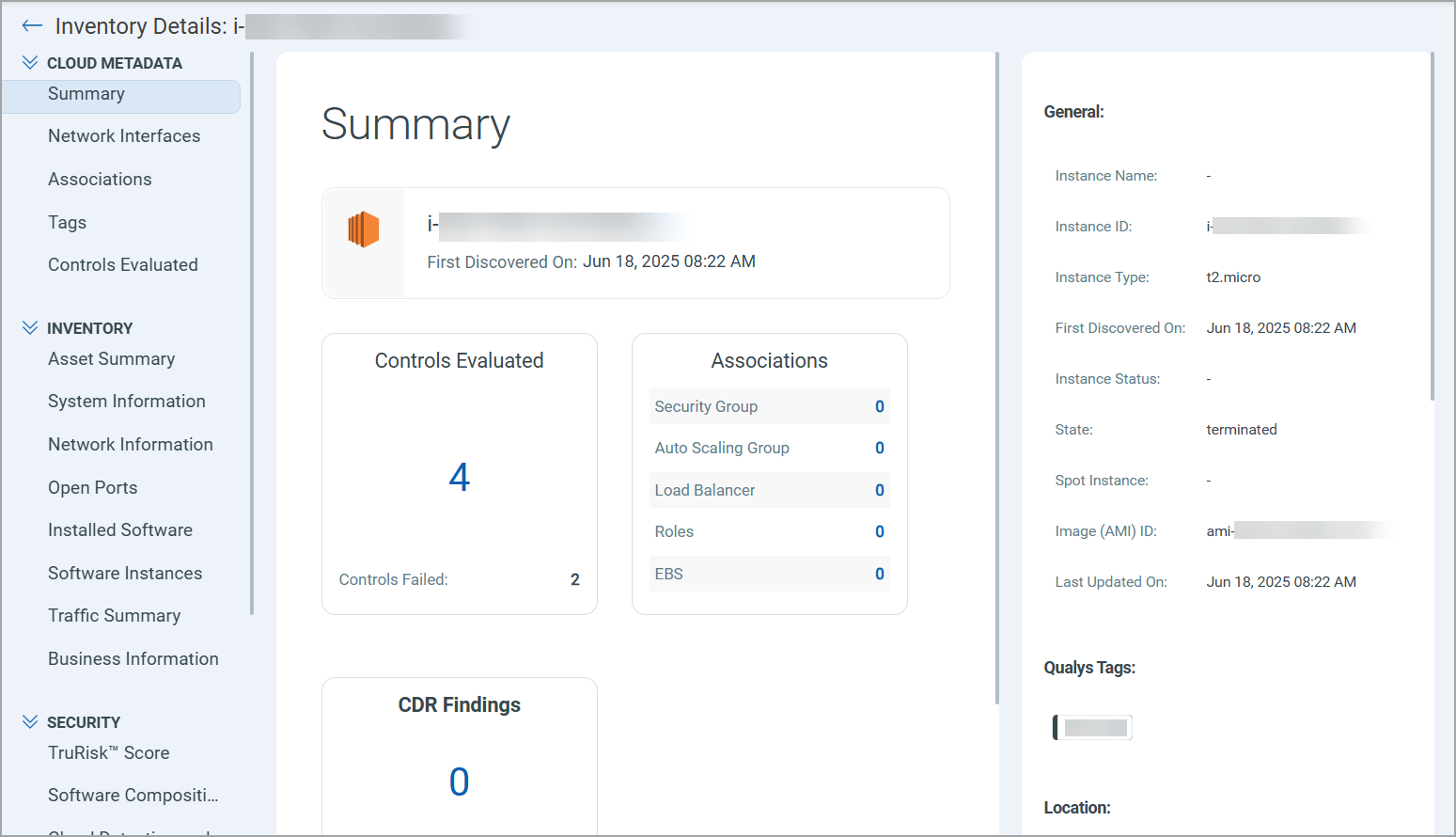
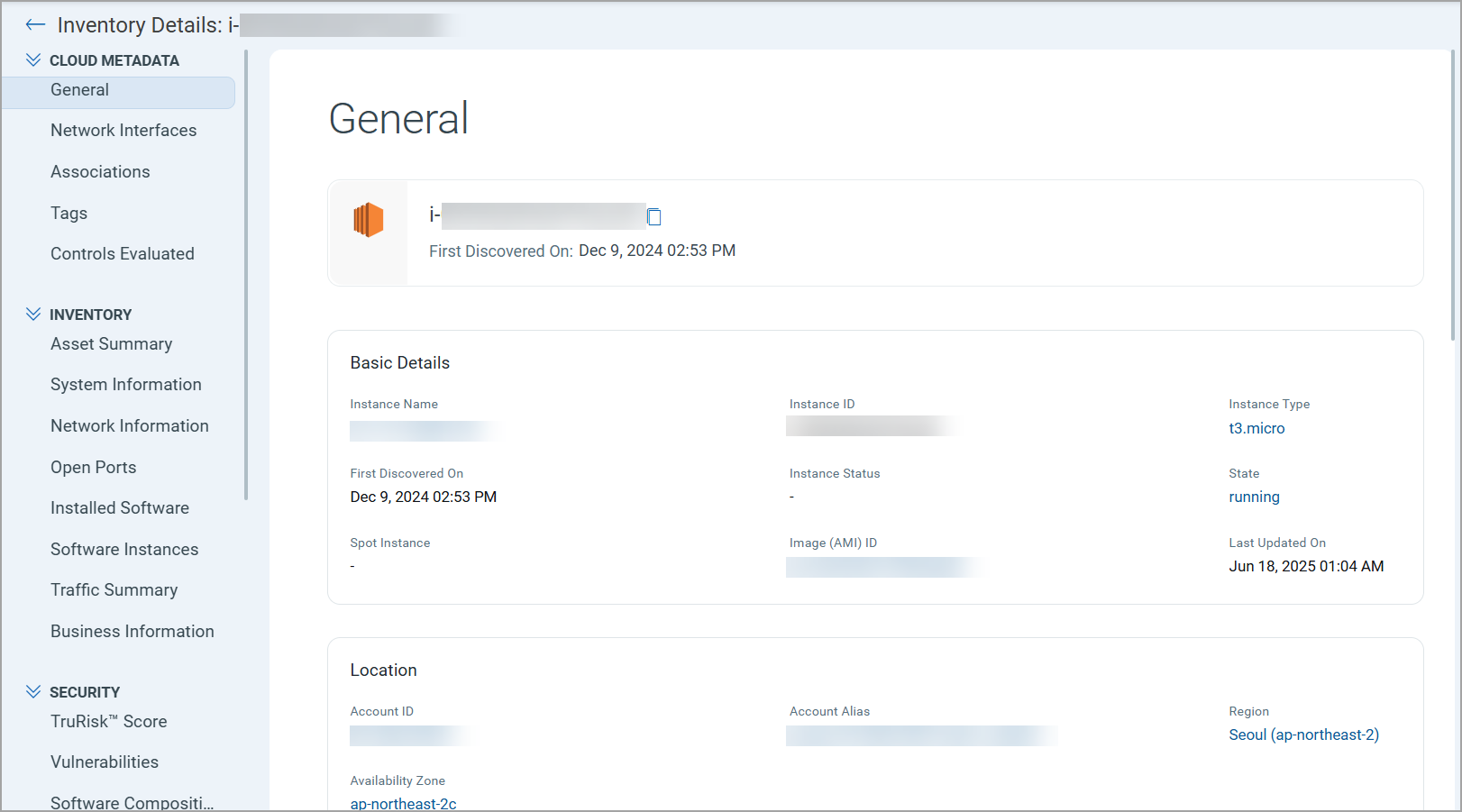
Redesigned Summary Details Screen for Inventory Details Workflow
The Summary Details screen within the Inventory Details workflow has been completely redesigned to enhance user experience and improve data clarity. The new layout provides a more intuitive interface, making it easier to view and manage inventory information efficiently.
Previous summary screen:
New redesigned summary screen:
Microsoft Azure
The following sections describe the enhancements made to the TotalCloud environment in this release for Azure.
New Insights with Azure Attack Path Visualization Support
With this release, we are adding new insights to improve visibility into potential risks in your cloud environment. Additionally, support for Attack Path visualization has been expanded to include these new insights, helping you better understand and analyze how these risks could be exploited in attack scenarios.
| Insight CID | Title |
|---|---|
| 5095 | Privilege escalation risk on public and vulnerable VM with active port scan |
| 5142 | Critical and exploitable vulnerability detected on public VM with attached disk not encrypted with CMEK |
| 5143 | Successful RDP brute-forcing on public VM with exposed attached disk |
| 5144 | Malware detected on public VM with attached disk not encrypted with CMEK |
| 5145 | Active Port scan on VM with SSH port exposed to internet |
| 5146 | C2 HTTP/HTTPS detected on VM with RDP port exposed to internet |
| 5147 | Public VM with vulnerability associated to ransomware with attached disk not encrypted with CMEK |
| 5148 | CISA known exploitable vulnerability on public VM with RDP port exposed to internet |
| 5149 | Qualys predicted high risk vulnerabilities on public VM |
| 5150 | Public VM with vulnerability detected with potential remote code execution exploitation risk |
Cloud Detection and Response (CDR)
The following sections describe the enhancements made to the CDR environment in the upcoming CDR release.
These CDR enhancements will be available by the end of July.
Exception Handling for Threat Findings
With this release, we have added a new exception handling feature that that enhances your ability to manage threat findings with greater precision. This feature allows you to:
- Define custom exception rules to filter out specific future threat findings.
- View all exceptions separately in the new "Risk Acceptance Rules" tab. This will allow for more precise threat detection and management and ensure that exceptions are handled efficiently.
In addition, you can now view the detailed findings associated with each exception rule. Simply click on the number of findings displayed next to a rule in the Risk Acceptance Rules tab. This will take you directly to the Investigate tab, where you can see a list of all related findings for that specific exception rule.
Navigate to Responses > Risk Acceptance Rules to create and manage Exception Rules and view the total security findings corresponding to them.
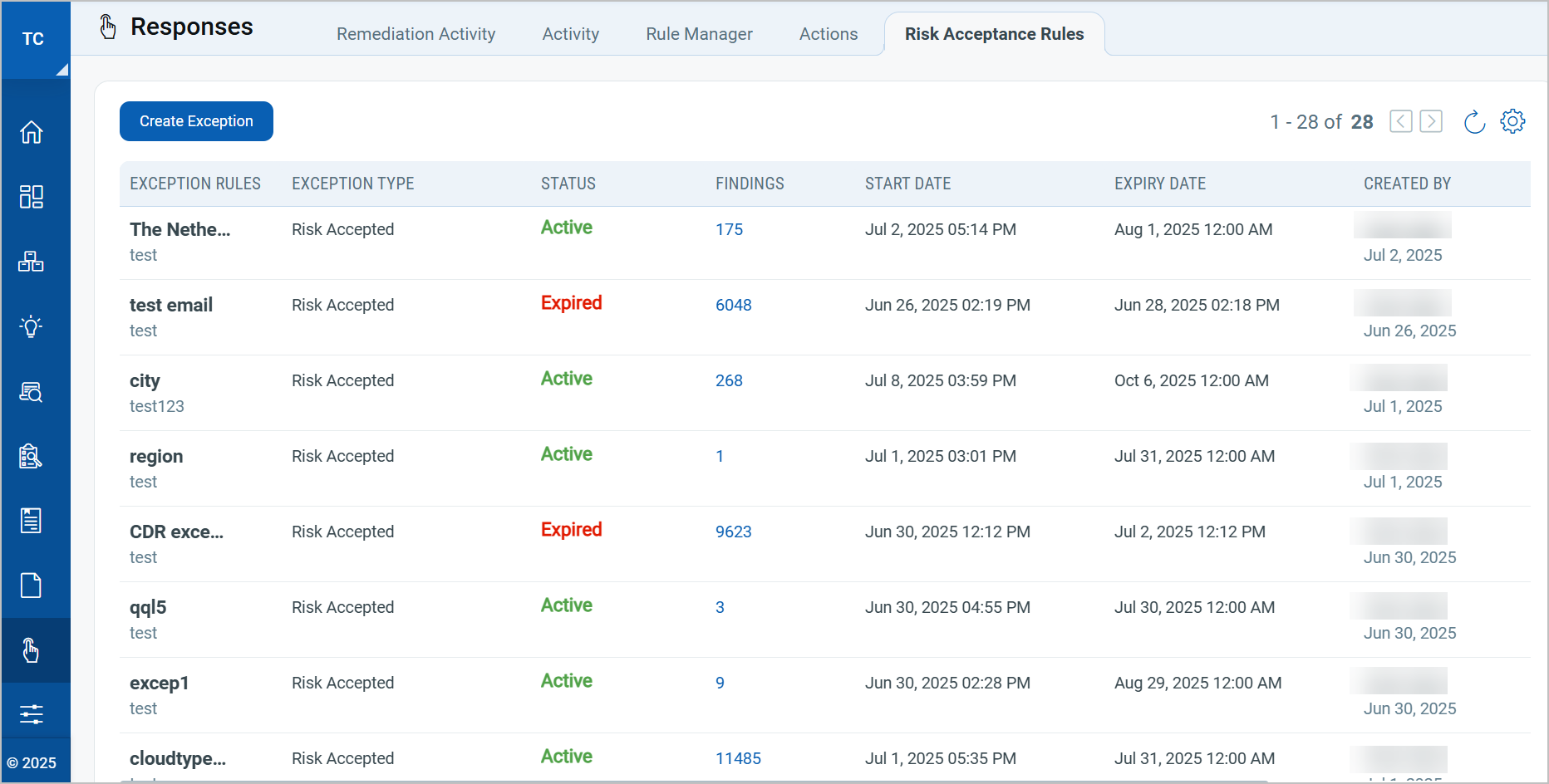
To learn more, refer to the Responses section of the TotalCloud Online Help.
Connection-based Analysis for AWS Appliances
With this release, we are introducing a new feature that analyzes network connection-based events for AWS appliances within the CDR Investigate tab. This enhancement allows you to gain deeper visibility into network activity.
These events offer detailed visibility into network activity, including:
- Total number of inbound and outbound communications.
- Data volume uploaded and downloaded.
- Originator and destination IP addresses.
- The timestamp and duration of each event.
- Appliance-level association for each event.
To support this capability, a new "Events" page has been added to the Investigate tab. This page allows users to explore and analyze network events in greater detail.
Additionally, we have introduced new search tokens to help you filter and refine search results more effectively, based on specific requirements.
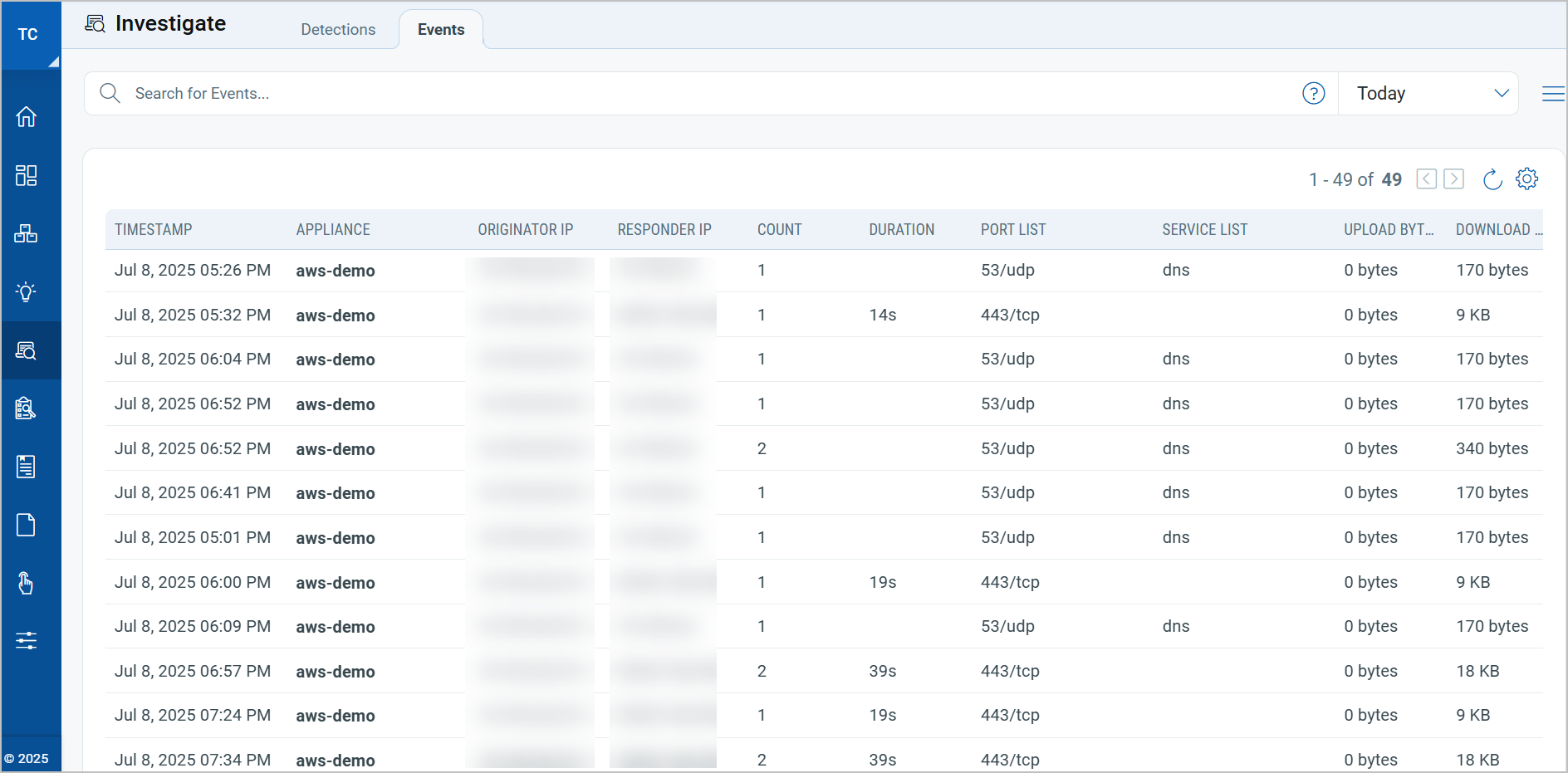
This feature will be available following the release of Container Security version 1.40.0.
Control Updates
New Runtime Controls
New runtime controls introduced to the cloud posture analysis.
New Controls in Amazon Web Services
New Controls for AWS Without Policy Attachment.
| CID | Title | Service | Resource |
|---|---|---|---|
| 561 | Ensure S3 general purpose bucket policies restricts access to other AWS accounts | S3 | BUCKET |
New Controls in Microsoft Azure
New Controls in CIS Microsoft Azure Foundation Benchmark Policy
| CID | Title | Service | Resource |
|---|---|---|---|
| 50483 | Ensure Allow storage account key access for Azure Storage Accounts is Disabled | STORAGE_ACCOUNT | STORAGE_ACCOUNT |
| 50484 | Ensure that an Activity Log Alert exists for Service Health | MONITOR | ACTIVITY_LOG_ALERT |
| 50486 | Ensure Versioning is set to Enabled on Azure Blob Storage storage accounts | STORAGE_ACCOUNT | STORAGE_ACCOUNT |
| 50487 | Ensure that Notify about attack paths with the following risk level (or higher) is enabled | SECURITY_CENTER | SECURITY_POLICY |
| 50488 | Ensure soft delete for Azure File Shares is Enabled | STORAGE_ACCOUNT | STORAGE_ACCOUNT |
| 50489 | Ensure SMB protocol version is set to SMB 3.1.1 or higher for SMB file shares | STORAGE_ACCOUNT | STORAGE_ACCOUNT |
| 50490 | Ensure SMB channel encryption is set to AES-256-GCM or higher for SMB file shares | STORAGE_ACCOUNT | STORAGE_ACCOUNT |
New Controls in Oracle Cloud Infrastructure
New controls in Oracle Cloud Infrastructure Best Practices Policy
| CID | Title | Service | Resource |
|---|---|---|---|
| 40089 | Ensure Compute Instances are configured with required tags | COMPUTE | INSTANCE |
| 40090 | Ensure only required Compute Instances have been assigned with Public IP | COMPUTE | INSTANCE |
New controls in CIS Oracle Cloud Infrastructure Foundation Benchmark Policy
| CID | Title | Service | Resource |
|---|---|---|---|
| 40091 | Ensure a notification is configured for Local OCI User Authentication | EVENTS_SERVICE | RULE |
| 40092 | Ensure there is only one active API Key for any single OCI IAM user | IAM | IAM_USER |
Control Title Changes
Changes to control titles.
| Platform | CID | Old Title | New Title |
|---|---|---|---|
| AWS | 302 | Ensure that DAX is encrypted at rest (default is unencrypted) | Ensure DAX is encrypted at rest |
| Azure | 50331 | Ensure azure spring cloud service apps have end to end TLS enabled | Ensure azure spring cloud service apps have Ingress-to-app (end-to-end) TLS enabled |
| Azure | 50335 | Ensure TLS Version is set to TLSV1.2 for MySQL flexible Database Server | Ensure TLS Version is set to TLSv1.2 or latest for MySQL flexible Database Server |
Control Migration
Migration from Annotation to DCEF
| Platform | CID | Title |
|---|---|---|
| AWS | 119 | Ensure no default Key Management Service (KMS) Key is used to protect secrets |
Migration of Azure Controls:
| Platform | CID | Current Policy | Migrated Policy |
|---|---|---|---|
| Azure | 50188 Ensure that Blob Storage is configured with Diagnostic Settings |
Azure Best Practice Policy | Azure CIS Policy |
| Azure | 50190 Ensure that Queue Storage is configured with Diagnostic Settings |
Azure Best Practice Policy | Azure CIS Policy |
| Azure | 50191 Ensure that Table Storage is configured with Diagnostic Settings |
Azure Best Practice Policy | Azure CIS Policy |
Controls Deprecated for AWS and Azure Best Practices Policy
With this release, we have deprecated the following controls for the AWS and Azure Best Practices Policy.
| Cloud Provider | CID | Service | Resource | Title |
|---|---|---|---|---|
| AWS | 327 | Cloudfront | Cloudfront Distribution | Ensure Cloudfront Distribution has Access Logging Enabled. |
| Azure | 50215 | Storage Account | Storage Account | Ensure Storage logging is Enabled for Queue Service for 'Read', 'Write', and 'Delete' requests. |
| Azure | 50246 | Data Lake Storage | Data Lake Storage | Ensure that encryption is enabled for Data Lake Store accounts. |
| Azure | 50275 | Data Lake Storage | Data Lake Storage | Ensure that Diagnostic logs are enabled in Azure Data Lake Storage accounts. |
| Azure | 50455 | Storage Account | Storage Account | Ensure Storage logging is Enabled for Blob Service for 'Read', 'Write', and 'Delete' requests. |
| Azure | 50456 | Storage Account | Storage Account | Ensure Storage logging is Enabled for Table Service for 'Read', 'Write', and 'Delete' requests. |
New Tokens
The following section describes the new tokens introduced as part of TotalCloud 2.18.0
AWS Tokens
This new AWS Inventory token is introduced with TotalCloud 2.18.0.
| Name | Description | Example |
|---|---|---|
| iam.classification | Find all the resources that are associated with the specific classification flag. This token is supported for the below resource types:
|
iam.classification: "Administrative With All Resources And No Condition" |
These new AWS tokens are introduced for Instance resources with TotalCloud 2.18.0.
| Name | Description | Example |
|---|---|---|
| instance.scanType | Use this to filter cloud instances based on the type of scan. Available options are: (API Based Scan, Cloud Agent Scan, Cloud Perimeter Scan, Snapshot Based Scan, VM Scan, and Other Scan)
|
instance.scanType: "API Based Scan" |
| instance.firstScanDate | Use this to filter instances based on the timestamp at which they were first scanned using any of the available scan techniques. | instance.firstScanDate: "2025-04-08" |
| instance.lastScanDate | Use this to filter instances based on the timestamp at which they were last scanned using any of the available scan techniques. | instance.lastScanDate: "2025-04-14" |
Azure Tokens
These new AWS tokens are introduced for Virtual Machine resources with TotalCloud 2.18.0.
| Name | Description | Example |
|---|---|---|
| virtualmachine.scanType | Use this to filter VM resources based on the type of scan. Available options are: ( Cloud Agent Scan, Cloud Perimeter Scan, Snapshot Based Scan, VM Scan, and Other Scan.) |
virtualmachine.scanType: "Cloud Agent Scan" |
| virtualmachine.firstScanDate | Use this to filter VMs based on the timestamp at which they were first scanned using any of the available scan techniques. | virtualmachine.firstScanDate: "2025-04-08" |
| virtualmachine.lastScanDate | Use this to filter VMs based on the timestamp at which they were last scanned using any of the available scan techniques. | virtualmachine.lastScanDate: "2025-04-14" |
GCP Tokens
These new GCP tokens are introduced with TotalCloud 2.18.0.
| Name | Description | Example |
|---|---|---|
| instance.scanType | Use this to filter VM instances based on the type of scan. Available options are: ( Cloud Agent Scan, Cloud Perimeter Scan, and Other Scan) |
instance.scanType: "Cloud Perimeter Scan" |
| instance.firstScanDate | Use this to filter VM Instances based on the timestamp at which they were first scanned using any of the available scan techniques. | instance.firstScanDate: "2025-04-08" |
| instance.lastScanDate | Use this to filter VM Instances based on the timestamp at which they were last scanned using any of the available scan techniques. | instance.lastScanDate: "2025-04-14" |
| subnetwork.ipv6Prefix | Use this to filter subnetwork resources based on the IPv6 Prefix (IPv6 CIDR Range) | subnetwork.ipv6Prefix: 'fd2X:XXX:XXXX:X:X:X:X:0X/64' |
CDR Investigate Tokens
These new Investigate tokens are introduced with TotalCloud 2.18.0.
| Name | Description | Example |
|---|---|---|
| event.destination.ip | Use this to filter network events by a specific destination IP address or a range of destination IP addresses. | event.destination.ip: "10.10.0.0"or, event.destination.ip > "10.0.0.0"
|
| event.destination. location.city |
Use this to filter network events based on the city associated with the destination IP. | event.destination.location.city: "Boardman" |
| event.destination. location.continent |
Use this to filter network events based on the continent associated with the destination IP. | event.destination.location.continent: "North America" |
| event.destination. location.country |
Use this to filter network events based on the country associated with the destination IP. | event.destination.location.country: "United States" |
| event.destination. location.region |
Use this to filter network events based on the region associated with the destination IP. | event.destination.location.region: "Oregon" |
| event.source.ip | Use this to filter network events by a specific source IP address or a range of source IP addresses. | event.source.ip: "10.10.0.0"or, event.source.ip > "10.0.0.0"
|
| event.source. location.city |
Use this to filter network events based on the city associated with the source IP. | event.source.location.city "Redmond" |
| event.source. location.continent |
Use this to filter network events based on the continent associated with the source IP. | event.source.location.continent: "North America" |
| event.source. location.country |
Use this to filter network events based on the country associated with the source IP. | event.source.location.country: "United States" |
| event.source. location.region |
Use this to filter network events based on the region associated with the source IP. | event.source.location.region: "Oregon" |
| event.appliance. name |
Use this to filter network events based on the appliance name. | event.appliance.name: "aws-appliance-1" |
| event.service | Use this to filter network events based on the network service. | event.service: "dns" |
| event.cloudType | Use this to filter network events based on the cloud provider. | event.cloudType: "AWS" |
| event.protocol | Use this to filter network events based on the network protocol. | event.protocol: "TCP" |
| event.port | Use this to filter network events based on the network port. | event.port: "53/udp" |
| event.traffic.out | Use this to filter network events by a specific range of uploaded data size. | event.traffic.out: > 1000
The data size must be specified in bytes. |
| event.traffic.in | Use this to filter network events by a specific range of downloaded data size. | event.traffic.in: > 1000
The data size must be specified in bytes. |
| event.traffic.total | Use this to filter network events based on total data transfer in bytes (upload + download). | event.traffic.total: > 1000 |
| tc.findings. exception.id |
Search findings based on exception Id's |
tc.findings.exception.id: 12345 |
| tc.findings. exception.name |
Search findings based on exception names |
tc.findings.exception.name: Exception_1 |
Issues Addressed
The following reported and notable customer issues are fixed in this release:
| Category/Component | Issue |
|---|---|
| CV-False Positive | We updated the detection logic of the following controls to resolve false positive cases - CID 539, 50250, 50393, and deprecated the control CID 327. |
| CV-False Negative | We updated the detection logic of the following controls to resolve false negative cases - CID 50215, |
| CV-Monitor | We have resolved the issue where the number of virtual machines was not displayed in the table view when using the query: virtualmachine.status: VM running |
| CV-UI | We have resolved the syntax help issue for the QQL token "iam.classification" |
| CV-Resources | We have resolved the issue where Redis resources were not visible in the TotalCloud Inventory. |
| CV-API | We have resolved the issue where API requests for the last page of data returned a null value along with a 500 INTERNAL SERVER ERROR. |
| CV-Monitor, TotalCloud-Portal | We have resolved the issue where inaccurate vulnerability data was being fetched for resources. The problem was caused by the incorrect mapping of the new asset ID, which led to the data discrepancies. |
| CV - Azure Connector | We have enhanced the control CID: 500335 to support the latest TLS versions. |
| CV-RemediationClarification | We have updated the title and remediation steps for the following controls according to the new Azure Portal: CID 50331, 50365. |
| CV - UI, Documentation | We have resolved an issue where the vulnerability.customerSeverity token displayed incorrect help description. |