EDR Release 3.3
May 20, 2024
What's New?
Connect to Host using Linux Operating Systems
We have added support for the Linux Operating Systems for the Connect to Host option in the Quick Actions menu of the Assets tab. Using the following Linux commands, you can access endpoints directly from the Qualys console. The Connect to Host option is available for Linux Agent 6.3.0 and above. Use the following commands for the Linux OS :
- auditctl
- dpkg
- rpm
For information about Connect to Host, refer to EDR Online Help.
New Remediation Status: Queued
From this release, we have added Queued as the initial status when you perform a Quarantine, Unquarantine, or any remediation action. Thus, the statuses are- Queued, Success, and Failed. The InProgress status is no longer available.
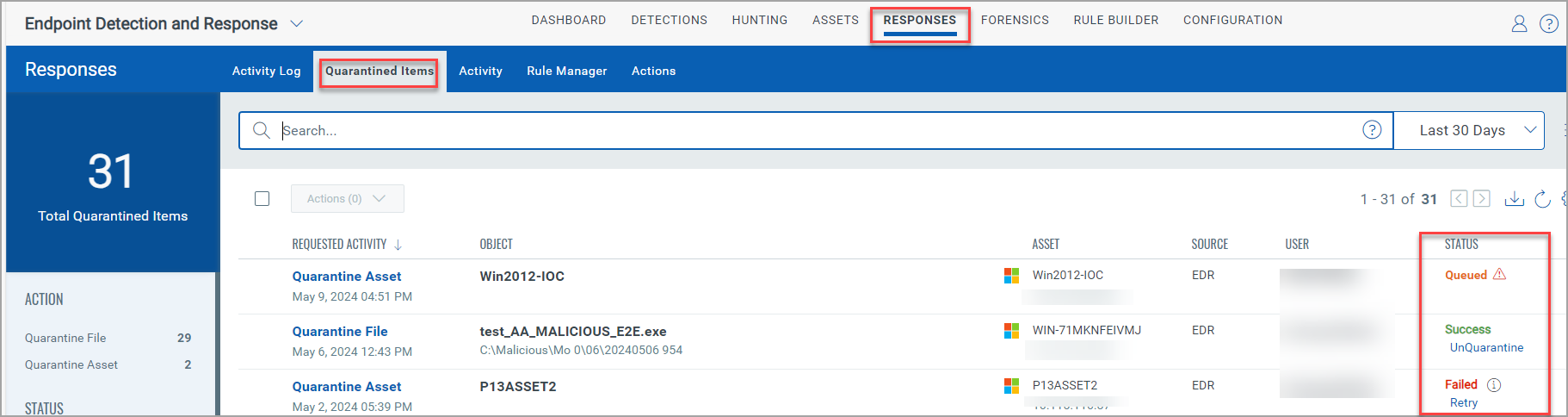
The following screenshot highlights all the three statuses in the Quarantined Items tab under Responses:
Upload .JSON file to Exclude Instances from Scans
While configuring the anti-malware profile in the Exclusions step, you can now upload a .JSON file and exclude the instance from the scan. This option was initially available only for the File Scan. However, you can now perform this action for the Behavioral Scan, Network Protection Scan, and Device Control. You can upload a JSON file up to 2 MB.
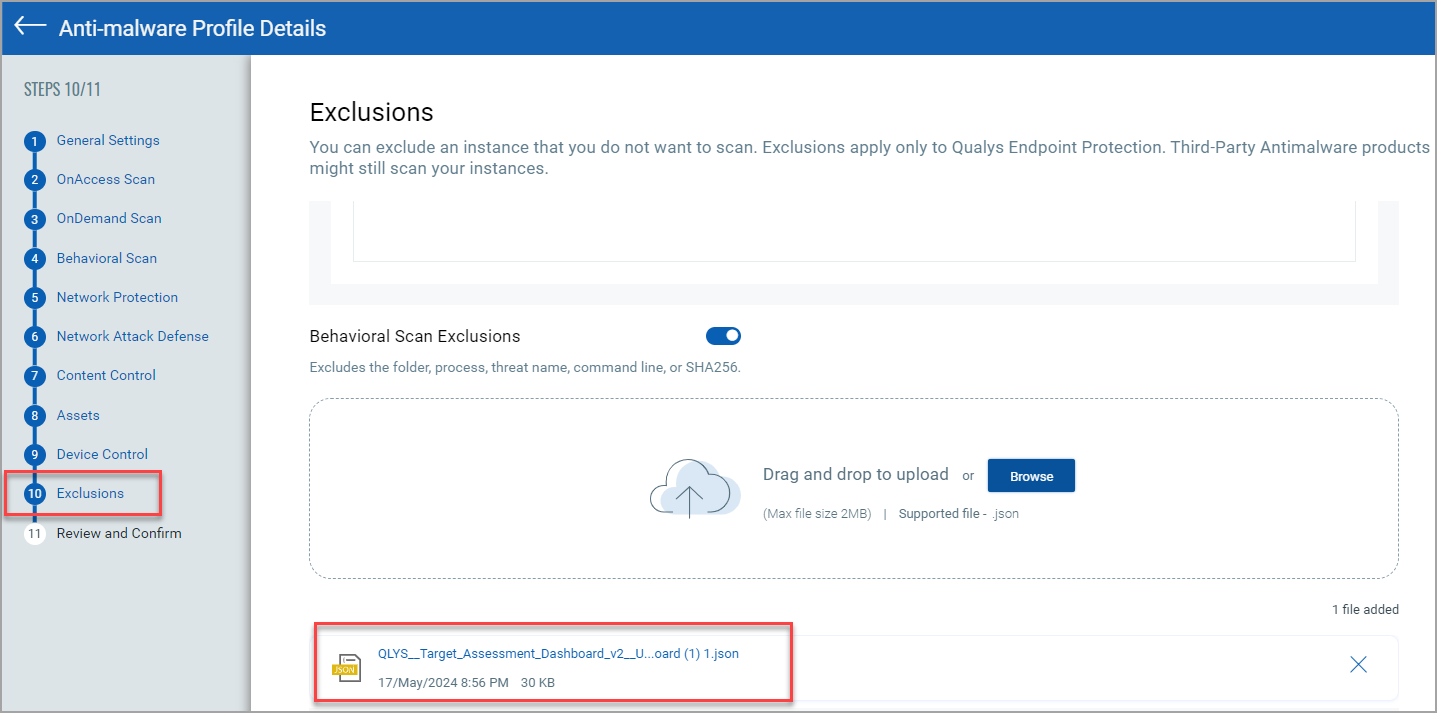
The following screenshot highlights the .JSON file uploaded to exclude during the Behavioral Scan:
To view sample .JSON files, refer to Exclusion Support in EDR Online Help.
Bulk Unquarantine Assets
You can now unquarantine assets in bulk; this reduces the time spent unquarantining the assets one at a time. The Bulk Unquarantine Assets action can be performed in the Assets tab. After the assets are successfully unquarantined, the Activity Log under the Responses tab lists the assets. However, the asset names are not listed in the Activity Log for Bulk UnQuarantine assets.
Points to consider for Bulk Unquarantine Assets using QQL tokens
- There is no limit on the number of assets that can be selected when using a QQL token.
- Upon searching and selecting a set of assets using QQL tokens and executing the bulk unquarantine asset action, a single bulk unquarantine job is generated. This job encompasses all impacted assets associated with the query.
Points to consider for Bulk Unquarantine Assets using the menu option
- You can unquarantine up to 100 assets without using the QQL tokens.
- When you select up to 100 quarantined assets from the Assets page and initiate the bulk unquarantine asset action, individual unquarantine requests are raised for each selected asset. Consequently, no bulk unquarantine asset job is created. Instead, all unquarantine actions are recorded and listed in the Activity Log.
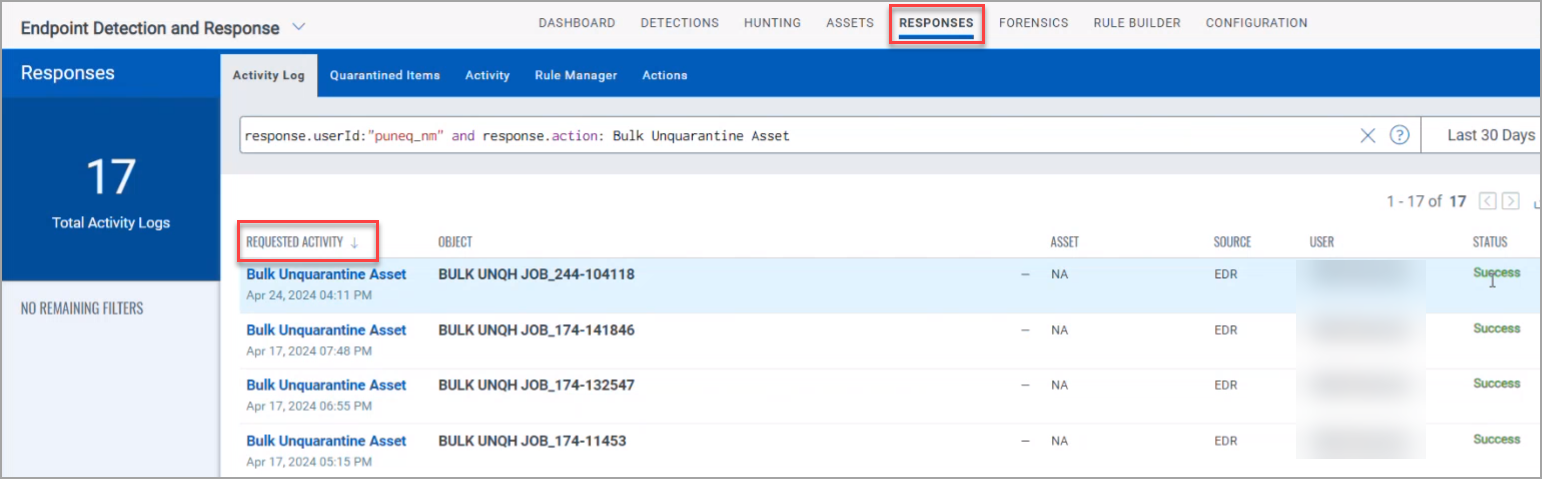
The following screenshot is an example of the bulk unquarantine option in the Assets tab:
For information about Bulk Unquarantine Assets, refer to EDR Online Help.
Use Allow IPs Option during Quarantine Asset Configuration
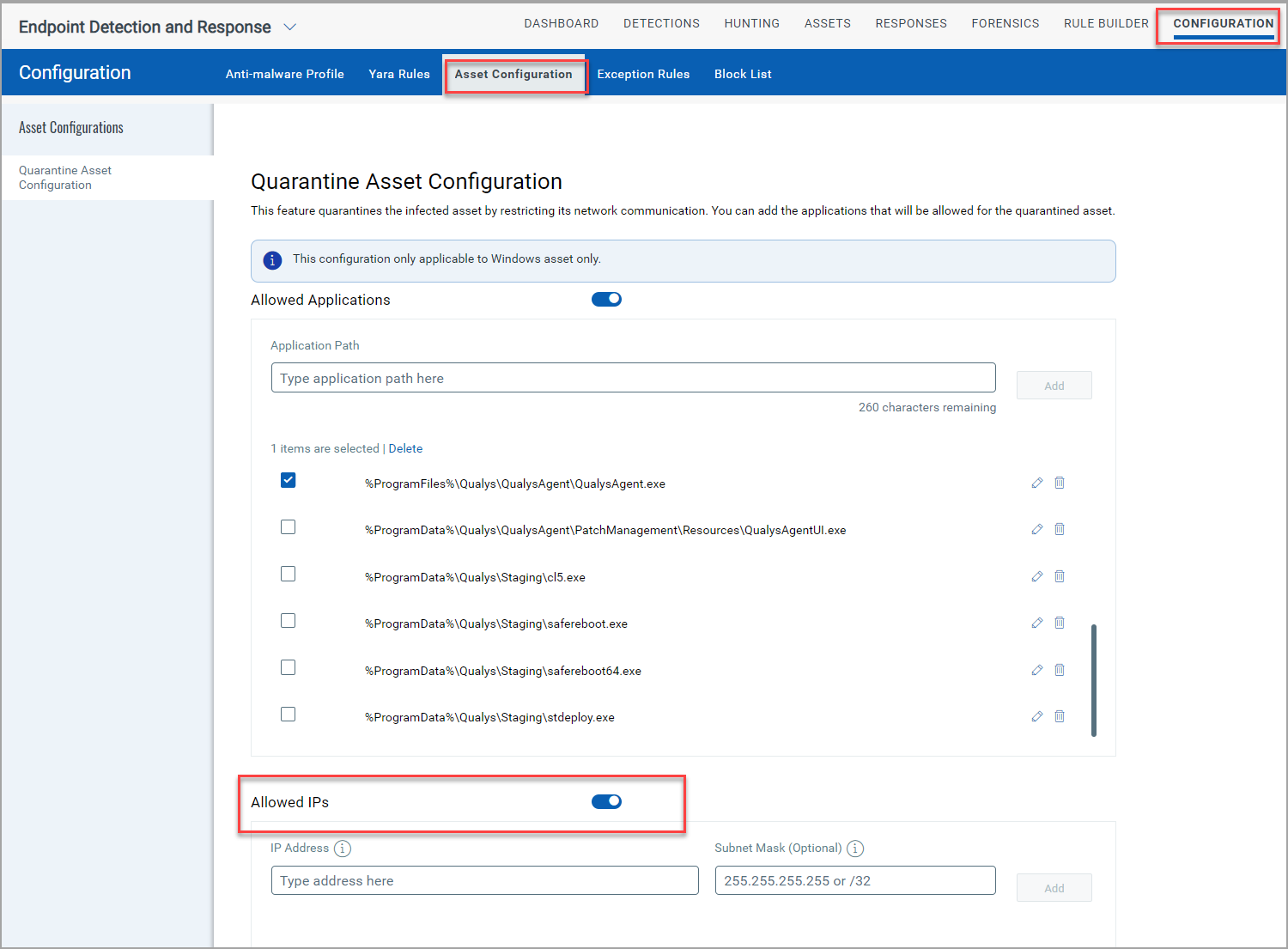
The Asset Configuration under the Configuration tab now has the Allowed IPs toggle. Enable the Allowed IPs toggle to allow the list of IP addresses during the Quarantine Asset configuration. The following screenshot is an example of the Allowed IPs toggle enabled:
For information about Quarantine Assets, refer to EDR Online Help.
Create Exception Option Added in the Alerts tab
From the Quick Actions menu of the Alerts under the Detections tab, you can select the Create Exception option to create rules to suppress a past or a future event that you consider non-malicious. The following screenshot is an example of the Create Exception in the Quick Actions menu of the Alerts tab:
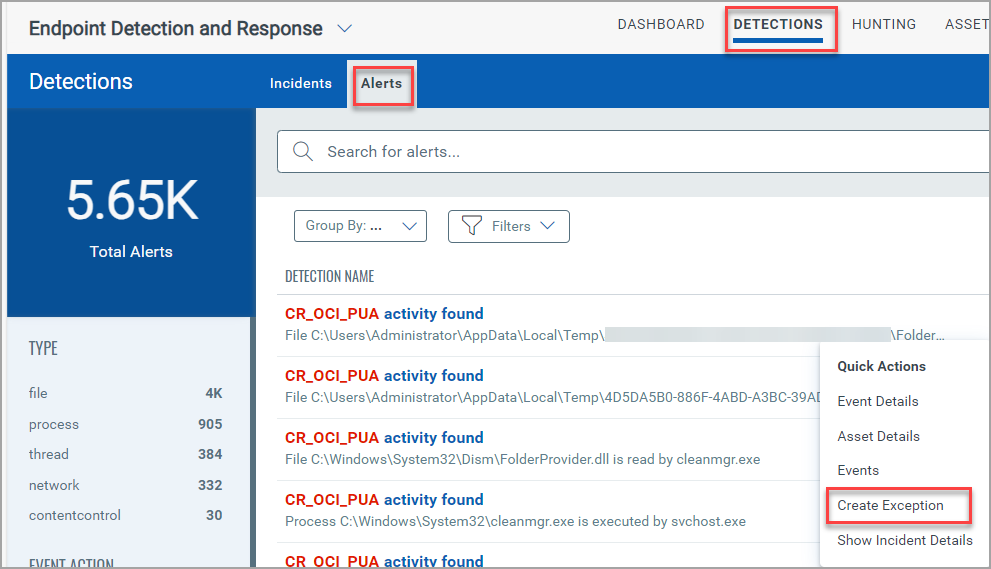
For more information about Create Exception, refer to EDR Online Help.
Enhancements in Forensics Collections
The Forensics Collection is now available for Process Memory Dump. This type of forensic collection allows you to collect data from active running processes, which will help you investigate and analyze system malicious activities. The .dmp file extension is created for the process memory dump.
The following screenshot is an example of the Process Dump in the Forensics tab:
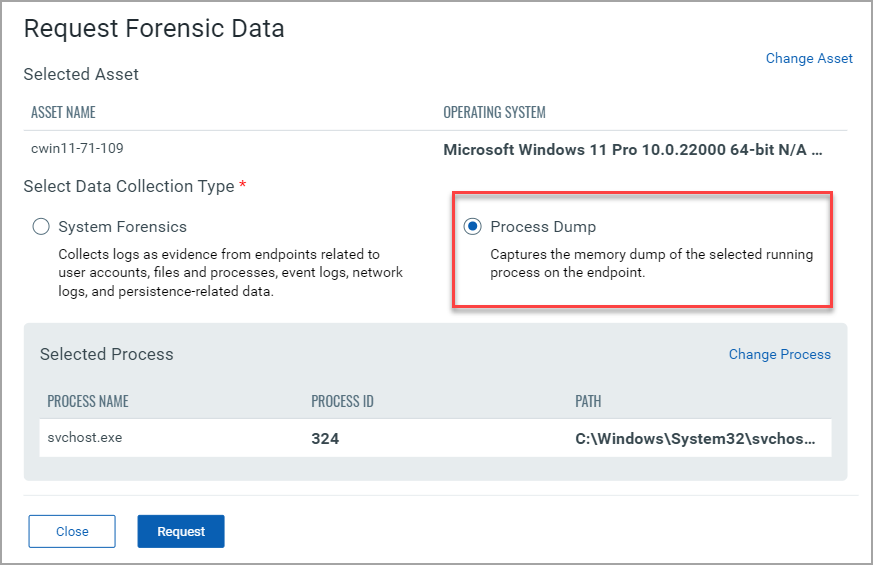
For more information about Forensics Collection, refer to Request Forensic Data in EDR Online Help.
Updated AMSI commands for the Events tab
The amsi.command and amsi.command.length has now been updated to amsi.buffer and amsi.buffer.length. This change applies only to the Events tab under Hunting.
Updated EDR and EPP Scoring Events
The EDR and EPP scoring events help you prioritize the events. The Protection Mode and the Detection Mode in the table signify the Primary and Secondary actions you select while configuring the Antimalware Profile in the Configuration tab. The following screenshot is an example of the File Event with Application as a threat:
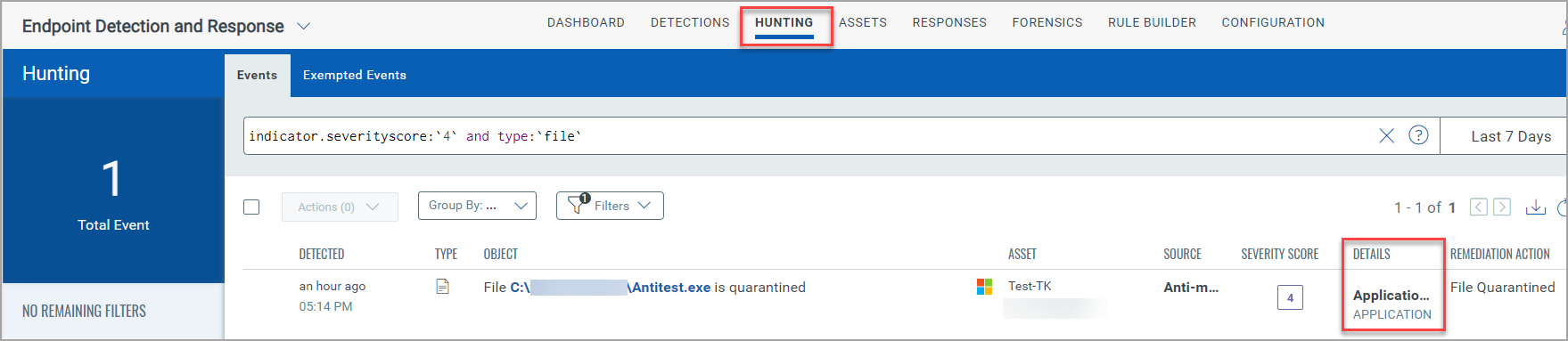
The following table lists the EPP and its respective EDR scoring events:
| EPP Event | EDR Event | Protection Mode Score | Detection Mode Score |
| Anti-Exploit | ProcessEvent | 7 | 8 |
| Anti-Phishing | NetworkEvent | 4 | 4 |
| Behavioral | ProcessEvent | 5 | 6 |
| File Scan (On Demand and On Access) | FileEvent | 6 | 8 |
| File Scan | ThreatName -Application and Adware | FileEvent | 4 | 4 |
| Network-Monitor | NetworkEvent | 6 | 9 |
| Fileless-AMSI | ProcessEvent | 5 | 6 |
| Fileless-Cmdline | FileEvent | 5 | 6 |
| Device-Control | DeviceControl | NA | NA |
| Content-Control | UserControl | 4 | NA |
| Traffic-Scan | NetworkEvent | 6 | 8 |
| Traffic Scan | Threat Name - CloudVirus | NetworkEvent | 4 | 4 |
| Anti-Ransomware | ProcessEvent | 8 | 9 |
Auto-Remediation Search Tokens
We added the following new search tokens for the auto-remediation rule trigger.
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
To know more about these Search Tokens, refer to the EDR Online Help.