Managing Events
With FIM, you receive real-time updates about anomalous activities that are detected. These updates (events) are sent with complete granular details such as who-what-when-where, about the changes occurring within the scope of your monitored area. Events can be expected and authorized or unexpected and malicious.
FIM provides one central location for viewing all of the events detected across all of your assets. The Events tab contains capabilities to search for events, group by options, and download the results.
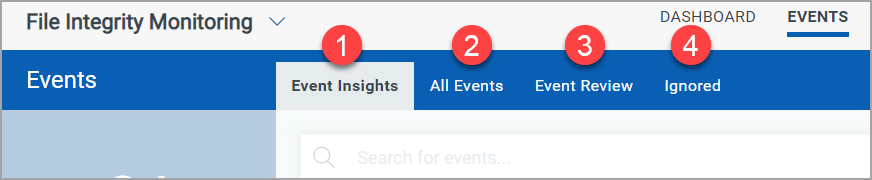
Use tabs in the Events section to quickly identify:
![]() Event Insights: View the rules, profiles, processes, and users that have generated the highest number of events.
Event Insights: View the rules, profiles, processes, and users that have generated the highest number of events.
![]() All Events: The events detected across all your assets are listed under this tab.
All Events: The events detected across all your assets are listed under this tab.
![]() Event Review: You can take actions such as ignoring events or creating incidents on the registered events from this tab. Only those events that are not mapped to an incident are listed on the Event Review tab.
Event Review: You can take actions such as ignoring events or creating incidents on the registered events from this tab. Only those events that are not mapped to an incident are listed on the Event Review tab.
![]() Ignored: Events ignored from the Event Review tab are moved to this tab.
Ignored: Events ignored from the Event Review tab are moved to this tab.
All the date-related events on the cloud agent happen in the UTC zone with respect to the Asset time zone. The actual results in the UI show you the date as per your time zone. In addition, the Generated Report has Date Time in UTC with respect to the Asset time zone.
To add a folder path for file.fullPath and actor.imagePath QQL, user should avoid using “ \” at the end of the path as it results in invalid QQL while searching.
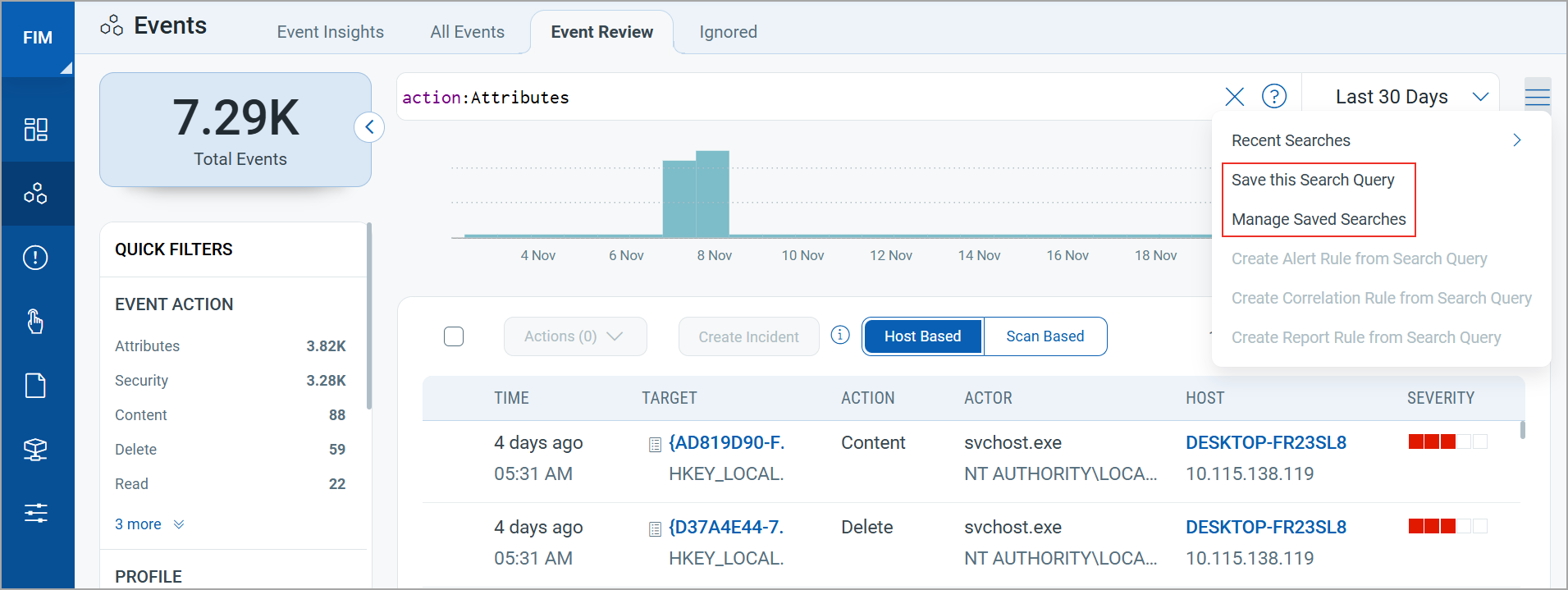
Searching for Events Using QQL
You can search events based on some criteria using the Qualys Query Language (QQL). For more information on QQL, see Search Tutorial and How to search. These searches can then be saved using the 'Save this Search Query' option. For more information, refer to the Search Action topic.
- The file.hash QQL token is supported only for PE files on Windows. On Linux, all types of files are supported.
- The actor's column in the Events List is not available for the AIS operating system host's events. Instead, you can view 'not applicable' there.
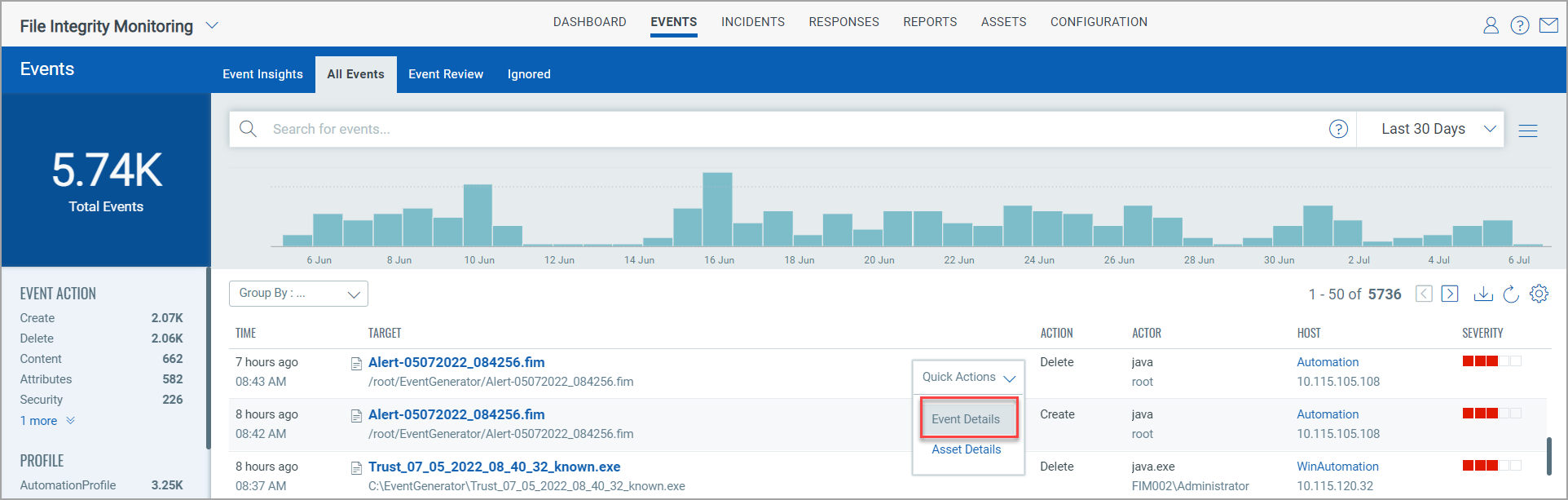
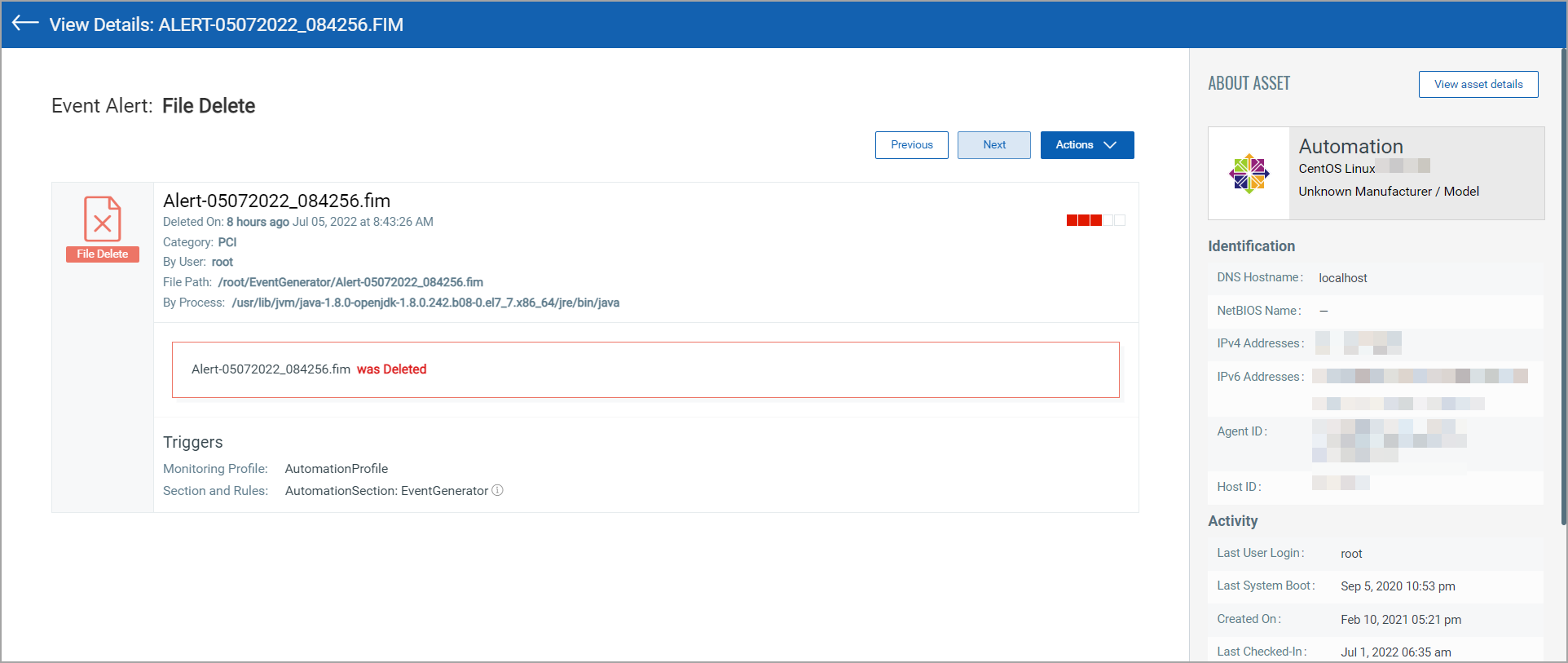
Viewing Event Details
Clicking Event Details in the Quick Actions for an event brings up the Event Details page. This page provides complete information about the FIM event.
FIM on Containers and FIM on network devices is the requirement of PCI DSS 4.0. Container based FIM is available on demand. Contact your Technical Account Manager (TAM) to activate this feature.
You can view FIM events detected by different sources, such as:
- Container Based
Events originating from dynamic container environments. The Qualys Enterprise TruRisk™ Platform stores any activity on the monitored locations in the containers for 13 months, even though the containers are short-lived. - Host Based
Events originate from hosts equipped with the Qualys Cloud Agent. - Scan Based
Events originate from network devices and databases, which send events at regular scan intervals.
To monitor databases, you must configure a script in the Custom Assessment and Remediation (CAR) module. For more information, refer to Database Monitoring with FIM.
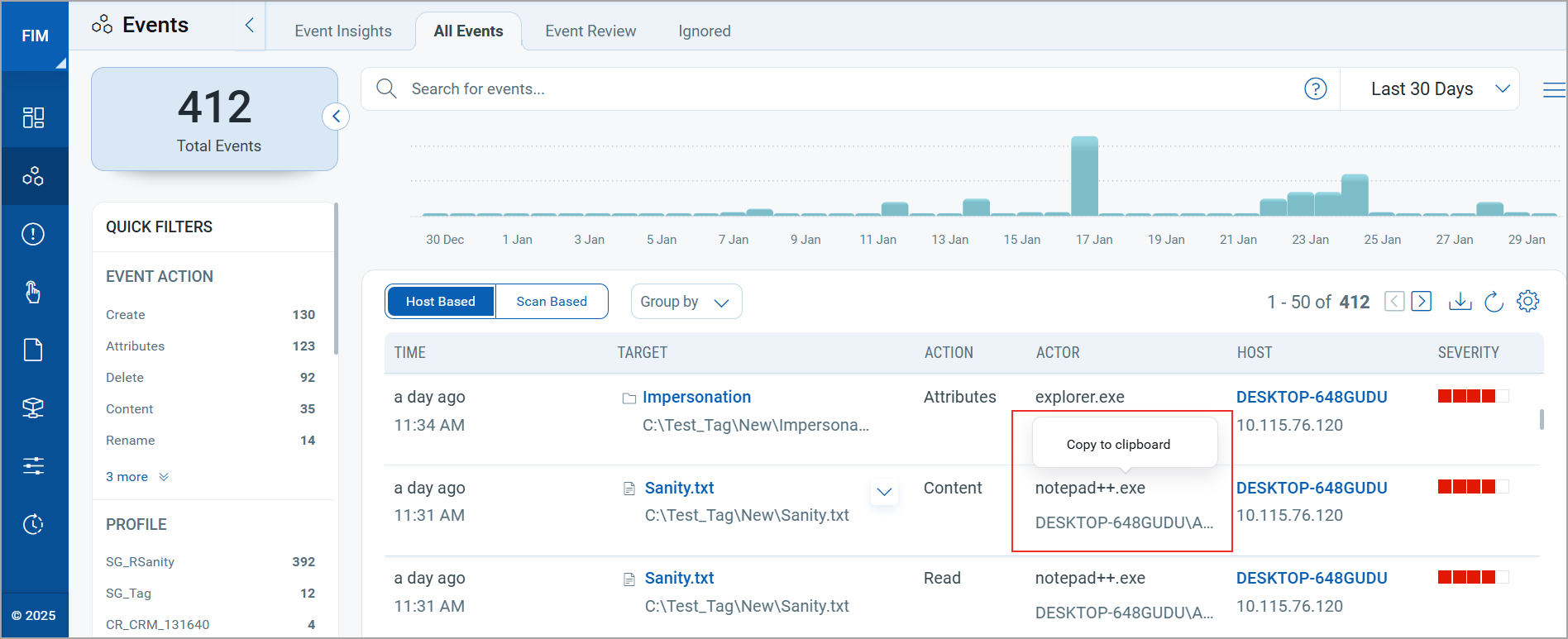
Copy Users and Processes
You can copy the user and process details directly to the clipboard from the FIM Events listing page. This allows you to copy the data without opening the event details.
Hover over a user or process on the Actor column and click to copy the data.
View the list of Events
You can sort and view the list of events based on specific hosts or scan results on All Events tab | Event Review tab | Ignored tab | Incidents Details page.
You can view the event by using Group by filter based on Host, Operating System, Monitoring Profile, Severity, or Platform.
The QQLs actor.process, actor.UserID, actor.UserName, actor.imagePath are not supported for FIM assets on AIX, hence no data is fetched for AIX assets if you use these QQLs and the Actor column does not display any data.
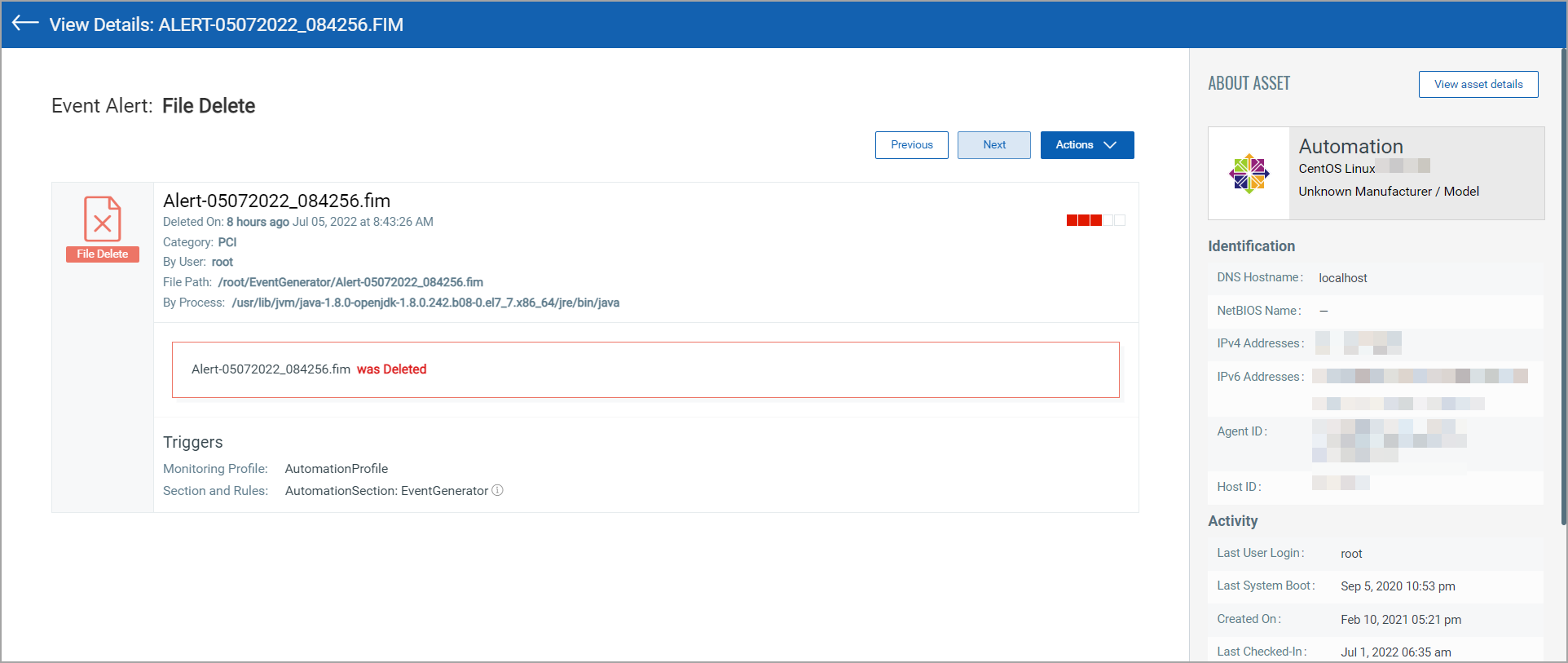
You can view the event details with the asset name, count of total events, user details, file hash, status, and so on for the selected asset.
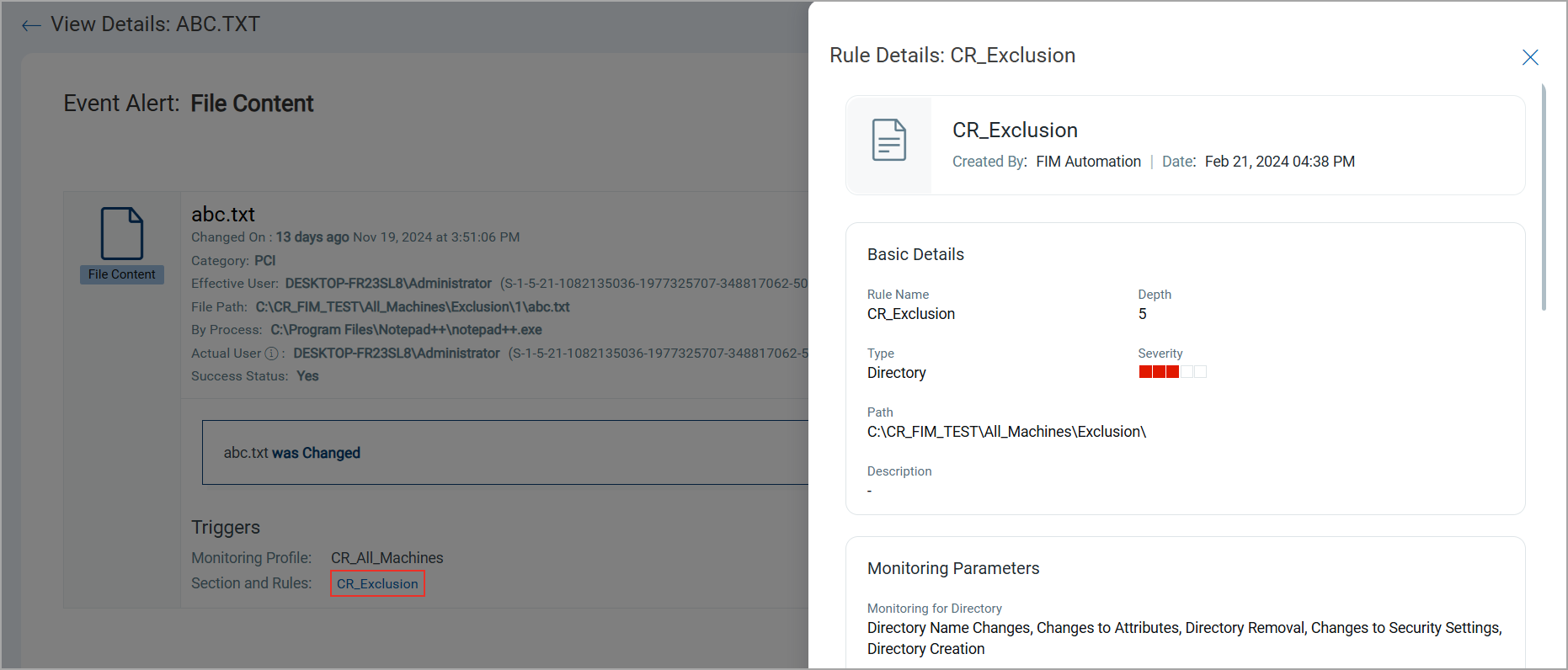
You can click the Rule to see the details.
The success status is shown as yes when the event is successfully executed and no when it is unsuccessful.
With Windows agent, you can see the File size of FIM events for Create, Content, and Attribute Action.
However, with Linux agents, you can see the File size of FIM events for Create, Content, and Security Action.
View User Impersonation Events
Qualys File Integrity Monitoring (FIM) includes the detection and alerting of user impersonation events, helping to prevent unauthorized activities or potential breaches. This feature allows you to distinguish between the Effective User and the Actual User for more granular access and activity insights.
Effective User: The user captured by the Operating System as actively performing changes on monitored locations on the host.
Actual User: The user who has been impersonated.
FIM event details display both users.
To view the user details, navigate to the Events Tab, select an event, and click View Details. If the Effective User and Actual User are not the same, it indicates a user impersonation event detected by FIM.
- For Windows events, the inclusion and exclusion filters work on effective users.
- For Linux events, the inclusion and exclusion filters work on actual users.
Ignoring Events
You can group false-positive events of similar nature and add them to the 'Ignored' list.
Go to Events > Event Review and select specific events and choose Ignore Events from the Actions menu. Optionally, choose Ignore All Matching Events to ignore all events that are currently matching your query for the time frame that you have selected. Ignored events are moved to the Ignored list.
You may get similar events in the future that may appear in your Events list and you may want to ignore those too.
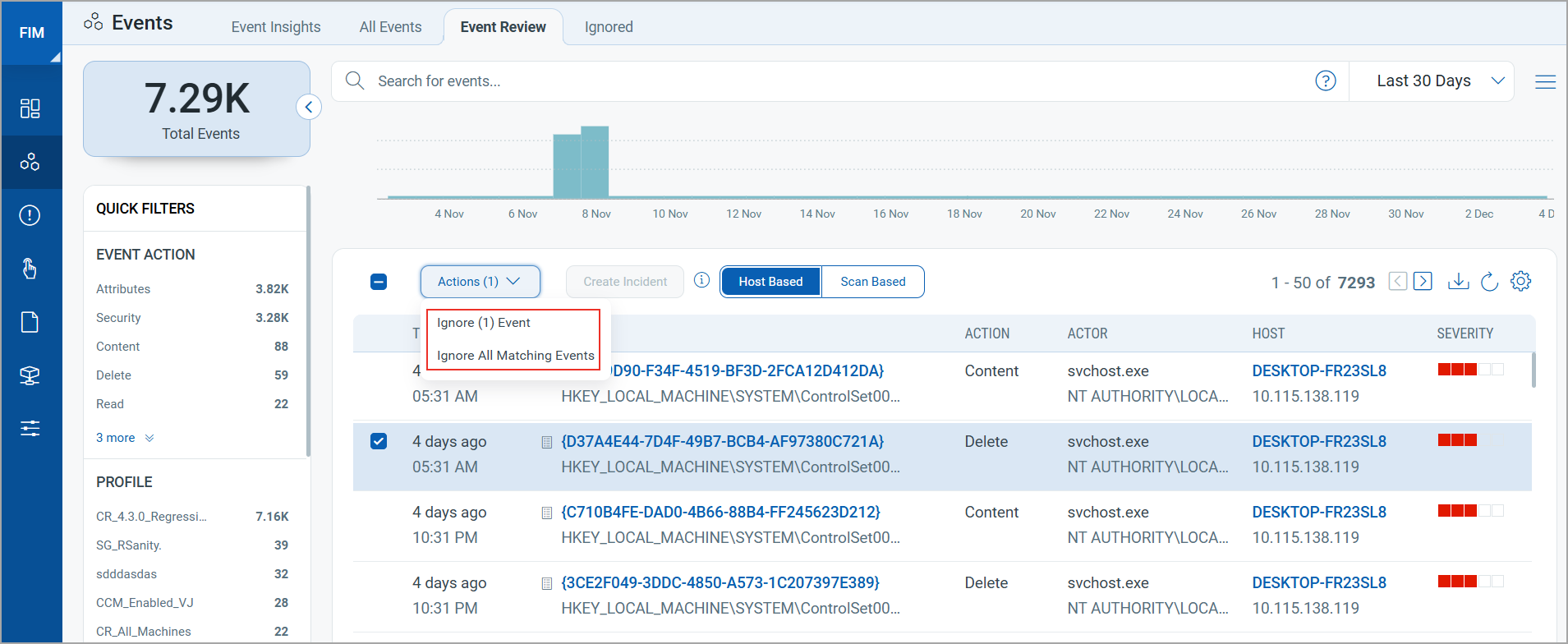
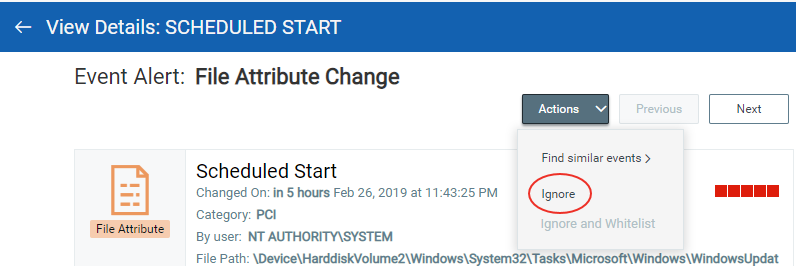
Alternatively, click an event to go to the Event Details page. Select Ignore from the Actions menu.
You can easily restore any ignored event from the Ignored list.
Ignoring Events and Applying Exclusion Filters
Ignore an event and at the same time modify the monitoring profile rule or rules that triggered the event. Identify the event and then click the event to go to the Event details page.
From the Actions menu, choose Ignore and Whitelist. This option is unavailable 1) for events for which incidents are created and 2) events that are created for the rules of the profile that are imported from the profile library and profile rules for which you have set Rule Type as File.
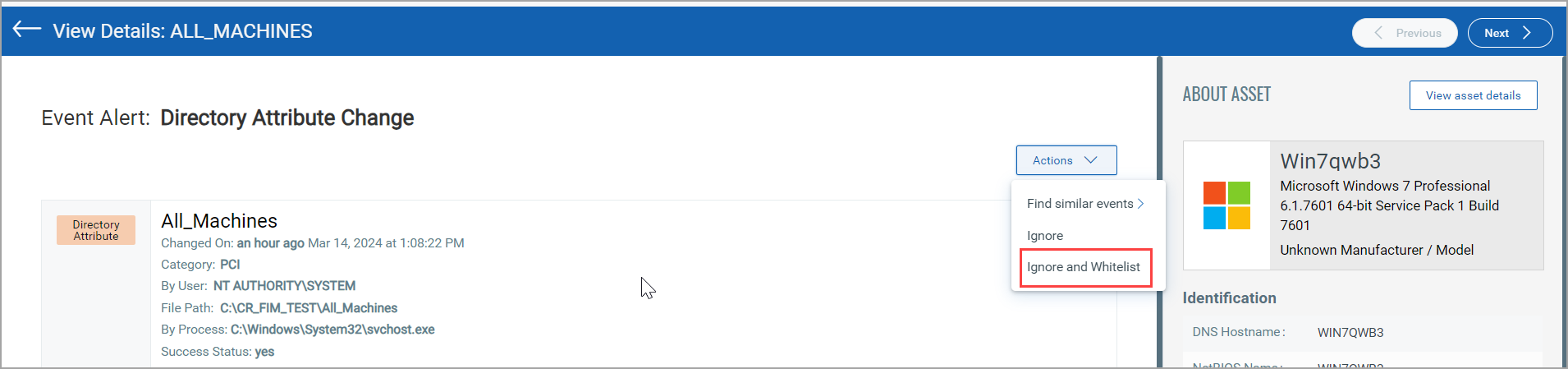
You can view a list of profiles and rules associated with the event and a new exclude filter for the target directory or file. Feel free to make changes to the exclude filter before saving it. Once you hit Save, we'll add the exclude filter to the selected profile rules. The event is moved to the Ignored list and new events do not be generated for the excluded directory/file.
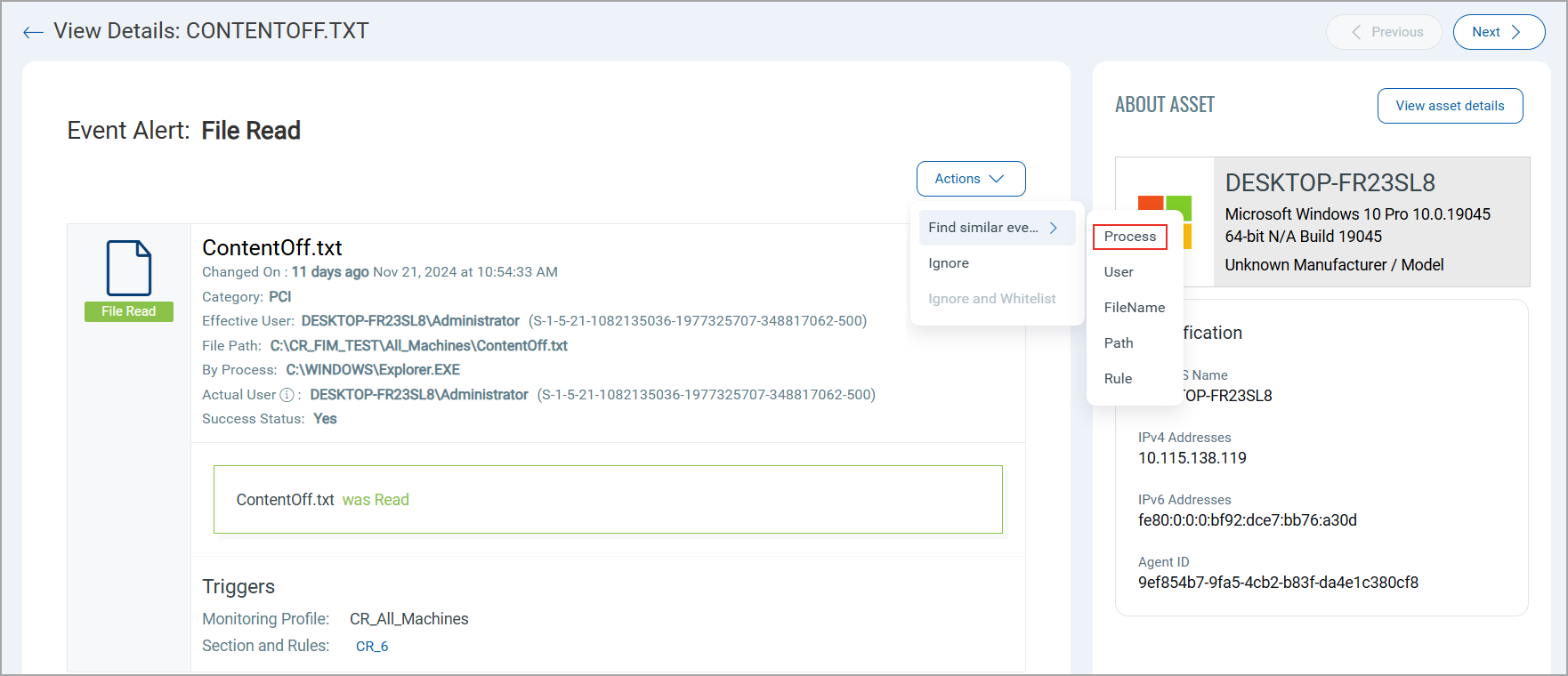
Finding Similar Events
Search for events generated by the same process, user, filename, path, and rule. Drill down on an event, and on the Event Details page, click the Actions menu at the top. Select Find similar events and then choose a filter to view events that match the value of the filter for the selected event.
For example, choose the Process filter to view all the events that are generated by the same process as the current event.
Creating Incidents
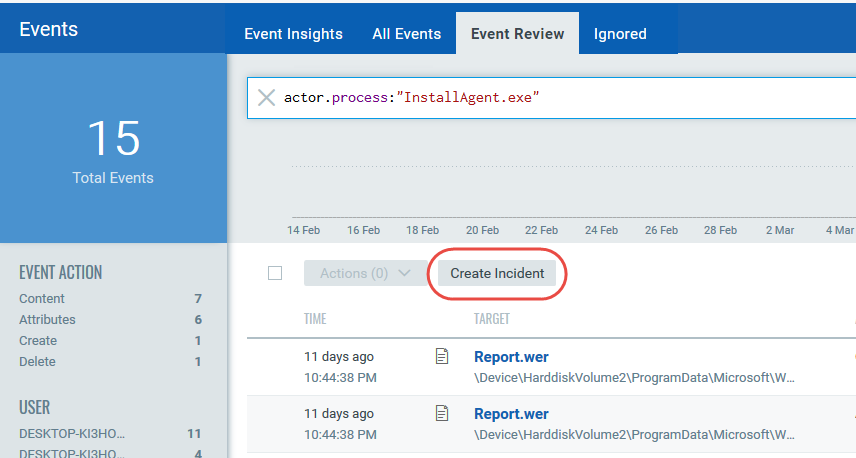
Go to Events > Event Review to see the events that are waiting to be reviewed.
Enter your search query to find related changes that are part of the same incident, and click Create Incident. All events matching your query is included in the incident. You can review the incident and decide if it's valid. View Incidents.
File Integrity Monitoring supports the Cloud Integration Platform Service (CIPS). CIPS pushes data to various cloud interfaces and receives data from FIM.
FIM determines the data in Events that must be sent to CIPS and publishes it.
Exporting Event Records
You can export event records in bulk to a CSV file, providing a convenient way to handle large volumes of data. The report can be exported containing up to 500,000 records. If you attempt to export more than 500,000 records, a notification displays that the export is limited to 500,000. To effectively manage and refine your export, consider utilizing the advanced search option, which allows you to narrow down your search results and focus on the most relevant data.
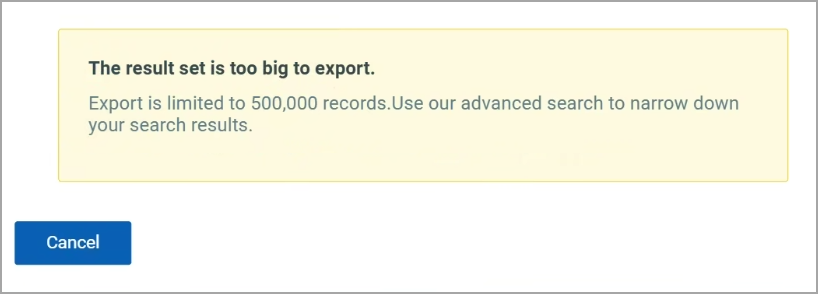
If you want to export event records of more than 500,000, Qualys recommends exporting records in batches of up to 500,000.
To export, follow these steps:
- Navigate to Events > All Events.
- From the list next to the search bar, select the time duration for which you want to download the report.
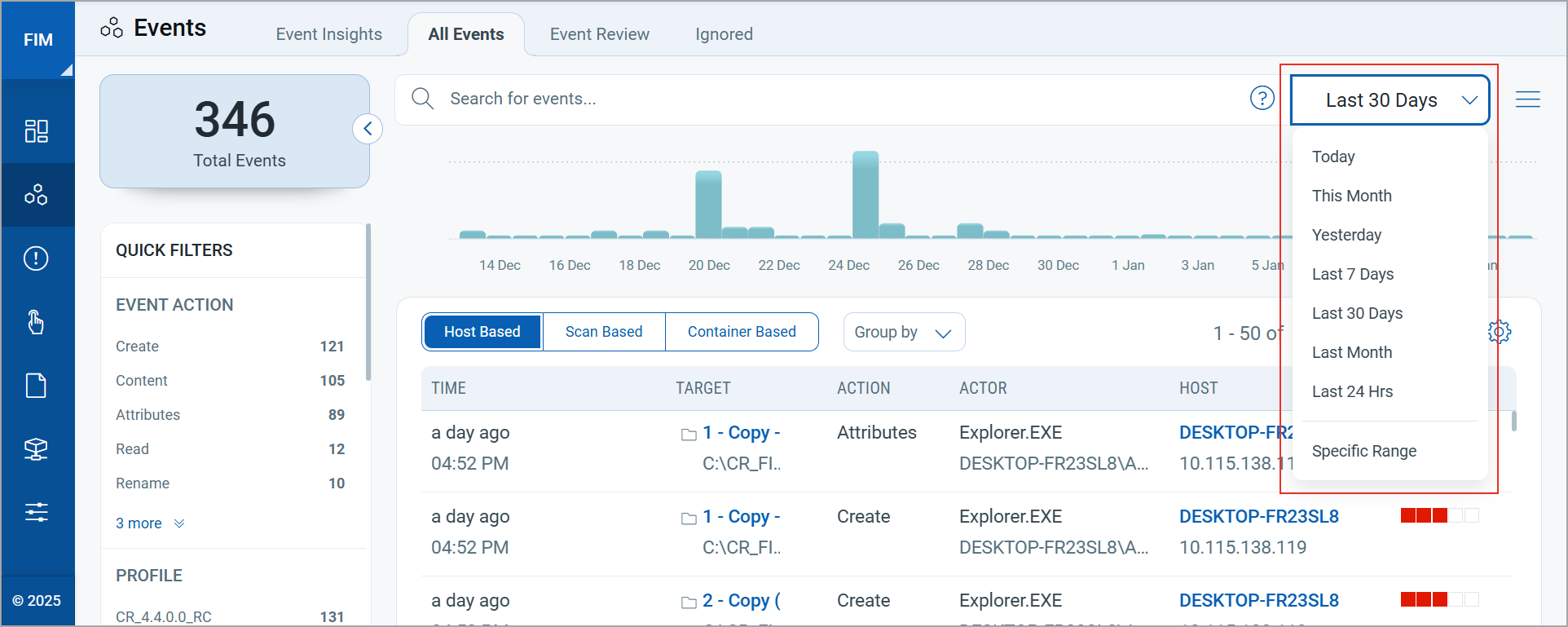
In accordance with the FIM Data Retention Policy, only data from the last 15 months is displayed. For more information, refer to the Data Retention Policy.
- Click
 .
.
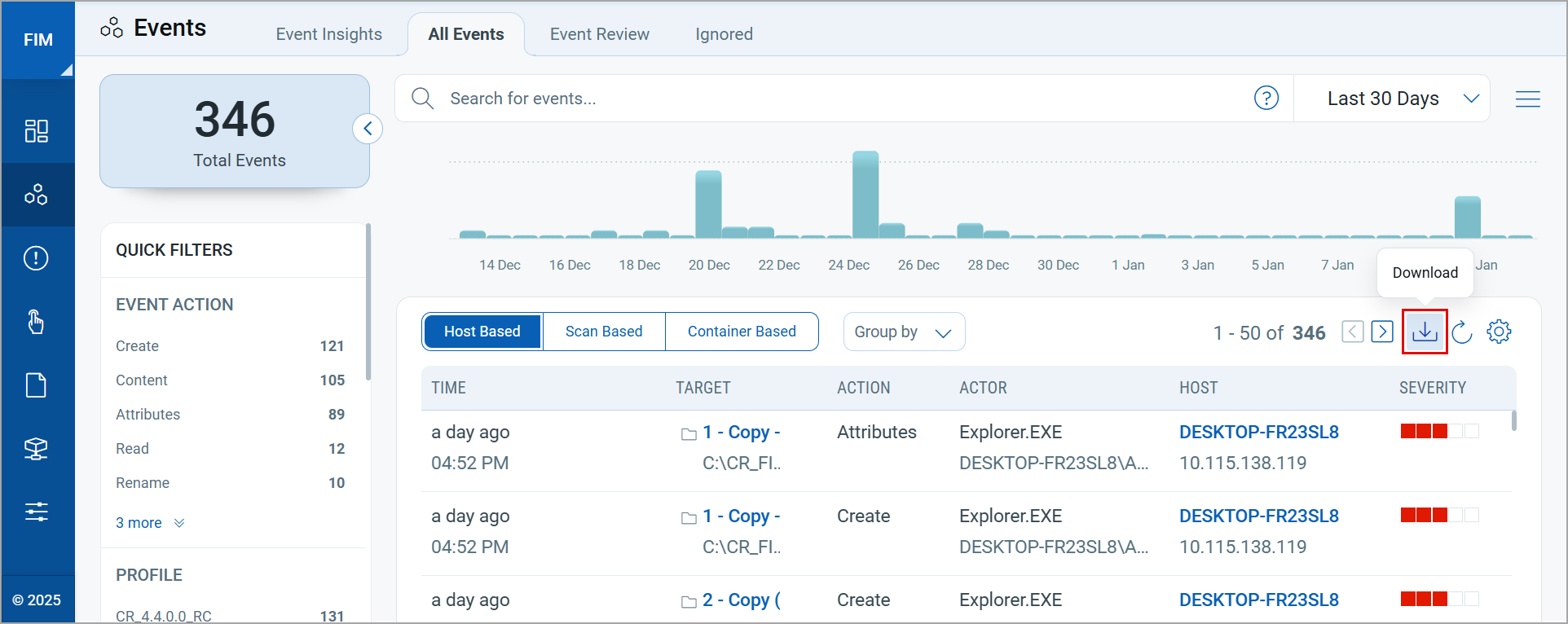
The Download Formats window is displayed.
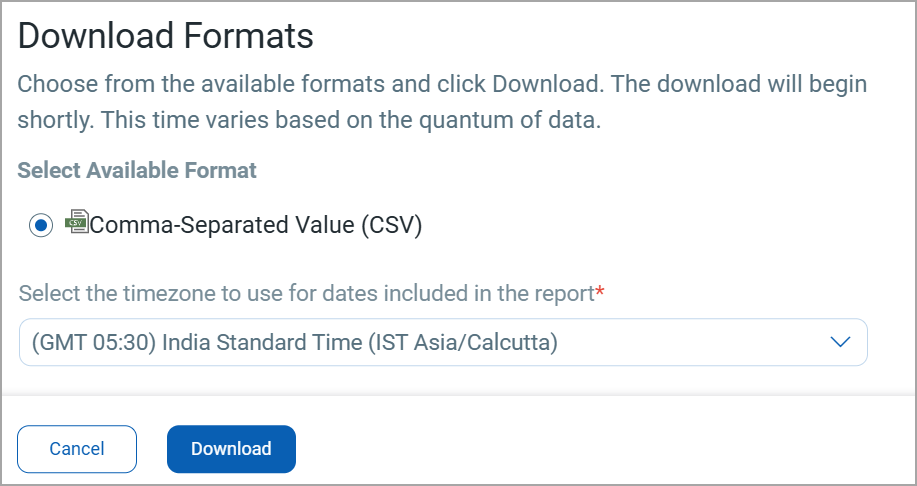
- Select the preferred timezone for the dates to be included in the report from the list.
- Click Download.
The file explorer is displayed.
-
Select a location and save the report on your local machine.
The report is downloaded on your local machine. You can also manage the generated report from the Reports tab.