Enterprise TruRisk™ Platform Release 10.35.1
August 4, 2025
Qualys Vulnerability Management (VM)
REST API Support for CyberArk AIM Authentication Vault
With this enhancement, you can now create a CyberArk AIM authentication record using REST (Representational State Transfer Protocol) APIs in addition to the existing support for SOAP (Simple Object Access Protocol). This extension gives you more flexibility in how you integrate with CyberArk’s AIM Central Credential Provider (CCP), supporting both modern and legacy protocols.
To create the record by using REST API, refer to the following navigation:
- Go to Scans > Authentication > New > Authentication Vaults
The Authentication Vaults window is displayed. - Select CyberArk AIM under New list.
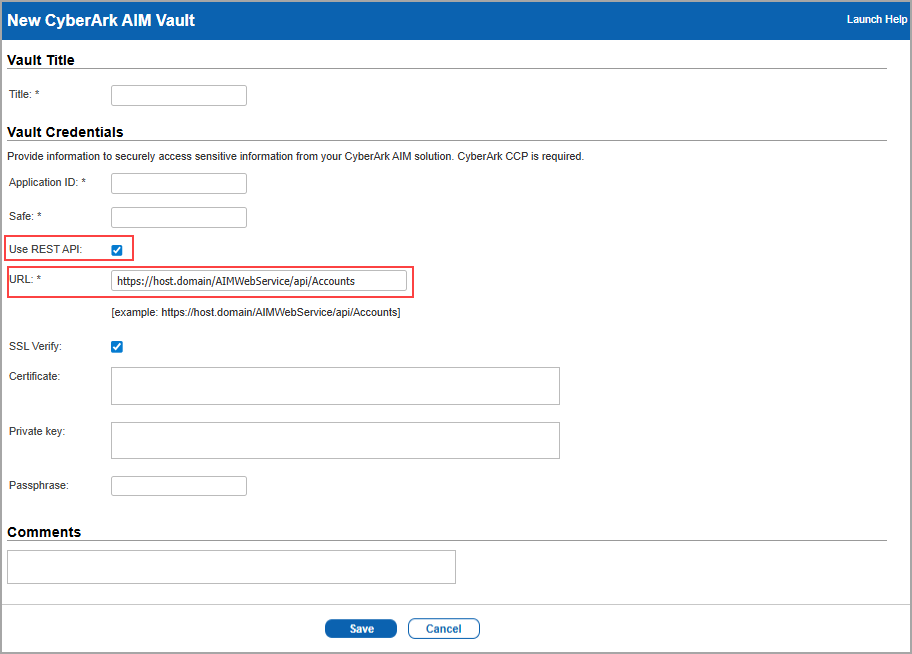
A New CyberArk AIM Vault window is displayed. - Select Use REST API checkbox and provide the REST API URL.
When you select Use REST API checkbox, you can find an example of a REST API URL to be provided in the URL field (example: https://host.domain/AIMWebService/api/Accounts). When unchecked, the URL is displayed for SOAP API as an example below the URL field (example: https://host.domain/AIMWebService/v1.1/AIM.asmx).
- Click Save.
- If you have migrated to CyberArk AIM vault version 14.0.1, you can use the REST API.
- If you require a flexible, lightweight, stateless, and secure API, you can use REST API else use SOAP API for more structured and formal integrations.
Enhanced Email Transparency for SAML Environments
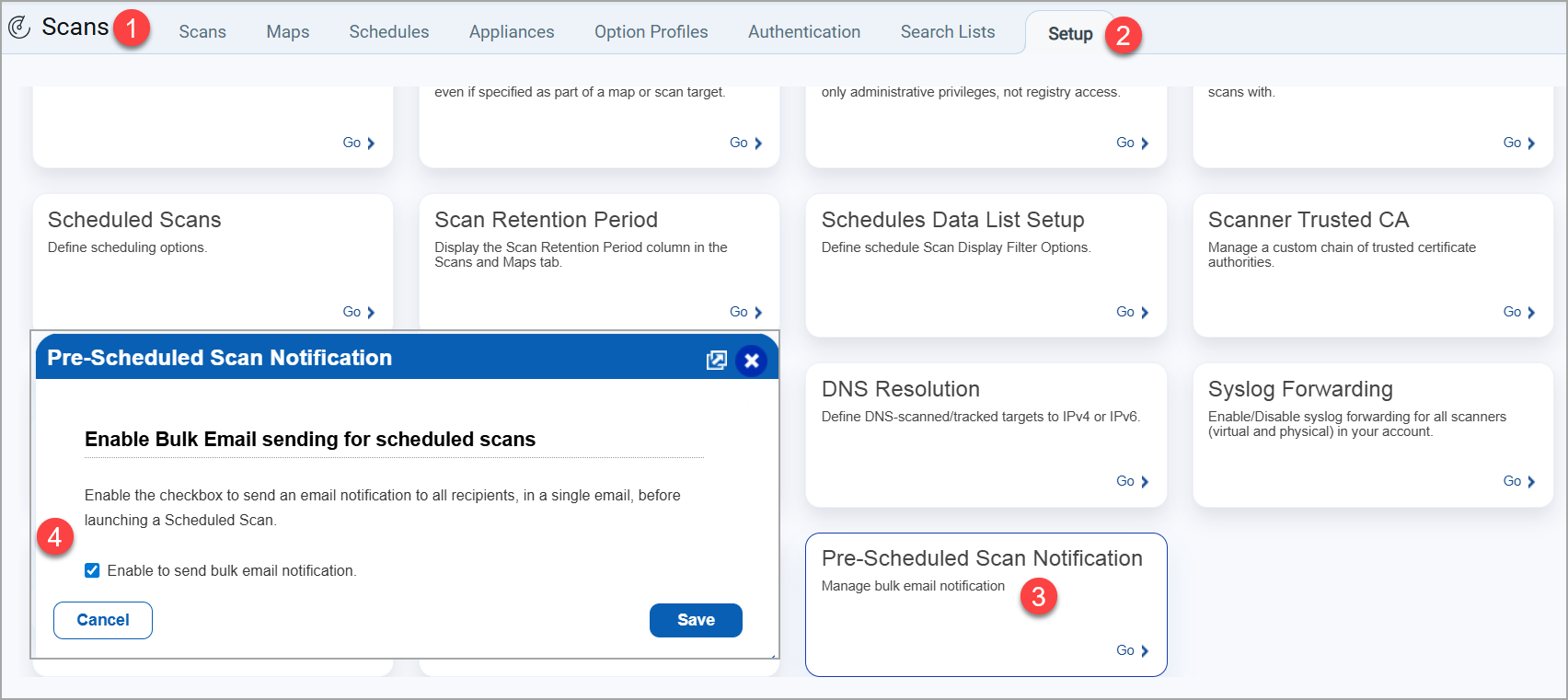
Previously, when pre-scan Vulnerability Management (VM) scheduled notification emails were sent to SAML-enabled users, all recipients were listed in the BCC field, making it unclear who else received the notification. Now, recipients are displayed in the To field for complete transparency. You can control this feature by activating Enable bulk email notification checkbox in the Scans > Setup > Pre-Scheduled Scan Notification.
Extended Permission to Launch Cloud Agent Deployment for Manager Users
With this feature, we have extended the permission to launch the Cloud Agent Deployment to all the Manager User roles. To launch the Cloud Agent Deployment, navigate to Scans > Setup > Cloud Agent Deployment and enable Enable Cloud Agent Deployment checkbox.
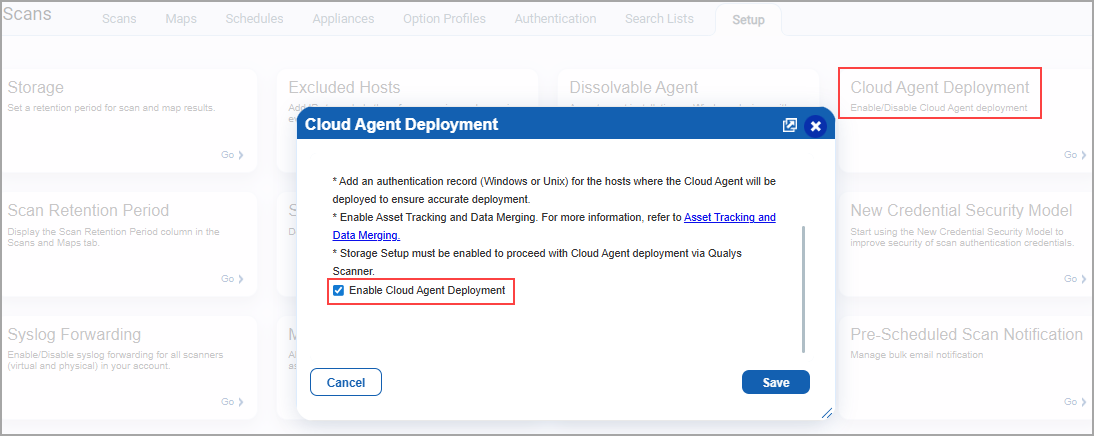
Earlier, only the Primary Contact Manager for the subscription was able to enable the Cloud Agent Deployment, and all the other users with the Manager role were only able to access it. With this enhancement, users with the Manager role can enable the Cloud Agent Deployment without depending on the Primary Contact Manager.
Ensure you meet all the prerequisites before you enable the Cloud Agent Deployment. For more information, refer to Online Help.
Qualys Policy Compliance (PC)
For the list of features and improvements we have made in Policy Audit/Policy Compliance, refer to the Policy Audit UI Release Notes for Release 1.2.0.
Issues Addressed
The following reported and notable customer issues are fixed in this release:
| Component/Category | Application |
Description |
| VM - Authentication Records | Vulnerability Management | When the users performed authenticated scans on the Palo Alto host, the scans did not work, and the scan results showed no host data (no host alive). Relevant code changes have been made to fix the issue. |
| VM - User Management | Vulnerability Management | When users with a consultant account tried to delete some of the existing clients, the delete action was not successful. Users can only create multiple clients and not delete them. This is as per the design. We have now documented this in the Online Help. |
| VM - Authentication Records | Vulnerability Management | When the users performed VMware ESXi authentication using vCenter, the authentication was not completed successfully. Relevant changes have been made to fix the issue. |
| VM - Host Based Report | Vulnerability Management | When the users generated a host based report, the PDF report displayed overlapping text in the result section of a few QIDs. Relevant code changes have been made to fix the issue. |
| VM - Remediation | Vulnerability Management | When the users resolved a ticket manually, and the service re-opened/closed the ticket as required, the resolved date did not modify unless it was manually resolved again. We have now documented this in the Online Help. |
| VM - Agent Deployment UI | Vulnerability Management | When the users performed Cloud Agent Deployment, the system was designed so that the Pre-Authorized AWS EC2 Scanner did not support the deployment. We have now documented this in the Online Help. |
| VM - API General | Vulnerability Management | When the users executed Knowledgebase API /api/2.0/fo/knowledge_base/vuln/, the closing tag was missing in the KnowledgeBase XML output. Relevant code changes have been made to fix the issue. |
| VM - Authentication Records | Vulnerability Management | When the users tried to download the list from the Authentication tab(VMDR > Scans > Authentication > New > Download), the Vault Type column, which had vault record information, was missing in the CSV file. Relevant code changes have been made to fix the issue. |
| VM - API General | Vulnerability Management | When users applied a date filter in the search window (Users > Activity Log > Search) to review the list of executed APIs, the results displayed were inaccurate, showing APIs executed on dates outside the selected range. Relevant code changes have been made to fix the issue. |
| VM - User Management | Vulnerability Management | When users with Reader or Scanner roles tried to view all the other users in the same subscription, they were unable to view all the other users, even though they were not part of any Business Unit. Relevant code changes have been made to fix the issue. |
| VM - Reports General | Vulnerability Management | When the users selected Host Based Findings in the New Scan Report Template and tried to apply the Fixed status filter, they were unable to do so. This is because they did not select the Include trending option under Host Based Findings. This information was not documented. We have now documented this in the Online Help. |
| VM - Remediation | Vulnerability Management | When the users viewed the tickets on the Remediation tab, they observed that the edited symbol is being displayed on a few QIDs in the remediation tickets, even though no edits had been made to those QIDs in the KnowledgeBase. Relevant code changes have been made to fix the issue. |
For the list of issues addressed in Policy Audit/Policy Compliance, refer to the Policy Audit UI Release Notes for Release 1.2.0.